EX-6001 4-Port USB2.0 to Ethernet Adapter (USB over IP)
... to your Local Area Network. The USBIP Windows Admin utility is capable enough to identify the USB Server’s based USB Servers by it’s IP address on the network. As soon as the USB Server’s box is detected with a specific IP address the Windows automatically invokes a Found New Hardware Wizard to inst ...
... to your Local Area Network. The USBIP Windows Admin utility is capable enough to identify the USB Server’s based USB Servers by it’s IP address on the network. As soon as the USB Server’s box is detected with a specific IP address the Windows automatically invokes a Found New Hardware Wizard to inst ...
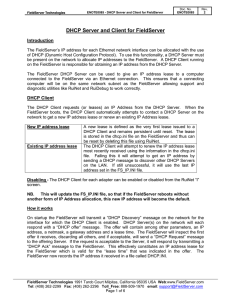
DHCP Server and Client for FieldServer
... The FieldServer DHCP Server is enabled by default on both Ethernet adapters* and will be active after restarting the FieldServer. The DHCP Server has the same IP address as the adapter it is operating on. The FieldServer probes the Ethernet network for other DHCP Servers every 3 minutes and will dis ...
... The FieldServer DHCP Server is enabled by default on both Ethernet adapters* and will be active after restarting the FieldServer. The DHCP Server has the same IP address as the adapter it is operating on. The FieldServer probes the Ethernet network for other DHCP Servers every 3 minutes and will dis ...
RFC 3261+ Session Initiation Protocol (SIP)
... intern converts it from one format to another if needed, then sends the packets on to their destination which decompress and converts it back into voice. ...
... intern converts it from one format to another if needed, then sends the packets on to their destination which decompress and converts it back into voice. ...
2. HBR Overview - Computer Science, Columbia University
... position in computer networking. As its usage base expands, so does the list of requirements, and much research and development is being done to enable IP to meet various needs. For example, the next major version of IP, IPv6, is being developed to address concerns such as the size of the address sp ...
... position in computer networking. As its usage base expands, so does the list of requirements, and much research and development is being done to enable IP to meet various needs. For example, the next major version of IP, IPv6, is being developed to address concerns such as the size of the address sp ...
Netgear WGU624 Manual - FTP Directory Listing
... Routing Information Protocol ................................................................................... B-2 IP Addresses and the Internet ....................................................................................... B-2 Netmask ..................................................... ...
... Routing Information Protocol ................................................................................... B-2 IP Addresses and the Internet ....................................................................................... B-2 Netmask ..................................................... ...
IPv6 and Transition Mechanisms
... Transition to IPv6 • Not an after-thought but designed to be part of the new protocol since the beginning • Overview of transition requirements: – Gradual site transition: a site may have only some of its systems supporting IPv6 – Minimum transition requirements: a site can support IPv6 just by off ...
... Transition to IPv6 • Not an after-thought but designed to be part of the new protocol since the beginning • Overview of transition requirements: – Gradual site transition: a site may have only some of its systems supporting IPv6 – Minimum transition requirements: a site can support IPv6 just by off ...
TCP/IP Tutorial and Technical Overview
... This edition applies to Transmission Control Protocol/Internet Protocol (TCP/IP) in general and selected IBM and OEM implementations thereof. Comments may be addressed to: IBM Corporation, International Technical Support Organization Dept. HZ8 Building 678 P.O. Box 12195 Research Triangle Park, NC 2 ...
... This edition applies to Transmission Control Protocol/Internet Protocol (TCP/IP) in general and selected IBM and OEM implementations thereof. Comments may be addressed to: IBM Corporation, International Technical Support Organization Dept. HZ8 Building 678 P.O. Box 12195 Research Triangle Park, NC 2 ...
information
... Confidentiality: ensures that certain information is not disclosed to unauthorized entities. Eg Routing information information should not be leaked out because it can help to identify and locate the targets Integrity: guarantee that a message being transferred is never corrupted. Authentication: en ...
... Confidentiality: ensures that certain information is not disclosed to unauthorized entities. Eg Routing information information should not be leaked out because it can help to identify and locate the targets Integrity: guarantee that a message being transferred is never corrupted. Authentication: en ...
