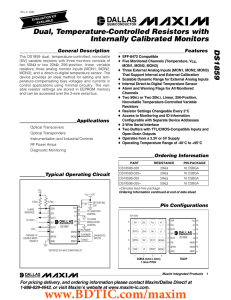
DS1859 Dual, Temperature-Controlled Resistors with Internally Calibrated Monitors General Description
... Each signal (VCC, MON1, MON2, MON3, and temperature) is available as a 16-bit value with 12-bit accuracy (left-justified) over the serial bus. See Table 1 for signal scales and Table 2 for signal format. The four LSBs should be masked when calculating the value. ...
... Each signal (VCC, MON1, MON2, MON3, and temperature) is available as a 16-bit value with 12-bit accuracy (left-justified) over the serial bus. See Table 1 for signal scales and Table 2 for signal format. The four LSBs should be masked when calculating the value. ...
MAX2880 General Description Benefits and Features
... General Description . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 1 ...
... General Description . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 1 ...
Virtual Ghost: Protecting Applications from Hostile Operating Systems
... contrast, previous systems like Overshadow [11] and InkTag [16] do not prevent such writes and only guarantee that the tampering will be detected before use by the application). Virtual Ghost introduces a thin hardware abstraction layer that provides a set of operations the kernel must use to manipu ...
... contrast, previous systems like Overshadow [11] and InkTag [16] do not prevent such writes and only guarantee that the tampering will be detected before use by the application). Virtual Ghost introduces a thin hardware abstraction layer that provides a set of operations the kernel must use to manipu ...
Memory Safety for Low-Level Software/Hardware Interactions
... is accessible by standard (even type-safe) load and store instructions. Any (buggy) code that modifies this state before restoring the state to the processor can alter control flow (the program counter, stack pointer, return address register, or condition code registers) or data values. In safe syst ...
... is accessible by standard (even type-safe) load and store instructions. Any (buggy) code that modifies this state before restoring the state to the processor can alter control flow (the program counter, stack pointer, return address register, or condition code registers) or data values. In safe syst ...
Memory Safety for Low-Level Software/Hardware Interactions
... is accessible by standard (even type-safe) load and store instructions. Any (buggy) code that modifies this state before restoring the state to the processor can alter control flow (the program counter, stack pointer, return address register, or condition code registers) or data values. In safe syst ...
... is accessible by standard (even type-safe) load and store instructions. Any (buggy) code that modifies this state before restoring the state to the processor can alter control flow (the program counter, stack pointer, return address register, or condition code registers) or data values. In safe syst ...
NOA1305 - Ambient Light Sensor with I2C Interface and Dark
... 1. Issue Start command 2. Issue 0x72 (lower seven bits of I2C slave address 0x39 followed by write−bit 0) 3. Issue 0x00 for the POWER_CONTROL register address 4. Issue 0x08 to put the device in the power on state 5. Issue Stop command After applying power to the device or after issuing a power−on co ...
... 1. Issue Start command 2. Issue 0x72 (lower seven bits of I2C slave address 0x39 followed by write−bit 0) 3. Issue 0x00 for the POWER_CONTROL register address 4. Issue 0x08 to put the device in the power on state 5. Issue Stop command After applying power to the device or after issuing a power−on co ...
DS1841 Temperature-Controlled, NV, I C, Logarithmic Resistor
... Logarithmic Resistor in the IVR is added to the values stored in the LUT. The dashed line/arrow shown in the LUT Drive Mode Block Diagram is not active in LUT Mode. When in LUT Mode, on power-up the IVR value is recalled into the WR. This value remains there until completion of the first temperature ...
... Logarithmic Resistor in the IVR is added to the values stored in the LUT. The dashed line/arrow shown in the LUT Drive Mode Block Diagram is not active in LUT Mode. When in LUT Mode, on power-up the IVR value is recalled into the WR. This value remains there until completion of the first temperature ...
cs0206 operating systems
... 1. Hardware – provides basic computing resources (CPU, memory, I/O devices). 2. Operating system – controls and coordinates the use of the hardware among the various application programs for the various users. 3. Applications programs – define the ways in which the system resources are used to solve ...
... 1. Hardware – provides basic computing resources (CPU, memory, I/O devices). 2. Operating system – controls and coordinates the use of the hardware among the various application programs for the various users. 3. Applications programs – define the ways in which the system resources are used to solve ...
