Buyer`s Guide - Windows IT Pro
... updates and patches and run periodic checks. Some firewalls are updated almost as frequently as antivirus scanners. Firewall updates include bug fixes, increased functionality, and increased ability to recognize new types of threats. In many cases, if a firewall notices a persistent threat, the fire ...
... updates and patches and run periodic checks. Some firewalls are updated almost as frequently as antivirus scanners. Firewall updates include bug fixes, increased functionality, and increased ability to recognize new types of threats. In many cases, if a firewall notices a persistent threat, the fire ...
Network Security Platform 8.2.7.71-8.2.3.84 Manager-Mxx30
... Currently port 4167 is used as the UDP source port number for the SNMP command channel communication between Manager and Sensors. This is to prevent opening up all UDP ports for inbound connectivity from SNMP ports on the sensor. Older JRE versions allowed the Manager to bind to the same source port ...
... Currently port 4167 is used as the UDP source port number for the SNMP command channel communication between Manager and Sensors. This is to prevent opening up all UDP ports for inbound connectivity from SNMP ports on the sensor. Older JRE versions allowed the Manager to bind to the same source port ...
Speech Title Here
... Available when needed Performs at expected levels Vendors provide quality products Product support is appropriate ...
... Available when needed Performs at expected levels Vendors provide quality products Product support is appropriate ...
Remote Control - Windows IT Pro
... who need to install or update software on users’ desktops from a CD-ROM in the Help desk staff member’s local drive. Some of the products in this Buyer’s Guide are specifically designed with Help desk functions. Last but not least, check for usability before settling on a particular product. Most ve ...
... who need to install or update software on users’ desktops from a CD-ROM in the Help desk staff member’s local drive. Some of the products in this Buyer’s Guide are specifically designed with Help desk functions. Last but not least, check for usability before settling on a particular product. Most ve ...
Network Policy and Access Services in Windows Server 2008
... – Requires manual creation and management – Should not be used on networks with more than 10 subnets – All affected routers require reconfiguration if the network changes ...
... – Requires manual creation and management – Should not be used on networks with more than 10 subnets – All affected routers require reconfiguration if the network changes ...
Computer Concepts
... computer user’s Internet usage and send this data back to the company or person that created it • usually installed without the computer user’s permission or knowledge • Anti-spyware software detects spyware and deletes them Adware • software installed with another program usually with the user’s pe ...
... computer user’s Internet usage and send this data back to the company or person that created it • usually installed without the computer user’s permission or knowledge • Anti-spyware software detects spyware and deletes them Adware • software installed with another program usually with the user’s pe ...
Planning and Configuring Routing and Switching
... subnets that can be created from n bits • RIP is a distance-vector routing algorithm that calculates paths based on hops • OSPF is a link-state routing algorithm that calculates paths based on a configurable metric called cost 70-293: MCSE Guide to Planning a Microsoft Windows Server 2003 Network ...
... subnets that can be created from n bits • RIP is a distance-vector routing algorithm that calculates paths based on hops • OSPF is a link-state routing algorithm that calculates paths based on a configurable metric called cost 70-293: MCSE Guide to Planning a Microsoft Windows Server 2003 Network ...
IMPACT OF SECURITY BREACHES
... rooms should be locked. Access to server rooms should be strictly controlled and logged. Some of the access control mechanisms that can be used include badges and biometrics. Access should be prearranged and authorized by a senior member of the staff. If dedicated server rooms do not exist, servers ...
... rooms should be locked. Access to server rooms should be strictly controlled and logged. Some of the access control mechanisms that can be used include badges and biometrics. Access should be prearranged and authorized by a senior member of the staff. If dedicated server rooms do not exist, servers ...
InterScan Messaging Security Solutions
... “Having been founded in 1988, Trend Micro has nearly two decades of experience in the enterprise, service provider, mid-sized, SOHO and consumer security market. With many years of success behind it, the company has grown to be a current global leader in network security” – Radicati 2 Trend Micro st ...
