Chapter 4
... • A hostid of 0 (all zeroes) is not assigned to an individual host, it indicates the network itself • A hostid of all ones is a broadcast address and refers to all hosts on the network (ones means all) • When a packet is broadcast: – a receiving router looks at the netid portion of the address to pa ...
... • A hostid of 0 (all zeroes) is not assigned to an individual host, it indicates the network itself • A hostid of all ones is a broadcast address and refers to all hosts on the network (ones means all) • When a packet is broadcast: – a receiving router looks at the netid portion of the address to pa ...
Routing
... specifying to which router a message that does not match any prefix should be forwarded to. Usually a gateway to other networks, e.g., the Internet. ...
... specifying to which router a message that does not match any prefix should be forwarded to. Usually a gateway to other networks, e.g., the Internet. ...
Wide Area Network Infrastructure IT 10
... IEEE - the Institute of Electrical and Electronics Engineers is one of the leading standardsmaking organizations in the world. IEEE standards adhered to by equipment manufacturers, affect a wide range of industries including Information Technology (IT) and Transportation. The IEEE 802 LAN/MAN group ...
... IEEE - the Institute of Electrical and Electronics Engineers is one of the leading standardsmaking organizations in the world. IEEE standards adhered to by equipment manufacturers, affect a wide range of industries including Information Technology (IT) and Transportation. The IEEE 802 LAN/MAN group ...
Network Control and Management in the 100x100 Architecture
... Example: OSPF and BGP are complex systems in its own right, they are components in a routing system of a network, interacting with each other and packet filters, interacting with management tools … ...
... Example: OSPF and BGP are complex systems in its own right, they are components in a routing system of a network, interacting with each other and packet filters, interacting with management tools … ...
05. Example Networks..
... • The Internet is not a network at all, but a vast collection of different networks that use certain common protocols and provide certain common services. It is an unusual system in that it was not planned by anyone and is not controlled by anyone • ARPHANET - the DoD wanted a command-and-control ne ...
... • The Internet is not a network at all, but a vast collection of different networks that use certain common protocols and provide certain common services. It is an unusual system in that it was not planned by anyone and is not controlled by anyone • ARPHANET - the DoD wanted a command-and-control ne ...
Intro to UDP and TCP
... Rethinking the design of the Internet: The end to end arguments vs. the brave new world ...
... Rethinking the design of the Internet: The end to end arguments vs. the brave new world ...
Network Planning Technical Sub
... being considered for replacing current equipment. Users are demanding more capabilities and more interoperability and Codian appears to meet these needs. NDIVN is considering a couple of different types of services. Rather than just scheduling rooms for video sessions, people may be able to reserve ...
... being considered for replacing current equipment. Users are demanding more capabilities and more interoperability and Codian appears to meet these needs. NDIVN is considering a couple of different types of services. Rather than just scheduling rooms for video sessions, people may be able to reserve ...
2.2 MANET Features - School of Information Technology, IIT kharagpur
... AODV is the routing algorithm specially designed for ad hoc networks. It is the distant relative of the Bellman-Ford distance vector algorithm but adapted to work in a mobile environment. It takes into account the limited bandwidth and low battery life of the mobile nodes found in the ad hoc environ ...
... AODV is the routing algorithm specially designed for ad hoc networks. It is the distant relative of the Bellman-Ford distance vector algorithm but adapted to work in a mobile environment. It takes into account the limited bandwidth and low battery life of the mobile nodes found in the ad hoc environ ...
msb201073-sup
... (http://www.cytoscape.org/) which allows the import of SBML files (Level 2 Version 1) which was exported from CellDesigner 4.0.1 version of the maps. In order to compute the network properties, the Cytoscape plugin NetworkAnalyzer 2.6.1 (http://med.bioinf.mpiinf.mpg.de/netanalyzer/) were employed w ...
... (http://www.cytoscape.org/) which allows the import of SBML files (Level 2 Version 1) which was exported from CellDesigner 4.0.1 version of the maps. In order to compute the network properties, the Cytoscape plugin NetworkAnalyzer 2.6.1 (http://med.bioinf.mpiinf.mpg.de/netanalyzer/) were employed w ...
Chapter 6
... Telecommunications – the exchange of information in any form over a network Industry Trends – massively changed from government regulated monopolies to a fiercely competitive markets with many choices Business Application Trends – all these changes have caused significant changes in the businesse ...
... Telecommunications – the exchange of information in any form over a network Industry Trends – massively changed from government regulated monopolies to a fiercely competitive markets with many choices Business Application Trends – all these changes have caused significant changes in the businesse ...
chapter 6 – network requirements
... Health Choice Integrated Care must design, establish and maintain a network that covers, at a minimum ...
... Health Choice Integrated Care must design, establish and maintain a network that covers, at a minimum ...
