4. cpp based products
... As mobile communications evolve, mobile end-users will be offered wideband multimedia capabilities. The associated multimedia streams require that the networks should be more flexible than networks that are based on time-division multiplexing (TDM) – at providing bandwidth on demand. Today's tele- a ...
... As mobile communications evolve, mobile end-users will be offered wideband multimedia capabilities. The associated multimedia streams require that the networks should be more flexible than networks that are based on time-division multiplexing (TDM) – at providing bandwidth on demand. Today's tele- a ...
Similarity of Nodes in A Social Network
... • Each node contains a set of keywords defined as resources • The keywords consists of music songs and the associated band and album • Each node/user has connections to its neighbors • A randomly selected node starts a query • The query keyword is selected from the node’s set of keywords to ensure t ...
... • Each node contains a set of keywords defined as resources • The keywords consists of music songs and the associated band and album • Each node/user has connections to its neighbors • A randomly selected node starts a query • The query keyword is selected from the node’s set of keywords to ensure t ...
bhoot pres1
... If one link fails for any reason, the network automatically routes messages through alternate paths. ...
... If one link fails for any reason, the network automatically routes messages through alternate paths. ...
LAN / WAN / Extranet และ Network Topology แบบต่าง ๆ
... PDU (protocol data unit) – Destination SAP, Sequence #, Error-Detection Code ...
... PDU (protocol data unit) – Destination SAP, Sequence #, Error-Detection Code ...
Security Tools
... • -h (m) max number of hops to search for target • -j (hostlist) loose source route along the host list • -w (timeout) wait (timeout) msec for each reply ...
... • -h (m) max number of hops to search for target • -j (hostlist) loose source route along the host list • -w (timeout) wait (timeout) msec for each reply ...
CH2-Topologies
... Network topology is the study of the arrangement or mapping of the elements (links, nodes, etc.) of a network, especially the physical (real) and logical (virtual) interconnections between nodes. There are two types of topologies: Physical and Logical. The physical topology of a network refers to t ...
... Network topology is the study of the arrangement or mapping of the elements (links, nodes, etc.) of a network, especially the physical (real) and logical (virtual) interconnections between nodes. There are two types of topologies: Physical and Logical. The physical topology of a network refers to t ...
tut1 - Webcourse
... If the packet is destined to other network then the router sends it to another router. Otherwise the router sends the packet to the appropriate host on its attached networks. ...
... If the packet is destined to other network then the router sends it to another router. Otherwise the router sends the packet to the appropriate host on its attached networks. ...
(3) 2013 test
... saleswoman. For a particular applicant for a sales job, my neural network gives estimated probability p=0.3 that she will be a good saleswoman. If she is not good, she will cost me $4,000 per month in the long run because her sales are less than her salary. On the other hand, if she is good, she wil ...
... saleswoman. For a particular applicant for a sales job, my neural network gives estimated probability p=0.3 that she will be a good saleswoman. If she is not good, she will cost me $4,000 per month in the long run because her sales are less than her salary. On the other hand, if she is good, she wil ...
CSC 335 Data Communications and Networking I
... • At each layer, protocols are used to communicate • Control information is added to user data at each layer • Transport layer may fragment user data • Each fragment has a transport header added – Destination SAP – Sequence number – Error detection code ...
... • At each layer, protocols are used to communicate • Control information is added to user data at each layer • Transport layer may fragment user data • Each fragment has a transport header added – Destination SAP – Sequence number – Error detection code ...
lecture12_2010
... • Every node can be reached from every other by a small number of steps Social networks, the Internet, and biological networks all exhibit small-world network characteristics ...
... • Every node can be reached from every other by a small number of steps Social networks, the Internet, and biological networks all exhibit small-world network characteristics ...
ADSL Network - Binus Repository
... that have been preconfigured by the carrier are used. • Virtual circuits may be established dynamically by sending signaling messages to the network. In this case they are called switched virtual circuits (SVCs). ...
... that have been preconfigured by the carrier are used. • Virtual circuits may be established dynamically by sending signaling messages to the network. In this case they are called switched virtual circuits (SVCs). ...
Network management
... 4) to configure ('provision') circuits or paths through non-switched networks ...