... “Having been founded in 1988, Trend Micro has nearly two decades of experience in the enterprise, service provider, mid-sized, SOHO and consumer security market. With many years of success behind it, the company has grown to be a current global leader in network security” – Radicati 2 Trend Micro st ...
TCP/IP for Security Administrators
... Security is (or will be) your job. Security is your life. You are security for your org. If you wanna be good, there are things you have gotta know— How to say “I don’t know” How to say “That’s not allowed” without giving away the fact that you really don’t know How to look innocent—or mean—really, ...
... Security is (or will be) your job. Security is your life. You are security for your org. If you wanna be good, there are things you have gotta know— How to say “I don’t know” How to say “That’s not allowed” without giving away the fact that you really don’t know How to look innocent—or mean—really, ...
Chapter 10 - SaigonTech
... security breach and notify the network administrator – May be able to take countermeasures if an attack is in progress – Invaluable tool to help administrators know how often their network is under attack and devise security policies aimed at thwarting threats before they have a chance to succeed Gu ...
... security breach and notify the network administrator – May be able to take countermeasures if an attack is in progress – Invaluable tool to help administrators know how often their network is under attack and devise security policies aimed at thwarting threats before they have a chance to succeed Gu ...
File
... the signs involved with an attack (false site details, no HTTPS flag, and/or missing security information) is when attacks are successful. System administrators overcome this by forcing user restrictions on what they can and cannot access, so that even if there is a security leak, the damage is mini ...
... the signs involved with an attack (false site details, no HTTPS flag, and/or missing security information) is when attacks are successful. System administrators overcome this by forcing user restrictions on what they can and cannot access, so that even if there is a security leak, the damage is mini ...
Hyper-V Cloud Fast Track
... Multiple logical paths with QoS (blade backplanes) 2x (or more) 10GbE 1 GbE management 4 or 8Gb FC or 10Gb based iSCSI SAN boot (blades), local boot (rack) Remote OOB management ...
... Multiple logical paths with QoS (blade backplanes) 2x (or more) 10GbE 1 GbE management 4 or 8Gb FC or 10Gb based iSCSI SAN boot (blades), local boot (rack) Remote OOB management ...
SharePoint Server 2010 應用程式底層邏輯開發
... Loads ADO.NET Data Services handler assembly Microsoft.SharePoint.ListDataService.dll ...
... Loads ADO.NET Data Services handler assembly Microsoft.SharePoint.ListDataService.dll ...
Chapter 10 - Computer Science Technology
... security breach and notify the network administrator – May be able to take countermeasures if an attack is in progress – Invaluable tool to help administrators know how often their network is under attack and devise security policies aimed at thwarting threats before they have a chance to succeed Gu ...
... security breach and notify the network administrator – May be able to take countermeasures if an attack is in progress – Invaluable tool to help administrators know how often their network is under attack and devise security policies aimed at thwarting threats before they have a chance to succeed Gu ...
Week 3 Chapter 04
... many types of changes that might be made in Active Directory, including when: – There are attribute changes to the schema – Objects are moved, such as user accounts moved from one OU to a different one – New objects are created, such as a new OU – A container or object is deleted and then brought ba ...
... many types of changes that might be made in Active Directory, including when: – There are attribute changes to the schema – Objects are moved, such as user accounts moved from one OU to a different one – New objects are created, such as a new OU – A container or object is deleted and then brought ba ...
David Mannies resume
... Technical lead and principal Java developer of a guest assistance kiosk for Target. Kiosk was used in locating products and viewing the weekly newspaper circular. Responsibilities were the complete design and implementation of the kiosk software. The software was developed as a browser application r ...
... Technical lead and principal Java developer of a guest assistance kiosk for Target. Kiosk was used in locating products and viewing the weekly newspaper circular. Responsibilities were the complete design and implementation of the kiosk software. The software was developed as a browser application r ...
windows and linux operating systems from a security perspective
... programs, tools, and utilities that manage computer hardware resources and offer common services for client application software [1]. The operating system is the first program to execute upon booting a computer and is thus considered the most vital type of system software. An operating system runs u ...
