슬라이드 1 - Dankook
... No shadow pages (VMWare) Xen provides constrained but direct MMU updates All guest OSes have read-only accesses to page tables Updates are batched into a single hypercall Updates must be validated by Xen Guest OSes are responsible for allocation and managing pages within their own domain Xen exists ...
... No shadow pages (VMWare) Xen provides constrained but direct MMU updates All guest OSes have read-only accesses to page tables Updates are batched into a single hypercall Updates must be validated by Xen Guest OSes are responsible for allocation and managing pages within their own domain Xen exists ...
Lecture 1 - inst.eecs.berkeley.edu
... – Does the programmer need to write a single program that performs many independent activities? – Does every program have to be altered for every ...
... – Does the programmer need to write a single program that performs many independent activities? – Does every program have to be altered for every ...
lecture1423726024
... devices accept them. It is also use for processing data at remote sides. The remote processing is done and its own speed with no CPU intervention. Spooling overlaps the input, output one job with computation of other jobs. Spooling has a beneficial effect on the performance of the systems by keeping ...
... devices accept them. It is also use for processing data at remote sides. The remote processing is done and its own speed with no CPU intervention. Spooling overlaps the input, output one job with computation of other jobs. Spooling has a beneficial effect on the performance of the systems by keeping ...
SimOS: A Fast Operating System Simulation Environment
... notification mechanism, allow a process to get control of such exception events as illegal instructions, bad memory references, and external notifications (such as interrupts.) Unix signals save the processor state and jump to the user specified routine for that signal. Most of the events that cause ...
... notification mechanism, allow a process to get control of such exception events as illegal instructions, bad memory references, and external notifications (such as interrupts.) Unix signals save the processor state and jump to the user specified routine for that signal. Most of the events that cause ...
lecture1422914790
... CPU to process data from disk. Those data must first be transferred to main memory by CPU generated E/O calls. Instruction must be in memory for the CPU to execute them. The OS is responsible for the following activities in connection with memory management. Keeping track of which parts of memory ar ...
... CPU to process data from disk. Those data must first be transferred to main memory by CPU generated E/O calls. Instruction must be in memory for the CPU to execute them. The OS is responsible for the following activities in connection with memory management. Keeping track of which parts of memory ar ...
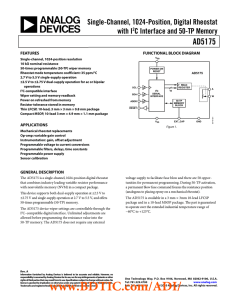
AD5175: 数据手册DataSheet 下载
... Programmable voltage to current conversions Programmable filters, delays, time constants Programmable power supply Sensor calibration ...
... Programmable voltage to current conversions Programmable filters, delays, time constants Programmable power supply Sensor calibration ...
experiment no 4
... The output of the operation is on the form of the magnitude and sign bit. The seven least significant bits represent the magnitude of the operation, and the eighth significant bit (MSB) represent the sign bit or carry. If a carry out(1) is generated out of the MSB, the number is positive and in tru ...
... The output of the operation is on the form of the magnitude and sign bit. The seven least significant bits represent the magnitude of the operation, and the eighth significant bit (MSB) represent the sign bit or carry. If a carry out(1) is generated out of the MSB, the number is positive and in tru ...
pptx
... an abnormal heart rhythm, due to changes in the conduction of electrical impulses through the heart. Pacemakers: use low-energy electrical pulses to overcome this abnormality. They create forced rhythms according to natural human heart beats, to let the heart to function in a normal manner. ...
... an abnormal heart rhythm, due to changes in the conduction of electrical impulses through the heart. Pacemakers: use low-energy electrical pulses to overcome this abnormality. They create forced rhythms according to natural human heart beats, to let the heart to function in a normal manner. ...
ERROR DETECTION AND CORRECTION
... desired. This material fits well with the desired coverage in some programs but not may not fit within others due to time constraints or local preferences. This supplement is referenced in Chapter 9 as a part of the coverage of memories. Error detection and correction codes serve as a basis for erro ...
