Universal WiFi Range Extender WN3000RP
... wireless device) to its wireless network. 3. Within 2 minutes, press the WPS button on your wireless device, or follow the WPS instructions that came with your wireless device. Your wireless device is now connected to the Extender. To log in to the Extender and use WPS to connect: 1. From the Extend ...
... wireless device) to its wireless network. 3. Within 2 minutes, press the WPS button on your wireless device, or follow the WPS instructions that came with your wireless device. Your wireless device is now connected to the Extender. To log in to the Extender and use WPS to connect: 1. From the Extend ...
OpenFlow1.3 GUI Manual
... form a control plane, and their connections are represented in the graphical user interface (GUI) as grey lines, as shown in the diagram below. In addition, the data plane can be formed by connecting OpenFlow switches to other network devices, such as other OpenFlow switches or hosts. Data plane con ...
... form a control plane, and their connections are represented in the graphical user interface (GUI) as grey lines, as shown in the diagram below. In addition, the data plane can be formed by connecting OpenFlow switches to other network devices, such as other OpenFlow switches or hosts. Data plane con ...
BASrouters — BACnet Routing Examples
... BASrouters — BACnet Routing Examples The BACnet 135 standard defines a network layer allowing multiple BACnet networks to send and receive messages over a single BACnet internetwork without concern for different data links. Interconnecting two BACnet networks requires a BACnet router and Contemporar ...
... BASrouters — BACnet Routing Examples The BACnet 135 standard defines a network layer allowing multiple BACnet networks to send and receive messages over a single BACnet internetwork without concern for different data links. Interconnecting two BACnet networks requires a BACnet router and Contemporar ...
JNCIA Study Guide - Open Shortest Path First (OSPF)
... Init The Init state is reached when an OSPF router receives a hello packet but the local router ID is not listed in the received Neighbor field. This means that bidirectional communication has not been established between the peers. Attempt The Attempt state is valid only for Non-Broadcast Multi-Acc ...
... Init The Init state is reached when an OSPF router receives a hello packet but the local router ID is not listed in the received Neighbor field. This means that bidirectional communication has not been established between the peers. Attempt The Attempt state is valid only for Non-Broadcast Multi-Acc ...
Architectures and Algorithms for IPv4/IPv6
... algorithm. It is suitable to use in simulation as its behaviour tends to be closer to the behaviour of real networks since it does not overload unnecessarily some links more than others. It may also be used in machines where the computation of paths is Dijkstra based and situations of equal-cost rou ...
... algorithm. It is suitable to use in simulation as its behaviour tends to be closer to the behaviour of real networks since it does not overload unnecessarily some links more than others. It may also be used in machines where the computation of paths is Dijkstra based and situations of equal-cost rou ...
The History of nordunet
... project was to develop a communication protocol that would guide the transmission of data across different networks. The Transmission Control Protocol, tcp, was outlined in 1974 by darpa researchers, and in a few years, it was developed as the tcp/ip Protocol Suite. Later, tcp/ip would become the st ...
... project was to develop a communication protocol that would guide the transmission of data across different networks. The Transmission Control Protocol, tcp, was outlined in 1974 by darpa researchers, and in a few years, it was developed as the tcp/ip Protocol Suite. Later, tcp/ip would become the st ...
8.2 Interim Agreements on Key Issue #2: QoS
... Interim agreements for Key issue #2 QoS framework are as follows: 1 Support Reflective QoS over RAN under control of the network. The network decides on the QoS to apply on the DL traffic and the UE reflects the DL QoS to the associated UL traffic. When the UE receives a DL packet for which reflecti ...
... Interim agreements for Key issue #2 QoS framework are as follows: 1 Support Reflective QoS over RAN under control of the network. The network decides on the QoS to apply on the DL traffic and the UE reflects the DL QoS to the associated UL traffic. When the UE receives a DL packet for which reflecti ...
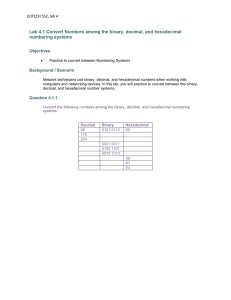
EDTECH 552, lab 4 Lab 4.1 Convert Numbers among the binary
... first 64 bits, or first four hextets, and the host portion, which is identified by the last 64 bits, or last four hextets. Remember that each number, or character, in an IPv6 address is written in hexadecimal, which is equivalent to four bits. The following is a typical global unicast address: The n ...
... first 64 bits, or first four hextets, and the host portion, which is identified by the last 64 bits, or last four hextets. Remember that each number, or character, in an IPv6 address is written in hexadecimal, which is equivalent to four bits. The following is a typical global unicast address: The n ...
