Trading Structure for Randomness in Wireless Opportunistic Routing
... and provided theoretical bounds on the capacity of such networks [2]. The combination of [26, 24, 18] shows that, for multicast traffic, linear codes achieve the maximum capacity bounds, and coding and decoding can be done in polynomial time. Additionally, Ho et al. show that the above is true even ...
... and provided theoretical bounds on the capacity of such networks [2]. The combination of [26, 24, 18] shows that, for multicast traffic, linear codes achieve the maximum capacity bounds, and coding and decoding can be done in polynomial time. Additionally, Ho et al. show that the above is true even ...
Trading Structure for Randomness in Wireless Opportunistic Routing
... routing protocol for mesh wireless networks. ExOR, however, requires node coordination, which is more difficult in larger networks. Consider again the example in the previous paragraph. R should forward only packet p2 because the first packet has already been received by the destination; but, withou ...
... routing protocol for mesh wireless networks. ExOR, however, requires node coordination, which is more difficult in larger networks. Consider again the example in the previous paragraph. R should forward only packet p2 because the first packet has already been received by the destination; but, withou ...
NETWORK LAN PLANNER
... server and each other. Client-server networks use servers in different capacities. These can be classified into two types: Single-service servers, where the server performs one task such as file server, print server, etc.; while other servers can not only perform in the capacity of file servers and ...
... server and each other. Client-server networks use servers in different capacities. These can be classified into two types: Single-service servers, where the server performs one task such as file server, print server, etc.; while other servers can not only perform in the capacity of file servers and ...
IP Datagram Header - California State University, Long Beach
... FLAGS -- 3-bit field with individual bits specifying whether the datagram is a fragment FRAGMENT OFFSET -- 13-bit field that specifies where in the original datagram the data in this fragment belongs (the value of the field is multiplied by 8 to obtain an offset) ...
... FLAGS -- 3-bit field with individual bits specifying whether the datagram is a fragment FRAGMENT OFFSET -- 13-bit field that specifies where in the original datagram the data in this fragment belongs (the value of the field is multiplied by 8 to obtain an offset) ...
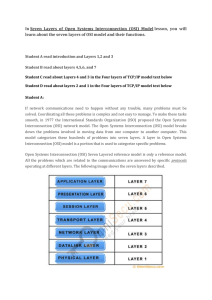
(Seven Layers of Open Systems Interconnection (OSI
... Transport layer. The Internet layer packs data into data packets known as IP datagrams, which contain a source and destination address (logical address or IP address) information that is used to forward the datagrams between hosts and across networks. The Internet layer is also responsible for the r ...
... Transport layer. The Internet layer packs data into data packets known as IP datagrams, which contain a source and destination address (logical address or IP address) information that is used to forward the datagrams between hosts and across networks. The Internet layer is also responsible for the r ...
COMPUTER NETWORKS
... topology and network technologies in order to be fast, reliable and easy expandable. The transmitted data is divided into the appropriate Protocol Data Units. Ability to analyse the data is required to understand the network protocols and to troubleshoot the network problems. Local Area Networks int ...
... topology and network technologies in order to be fast, reliable and easy expandable. The transmitted data is divided into the appropriate Protocol Data Units. Ability to analyse the data is required to understand the network protocols and to troubleshoot the network problems. Local Area Networks int ...
IP Datagram - La Salle University
... Based on Chapter 20 of Computer Networks and Internets (Comer) ...
... Based on Chapter 20 of Computer Networks and Internets (Comer) ...
IOSR Journal of Computer Engineering (IOSR-JCE)
... Black hole attack is one of the most common attacks made against the reactive routing protocol in MANETs. The black hole attack involves malicious node(s) fabricating the sequence number, hence pretending to have the shortest and freshest route to the destination. Numerous studies have attempted to ...
... Black hole attack is one of the most common attacks made against the reactive routing protocol in MANETs. The black hole attack involves malicious node(s) fabricating the sequence number, hence pretending to have the shortest and freshest route to the destination. Numerous studies have attempted to ...
Communicating over the Network - Seneca
... – Commonly referred to as hosts (source or destination of a message) – Each host has an address that will identify it on the network – Role of end devices: • Client (software installed so they can request & display info from the ...