TL-WR642G 108M Wireless Router - TP-Link
... authentication, as well as TKIP/AES encryption security. It also supports VPN Pass-through for sensitive data secure transmission. It adopts 108M Super G™ WLAN Transmission Technology, which offers the highest throughput performance available on the market today, and data rates of up to 108Mbps. In ...
... authentication, as well as TKIP/AES encryption security. It also supports VPN Pass-through for sensitive data secure transmission. It adopts 108M Super G™ WLAN Transmission Technology, which offers the highest throughput performance available on the market today, and data rates of up to 108Mbps. In ...
CCENT/CCNA ICND1 100-105 Official
... In particular, Greg Cote, Joe Stralo, and Phil Vancil were a great help while we worked on these titles. Chris Cleveland did the development editing for the very first Cisco Press exam certification guide way back in 1998, and he’s been involved with the series ever since. It’s always great to work ...
... In particular, Greg Cote, Joe Stralo, and Phil Vancil were a great help while we worked on these titles. Chris Cleveland did the development editing for the very first Cisco Press exam certification guide way back in 1998, and he’s been involved with the series ever since. It’s always great to work ...
Defense
... IETF Draft-standard proposed by RSA, Microsoft, Cisco • draft-josefsson-pppext-eap-tls-eap-02.txt. PEAP is an 802.1x Authentication protocol typically designed for enhancing access control in wireless LANs (WLANs) It is built on top of two well known protocols • Extensible Authentication Proto ...
... IETF Draft-standard proposed by RSA, Microsoft, Cisco • draft-josefsson-pppext-eap-tls-eap-02.txt. PEAP is an 802.1x Authentication protocol typically designed for enhancing access control in wireless LANs (WLANs) It is built on top of two well known protocols • Extensible Authentication Proto ...
Pastry: Scalable, distributed object location and routing for large
... FreeNet [1–4] have recently gained popularity. Several research projects aim at constructing other types of peer-to-peer applications and understanding more of the issues and requirements of such applications and systems [5, 4]. Peer-to-peer systems can be characterized as distributed systems in whi ...
... FreeNet [1–4] have recently gained popularity. Several research projects aim at constructing other types of peer-to-peer applications and understanding more of the issues and requirements of such applications and systems [5, 4]. Peer-to-peer systems can be characterized as distributed systems in whi ...
ITE PC v4.0 Chapter 1 - Chakarov - Ivailo Chakarov
... process uses a client’s 48-bit Ethernet MAC address, and inserts another 16 bits in the middle of the 46-bit MAC address to create a 64-bit Interface ID advantage is Ethernet MAC address can be used to determine the Interface – easily tracked EUI-64 Interface ID is represented in binary and is m ...
... process uses a client’s 48-bit Ethernet MAC address, and inserts another 16 bits in the middle of the 46-bit MAC address to create a 64-bit Interface ID advantage is Ethernet MAC address can be used to determine the Interface – easily tracked EUI-64 Interface ID is represented in binary and is m ...
Chapter 4
... • The VC network came about because of its similarity to telephone networks • But the Internet was connecting complex computers, so the datagram network was created because the computers could handle more complex operations than the routers (recall our IMP friends from Chapter 1) – This also makes i ...
... • The VC network came about because of its similarity to telephone networks • But the Internet was connecting complex computers, so the datagram network was created because the computers could handle more complex operations than the routers (recall our IMP friends from Chapter 1) – This also makes i ...
Module 01 - IPv6 ISIS and iBGP
... somewhat lighter than it is for IPv4. A bigger advantage starts with the customer assignments made by the ISP – the ISP simply has to assign a /48 to each of their customers. This is the minimum assignment for any site/customer – within this /48 there are 64k possible subnets, deemed sufficient for ...
... somewhat lighter than it is for IPv4. A bigger advantage starts with the customer assignments made by the ISP – the ISP simply has to assign a /48 to each of their customers. This is the minimum assignment for any site/customer – within this /48 there are 64k possible subnets, deemed sufficient for ...
NOTE - Surveillance System, Security Cameras, CCTV Articles
... Configure Specific Pinholes . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 70 Planning for Your Pinholes . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 70 Example: A LAN Requiring Three Pinholes . . . . . . . . . . . . . . . . . 70 Pinhole Configuration Procedure . . . . . . ...