... programs, tools, and utilities that manage computer hardware resources and offer common services for client application software [1]. The operating system is the first program to execute upon booting a computer and is thus considered the most vital type of system software. An operating system runs u ...
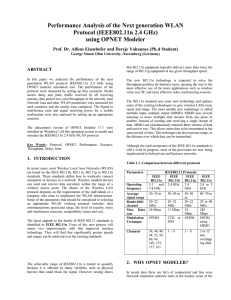
Performance Analysis of the Next generation WLAN Protocol
... Scenario1:- A wired LAN and three access points which are connected through a central WLAN controller and three Wireless workstations connected at each access points. Fig.1 Scenario2:- A wired LAN and three access points which are connected through a central WLAN controller and five Wireless worksta ...
... Scenario1:- A wired LAN and three access points which are connected through a central WLAN controller and three Wireless workstations connected at each access points. Fig.1 Scenario2:- A wired LAN and three access points which are connected through a central WLAN controller and five Wireless worksta ...
Windows 7 and Windows Server 2008 R2 Networking
... Background synchronization for offline files With Windows Vista®, user updates to files are written to the server computer when the user is online. If the user is offline, the file updates are cached on the client computer’s disk and synchronized with the server the next time the user is online. In ...
... Background synchronization for offline files With Windows Vista®, user updates to files are written to the server computer when the user is online. If the user is offline, the file updates are cached on the client computer’s disk and synchronized with the server the next time the user is online. In ...
Resume for Van Renier
... Understand commonly protocols (ie. HTTP/DNS/Telnet/SSH/FTP/TFTP) to monitor/report anomalies or suspicious activity. Identify infrastructure/application bottlenecks using monitoring applications and notify responsible teams. Serve as business partner to customers, understanding their needs and ...
... Understand commonly protocols (ie. HTTP/DNS/Telnet/SSH/FTP/TFTP) to monitor/report anomalies or suspicious activity. Identify infrastructure/application bottlenecks using monitoring applications and notify responsible teams. Serve as business partner to customers, understanding their needs and ...
Windows HPC Server 2008 and Productivity Overview
... major metric of value to highend computing users… A common software environment for scientific computation encompassing desktop to highend systems will enhance productivity gains by promoting ease of use and manageability of systems.” ...
... major metric of value to highend computing users… A common software environment for scientific computation encompassing desktop to highend systems will enhance productivity gains by promoting ease of use and manageability of systems.” ...
RECOMMENDED SETTINGS FOR AVIMARK
... Keep your drivers up to date for printers and any other devices. Stay current with all Windows updates. Keep your router and peripherals firmware up to date. Make sure computers are connected at the same speed and duplex. (ex. 100 mbs or 1 gbs) When workstations with Windows 7, 8, 8.1, and 10 get co ...
... Keep your drivers up to date for printers and any other devices. Stay current with all Windows updates. Keep your router and peripherals firmware up to date. Make sure computers are connected at the same speed and duplex. (ex. 100 mbs or 1 gbs) When workstations with Windows 7, 8, 8.1, and 10 get co ...
CS 356 – Lecture 9 Malicious Code
... • the most difficult design issue with a GD scanner is to determine how long to run each interpretation ...
... • the most difficult design issue with a GD scanner is to determine how long to run each interpretation ...
Forcepoint™ Stonesoft Next Generation Firewall
... AETs and traffic anomalies that evade other next-generation firewalls. Only after traffic has been fully normalized can it be properly inspected across all protocols and layers for threats and malware. And only Forcepoint NGFW has been successfully tested against more than 800 million AETs. KNOWLEDG ...
... AETs and traffic anomalies that evade other next-generation firewalls. Only after traffic has been fully normalized can it be properly inspected across all protocols and layers for threats and malware. And only Forcepoint NGFW has been successfully tested against more than 800 million AETs. KNOWLEDG ...