Network Working Group G. Bernstein Request for
... (LSRs) connected via Label Switched Paths (LSPs). An LSP is unidirectional and could be of several different types such as pointto-point, point-to-multipoint, and multipoint-to-point. Border LSRs in an MPLS network act as either ingress or egress LSRs, depending on the direction of the traffic being ...
... (LSRs) connected via Label Switched Paths (LSPs). An LSP is unidirectional and could be of several different types such as pointto-point, point-to-multipoint, and multipoint-to-point. Border LSRs in an MPLS network act as either ingress or egress LSRs, depending on the direction of the traffic being ...
Chapter 1 - Introduction
... – Each datagram consists of a header followed by data area (payload) • The amount of data carried in a datagram is not fixed • The size of a datagram is determined by the application that sends data. • A datagram can contain as little as a single octet of data or at most 64K ...
... – Each datagram consists of a header followed by data area (payload) • The amount of data carried in a datagram is not fixed • The size of a datagram is determined by the application that sends data. • A datagram can contain as little as a single octet of data or at most 64K ...
Offset Time-Emulated Architecture for Optical Burst Switching - Modelling and Performance Evaluation
... issues when developing OBS networks. Another important aspect is routing problem, which concerns effective balancing of traffic load so that to reduce burst congestion at overloaded links. Accounting for these requirements, the design objectives for the E-OBS architecture are (i) feasibility of offs ...
... issues when developing OBS networks. Another important aspect is routing problem, which concerns effective balancing of traffic load so that to reduce burst congestion at overloaded links. Accounting for these requirements, the design objectives for the E-OBS architecture are (i) feasibility of offs ...
slides 3
... • Does the problem occur all the time, frequently, or rarely? • Does the problem occur for only a specific application, many applications, or only some applications? • Is the problem reproducible on other machines? ...
... • Does the problem occur all the time, frequently, or rarely? • Does the problem occur for only a specific application, many applications, or only some applications? • Is the problem reproducible on other machines? ...
The OAM Jigsaw Puzzle
... What about Passive Optical Network (PON) OAM? While PON is outside the focus of this paper, it should not go unmentioned. EPON and 10G-EPON provide link-level OAM using the IEEE 802.3ah Ethernet on the First Mile (EFM), while GPON and XG-PON use Physical Layer OAM (PLOAM), defined in the ITU-T PON s ...
... What about Passive Optical Network (PON) OAM? While PON is outside the focus of this paper, it should not go unmentioned. EPON and 10G-EPON provide link-level OAM using the IEEE 802.3ah Ethernet on the First Mile (EFM), while GPON and XG-PON use Physical Layer OAM (PLOAM), defined in the ITU-T PON s ...
International Technical Support Organization Asynchronous
... Copyright International Business Machines Corporation 1995. All rights reserved. Note to U.S. Government Users — Documentation related to restricted rights — Use, duplication or disclosure is subject to restrictions set forth in GSA ADP Schedule Contract with IBM Corp. ...
... Copyright International Business Machines Corporation 1995. All rights reserved. Note to U.S. Government Users — Documentation related to restricted rights — Use, duplication or disclosure is subject to restrictions set forth in GSA ADP Schedule Contract with IBM Corp. ...
VMware Virtual SAN Network Design Guide
... The Virtual SAN network is an integral part of an overall vSphere network configuration and therefore cannot work in isolation from other vSphere network services. Virtual SAN utilizes either VMware vSphere® Standard Switch (VSS) or VMware vSphere® Distributed Switch™ (VDS) to construct a dedicated ...
... The Virtual SAN network is an integral part of an overall vSphere network configuration and therefore cannot work in isolation from other vSphere network services. Virtual SAN utilizes either VMware vSphere® Standard Switch (VSS) or VMware vSphere® Distributed Switch™ (VDS) to construct a dedicated ...
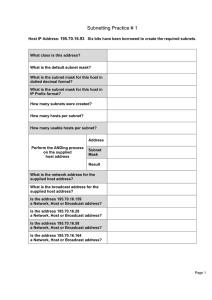
Subnetting Practice # 1
... You are the network administrator for Bunch-A-Hosts Limited in Windsor and are required to subnet the network according to the diagram. You have decided to use the network 172.16.0.0. There are multiple subnets at each site but you are only responsible for providing usable subnetworks with enough IP ...
... You are the network administrator for Bunch-A-Hosts Limited in Windsor and are required to subnet the network according to the diagram. You have decided to use the network 172.16.0.0. There are multiple subnets at each site but you are only responsible for providing usable subnetworks with enough IP ...
