Security+ Guide to Network Security Fundamentals, Third
... Recognize several common networking-related security problems Report the problems _________________________ Offer a tutorial that explained the problem, what its impact could be, and how to resolve the problem ...
... Recognize several common networking-related security problems Report the problems _________________________ Offer a tutorial that explained the problem, what its impact could be, and how to resolve the problem ...
Top Ten Database Threats
... Enrich Access Rights Information with User Details and Data Sensitivity: Adding information related to user roles and their database behavior adds considerable value to user rights analysis and helps zero-in on the abuse of privileges. Collect and append contextual details to user rights information ...
... Enrich Access Rights Information with User Details and Data Sensitivity: Adding information related to user roles and their database behavior adds considerable value to user rights analysis and helps zero-in on the abuse of privileges. Collect and append contextual details to user rights information ...
Security+ Guide to Network Security Fundamentals, Third Edition
... Data is accumulated through the ___________ _________________ and networks through _____________________________ _____________ is compared with the baseline data to determine how closely the norm is being met and if any adjustments need to be made ...
... Data is accumulated through the ___________ _________________ and networks through _____________________________ _____________ is compared with the baseline data to determine how closely the norm is being met and if any adjustments need to be made ...
Tenable Malware Detection
... technique is the use of signatures, which are periodically released from the AV vendor. More recently heuristic analysis has also become more common, which tries to rely on more generic signatures to catch malware variants. Other techniques include malicious activity detection (OS, kernel, registry ...
... technique is the use of signatures, which are periodically released from the AV vendor. More recently heuristic analysis has also become more common, which tries to rely on more generic signatures to catch malware variants. Other techniques include malicious activity detection (OS, kernel, registry ...
CN 2015 5 - SNGCE DIGITAL LIBRARY
... Cryptographic techniques allow sender to mask data. Cryptographic techniques allow receiver to recover data from masked data. It is the study of Encryption and Decryption methods. Encryption—Plain text to cipher text Decryption—Cipher text to Plain text ...
... Cryptographic techniques allow sender to mask data. Cryptographic techniques allow receiver to recover data from masked data. It is the study of Encryption and Decryption methods. Encryption—Plain text to cipher text Decryption—Cipher text to Plain text ...
Edgenuity SSL Protocols
... interpreted one way. A FQDN will need to be established for your school’s DNS records. After the certificate has been applied to your media appliance you will need to contact the IT of the site and make sure the FQDN has been set up in the school’s DNS records to point to the media appliances IP add ...
... interpreted one way. A FQDN will need to be established for your school’s DNS records. After the certificate has been applied to your media appliance you will need to contact the IT of the site and make sure the FQDN has been set up in the school’s DNS records to point to the media appliances IP add ...
Introduction
... Threats that are carried out are attacks. Intentional attacks are carried out by an attacker. Objects of attacks are assets. ...
... Threats that are carried out are attacks. Intentional attacks are carried out by an attacker. Objects of attacks are assets. ...
The Role of People in Security
... Overview of Baselines • The process of establishing a system’s security state is called baselining. • The resulting product is a security baseline that allows the system to run safely and securely. • Once the process has been completed, any similar systems can be configured with the same baseline to ...
... Overview of Baselines • The process of establishing a system’s security state is called baselining. • The resulting product is a security baseline that allows the system to run safely and securely. • Once the process has been completed, any similar systems can be configured with the same baseline to ...
General Assembly 1 Background Guide
... (UNIDIR), a cyber-attack may be defined as an unauthorized attempt to infiltrate, gain access to, or shut down a computer, system, or network. Therefore, cyber security can be defined as “the collection of tools, policies, security concepts, security safeguards, guidelines, risk management approache ...
... (UNIDIR), a cyber-attack may be defined as an unauthorized attempt to infiltrate, gain access to, or shut down a computer, system, or network. Therefore, cyber security can be defined as “the collection of tools, policies, security concepts, security safeguards, guidelines, risk management approache ...
EAP
... A client device connects to a port on an 802.1x switch and AP The switch port can determine the authenticity of the devices The services offered by the switch can be made available on that port Only EAPOL frames can be sent and received on that port until authentication is complete. When the device ...
... A client device connects to a port on an 802.1x switch and AP The switch port can determine the authenticity of the devices The services offered by the switch can be made available on that port Only EAPOL frames can be sent and received on that port until authentication is complete. When the device ...
windows and linux operating systems from a security perspective
... each user is a good idea, though not strictly required. The mapping of username to UID is kept in the file /etc/passwd, and is centrally managed by NIS. The super user,also known as root, has a UID equals to 0. Every user belongs to one or more groups. A group is identified with a group identificati ...
... each user is a good idea, though not strictly required. The mapping of username to UID is kept in the file /etc/passwd, and is centrally managed by NIS. The super user,also known as root, has a UID equals to 0. Every user belongs to one or more groups. A group is identified with a group identificati ...
CHAPTER 1 Networking Concepts
... Business Requirements for SET over Internet Provide confidentiality of payment and order information Ensure the integrity of all transmitted data Provide authentication that a cardholder is a legitimate user of a credit card account Provide authentication that a merchant can accept credit ca ...
