Document
... •Includes all header fields •Bit in header indicates datagram is a fragment •Other fields have information for reconstructing original datagram •FRAGMENT OFFSET gives original location of ...
... •Includes all header fields •Bit in header indicates datagram is a fragment •Other fields have information for reconstructing original datagram •FRAGMENT OFFSET gives original location of ...
Telecommunications Concepts - Vrije Universiteit Brussel
... • Designed by the IETF (RFC 1661,RFC 1662,RFC 1663) • For temporary links (various network protocols) • Data Link : similar to HDLC or 802.2, but with bytes – Payload encapsulated in P frames – Frame delimited by 802.2 flag (01111110) – Character stuffing within the frame – Optional error correction ...
... • Designed by the IETF (RFC 1661,RFC 1662,RFC 1663) • For temporary links (various network protocols) • Data Link : similar to HDLC or 802.2, but with bytes – Payload encapsulated in P frames – Frame delimited by 802.2 flag (01111110) – Character stuffing within the frame – Optional error correction ...
On Monitoring of End-to-End Packet Reordering over the Internet Bin Ye
... application in the same order that they arrive at the IP layer, thus forcing the application to deal with reordering unless the application itself is not sensitive to the order of packets. For delay sensitive applications based on UDP, such as videoconferencing, an out-oforder packet that arrives af ...
... application in the same order that they arrive at the IP layer, thus forcing the application to deal with reordering unless the application itself is not sensitive to the order of packets. For delay sensitive applications based on UDP, such as videoconferencing, an out-oforder packet that arrives af ...
Delay-sensitive and multimedia communication in cognitive radio
... open research challenges for design of real-time CRSN transport protocols are explored. Finally, the paper is concluded in Section 5. 2. Real-time transport in cognitive radio sensor networks In order to realize real-time communication in CRSN, a reliable transport mechanism is imperative. Mainly tr ...
... open research challenges for design of real-time CRSN transport protocols are explored. Finally, the paper is concluded in Section 5. 2. Real-time transport in cognitive radio sensor networks In order to realize real-time communication in CRSN, a reliable transport mechanism is imperative. Mainly tr ...
Systems and methods for forwarding data units in a communications
... (110), determine one of the network interfaces (240) to trans mit the data unit When the data unit is ready to be transmitted by the network device (110), and forward the data unit to the determined network interface (240) for network When the determined network interface (240) is the identi?ed netw ...
... (110), determine one of the network interfaces (240) to trans mit the data unit When the data unit is ready to be transmitted by the network device (110), and forward the data unit to the determined network interface (240) for network When the determined network interface (240) is the identi?ed netw ...
THE OPTIMIZATION OF STEPPING STONE DETECTION: PACKET CAPTURING STEPS MOHD NIZAM OMAR
... Host A is known as Sender and Host B is known as Receiver. This experiment was restricted only to these two hosts as to assure the isolation of the testbed from external sources, therefore, allowing more accurate tests. This same testbed had also been used by [23]. Host A generated traffic using sof ...
... Host A is known as Sender and Host B is known as Receiver. This experiment was restricted only to these two hosts as to assure the isolation of the testbed from external sources, therefore, allowing more accurate tests. This same testbed had also been used by [23]. Host A generated traffic using sof ...
cn_bca4_nazir
... A. Allows gateways to send error a control messages to other gateways or hosts B. Provides communication between the Internet Protocol Software on one machine and the Internet Protocol Software on another C. Only reports error conditions to the original source, the source must relate errors to indiv ...
... A. Allows gateways to send error a control messages to other gateways or hosts B. Provides communication between the Internet Protocol Software on one machine and the Internet Protocol Software on another C. Only reports error conditions to the original source, the source must relate errors to indiv ...
Ch. 8 TCP/IP Suite Error and Control Messages (ICMP)
... The following list is a best effort overview of some widely used TCP/IP stacks. The information was provided by vendors and many helpful system administrators. We would like to thank all these contributors for their precious help ! SWITCH cannot, however, take any responsibility that the provided in ...
... The following list is a best effort overview of some widely used TCP/IP stacks. The information was provided by vendors and many helpful system administrators. We would like to thank all these contributors for their precious help ! SWITCH cannot, however, take any responsibility that the provided in ...
A Survey on Network Attacks
... computer systems, mainly through the internet. There are many different types of IDS; some of them are described in next section. The manipulations may take the form of attacks by skilled malicious hackers, or script kiddies using automated tools. An Intrusion Detection System is used to detect all ...
... computer systems, mainly through the internet. There are many different types of IDS; some of them are described in next section. The manipulations may take the form of attacks by skilled malicious hackers, or script kiddies using automated tools. An Intrusion Detection System is used to detect all ...
