Guidelines on Cyber Security onboard ships
... threats that may realistically be faced. This should be followed by an assessment of the systems and procedures on board, in order to map their robustness to handle the current level of threat. These vulnerability assessments should then serve as the foundation for a senior management level discussi ...
... threats that may realistically be faced. This should be followed by an assessment of the systems and procedures on board, in order to map their robustness to handle the current level of threat. These vulnerability assessments should then serve as the foundation for a senior management level discussi ...
Security
... • Security refers to the overall security problem. • Protection mechanisms refers to the specific operating system mechanisms used to safeguard information in the computer. • Threats to computer systems: – Data confidentiality is concerned with having secret data remain secret. – Data integrity mean ...
... • Security refers to the overall security problem. • Protection mechanisms refers to the specific operating system mechanisms used to safeguard information in the computer. • Threats to computer systems: – Data confidentiality is concerned with having secret data remain secret. – Data integrity mean ...
Public Presentation - Academic Conferences
... “you can exfiltrate massive amounts of information electronically from the comfort of your own office.” – Joel Brenner, counterintelligence executive in CNN.com, October 19, 2007 ...
... “you can exfiltrate massive amounts of information electronically from the comfort of your own office.” – Joel Brenner, counterintelligence executive in CNN.com, October 19, 2007 ...
Joint Information Environment (JIE)
... - Scalability and flexibility to provide new services - Use of common standards and operational techniques - Transition to a single security architecture • The DOD plans to achieve these goals via the following interrelated initiatives: - Implementation of Joint Regional Security Stack (JRSS) h ...
... - Scalability and flexibility to provide new services - Use of common standards and operational techniques - Transition to a single security architecture • The DOD plans to achieve these goals via the following interrelated initiatives: - Implementation of Joint Regional Security Stack (JRSS) h ...
Availability Confidentiality Integrity
... Fail gracefully without exposing assets Balance usability with security Log actions of users and applications Reduce risks with redundancy and ...
... Fail gracefully without exposing assets Balance usability with security Log actions of users and applications Reduce risks with redundancy and ...
Hackers and Attackers
... – Use a variety of techniques, technical, social engineering, and phishing to gain access – Want user or customer data, company secrets – Loss is potentially more severe • Direct loss of assets and loss from law suites ...
... – Use a variety of techniques, technical, social engineering, and phishing to gain access – Want user or customer data, company secrets – Loss is potentially more severe • Direct loss of assets and loss from law suites ...
e-Security extra notes
... public Internet to carry information but remains private Encryption—scramble communications Authentication—ensure information remains untampered with and comes from legitimate source Access control—verify identity of anyone using network Prentice Hall, 2002 ...
... public Internet to carry information but remains private Encryption—scramble communications Authentication—ensure information remains untampered with and comes from legitimate source Access control—verify identity of anyone using network Prentice Hall, 2002 ...
Five Business Takeaways from Gartner`s “Web
... Unlike traditional firewalls, NGFWs are able to recognize what applications are communicating on your network. NGFW vendors call this “application awareness,” which is the source of the confusion. Application awareness is irrelevant for preventing attacks on your web applications—exactly the thing a ...
... Unlike traditional firewalls, NGFWs are able to recognize what applications are communicating on your network. NGFW vendors call this “application awareness,” which is the source of the confusion. Application awareness is irrelevant for preventing attacks on your web applications—exactly the thing a ...
Slide 1
... to its intended users. • motives for, and targets of a DoS attack may vary • generally consists of the concerted efforts of a person or people to prevent an Internet site or service from functioning efficiently or at all, temporarily or indefinitely. • perpetrators of DoS attacks typically target si ...
... to its intended users. • motives for, and targets of a DoS attack may vary • generally consists of the concerted efforts of a person or people to prevent an Internet site or service from functioning efficiently or at all, temporarily or indefinitely. • perpetrators of DoS attacks typically target si ...
Fraudulent Emails, Websites and Phishing Variations Fraudulent
... Phishing is usually a two-part scam involving emails and spoof websites. Fraudsters, also known as phishers, send an email to a wide audience that appears to come from a reputable company. This is known as a phish email. In the phish email, there are links to spoof websites that imitate a reputable ...
... Phishing is usually a two-part scam involving emails and spoof websites. Fraudsters, also known as phishers, send an email to a wide audience that appears to come from a reputable company. This is known as a phish email. In the phish email, there are links to spoof websites that imitate a reputable ...
Web Security Security+ Guide to Network Security Fundamentals
... server stores that information in a file on the local computer • Attackers often target cookies because they can contain sensitive information (usernames and other private information) Security+ Guide to Network Security Fundamentals, 2e ...
... server stores that information in a file on the local computer • Attackers often target cookies because they can contain sensitive information (usernames and other private information) Security+ Guide to Network Security Fundamentals, 2e ...
Securing IT Assets with Linux
... • Security should be a concern in every situation. Whether you’re building a network for a small trucking firm or working for NASDAQ as a financial advisor. • The Internet is a vast system of information with varying degrees of confidentiality; it is inviting to criminal activity because users may b ...
... • Security should be a concern in every situation. Whether you’re building a network for a small trucking firm or working for NASDAQ as a financial advisor. • The Internet is a vast system of information with varying degrees of confidentiality; it is inviting to criminal activity because users may b ...
6 - Kuroski
... Circuit Gateways Circuit gateway firewall operates at transport layer Like filtering firewalls, do not usually look at data traffic flowing between two networks, but prevent direct connections between one network and another Accomplished by creating tunnels connecting specific processes or sy ...
