* Your assessment is very important for improving the work of artificial intelligence, which forms the content of this project
Download Fragmentation and IP Forwarding
TCP congestion control wikipedia , lookup
Distributed firewall wikipedia , lookup
IEEE 802.1aq wikipedia , lookup
Point-to-Point Protocol over Ethernet wikipedia , lookup
Piggybacking (Internet access) wikipedia , lookup
Computer network wikipedia , lookup
Network tap wikipedia , lookup
Multiprotocol Label Switching wikipedia , lookup
Asynchronous Transfer Mode wikipedia , lookup
Deep packet inspection wikipedia , lookup
Airborne Networking wikipedia , lookup
Internet protocol suite wikipedia , lookup
Zero-configuration networking wikipedia , lookup
Wake-on-LAN wikipedia , lookup
Packet switching wikipedia , lookup
Recursive InterNetwork Architecture (RINA) wikipedia , lookup
Cracking of wireless networks wikipedia , lookup
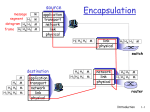
Discussion Monday (11-3-2014) IP protocol version number header length (bytes) “type” of data max number remaining hops (decremented at each router) upper layer protocol to deliver payload to how much overhead with TCP? 20 bytes of TCP 20 bytes of IP = 40 bytes + app layer overhead 32 bits type of ver head. len service length fragment 16-bit identifier flgs offset time to upper header layer live checksum total datagram length (bytes) for fragmentation/ reassembly 32 bit source IP address 32 bit destination IP address Options (if any) data (variable length, typically a TCP or UDP segment) E.g. timestamp, record route taken, specify list of routers to visit. network links have MTU (max.transfer size) - largest possible link-level frame. different link types, different MTUs fragmentation: in: one large datagram out: 3 smaller datagrams large IP datagram divided (“fragmented”) within net one datagram becomes several datagrams “reassembled” only at final destination IP header bits used to identify, order related fragments reassembly Example 4000 byte datagram MTU = 1500 bytes length ID =4000 =x MF =0 offset =0 One large datagram becomes several smaller datagrams 1480 bytes in data field offset = 1480 length = 3980(total data)-1480-1480+20(Header) offset = 1480+1480 length ID =1500 =x MF =1 offset =0 length ID =1500 =x MF =1 offset =1480 length ID =1040 =x MF =0 offset =2960 Classless Inter-Domain Routing (1993) Networks described by variable-length prefix Allows arbitrary allocation between network and host address Forwarding table contains: List of network names and next hop routers Local networks have entries specifying which interface Link-local hosts can be delivered with Layer-2 forwarding Longest prefix matching IP Address Netmask Next hop Interface 0.0.0.0/0 0.0.0.0 5.10.1.1 eth0 12.1.0.0/16 255.255.0.0 12.1.0.1 eth1 12.1.1.0/24 255.255.255.0 12.1.1.1 eth2 12.1.1.200/32 255.255.255.255 12.1.1.200 What is the longest prefix matching for: 1. 12.1.1.200 ---- 2. 12.1.0.20 ---- 3. 128.12.92.53 ---- eth3 Consider sending a 2100 byte datagram over a link with MTU of 700 bytes. How many fragments will be generated ? IP forwarding. Consider the network diagram below. Each router (a square in the figure) is labeled with the names of its interfaces (e.g., eth0) and the IP addresses assigned to each. Each network (a circle) is labeled with its network name and prefix length. A 192.168.128/17 B 192.168.128.1 192.168.16.1 eth0 10.0.1.2 eth3 R1 192.168.16/21 eth0 10.0.2.2 eth1 eth3 10.0.2.1 eth2 R2 eth1 192.168.8.1 C eth2 192.168.7.2 10.0.3.1 192.168.8/22 10.0.3.2 eth0 D 192.168.7.1 eth3 R3 eth1 192.168.4.1 E eth2 192.168.6.1 192.168.7/24 F 192.168.6/24 192.168.4/23 Continued The machine I’m typing this on has an IP address 192.168.9.12. To which of the networks above am I connected? What is the subnet mask my machine should use? What is the most concise CIDR block R2 can use to describe the networks reachable through R3? Suppose R1 and R3 contain the following forwarding tables, on the next slide: What path would a packet from my machine follow to a host on network F? Explain how the packet is forwarded by showing the rows in each forwarding table that would be invoked. If the packet is forwarded by R2, please list the forwarding table entries in R2’s table that would be used.?