OSI Network Layer OSI Layer 3 Network Fundamentals – Chapter 5 ١
... An example of connectionless communication is sending a letter to someone without notifying the recipient in advance, see next figure. Connectionless data communications works on the same principle. IP packets are sent without notifying the end host that they are coming. Connection-oriented protocol ...
... An example of connectionless communication is sending a letter to someone without notifying the recipient in advance, see next figure. Connectionless data communications works on the same principle. IP packets are sent without notifying the end host that they are coming. Connection-oriented protocol ...
View
... details. • Layer 3—Network layer: Provides the routing of packets though a network from source to destination. • Layer 2—Data link layer: Ensures medium access, as well as synchronization and error control between two entities. • Layer 1—Physical layer: Provides the actual transmission of informatio ...
... details. • Layer 3—Network layer: Provides the routing of packets though a network from source to destination. • Layer 2—Data link layer: Ensures medium access, as well as synchronization and error control between two entities. • Layer 1—Physical layer: Provides the actual transmission of informatio ...
S-38.310 Thesis Seminar on Networking Technology
... • The purpose is to allow flexible wireless data networks without the need for an existing wired infrastrcture • HIPERLAN type 1 provide 20Mbit/s with 5GHz range, multimedia application are possible • HIPERLAN/2 is specified for short range radio access in 5GHz band for mobile terminals • High-speed ...
... • The purpose is to allow flexible wireless data networks without the need for an existing wired infrastrcture • HIPERLAN type 1 provide 20Mbit/s with 5GHz range, multimedia application are possible • HIPERLAN/2 is specified for short range radio access in 5GHz band for mobile terminals • High-speed ...
Multi-Protocol Label Switch (MPLS)
... • Any-to-Any Connectivity. Multiple locations are connected (meshed topology). You no longer need PVCs to communicate between sites; rather • Cost-Effective Solution. Private IP Service utilizes existing network infrastructure without building and operating a private VPN. • Intranets and Extranets. ...
... • Any-to-Any Connectivity. Multiple locations are connected (meshed topology). You no longer need PVCs to communicate between sites; rather • Cost-Effective Solution. Private IP Service utilizes existing network infrastructure without building and operating a private VPN. • Intranets and Extranets. ...
BOSNST - Openwall
... * Figure out which layer 2 protocol the frame belongs to and call * the corresponding decoding module. The protocol field of an * Ethernet II header is the 13th + 14th byte. This is an endian * independent way of extracting a big endian short from memory. We * extract the first byte and make it the ...
... * Figure out which layer 2 protocol the frame belongs to and call * the corresponding decoding module. The protocol field of an * Ethernet II header is the 13th + 14th byte. This is an endian * independent way of extracting a big endian short from memory. We * extract the first byte and make it the ...
ppt 3.8MB - Star Tap
... In a transient service environment protection is not as expensive – Telco thinking: 1+1 protection is expensive- I need to plan for twice the capacity, therefore I need to charge my customer twice as much (bronze service, silver service, platinum service, …) – Grid thinking: Provide as much protecti ...
... In a transient service environment protection is not as expensive – Telco thinking: 1+1 protection is expensive- I need to plan for twice the capacity, therefore I need to charge my customer twice as much (bronze service, silver service, platinum service, …) – Grid thinking: Provide as much protecti ...
ICMP
... • Since ICMP messages are transmitted in the same way as any other data, they are subject to the same delivery failures. • This creates a scenario where error reports could generate more error reports, causing increased congestion on an already ailing network. • For this reason, errors created by I ...
... • Since ICMP messages are transmitted in the same way as any other data, they are subject to the same delivery failures. • This creates a scenario where error reports could generate more error reports, causing increased congestion on an already ailing network. • For this reason, errors created by I ...
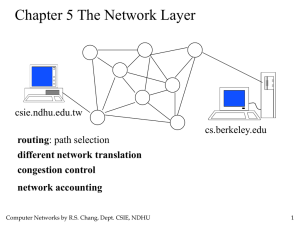
Network Layer
... reason not to put the complexity in the hosts. 2. The subnet is a major international investment that will last for decades, so it should not be cluttered up with features that may become obsolete quickly. 3. Some applications, such as digitized voice and real-time data collection may regard speedy ...
... reason not to put the complexity in the hosts. 2. The subnet is a major international investment that will last for decades, so it should not be cluttered up with features that may become obsolete quickly. 3. Some applications, such as digitized voice and real-time data collection may regard speedy ...
Metrics for Degree of Reordering in Packet Sequences
... without loss or duplication. Table 1 shows steps in computing displacements for RH. Initially, (see column 1) E, the expected sequence number is 1 and S, the arrived sequence number is also 1. The displacement value thus is 0 and hence frequency corresponding to displacement=0, F[0] becomes 1. For n ...
