PPT_ch01 - Mercer University Computer Science Department
... • The main goals of information security are to prevent data theft, thwart identity theft, avoid the legal consequences of not securing information, maintain productivity, and foil cyberterrorism • The types of people behind computer attacks are generally divided into several categories • There are ...
... • The main goals of information security are to prevent data theft, thwart identity theft, avoid the legal consequences of not securing information, maintain productivity, and foil cyberterrorism • The types of people behind computer attacks are generally divided into several categories • There are ...
Security+ Guide to Network Security Fundamentals, Third Edition
... • The main goals of information security are to prevent data theft, thwart identity theft, avoid the legal consequences of not securing information, maintain productivity, and foil cyberterrorism • The types of people behind computer attacks are generally divided into several categories • There are ...
... • The main goals of information security are to prevent data theft, thwart identity theft, avoid the legal consequences of not securing information, maintain productivity, and foil cyberterrorism • The types of people behind computer attacks are generally divided into several categories • There are ...
Information Security Attack Tree Modeling for Enhancing Student Learning
... • Students’ inability to think like hackers in modeling attack scenarios - Given a vulnerability, they tend to think in terms of what the system administrator should do rather than system exploitation strategies • The challenge of modeling all possible attack scenarios--Coverage • The challenge of t ...
... • Students’ inability to think like hackers in modeling attack scenarios - Given a vulnerability, they tend to think in terms of what the system administrator should do rather than system exploitation strategies • The challenge of modeling all possible attack scenarios--Coverage • The challenge of t ...
CCNPv5 Module 5 Lesson 1
... Inoculation: Start patching all systems and, if possible, scanning for vulnerable systems. Quarantine: Track down each infected machine inside your network. Disconnect, remove, or block infected machines from the network. Treatment: Clean and patch each infected system. Some worms may require comple ...
... Inoculation: Start patching all systems and, if possible, scanning for vulnerable systems. Quarantine: Track down each infected machine inside your network. Disconnect, remove, or block infected machines from the network. Treatment: Clean and patch each infected system. Some worms may require comple ...
CISCO Secure Intrusion Detection System
... The sensor can also log more detailed alarm information in a local text-based log file, which allows for in-depth analysis of attack data and the use of custom scripts to present alarm data specific to your requirements. ...
... The sensor can also log more detailed alarm information in a local text-based log file, which allows for in-depth analysis of attack data and the use of custom scripts to present alarm data specific to your requirements. ...
Acceptable Use Policy for IT
... level of personal use of the company’s IT systems. If employees are uncertain they should consult their manager. Any information that is particularly sensitive or vulnerable must be encrypted and/or securely stored so that unauthorised access is prevented (or at least made extremely difficult). Howe ...
... level of personal use of the company’s IT systems. If employees are uncertain they should consult their manager. Any information that is particularly sensitive or vulnerable must be encrypted and/or securely stored so that unauthorised access is prevented (or at least made extremely difficult). Howe ...
Network Vulnerability Scanning - Texas Tech University Departments
... • Manual detection and remediation workflow is too slow, too expensive and ineffective ...
... • Manual detection and remediation workflow is too slow, too expensive and ineffective ...
Cafe Cracks: Attacks on Unsecured Wireless Networks
... users to phishing sites using DNS. It is possible that users will have some of their own network parameters, such as DNS server, manually configured. To still perform DNS attacks the attack machine will need to be able to perform packet redirects as part of its routing capabilities. For example, sin ...
... users to phishing sites using DNS. It is possible that users will have some of their own network parameters, such as DNS server, manually configured. To still perform DNS attacks the attack machine will need to be able to perform packet redirects as part of its routing capabilities. For example, sin ...
SOW
... Expert level: master’s degree in computer science, engineering or a related technical discipline, 8+ years of related technical experience. Intermediate level: bachelor’s degree in computer science, engineering or a related technical discipline, 5+ years of related technical experience. Junior level ...
... Expert level: master’s degree in computer science, engineering or a related technical discipline, 8+ years of related technical experience. Intermediate level: bachelor’s degree in computer science, engineering or a related technical discipline, 5+ years of related technical experience. Junior level ...
Introduction to Computer Security
... • Overt channel – Communication channel that is used in the way it is intended to use ...
... • Overt channel – Communication channel that is used in the way it is intended to use ...
POLICY Number: 0-501 Title: Information Technology Resources
... System) campuses, colleges, departments and entities. In some cases, these applications have become critical to the operation of the organization and the USF System. It is essential, therefore, that adequate measures be used to protect the integrity and reliability of those computing systems and the ...
... System) campuses, colleges, departments and entities. In some cases, these applications have become critical to the operation of the organization and the USF System. It is essential, therefore, that adequate measures be used to protect the integrity and reliability of those computing systems and the ...