... – Commonly referred to as hosts (source or destination of a message) – Each host has an address that will identify it on the network – Role of end devices: • Client (software installed so they can request & display info from the ...
Liaison Statement to IETF PWE3 WG on MS-PW over T-MPLS
... During the meeting requirements have been identified and agreed to carry a Multi-Segment Pseudowire (MS-PW) across IP/MPLS and T-MPLS networks. Q12/15 would appreciate feedbacks from IETF PWE3 WG on the problem statement and whether this application can be taken into consideration in the on-going wo ...
... During the meeting requirements have been identified and agreed to carry a Multi-Segment Pseudowire (MS-PW) across IP/MPLS and T-MPLS networks. Q12/15 would appreciate feedbacks from IETF PWE3 WG on the problem statement and whether this application can be taken into consideration in the on-going wo ...
popular short SDN + NFV talk
... (Service) function chaining is a new SDN+NFV application that has been receiving a lot of attention Its main application is inside data centers but there are also applications in mobile networks A packet needs to be steered through a chain of functions (services) Examples of services (functions) : • ...
... (Service) function chaining is a new SDN+NFV application that has been receiving a lot of attention Its main application is inside data centers but there are also applications in mobile networks A packet needs to be steered through a chain of functions (services) Examples of services (functions) : • ...
Chapter 9.doc
... Darken the letter on a Scantron that indicates whether the sentence or statement is true or false. 1. Today, only large computers have communications capabilities. 2. To place an Internet telephone call, Internet software and a computer’s sound card are needed to digitize and compress the spoken wor ...
... Darken the letter on a Scantron that indicates whether the sentence or statement is true or false. 1. Today, only large computers have communications capabilities. 2. To place an Internet telephone call, Internet software and a computer’s sound card are needed to digitize and compress the spoken wor ...
Internet Control Message Protocol
... Path Discovery with TRACEROUTE (Contd.) To identify the next hop, traceroute sends a UDP packet with a TTL value of 2. The first router decrements the TTL field by 1 and sends the datagram to the next router. The second router sees a TTL value of 1, discards the datagram, and returns the Time-Exc ...
... Path Discovery with TRACEROUTE (Contd.) To identify the next hop, traceroute sends a UDP packet with a TTL value of 2. The first router decrements the TTL field by 1 and sends the datagram to the next router. The second router sees a TTL value of 1, discards the datagram, and returns the Time-Exc ...
I Know What Your Packet Did Last Hop: Using Packet
... constructing them, we built NetSight, an extensible platform that captures packet histories and enables applications to concisely and flexibly retrieve packet histories of interest. Atop NetSight, we built four applications that illustrate its flexibility: an interactive network debugger, a live inv ...
... constructing them, we built NetSight, an extensible platform that captures packet histories and enables applications to concisely and flexibly retrieve packet histories of interest. Atop NetSight, we built four applications that illustrate its flexibility: an interactive network debugger, a live inv ...
Control System Specification
... 2.14. Device External Interface Files: The external interface file of a device defines the product’s network data, message tags, and hardware related parameters. 2.15. Device Resource File: A device’s detailed information file describing any specific interfaces, ...
... 2.14. Device External Interface Files: The external interface file of a device defines the product’s network data, message tags, and hardware related parameters. 2.15. Device Resource File: A device’s detailed information file describing any specific interfaces, ...
A Performance Comparison of Multi-Hop Wireless Ad Hoc
... Each mobile node has a position and a velocity and moves around on a topography that is specified using either a digital elevation map or a flat grid. The position of a mobile node can be calculated as a function of time, and is used by the radio propagation model to calculate the propagation delay ...
... Each mobile node has a position and a velocity and moves around on a topography that is specified using either a digital elevation map or a flat grid. The position of a mobile node can be calculated as a function of time, and is used by the radio propagation model to calculate the propagation delay ...
The TCP/IP Protocol Suite
... formatted and encoded for digital transmission over a node-tonode link. Frames typically are used from the MAC sublayer downward. A frame can be thought of as the physical envelope that delivers an upper level packet or datagram. Cell A cell is a 53-byte fixed-length MAC sublayer PDU used by Asynchr ...
... formatted and encoded for digital transmission over a node-tonode link. Frames typically are used from the MAC sublayer downward. A frame can be thought of as the physical envelope that delivers an upper level packet or datagram. Cell A cell is a 53-byte fixed-length MAC sublayer PDU used by Asynchr ...