... Configure Specific Pinholes . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 70 Planning for Your Pinholes . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 70 Example: A LAN Requiring Three Pinholes . . . . . . . . . . . . . . . . . 70 Pinhole Configuration Procedure . . . . . . ...
Netopia Software User Guide V7
... Pinholes . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 75 Configure Specific Pinholes . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 76 Planning for Your Pinholes . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 76 Example: A LA ...
... Pinholes . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 75 Configure Specific Pinholes . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 76 Planning for Your Pinholes . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 76 Example: A LA ...
project report
... The growth of the Internet has been a phenomenon, which has been receiving a lot of analysis and discussion these past few years. Few who have been working with it from it's inception as ARPANET predicted this expansion, especially as the concept of a packet switched network was created by the milit ...
... The growth of the Internet has been a phenomenon, which has been receiving a lot of analysis and discussion these past few years. Few who have been working with it from it's inception as ARPANET predicted this expansion, especially as the concept of a packet switched network was created by the milit ...
DEPLOYMENT IPV6 OVER IPV4 NETWORK INFRASTRUCTURE Tien Dung Hoang
... writing, each group of 4 octets (16 bits) is represented as unsigned integer which is written in hexadecimal form and separated by colons (:). With 128 bits are used, IPv6 will have 2128 ~ 340,282,366,920,938,463,463,374,607,431,768,211,456 ~ 3.4 * 1038 IPv6 addresses. It is 296 times more than IPv4 ...
... writing, each group of 4 octets (16 bits) is represented as unsigned integer which is written in hexadecimal form and separated by colons (:). With 128 bits are used, IPv6 will have 2128 ~ 340,282,366,920,938,463,463,374,607,431,768,211,456 ~ 3.4 * 1038 IPv6 addresses. It is 296 times more than IPv4 ...
Introducing the Specifications of the MEF
... All, since they provide the fundamentals required to build devices and services that deliver Carrier Ethernet. For Enterprise users it gives the background to Service Level Specifications for Carrier Ethernet Services being offered by their Service Providers and helps to plan Ethernet Services as pa ...
... All, since they provide the fundamentals required to build devices and services that deliver Carrier Ethernet. For Enterprise users it gives the background to Service Level Specifications for Carrier Ethernet Services being offered by their Service Providers and helps to plan Ethernet Services as pa ...
Magnum Network Software – DX
... brought against purchaser so far as based on a claim that said equipment constitutes an infringement of any patent of the United States, if notified promptly in writing and given authority, information, and assistance at GarrettCom's expense for the defense of the claim. In event of a final award of ...
... brought against purchaser so far as based on a claim that said equipment constitutes an infringement of any patent of the United States, if notified promptly in writing and given authority, information, and assistance at GarrettCom's expense for the defense of the claim. In event of a final award of ...
Multicast_I
... •A unicast address identifies a single IP interface •A broadcast address identifies all IP interfaces on the subnet •A multicast address identifies a set of IP interfaces •A multicast datagram is received only by those interfaces interested in the datagram (applications wishing to participate in the ...
... •A unicast address identifies a single IP interface •A broadcast address identifies all IP interfaces on the subnet •A multicast address identifies a set of IP interfaces •A multicast datagram is received only by those interfaces interested in the datagram (applications wishing to participate in the ...
PDF
... For flexibility, the EHWIC includes one SFP slot, which supports a Cisco SFP (see Table 1 later in this document) and a copper RJ-45 port, where either the SFP port (operating at 100/1000 Mbps) or the RJ-45 (operating at 10/100/1000 Mbps) port can be active at one time. The SFP port supports digital ...
... For flexibility, the EHWIC includes one SFP slot, which supports a Cisco SFP (see Table 1 later in this document) and a copper RJ-45 port, where either the SFP port (operating at 100/1000 Mbps) or the RJ-45 (operating at 10/100/1000 Mbps) port can be active at one time. The SFP port supports digital ...
IPv4/IPv6 Translation: Framework
... – In the stateless mode, there is no IPv4 address pool in the translator. A special block of IPv4 addresses are reserved, embedded in the IPv6 addresses and represented by the IPv6 end ...
... – In the stateless mode, there is no IPv4 address pool in the translator. A special block of IPv4 addresses are reserved, embedded in the IPv6 addresses and represented by the IPv6 end ...