... without loss or duplication. Table 1 shows steps in computing displacements for RH. Initially, (see column 1) E, the expected sequence number is 1 and S, the arrived sequence number is also 1. The displacement value thus is 0 and hence frequency corresponding to displacement=0, F[0] becomes 1. For n ...
Document
... – The network layer protocol first makes a connection with the network layer protocol at the remote site before sending a packet. – When the connection is established, a sequence of packets from the same source to the same destination can be sent one after another. – There is a relationship between ...
... – The network layer protocol first makes a connection with the network layer protocol at the remote site before sending a packet. – When the connection is established, a sequence of packets from the same source to the same destination can be sent one after another. – There is a relationship between ...
plaNET - Semantic Scholar
... The COPY and reverse path accumulation options are available in the TREE routing mode as well. Another useful option available with the TREE routing mode is that of Remote Access to TREE. This feature allows a remote station which is not member of a tree, to multicast messages to all stations on tha ...
... The COPY and reverse path accumulation options are available in the TREE routing mode as well. Another useful option available with the TREE routing mode is that of Remote Access to TREE. This feature allows a remote station which is not member of a tree, to multicast messages to all stations on tha ...
Translation
... – 1. Original: Ethernet defines a number of wiring and signaling standards for the physical layer, through means of network access at the Media Access Control (MAC)/Data Link Layer and a common addressing format. – Translation: – 2. Original Adapters generally come programmed with a globally unique ...
... – 1. Original: Ethernet defines a number of wiring and signaling standards for the physical layer, through means of network access at the Media Access Control (MAC)/Data Link Layer and a common addressing format. – Translation: – 2. Original Adapters generally come programmed with a globally unique ...
Layer 3 Multiprotocol Label Switching Vir-
... MPLS packets can run on other Layer 2 technologies such as ATM, Frame Relay, PPP, POS and Ethernet, in the same manner as these Layer 2 technologies can run on MPLS network /4/. MPLS is normally used by Service Providers, however large scale corporations also build their own private MPLS network. Th ...
... MPLS packets can run on other Layer 2 technologies such as ATM, Frame Relay, PPP, POS and Ethernet, in the same manner as these Layer 2 technologies can run on MPLS network /4/. MPLS is normally used by Service Providers, however large scale corporations also build their own private MPLS network. Th ...
Chapter 5
... Fragments from different datagrams can arrive out of order and still be sorted out by : matching them using the IDENT field values; recognizing the last fragment from the bit set in its header; and recognizing when all fragments in an original datagram have been received. ...
... Fragments from different datagrams can arrive out of order and still be sorted out by : matching them using the IDENT field values; recognizing the last fragment from the bit set in its header; and recognizing when all fragments in an original datagram have been received. ...
Network Deployment Guide for NovoPRO
... WiFi interference and channel selection, intranet firewall, Bonjour protocol support across different subnets/VLANs, Quality of Service and device management. In this whitepaper, we are going to illustrate these points one by one to facilitate a successful NovoPRO deployment in your network. ...
... WiFi interference and channel selection, intranet firewall, Bonjour protocol support across different subnets/VLANs, Quality of Service and device management. In this whitepaper, we are going to illustrate these points one by one to facilitate a successful NovoPRO deployment in your network. ...
1.Physical Layer & Data Link Layer
... Never have collisions because no station can transmit without a token, and there's only one token Token ring networks perform linearly with the amount of data to be transmitted, almost up to the theoretical maximum Ethernet transmission rates plateau well before the theoretical maximum when seve ...
... Never have collisions because no station can transmit without a token, and there's only one token Token ring networks perform linearly with the amount of data to be transmitted, almost up to the theoretical maximum Ethernet transmission rates plateau well before the theoretical maximum when seve ...
Packet switching

Packet switching is a digital networking communications method that groups all transmitted data into suitably sized blocks, called packets, which are transmitted via a medium that may be shared by multiple simultaneous communication sessions. Packet switching increases network efficiency, robustness and enables technological convergence of many applications operating on the same network.Packets are composed of a header and payload. Information in the header is used by networking hardware to direct the packet to its destination where the payload is extracted and used by application software.Starting in the late 1950s, American computer scientist Paul Baran developed the concept Distributed Adaptive Message Block Switching with the goal to provide a fault-tolerant, efficient routing method for telecommunication messages as part of a research program at the RAND Corporation, funded by the US Department of Defense. This concept contrasted and contradicted the heretofore established principles of pre-allocation of network bandwidth, largely fortified by the development of telecommunications in the Bell System. The new concept found little resonance among network implementers until the independent work of Donald Davies at the National Physical Laboratory (United Kingdom) (NPL) in the late 1960s. Davies is credited with coining the modern name packet switching and inspiring numerous packet switching networks in Europe in the decade following, including the incorporation of the concept in the early ARPANET in the United States.