Security policy design with IPSec
... Network security design can be compared to the design of software, and many of the principles that have been developed and used over the years can be used (Porto and De Geus 2003:1). It is unfortunate that many software products are developed using what might be termed a ‘build and fix’ model. This ...
... Network security design can be compared to the design of software, and many of the principles that have been developed and used over the years can be used (Porto and De Geus 2003:1). It is unfortunate that many software products are developed using what might be termed a ‘build and fix’ model. This ...
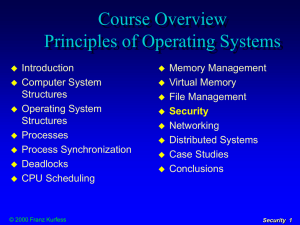
Introduction to Information Security Chapter N
... table which tracks the state and context of each packet in the conversation by recording which station sent what packet and when If the stateful firewall receives an incoming packet that it cannot match in its state table, then it defaults to its ACL to determine whether to allow the packet to pas ...
... table which tracks the state and context of each packet in the conversation by recording which station sent what packet and when If the stateful firewall receives an incoming packet that it cannot match in its state table, then it defaults to its ACL to determine whether to allow the packet to pas ...
Slide 1
... Survey” - %95 of the correspondents experienced more than 10 web site incidents in 2005 ...
... Survey” - %95 of the correspondents experienced more than 10 web site incidents in 2005 ...
- Learn Group
... This course uses a number of terms and concepts that are essential to any discussion of information security. Access: A subject or object’s ability to use, manipulate, modify, or affect another subject or object. Authorized users have legal access to a system, whereas hackers have illegal access to ...
... This course uses a number of terms and concepts that are essential to any discussion of information security. Access: A subject or object’s ability to use, manipulate, modify, or affect another subject or object. Authorized users have legal access to a system, whereas hackers have illegal access to ...
Network Flow Analysis in Information Security Strategy
... This material has been approved for public release and unlimited distribution except as restricted below. This material may be reproduced in its entirety, without modification, and freely distributed in written or electronic form without requesting formal permission. Permission is required for any o ...
... This material has been approved for public release and unlimited distribution except as restricted below. This material may be reproduced in its entirety, without modification, and freely distributed in written or electronic form without requesting formal permission. Permission is required for any o ...
Computer Network Security Protocols and Standards
... – IPSec is a suite of authentication and encryption protocols developed by the Internet Engineering Task Force (IETF) and designed to address the inherent lack of security for IP-based networks. – IPSec, has a very complex set of protocols described in a number of RFCs including RFC 2401 and 2411. – ...
... – IPSec is a suite of authentication and encryption protocols developed by the Internet Engineering Task Force (IETF) and designed to address the inherent lack of security for IP-based networks. – IPSec, has a very complex set of protocols described in a number of RFCs including RFC 2401 and 2411. – ...
Common Endpoint Locator Pools (CELP)
... degrees of of security security concern concern about about weakest weakest participant participant affects affects entire entire service service Maintaining Maintaining synchrony synchrony among among different different modifiers modifiers of of pool pool ...
... degrees of of security security concern concern about about weakest weakest participant participant affects affects entire entire service service Maintaining Maintaining synchrony synchrony among among different different modifiers modifiers of of pool pool ...
Chapter 1
... Forces of nature, force majeure, or acts of God are dangerous because they are unexpected and can occur with very little warning Can disrupt not only the lives of individuals, but also the storage, transmission, and use of information Include fire, flood, earthquake, and lightning as well as e ...
... Forces of nature, force majeure, or acts of God are dangerous because they are unexpected and can occur with very little warning Can disrupt not only the lives of individuals, but also the storage, transmission, and use of information Include fire, flood, earthquake, and lightning as well as e ...
IPSEC Presentation
... • A collection of protocols for securing Internet Protocol (IP) communications by encrypting and authenticating all IP packets1 • Progressive standard • Defined in RFC 2401 thru 2409 • Purpose: – To protect IP packets – To provide defense against network attacks 1: From wikipedia.org ...
... • A collection of protocols for securing Internet Protocol (IP) communications by encrypting and authenticating all IP packets1 • Progressive standard • Defined in RFC 2401 thru 2409 • Purpose: – To protect IP packets – To provide defense against network attacks 1: From wikipedia.org ...
High Assurance MLS File Service - Center for Computer Systems
... release packets to interfaces with sensitivity matching their sealed labels. The seal is a Message Authentication Code (MAC) created by using the Cipher-BlockChaining (CBC) mode of a symmetric encryption operation. Packet contents and the canonical representation of the source network sensitivity le ...
... release packets to interfaces with sensitivity matching their sealed labels. The seal is a Message Authentication Code (MAC) created by using the Cipher-BlockChaining (CBC) mode of a symmetric encryption operation. Packet contents and the canonical representation of the source network sensitivity le ...
Chap 6: Web Security - IUP Personal Websites
... • Recent versions of Windows allow filenames to contain up to 256 characters • To maintain backward compatibility with DOS, Windows automatically creates an 83 “alias” filename for every long filename Security+ Guide to Network Security Fundamentals, 2e ...
... • Recent versions of Windows allow filenames to contain up to 256 characters • To maintain backward compatibility with DOS, Windows automatically creates an 83 “alias” filename for every long filename Security+ Guide to Network Security Fundamentals, 2e ...