... Business Requirements for SET over Internet Provide confidentiality of payment and order information Ensure the integrity of all transmitted data Provide authentication that a cardholder is a legitimate user of a credit card account Provide authentication that a merchant can accept credit ca ...
latest AHIA and Grant Thornton LLP White Paper: Third
... • HHS is reported to annually via a website for breaches affecting fewer than 500 individuals Before auditors can assess the risks associated with • HHS and the media are notified within 60 days a vendor’s processes, they must first understand of determination that a breach affects 500 or ho ...
... • HHS is reported to annually via a website for breaches affecting fewer than 500 individuals Before auditors can assess the risks associated with • HHS and the media are notified within 60 days a vendor’s processes, they must first understand of determination that a breach affects 500 or ho ...
Threats To Windows Users and Countermeasures
... DOS program, the Tribe Flood Network is installed in compromised computers weeks or months before the attack. Another DDOS tool known as "Knight" was found on approximately 1500 hosts as reported by CERT Advisory CA-2001-20. This tool also uses IRC as the control channel. ...
... DOS program, the Tribe Flood Network is installed in compromised computers weeks or months before the attack. Another DDOS tool known as "Knight" was found on approximately 1500 hosts as reported by CERT Advisory CA-2001-20. This tool also uses IRC as the control channel. ...
Hotspot Shield Vpn Getjar
... Hotspot Shield Vpn Getjar - A virtual private network (VPN) extends a private network across a public network, such as the Internet. It enables a computer or network-enabled device to send and receive data across shared or public networks as if it were directly connected to the private network, whil ...
... Hotspot Shield Vpn Getjar - A virtual private network (VPN) extends a private network across a public network, such as the Internet. It enables a computer or network-enabled device to send and receive data across shared or public networks as if it were directly connected to the private network, whil ...
Cloudinomicon - Rational Survivability
... + Applications Are Likely Not Composable In This Manner As They Are More Topologically & Infrastructure-Insensitive Than Ever (See ...
... + Applications Are Likely Not Composable In This Manner As They Are More Topologically & Infrastructure-Insensitive Than Ever (See ...
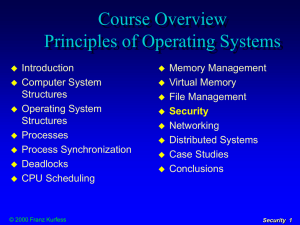
Security
... user writes a program that looks exactly like the login procedure for a multi-user system it is left on the terminal for the next unsuspecting user this program reads the password and stores it © 2000 Franz Kurfess ...
... user writes a program that looks exactly like the login procedure for a multi-user system it is left on the terminal for the next unsuspecting user this program reads the password and stores it © 2000 Franz Kurfess ...
WP- Evolution of Network Security
... several different port numbers in a brief period, or attempts to open sessions on a range of internal IP addresses, these are signs of scanning attempts. The firewall can deem this to be suspicious behaviour, and take action. Although TCP is the most session-oriented of the IP protocols, it is still ...
... several different port numbers in a brief period, or attempts to open sessions on a range of internal IP addresses, these are signs of scanning attempts. The firewall can deem this to be suspicious behaviour, and take action. Although TCP is the most session-oriented of the IP protocols, it is still ...
Introduction to Information Security Chapter N
... It does this by understanding how the protocol functions, and opening and closing “doors” in the firewall, based on the information contained in the packet header. In this manner, dynamic packet filters are an intermediate form, between traditional static packet filters and ...
... It does this by understanding how the protocol functions, and opening and closing “doors” in the firewall, based on the information contained in the packet header. In this manner, dynamic packet filters are an intermediate form, between traditional static packet filters and ...
Chapter 19: Malicious Logic - Welcome to nob.cs.ucdavis.edu!
... records when one particular record is deleted – The “particular record” is usually that of the person writing the logic bomb – Idea is if (when) he or she is fired, and the payroll record deleted, the company loses all those records November 1, 2004 ...
... records when one particular record is deleted – The “particular record” is usually that of the person writing the logic bomb – Idea is if (when) he or she is fired, and the payroll record deleted, the company loses all those records November 1, 2004 ...
Example: Data Mining for the NBA - The University of Texas at Dallas
... protection at various levels within a same system from the application layer down to the OS, Virtual Machine Monitor (VMM), and hardware. It is our contention that single-layer solutions typically improve one layer by pushing performance and security limitations to other layers, with questionable ov ...
... protection at various levels within a same system from the application layer down to the OS, Virtual Machine Monitor (VMM), and hardware. It is our contention that single-layer solutions typically improve one layer by pushing performance and security limitations to other layers, with questionable ov ...
Chapter 10
... electronically transmitted message that is used to verify the origin and contents of a message • Digital certificates: Data files used to establish the identity of users and electronic assets for protection of online transactions • Public Key Infrastructure (PKI): Use of public key cryptography work ...
... electronically transmitted message that is used to verify the origin and contents of a message • Digital certificates: Data files used to establish the identity of users and electronic assets for protection of online transactions • Public Key Infrastructure (PKI): Use of public key cryptography work ...
white paper - Nuage Networks
... The VSP solution is designed to enable communication only through established network policies (which ensure restricting access to only authorized networks/ services). ...
... The VSP solution is designed to enable communication only through established network policies (which ensure restricting access to only authorized networks/ services). ...
The Stuxnet Worm: Just Another Computer Attack or a Game
... First, wired and open societies are target-rich environments for cyber-theft, espionage or attack, against which they must protect themselves. ...
... First, wired and open societies are target-rich environments for cyber-theft, espionage or attack, against which they must protect themselves. ...