... Circuit Gateways Circuit gateway firewall operates at transport layer Like filtering firewalls, do not usually look at data traffic flowing between two networks, but prevent direct connections between one network and another Accomplished by creating tunnels connecting specific processes or sy ...
The Role of People in Security
... Overview of Baselines • The process of establishing a system’s security state is called baselining. • The resulting product is a security baseline that allows the system to run safely and securely. • Once the process has been completed, any similar systems can be configured with the same baseline to ...
... Overview of Baselines • The process of establishing a system’s security state is called baselining. • The resulting product is a security baseline that allows the system to run safely and securely. • Once the process has been completed, any similar systems can be configured with the same baseline to ...
Making your Enterprise Cyber Resilient
... So-called “penetration testing” has become one way to proactively identify weaknesses in a firm’s cyber defense structures. We believe firms need to go beyond executing prepared scripts and move to advanced adversary impersonation. Inside and/or outside groups are hired or assigned to attempt to bre ...
... So-called “penetration testing” has become one way to proactively identify weaknesses in a firm’s cyber defense structures. We believe firms need to go beyond executing prepared scripts and move to advanced adversary impersonation. Inside and/or outside groups are hired or assigned to attempt to bre ...
SAQ D Compliance Scott St. Aubin Senior Security Consultant QSA, CISM, CISSP
... – E.g. e-mail, IM, chat – Effective solutions may differ, depending on the number of individuals impacted • Small org – policy may be sufficient • Large org – policy and technology may be necessary for enforcability ...
... – E.g. e-mail, IM, chat – Effective solutions may differ, depending on the number of individuals impacted • Small org – policy may be sufficient • Large org – policy and technology may be necessary for enforcability ...
Slide 1
... RBAC uses the role to identify the users who have permissions to a resource, and may be implemented system wide. Users may be able to access information from any station in the network, based strictly on their role. Privileges would be limited to the role and wouldn’t be present during the ...
... RBAC uses the role to identify the users who have permissions to a resource, and may be implemented system wide. Users may be able to access information from any station in the network, based strictly on their role. Privileges would be limited to the role and wouldn’t be present during the ...
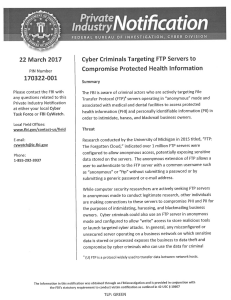
Notification
... submitting a generic password ore-mail address. While computer security researchers are actively seeking FTP servers i n anonymous mode to conduct legitimate research, other individuals are making connections to these servers to compromise PHI and PII for the purposes of intimidating, harassing, and ...
... submitting a generic password ore-mail address. While computer security researchers are actively seeking FTP servers i n anonymous mode to conduct legitimate research, other individuals are making connections to these servers to compromise PHI and PII for the purposes of intimidating, harassing, and ...
Guide to Operating System Security
... Programs that replicate on the same computer or send themselves to many other computers Can open a back door ...
... Programs that replicate on the same computer or send themselves to many other computers Can open a back door ...
Risk Mgmt - WCU Computer Science
... information system and the POTENTIAL IMPACT the loss of information or capabilities of a system would have. The resulting analysis is used as a basis for identifying appropriate and cost-effective counter-measures. (Definition from National Information Systems Security (INFOSEC) Glossary, NSTISSI No ...
... information system and the POTENTIAL IMPACT the loss of information or capabilities of a system would have. The resulting analysis is used as a basis for identifying appropriate and cost-effective counter-measures. (Definition from National Information Systems Security (INFOSEC) Glossary, NSTISSI No ...
The wild world of malware: Keeping your
... Threats are continuously evolving but your firewall protection may not. Now is the time to look beyond traditional network security and incorporate protection against malware and exploits that pass through PCs and mobile devices when users browse the Internet, send or receive email and download appl ...
... Threats are continuously evolving but your firewall protection may not. Now is the time to look beyond traditional network security and incorporate protection against malware and exploits that pass through PCs and mobile devices when users browse the Internet, send or receive email and download appl ...
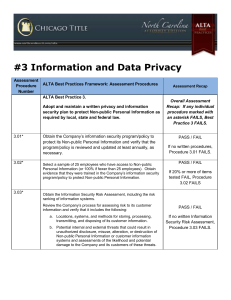
ALTA Assessment Procedures
... Obtain and review written policies and procedures to verify logical access to information systems (i.e., network, data base, and application layers) containing Non-public Personal Information is restricted to authorized persons only. a. For the sample of employees tested in Assessment Procedure 3.02 ...
... Obtain and review written policies and procedures to verify logical access to information systems (i.e., network, data base, and application layers) containing Non-public Personal Information is restricted to authorized persons only. a. For the sample of employees tested in Assessment Procedure 3.02 ...
Chapter 5 Protection of Information Assets
... information associated with business processes • Document the collection, use, disclosure and destruction of personally identifiable information • Ensure that accountability for privacy issues exists • Be the foundation for informed policy, operations and system design decisions based on an understa ...
... information associated with business processes • Document the collection, use, disclosure and destruction of personally identifiable information • Ensure that accountability for privacy issues exists • Be the foundation for informed policy, operations and system design decisions based on an understa ...
Access Control Policies
... not able to decide which other entities they want to allow to access resources, the system rules apply the system denies users full control over access to the resources they create ...
... not able to decide which other entities they want to allow to access resources, the system rules apply the system denies users full control over access to the resources they create ...