... 4) to configure ('provision') circuits or paths through non-switched networks ...
PowerPoint Presentation - No Slide Title
... Fiber optics, free-space optics, wireless, satellite, WiFi. WiMax 100 Mbps, ~Gbps, ~Tbps ...
... Fiber optics, free-space optics, wireless, satellite, WiFi. WiMax 100 Mbps, ~Gbps, ~Tbps ...
Modeling Channel Conflict Probabilities between IEEE 802
... Compare the proposed approach using the pathChirp-like model with pathChirp and Spruce. Run 1,500 tests for both pathChirp and Spruce in the same network scenario. ...
... Compare the proposed approach using the pathChirp-like model with pathChirp and Spruce. Run 1,500 tests for both pathChirp and Spruce in the same network scenario. ...
Part I: Introduction
... Q: How to connect end systems to edge router? o residential access nets o institutional access networks ...
... Q: How to connect end systems to edge router? o residential access nets o institutional access networks ...
New services call for new financial networks TextStart With China`s
... Huawei's high-end switches and routers, with a proven track record of reliable performance and stable operation during a trial run by the bank, were praised by ABC for their compatibility, switching, and Layer 3 routing. Successfully passing various tests by the bank's head office and tier-1 branche ...
... Huawei's high-end switches and routers, with a proven track record of reliable performance and stable operation during a trial run by the bank, were praised by ABC for their compatibility, switching, and Layer 3 routing. Successfully passing various tests by the bank's head office and tier-1 branche ...
CS514-lec
... is bound to that port, packet is dropped) • Fixed maximum size of 1400 bytes • Each machine can have multiple addresses • Special “broadcast” address delivered to all • “Class D” addresses used for multicast groups • Running out of addresses, so tricks with addresses are increasingly common ...
... is bound to that port, packet is dropped) • Fixed maximum size of 1400 bytes • Each machine can have multiple addresses • Special “broadcast” address delivered to all • “Class D” addresses used for multicast groups • Running out of addresses, so tricks with addresses are increasingly common ...
Network Protocols
... If one machine goes down, use another A user is able to store data in multiple locations ...
... If one machine goes down, use another A user is able to store data in multiple locations ...
Meet Horatio How it Works
... provides a clean and easy-to-use mobile and desktop experience. The Horatio Bridge Device is a 1RU embedded system that bridges between a lighting network and the internet. It provides a secure connection into the lighting network, queues reports, and provides local storage of data, even if the netw ...
... provides a clean and easy-to-use mobile and desktop experience. The Horatio Bridge Device is a 1RU embedded system that bridges between a lighting network and the internet. It provides a secure connection into the lighting network, queues reports, and provides local storage of data, even if the netw ...
Grid: Scalable Ad Hoc Networking
... • Nodes that know their location can act as location proxies • Location proxies can communicate with each other using geographic forwarding and the local routing protocol • Nodes without location select proxies, and communicate through them using the local protocol • Nodes advertise proxy locations ...
... • Nodes that know their location can act as location proxies • Location proxies can communicate with each other using geographic forwarding and the local routing protocol • Nodes without location select proxies, and communicate through them using the local protocol • Nodes advertise proxy locations ...
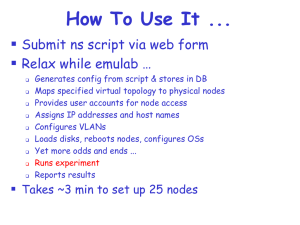
emulab.net: A Network Emulation and Distributed Systems Testbed
... interconnect bandwidth In our example, there are four switches, each with 400 Mbps interconnect More than 4 links mapped onto a given interconnect would produce an artifact because of the bottleneck In solution, node color indicates its switch ...
... interconnect bandwidth In our example, there are four switches, each with 400 Mbps interconnect More than 4 links mapped onto a given interconnect would produce an artifact because of the bottleneck In solution, node color indicates its switch ...
Chapter 10
... network is dependent on the switch • However, in most large star networks, backup switches are available immediately in case of hardware failure ...
... network is dependent on the switch • However, in most large star networks, backup switches are available immediately in case of hardware failure ...