PPT - ME Kabay
... Universal architecture for datacomm Allow interoperability of equipment from all manufacturers Defines 7 layers for specific functions Number of layers is arbitrary ...
... Universal architecture for datacomm Allow interoperability of equipment from all manufacturers Defines 7 layers for specific functions Number of layers is arbitrary ...
William Stallings Data and Computer Communications
... Data sent out of sequence Small chunks (packets) of data at a time Packets passed from node to node between source and destination Used for terminal to computer and computer to computer communications ...
... Data sent out of sequence Small chunks (packets) of data at a time Packets passed from node to node between source and destination Used for terminal to computer and computer to computer communications ...
layered
... Protocol A may use protocol B as a step in its execution for example, packet transfer is one step in the execution of the example reliable file transfer protocol This form of dependency is called layering reliable file transfer is layered above packet transfer protocol like a subroutine ...
... Protocol A may use protocol B as a step in its execution for example, packet transfer is one step in the execution of the example reliable file transfer protocol This form of dependency is called layering reliable file transfer is layered above packet transfer protocol like a subroutine ...
Week 6 - cda college
... The idea behind the model: Break up the design to make implementation simpler. Each layer has a well-defined function. Layers pass to one another only the information that is relevant at each level. Communication happens only between adjacent layers. ...
... The idea behind the model: Break up the design to make implementation simpler. Each layer has a well-defined function. Layers pass to one another only the information that is relevant at each level. Communication happens only between adjacent layers. ...
PowerPoint Template
... Sends data to another computer in the form of bits 0 and 1. Control data flow between computer and cable systems ...
... Sends data to another computer in the form of bits 0 and 1. Control data flow between computer and cable systems ...
HyperText Transfer Protocol
... Provides the functional and procedural means of transferring variable length data sequences from a source to a destination via one or more networks while maintaining the quality of service requested by the Transport layer. ...
... Provides the functional and procedural means of transferring variable length data sequences from a source to a destination via one or more networks while maintaining the quality of service requested by the Transport layer. ...
Week 9
... Link layer device: stores and forwards Ethernet frames forwards frame based on MAC dest address uses CSMA/CD to access segment Transparent: hosts are unaware of presence of switches plug-and-play: switches do not need to be configured ...
... Link layer device: stores and forwards Ethernet frames forwards frame based on MAC dest address uses CSMA/CD to access segment Transparent: hosts are unaware of presence of switches plug-and-play: switches do not need to be configured ...
Mac: new
... How to send the mail from one station to another. Decision maker on this lever doesn’t consider the physical layer specifics such as what kind of car, road condition, car speed. Use Google Map to figure out the direction Traffic Lights Damage control (car incidence) ...
... How to send the mail from one station to another. Decision maker on this lever doesn’t consider the physical layer specifics such as what kind of car, road condition, car speed. Use Google Map to figure out the direction Traffic Lights Damage control (car incidence) ...
Intro to UDP and TCP
... No initial connection setup overhead No connection state Small packet header overhead Finer application-level control ...
... No initial connection setup overhead No connection state Small packet header overhead Finer application-level control ...
Data Link Layer
... Starting and ending flags with bit stuffing; Physical Layer coding violations ...
... Starting and ending flags with bit stuffing; Physical Layer coding violations ...
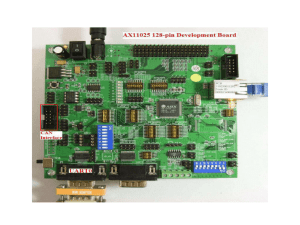
glossary - Homework Market
... A device is a unit of physical hardware or equipment that provides one or more computing functions within a computer system. It can provide input to the computer, accept output or both. A device can be any electronic element with some computing ability that supports the installation of firmware or t ...
... A device is a unit of physical hardware or equipment that provides one or more computing functions within a computer system. It can provide input to the computer, accept output or both. A device can be any electronic element with some computing ability that supports the installation of firmware or t ...
Protocols - Teach ICT
... protocols and access protocols. • LAN protocols refer to network operating systems. Access protocols determine how an attached device communicates with the network transmission medium (often cabling). ...
... protocols and access protocols. • LAN protocols refer to network operating systems. Access protocols determine how an attached device communicates with the network transmission medium (often cabling). ...
投影片 1
... when received data doesn’t match what was sent. Flow-control information helps the sender determine when the receiver is ready for more data. And a value that identifies an application-level port, or process, can help in routing received data to the correct process in the application layer. TCP pe ...
... when received data doesn’t match what was sent. Flow-control information helps the sender determine when the receiver is ready for more data. And a value that identifies an application-level port, or process, can help in routing received data to the correct process in the application layer. TCP pe ...
Chapter 2 - William Stallings, Data and Computer
... data exchange can involve complex procedures. better if task broken into subtasks implemented separately in layers in stack each layer provides functions needed to perform functions for layers above using functions provided by layers below layers communicate using a set of rules known as a proto ...
... data exchange can involve complex procedures. better if task broken into subtasks implemented separately in layers in stack each layer provides functions needed to perform functions for layers above using functions provided by layers below layers communicate using a set of rules known as a proto ...