DS1841 - Maxim Part Number Search
... Logarithmic Resistor in the IVR is added to the values stored in the LUT. The dashed line/arrow shown in the LUT Drive Mode Block Diagram is not active in LUT Mode. When in LUT Mode, on power-up the IVR value is recalled into the WR. This value remains there until completion of the first temperature ...
... Logarithmic Resistor in the IVR is added to the values stored in the LUT. The dashed line/arrow shown in the LUT Drive Mode Block Diagram is not active in LUT Mode. When in LUT Mode, on power-up the IVR value is recalled into the WR. This value remains there until completion of the first temperature ...
2300_Final_Sum2000
... ECE 2300 – Final Exam July 20, 2000 1. This exam is open book, open notes. 2. Show all work on these pages. Show all work necessary to complete the problem. If you go on to another page, indicate clearly where your work can be found. A solution without the work shown will receive no credit. 3. Show ...
... ECE 2300 – Final Exam July 20, 2000 1. This exam is open book, open notes. 2. Show all work on these pages. Show all work necessary to complete the problem. If you go on to another page, indicate clearly where your work can be found. A solution without the work shown will receive no credit. 3. Show ...
Bringing Virtualization to the x86 Architecture with the Original
... monitors (VMMs) had been around for decades, they were traditionally designed as part of monolithic, single-vendor architectures with explicit support for virtualization. In contrast, the x86 architecture lacked virtualization support, and the industry around it had disaggregated into an ecosystem, ...
... monitors (VMMs) had been around for decades, they were traditionally designed as part of monolithic, single-vendor architectures with explicit support for virtualization. In contrast, the x86 architecture lacked virtualization support, and the industry around it had disaggregated into an ecosystem, ...
Bringing Virtualization to the x86 Architecture with
... monitors (VMMs) had been around for decades, they were traditionally designed as part of monolithic, single-vendor architectures with explicit support for virtualization. In contrast, the x86 architecture lacked virtualization support, and the industry around it had disaggregated into an ecosystem, ...
... monitors (VMMs) had been around for decades, they were traditionally designed as part of monolithic, single-vendor architectures with explicit support for virtualization. In contrast, the x86 architecture lacked virtualization support, and the industry around it had disaggregated into an ecosystem, ...
COA 2
... together to form Computer system. b. The determination of what hardware should be used and how the parts be connected. c. The structure and behavior of the computer as seen by the user. d. Design of electronic components of computer. 4. Computer architecture is concerned with a. The way hardware com ...
... together to form Computer system. b. The determination of what hardware should be used and how the parts be connected. c. The structure and behavior of the computer as seen by the user. d. Design of electronic components of computer. 4. Computer architecture is concerned with a. The way hardware com ...
operating system functions
... 1. All the resources are shared amongst a no of user’s who are not a ware of such sharing. ...
... 1. All the resources are shared amongst a no of user’s who are not a ware of such sharing. ...
CS-703 Advance Operating Systems
... • C/C++ programming. This is an essential pre-requisite since without this; you won‘t be able to do the assignments. • An undergraduate first course on data structures. This should include implementation of elementary data structures e.g. lists, stack, queues, trees etc. in a high level language lik ...
... • C/C++ programming. This is an essential pre-requisite since without this; you won‘t be able to do the assignments. • An undergraduate first course on data structures. This should include implementation of elementary data structures e.g. lists, stack, queues, trees etc. in a high level language lik ...
Virtual Machine Monitors Dr. Marc E. Fiuczynski Research Scholar Princeton University
... Translator, which emulates problematic instructions Fast compared to other binary translators as source and destination instruction sets are nearly identical Fiuczynski -- cs318 ...
... Translator, which emulates problematic instructions Fast compared to other binary translators as source and destination instruction sets are nearly identical Fiuczynski -- cs318 ...
STK300 USER MANUAL
... The code to be programmed into the device is loaded into this buffer by the File, Load, EEPROM option, or read from the device by the Device - Read - EEPROM option. The size of the buffer changes to mirror the EEPROM memory size on the selected device. If Device, Verify, EEPROM is used, the contents ...