XML: Part - Houston Community College System
... • Recent versions of Windows allow filenames to contain up to 256 characters • To maintain backward compatibility with DOS, Windows automatically creates an 83 “alias” filename for every long filename Security+ Guide to Network Security Fundamentals, 2e ...
... • Recent versions of Windows allow filenames to contain up to 256 characters • To maintain backward compatibility with DOS, Windows automatically creates an 83 “alias” filename for every long filename Security+ Guide to Network Security Fundamentals, 2e ...
Review Techniques
... and assess technical vulnerabilities, which helps organizations to understand and improve the security posture of their systems and networks. Security testing is required by FISMA and other regulations. ...
... and assess technical vulnerabilities, which helps organizations to understand and improve the security posture of their systems and networks. Security testing is required by FISMA and other regulations. ...
Integrate and Accelerate Endpoint Threat Defense
... It’s time for a more integrated and automated security framework. With McAfee® Dynamic Endpoint Threat Defense from Intel® Security, organizations can combat emerging threats, defeat the unknown, and radically simplify security operations. McAfee Dynamic Endpoint Threat Defense integrates multiple l ...
... It’s time for a more integrated and automated security framework. With McAfee® Dynamic Endpoint Threat Defense from Intel® Security, organizations can combat emerging threats, defeat the unknown, and radically simplify security operations. McAfee Dynamic Endpoint Threat Defense integrates multiple l ...
Computer Security And The Law: What You Can Do To Protect
... Federal Computer Systems.” [11] This law basically requires every government computer system that contains sensitive information to establish a security plan and provide periodic mandatory training for all persons who manage, operate, or use these systems. This law also identifies NIST (originally t ...
... Federal Computer Systems.” [11] This law basically requires every government computer system that contains sensitive information to establish a security plan and provide periodic mandatory training for all persons who manage, operate, or use these systems. This law also identifies NIST (originally t ...
in the form of a new interim recommendation
... Leaders need to compensate for the natural inertial pressure of large organizations to proliferate barriers and processes by constantly repeating a mantra of simplification New Recommendation Interim Recommendation 12: Establish Global and Secure Repository for Data Collection, Sharing, and Analys ...
... Leaders need to compensate for the natural inertial pressure of large organizations to proliferate barriers and processes by constantly repeating a mantra of simplification New Recommendation Interim Recommendation 12: Establish Global and Secure Repository for Data Collection, Sharing, and Analys ...
Security+ Guide to Network Security Fundamentals, Third Edition
... Summary (continued) • The main goals of information security are to prevent data theft, thwart identity theft, avoid the legal consequences of not securing information, maintain productivity, and foil cyberterrorism • The types of people behind computer attacks are generally divided into several ca ...
... Summary (continued) • The main goals of information security are to prevent data theft, thwart identity theft, avoid the legal consequences of not securing information, maintain productivity, and foil cyberterrorism • The types of people behind computer attacks are generally divided into several ca ...
PPT_ch01 - Mercer University Computer Science Department
... Summary (continued) • The main goals of information security are to prevent data theft, thwart identity theft, avoid the legal consequences of not securing information, maintain productivity, and foil cyberterrorism • The types of people behind computer attacks are generally divided into several ca ...
... Summary (continued) • The main goals of information security are to prevent data theft, thwart identity theft, avoid the legal consequences of not securing information, maintain productivity, and foil cyberterrorism • The types of people behind computer attacks are generally divided into several ca ...
Caldicott - Acute Trusts Knowledge base
... Unauthorised access to data. Unauthorised access is possible in a number of ways. Users may leave their equipment or media containing data unattended in a place where it may be seen or used by unauthorised individuals. The use of a clear screen and desk policy, together with user training, can help ...
... Unauthorised access to data. Unauthorised access is possible in a number of ways. Users may leave their equipment or media containing data unattended in a place where it may be seen or used by unauthorised individuals. The use of a clear screen and desk policy, together with user training, can help ...
D1S1_TSV404_Course_Intro_2011_v1
... ■ Exploitation of the technical or procedural vulnerability will significantly impact the confidentiality, integrity, and/or availability of the system, application, or data ■ Exploitation of the vulnerability may cause moderate financial loss or public embarrassment ■ The threat exposure is moderat ...
... ■ Exploitation of the technical or procedural vulnerability will significantly impact the confidentiality, integrity, and/or availability of the system, application, or data ■ Exploitation of the vulnerability may cause moderate financial loss or public embarrassment ■ The threat exposure is moderat ...
The Guidelines on Cyber Security onboard Ships - ics
... threats that may realistically be faced. This should be followed by an assessment of the systems and procedures on board, in order to map their robustness to handle the current level of threat. These vulnerability assessments should then serve as the foundation for a senior management level discussi ...
... threats that may realistically be faced. This should be followed by an assessment of the systems and procedures on board, in order to map their robustness to handle the current level of threat. These vulnerability assessments should then serve as the foundation for a senior management level discussi ...
What is Trusted Computing and Digital Rights Management
... today. TC hardware can be useful to governments by guaranteeing that their machines have not been tampered with or to prevent unauthorised access to stolen machines. Digital Rights Management (DRM) software provides a way for information providers to control access to information while making it ava ...
... today. TC hardware can be useful to governments by guaranteeing that their machines have not been tampered with or to prevent unauthorised access to stolen machines. Digital Rights Management (DRM) software provides a way for information providers to control access to information while making it ava ...