Napster & Gnutella
... • Peers check to see if they have matches & respond (if they have any matches) & send packet to connected peers • Continues for TTL Step 3: Downloading • Peers respond with a “QueryHit” (contains contact info) • File transfers use direct connection using HTTP protocol’s GET method • When there is a ...
... • Peers check to see if they have matches & respond (if they have any matches) & send packet to connected peers • Continues for TTL Step 3: Downloading • Peers respond with a “QueryHit” (contains contact info) • File transfers use direct connection using HTTP protocol’s GET method • When there is a ...
COE 308: Computer Architecture (T032) Dr. Marwan Abu
... Circuit switching is used in the public telephone network for voice communication. Dedicated path is established for the duration of the call (session) Switching and transmission resources are committed for exclusive use of the call throughout its duration OK with telephony, as people keep talking t ...
... Circuit switching is used in the public telephone network for voice communication. Dedicated path is established for the duration of the call (session) Switching and transmission resources are committed for exclusive use of the call throughout its duration OK with telephony, as people keep talking t ...
Server-Based Networks
... “linked” together in order and they can share resources ( e.g. data, printers or CD-ROMs), exchange files, and allow electronic communication. Networking arose from the need to share data in a timely fashion. The computers on the network may be connect through cables, telephone lines, radio waves, s ...
... “linked” together in order and they can share resources ( e.g. data, printers or CD-ROMs), exchange files, and allow electronic communication. Networking arose from the need to share data in a timely fashion. The computers on the network may be connect through cables, telephone lines, radio waves, s ...
Document
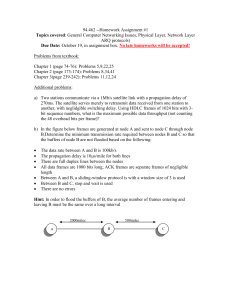
... a) Two stations communicate via a 1Mb/s satellite link with a propagation delay of 270ms. The satellite serves merely to retransmit data received from one station to another, with neglidgible switching delay. Using HDLC frames of 1024 bits with 3bit sequence numbers, what is the maximum possible dat ...
... a) Two stations communicate via a 1Mb/s satellite link with a propagation delay of 270ms. The satellite serves merely to retransmit data received from one station to another, with neglidgible switching delay. Using HDLC frames of 1024 bits with 3bit sequence numbers, what is the maximum possible dat ...
Security Fundamentals
... Secure topologies • Goal is to separate network traffic so that no network segment carries traffic not required on the segment • Performance will also be more efficient • Security zones: – Areas of the network that contain resources with similar security requirements – Group computers and devices a ...
... Secure topologies • Goal is to separate network traffic so that no network segment carries traffic not required on the segment • Performance will also be more efficient • Security zones: – Areas of the network that contain resources with similar security requirements – Group computers and devices a ...
The Impact of SDN On MPLS Networks
... • Micro-management of forwarding decisions • Control of end-to-end paths • Whole-sale operation of network ...
... • Micro-management of forwarding decisions • Control of end-to-end paths • Whole-sale operation of network ...
Fragmentation and IP Forwarding
... length fragment 16-bit identifier flgs offset time to upper header layer live checksum ...
... length fragment 16-bit identifier flgs offset time to upper header layer live checksum ...
Comp 100 Lecture Notes Chapter 7
... Other Devices – check the network adapter card Network–Ready Devices network adapter cards inside connect directly to the router o printers o game consoles o blu-ray players o television sets o home-security systems NAS Devices, i.e., Network–Attached Storage Devices LinkStation Series from ...
... Other Devices – check the network adapter card Network–Ready Devices network adapter cards inside connect directly to the router o printers o game consoles o blu-ray players o television sets o home-security systems NAS Devices, i.e., Network–Attached Storage Devices LinkStation Series from ...
Slide 1
... Network planning – topology /nodes/links Network deployment- to install equipment Network maintenance and planning – perform software and hardware upgrade Workforce management Inventory management Order management – take order from ...
... Network planning – topology /nodes/links Network deployment- to install equipment Network maintenance and planning – perform software and hardware upgrade Workforce management Inventory management Order management – take order from ...
IETF 報告 UDLR-WG
... • Network Broadcast Address – Host Address part’s all bit are 1 192.168.1.255 / netmask 255.255.255.0 ...
... • Network Broadcast Address – Host Address part’s all bit are 1 192.168.1.255 / netmask 255.255.255.0 ...
Lec 1
... • Physical layer devices • Carries out some network management functions – if an adaptor malfunctions and floods the Ethernet it can internally disconnect the link – collects some statistics • Extends the length of the LAN as each link has a discrete ...
... • Physical layer devices • Carries out some network management functions – if an adaptor malfunctions and floods the Ethernet it can internally disconnect the link – collects some statistics • Extends the length of the LAN as each link has a discrete ...