AiroPeek NX v1.2 QuickTour
... help you become familiar with some key program features, including the Expert and Peer Map views. EtherPeek NX works by capturing traffic from one or more adapters, providing the tools to filter, analyze and interpret traffic patterns, data packet contents, statistics, and protocol types. EtherPeek ...
... help you become familiar with some key program features, including the Expert and Peer Map views. EtherPeek NX works by capturing traffic from one or more adapters, providing the tools to filter, analyze and interpret traffic patterns, data packet contents, statistics, and protocol types. EtherPeek ...
ppt
... • http://www.cs.cmu.edu/~srini • [email protected] • Office hours: Wed 11:00-12:00 (for now…) ...
... • http://www.cs.cmu.edu/~srini • [email protected] • Office hours: Wed 11:00-12:00 (for now…) ...
Document
... o Important: = interface between carrier and customer o Designed with following goals in mind: • Services should be independent of the subnet technology • Transport layer should be shielded from the number, type, topology of the subnets • Network addresses should use a uniform numbering plan, even a ...
... o Important: = interface between carrier and customer o Designed with following goals in mind: • Services should be independent of the subnet technology • Transport layer should be shielded from the number, type, topology of the subnets • Network addresses should use a uniform numbering plan, even a ...
15-744: Computer Networking
... • E.g. www.cmu.edu • Globally unique (can correspond to multiple hosts) ...
... • E.g. www.cmu.edu • Globally unique (can correspond to multiple hosts) ...
Hash-Based IP Traceback - Events
... option processing, ICMP processing, and packet duplication. Network address translation (NAT) and both IP-in-IP and IPsec tunneling are also notable forms of packet transformation. Many of these transformations result in an irrecoverable loss of the original packet state due to the stateless nature ...
... option processing, ICMP processing, and packet duplication. Network address translation (NAT) and both IP-in-IP and IPsec tunneling are also notable forms of packet transformation. Many of these transformations result in an irrecoverable loss of the original packet state due to the stateless nature ...
Computer Networking Tutorial - ECE, Rutgers
... - Autonomy: Different parts of the Internet are controlled by independent organizations. Even a sub-network controlled by the same multinational organization, such as IBM or Coca Cola, may cross many state borders. These independent organizations are generally in competition with each other and do n ...
... - Autonomy: Different parts of the Internet are controlled by independent organizations. Even a sub-network controlled by the same multinational organization, such as IBM or Coca Cola, may cross many state borders. These independent organizations are generally in competition with each other and do n ...
Document
... Cannot ensure that communication is carried out between the two desired hosts, and not intercepted in the middle ...
... Cannot ensure that communication is carried out between the two desired hosts, and not intercepted in the middle ...
common lower-layer protocols
... of addressing must work together in order for communication to occur. Consider a scenario where you wish to communicate with a device on your network. This device may be a server of some sort or just another workstation you need to share files with. The application you are using to initiate the comm ...
... of addressing must work together in order for communication to occur. Consider a scenario where you wish to communicate with a device on your network. This device may be a server of some sort or just another workstation you need to share files with. The application you are using to initiate the comm ...
Packet switching

Packet switching is a digital networking communications method that groups all transmitted data into suitably sized blocks, called packets, which are transmitted via a medium that may be shared by multiple simultaneous communication sessions. Packet switching increases network efficiency, robustness and enables technological convergence of many applications operating on the same network.Packets are composed of a header and payload. Information in the header is used by networking hardware to direct the packet to its destination where the payload is extracted and used by application software.Starting in the late 1950s, American computer scientist Paul Baran developed the concept Distributed Adaptive Message Block Switching with the goal to provide a fault-tolerant, efficient routing method for telecommunication messages as part of a research program at the RAND Corporation, funded by the US Department of Defense. This concept contrasted and contradicted the heretofore established principles of pre-allocation of network bandwidth, largely fortified by the development of telecommunications in the Bell System. The new concept found little resonance among network implementers until the independent work of Donald Davies at the National Physical Laboratory (United Kingdom) (NPL) in the late 1960s. Davies is credited with coining the modern name packet switching and inspiring numerous packet switching networks in Europe in the decade following, including the incorporation of the concept in the early ARPANET in the United States.