Single Packet IP Traceback in AS-level Partial Deployment Scenario
... AS-level) they are far away, and their respective STMs. The STM of each AS keeps track of those information. The STM of each AS is able to dispatch queries to other ASes’ STMs level-by-level. It first sends queries to its level-1 SPIE-deployed AS neighbors (adjacent ASes, 1-hop away from the current ...
... AS-level) they are far away, and their respective STMs. The STM of each AS keeps track of those information. The STM of each AS is able to dispatch queries to other ASes’ STMs level-by-level. It first sends queries to its level-1 SPIE-deployed AS neighbors (adjacent ASes, 1-hop away from the current ...
Sniffer University 1-3
... Connection management (e.g., TCP) Error and flow control Connectionless, unreliable (e.g., UDP) ...
... Connection management (e.g., TCP) Error and flow control Connectionless, unreliable (e.g., UDP) ...
third edition
... and to see the big picture of networking. It is our experience that both students and professionals learning about networks for the first time often have the impression that network protocols are some sort of edict handed down from on high, and that their job is to learn as many TLAs (three-letter a ...
... and to see the big picture of networking. It is our experience that both students and professionals learning about networks for the first time often have the impression that network protocols are some sort of edict handed down from on high, and that their job is to learn as many TLAs (three-letter a ...
Chapter 1 - Introduction
... • TCP/IP use the name IP datagram to refer to a packet • Figure 22.1 illustrates an IP datagram format – Each datagram consists of a header followed by data area (payload) • The amount of data carried in a datagram is not fixed • The size of a datagram is determined by the application that sends dat ...
... • TCP/IP use the name IP datagram to refer to a packet • Figure 22.1 illustrates an IP datagram format – Each datagram consists of a header followed by data area (payload) • The amount of data carried in a datagram is not fixed • The size of a datagram is determined by the application that sends dat ...
Chapter 1 - Introduction
... • TCP/IP uses the name IP datagram to refer to a packet • Figure 22.1 illustrates an IP datagram format – Each datagram consists of a header followed by data area (payload) • The amount of data carried in a datagram is not fixed • The size of a datagram is determined by the application that sends da ...
... • TCP/IP uses the name IP datagram to refer to a packet • Figure 22.1 illustrates an IP datagram format – Each datagram consists of a header followed by data area (payload) • The amount of data carried in a datagram is not fixed • The size of a datagram is determined by the application that sends da ...
Network Working Group G. Gross Request for
... structure described in "Multiprotocol Encapsulation over ATM Adaptation Layer 5" [4]. The purpose of this specification is not to document what is already standardized in [4], but to specify how the mechanisms described in [4] are to be used to map PPP onto a FUNI-based ATM network. Section 1 within ...
... structure described in "Multiprotocol Encapsulation over ATM Adaptation Layer 5" [4]. The purpose of this specification is not to document what is already standardized in [4], but to specify how the mechanisms described in [4] are to be used to map PPP onto a FUNI-based ATM network. Section 1 within ...
Chapter 7 - SaigonTech
... – How computers put data on the cable – How they ensure that the data reaches its destination undamaged ...
... – How computers put data on the cable – How they ensure that the data reaches its destination undamaged ...
Network Reference Model for cdma2000 Spread Spectrum
... choose any physical implementation of network entities, either individually or in combination, as long as the implementation meets the functional requirements. Sometimes, for practical reasons, the functional network entity is a physical device. The Mobile Station (MS) is an excellent example. • A r ...
... choose any physical implementation of network entities, either individually or in combination, as long as the implementation meets the functional requirements. Sometimes, for practical reasons, the functional network entity is a physical device. The Mobile Station (MS) is an excellent example. • A r ...
Packet switching

Packet switching is a digital networking communications method that groups all transmitted data into suitably sized blocks, called packets, which are transmitted via a medium that may be shared by multiple simultaneous communication sessions. Packet switching increases network efficiency, robustness and enables technological convergence of many applications operating on the same network.Packets are composed of a header and payload. Information in the header is used by networking hardware to direct the packet to its destination where the payload is extracted and used by application software.Starting in the late 1950s, American computer scientist Paul Baran developed the concept Distributed Adaptive Message Block Switching with the goal to provide a fault-tolerant, efficient routing method for telecommunication messages as part of a research program at the RAND Corporation, funded by the US Department of Defense. This concept contrasted and contradicted the heretofore established principles of pre-allocation of network bandwidth, largely fortified by the development of telecommunications in the Bell System. The new concept found little resonance among network implementers until the independent work of Donald Davies at the National Physical Laboratory (United Kingdom) (NPL) in the late 1960s. Davies is credited with coining the modern name packet switching and inspiring numerous packet switching networks in Europe in the decade following, including the incorporation of the concept in the early ARPANET in the United States.