... The code to be programmed into the device is loaded into this buffer by the File, Load, EEPROM option, or read from the device by the Device - Read - EEPROM option. The size of the buffer changes to mirror the EEPROM memory size on the selected device. If Device, Verify, EEPROM is used, the contents ...
Making Sense of Effective Bits in Oscilloscope Measurements
... directly, without having to set up a histogram manually. It is important not to include the DC offset in this measurement, so histograms or AC RMS measurements must be used. The Figure 5 screen capture shows a baseline noise measurement. Figure 6 shows a comparison of baseline noise for the Tektroni ...
... directly, without having to set up a histogram manually. It is important not to include the DC offset in this measurement, so histograms or AC RMS measurements must be used. The Figure 5 screen capture shows a baseline noise measurement. Figure 6 shows a comparison of baseline noise for the Tektroni ...
Document
... 11. What are the common strategies to select a free hole from a set of available holes? ...
... 11. What are the common strategies to select a free hole from a set of available holes? ...
Secure Virtualization for an Ever Increasing Vehicle
... Typically the user level access mode forbade direct hardware access as well as access to a number of the on-board processor registers. For example, it could have fatal consequences if an arbitrary user program were to modify the contents of the memory protection unit. This is an operation that is re ...
... Typically the user level access mode forbade direct hardware access as well as access to a number of the on-board processor registers. For example, it could have fatal consequences if an arbitrary user program were to modify the contents of the memory protection unit. This is an operation that is re ...
Disco: Running Commodity Operating Systems on Scalable
... ware. Operations such as the execution of privileged instructions cannot be safely exported directly to the operating system and must be emulated in software by the monitor. Similarly, the access to I/O devices is virtualized, so requests must be intercepted and remapped by the monitor. In addition ...
... ware. Operations such as the execution of privileged instructions cannot be safely exported directly to the operating system and must be emulated in software by the monitor. Similarly, the access to I/O devices is virtualized, so requests must be intercepted and remapped by the monitor. In addition ...
Chapter 1 – 15 Essay Question Review
... term scheduler must be fast. The long-term scheduler executes much less frequently; minutes may separate the creation of one new process and the next. The long-term scheduler controls the degree of multiprogramming. Because of the longer interval between executions, the long-term scheduler can affor ...
... term scheduler must be fast. The long-term scheduler executes much less frequently; minutes may separate the creation of one new process and the next. The long-term scheduler controls the degree of multiprogramming. Because of the longer interval between executions, the long-term scheduler can affor ...
Adopting and Commenting the Old Kernel Source Code for Education
... first read into the cache area from the block device. When a task needs to output the data to a block device, the data is put into the cache area first and then is written into the block device by the hardware driver in due time. The last part of the physical memory is the main area used dynamically ...
... first read into the cache area from the block device. When a task needs to output the data to a block device, the data is put into the cache area first and then is written into the block device by the hardware driver in due time. The last part of the physical memory is the main area used dynamically ...
DS3503 NV, I C, Stepper Potentiometer 2
... and Y potentiometers (see the Stepping section). The five LSBs, bits 4:0, control the STEPCOUNT, which is the number of steps up and down the wiper moves when stepping is enabled. Bits 5 and 6 control the PERIOD, which is the number of pulses of the SYNC pin required to perform one step. Setting STE ...
... and Y potentiometers (see the Stepping section). The five LSBs, bits 4:0, control the STEPCOUNT, which is the number of steps up and down the wiper moves when stepping is enabled. Bits 5 and 6 control the PERIOD, which is the number of pulses of the SYNC pin required to perform one step. Setting STE ...
Lecture 1 - The Laboratory for Advanced Systems Research
... • It is always in control of the hardware – Automatically loaded when the machine boots – First software to have access to hardware – Continues running while apps come & go ...
... • It is always in control of the hardware – Automatically loaded when the machine boots – First software to have access to hardware – Continues running while apps come & go ...
Memory management unit

A memory management unit (MMU), sometimes called paged memory management unit (PMMU), is a computer hardware unit having all memory references passed through itself, primarily performing the translation of virtual memory addresses to physical addresses. It is usually implemented as part of the central processing unit (CPU), but it also can be in the form of a separate integrated circuit.An MMU effectively performs virtual memory management, handling at the same time memory protection, cache control, bus arbitration and, in simpler computer architectures (especially 8-bit systems), bank switching.