Principles of Computer Security
... Intrusion Prevention Systems • In addition to IDS functions, it has the capability of stopping or preventing malicious attack. • Some can inspect encrypted traffic (SSL traffic) • Often rated by the amount of traffic that can be processed without dropping packets. ...
... Intrusion Prevention Systems • In addition to IDS functions, it has the capability of stopping or preventing malicious attack. • Some can inspect encrypted traffic (SSL traffic) • Often rated by the amount of traffic that can be processed without dropping packets. ...
IPCablecom - Network and Service Architecture
... IETF – Services: allocation and authorization of gates (access control entities for QoS), prevention of theft of service – Gate co-ordination based on RADIUS IPCablecom/Mediacom 2004/Interactivity in Multimedia Dipl.-Ing. Volker Leisse · Institute for Communications Technology · Braunschweig Technic ...
... IETF – Services: allocation and authorization of gates (access control entities for QoS), prevention of theft of service – Gate co-ordination based on RADIUS IPCablecom/Mediacom 2004/Interactivity in Multimedia Dipl.-Ing. Volker Leisse · Institute for Communications Technology · Braunschweig Technic ...
Federal Systems Level Guidance for Securing
... As most of us know, routers are the traffic cops of computer networks. Routers direct and control data flowing across networks and the Internet. Network administrators and security officers work in conjunction to secure network perimeters. They use routers to control network access, ward-off attacks ...
... As most of us know, routers are the traffic cops of computer networks. Routers direct and control data flowing across networks and the Internet. Network administrators and security officers work in conjunction to secure network perimeters. They use routers to control network access, ward-off attacks ...
Devireddy
... dynamic way for securing data. It uses the same RC4 algorithm as WEP does and it is not considered as a long term solution. ...
... dynamic way for securing data. It uses the same RC4 algorithm as WEP does and it is not considered as a long term solution. ...
SECDO Platform White Paper -
... Today it’s clear that despite the massive amount of log information that IT systems are generating, Security Operations teams simply do not have enough information about endpoint and server activity. The only way to understand the full context of an alert like the suspicious query above is to see th ...
... Today it’s clear that despite the massive amount of log information that IT systems are generating, Security Operations teams simply do not have enough information about endpoint and server activity. The only way to understand the full context of an alert like the suspicious query above is to see th ...
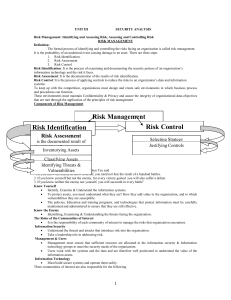
IT2042-UNIT3-Notes
... -The inventory listing is usually available in a data base. - Once stored, the inventory listing must be kept current, often by means of a tool that periodically refreshes the data. Information Asset Classification- In addition to the categories, it is advisable to add another dimension to represent ...
... -The inventory listing is usually available in a data base. - Once stored, the inventory listing must be kept current, often by means of a tool that periodically refreshes the data. Information Asset Classification- In addition to the categories, it is advisable to add another dimension to represent ...
Physical Security
... and be able to analyze traffic according to protocol, type, amount, source, destination, content, traffic already seen, and other factors. – This analysis must happen quickly, and the NIDS must be able to handle traffic at whatever speed the network operates to be effective. ...
... and be able to analyze traffic according to protocol, type, amount, source, destination, content, traffic already seen, and other factors. – This analysis must happen quickly, and the NIDS must be able to handle traffic at whatever speed the network operates to be effective. ...
CIS484-FIREWALL
... Packet filtering - a simple method, packet filtering entails analyzing small packets or chunks of data through a series of filters. ...
... Packet filtering - a simple method, packet filtering entails analyzing small packets or chunks of data through a series of filters. ...
3_firewall_m
... Mode or IP Masquerade) • Wherein a large group of internal clients share a single or small group of internal IP addresses for the purpose of hiding their identities or expanding the internal network address space. – Static Translation (also called Port Forwarding) • Wherein a specific internal netwo ...
... Mode or IP Masquerade) • Wherein a large group of internal clients share a single or small group of internal IP addresses for the purpose of hiding their identities or expanding the internal network address space. – Static Translation (also called Port Forwarding) • Wherein a specific internal netwo ...
1. The Threat Environment: Attackers and their Attacks
... ◦ Criminals are learning to conduct traditional frauds and new frauds over networks ◦ Also, new types of fraud, such as click fraud ...
... ◦ Criminals are learning to conduct traditional frauds and new frauds over networks ◦ Also, new types of fraud, such as click fraud ...
PCI Compliance Without Compensating Controls – How to Take Ulf Mattsson
... Assign a unique ID to each person with computer access Restrict physical access to cardholder data ...
... Assign a unique ID to each person with computer access Restrict physical access to cardholder data ...