... desired. This material fits well with the desired coverage in some programs but not may not fit within others due to time constraints or local preferences. This supplement is referenced in Chapter 9 as a part of the coverage of memories. Error detection and correction codes serve as a basis for erro ...
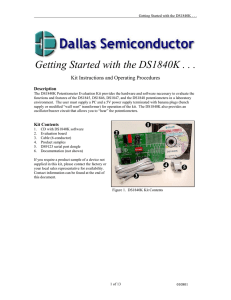
DS1840KGettingStarte..
... The default for these first 4 switches is the “ON” position. This corresponds to a device address of 000h and NO write protection. The DS1847 and the DS1848 contain two temperature-controlled variable resistors (not potentiometers). Each device offers a temperature-controlled mode, as well as a manu ...
... The default for these first 4 switches is the “ON” position. This corresponds to a device address of 000h and NO write protection. The DS1847 and the DS1848 contain two temperature-controlled variable resistors (not potentiometers). Each device offers a temperature-controlled mode, as well as a manu ...
ARMvisor: System Virtualization for ARM
... and allow hypervisor to manage the resource of system, guest operating system is de-privileged to execute in non-privilege mode while hypervisor is located in privilege level for resource management. Pure virtualization that executes guest OS directly in user mode is proposed under the premise that ...
... and allow hypervisor to manage the resource of system, guest operating system is de-privileged to execute in non-privilege mode while hypervisor is located in privilege level for resource management. Pure virtualization that executes guest OS directly in user mode is proposed under the premise that ...
Modern Operating System - Tanenbaum solution 3rd
... 2. You could have a register containing a pointer to the current process table entry. When I/O completed, the CPU would store the current machine state in the current process table entry. Then it would go to the interrupt vector for the interrupting device and fetch a pointer to another process tabl ...
... 2. You could have a register containing a pointer to the current process table entry. When I/O completed, the CPU would store the current machine state in the current process table entry. Then it would go to the interrupt vector for the interrupting device and fetch a pointer to another process tabl ...
ch8
... 3. (1, 0) recently used but clean – probably will be used again soon 4. (1, 1) recently used and modified – probably will be used again ...
... 3. (1, 0) recently used but clean – probably will be used again soon 4. (1, 1) recently used and modified – probably will be used again ...
EN_C2_Eng - BCS Koolitus
... The concept of concurrency exists is several daily activities. For example it is possible at the same time to cook and to write a letter: if the water boils while writing the letter, it is possible to stop writing, put the pasta in the water and then start writing again. The two activities (cooking ...
... The concept of concurrency exists is several daily activities. For example it is possible at the same time to cook and to write a letter: if the water boils while writing the letter, it is possible to stop writing, put the pasta in the water and then start writing again. The two activities (cooking ...
Silberschatz_ AllNotes
... o process creation and management (e.g. running a program) o I/O handling (e.g. set terminal type) o secondary-storage management (e.g. format a disk) o main-memory management (e.g. specify virtual memory parameters) o file-system access (e.g. print file) o protection (e.g. set permissions) o networ ...
... o process creation and management (e.g. running a program) o I/O handling (e.g. set terminal type) o secondary-storage management (e.g. format a disk) o main-memory management (e.g. specify virtual memory parameters) o file-system access (e.g. print file) o protection (e.g. set permissions) o networ ...
Chapter 9 - cse.sc.edu
... Demand page in from program binary on disk, but discard rather than paging out when freeing frame ...
... Demand page in from program binary on disk, but discard rather than paging out when freeing frame ...
Chap. 9, Virtual Memory Management
... When page replacement called for, use the clock scheme but use the four classes replace page in lowest non-empty class ...
... When page replacement called for, use the clock scheme but use the four classes replace page in lowest non-empty class ...
Operating System
... information incorrectly, computer B might not be able to read the data and a protocol error would arise. More generally, a protocol is an agreed sequence of behavior which must be followed. For example, when passing parameters to functions in a computer program, there are rules about how the paramet ...
... information incorrectly, computer B might not be able to read the data and a protocol error would arise. More generally, a protocol is an agreed sequence of behavior which must be followed. For example, when passing parameters to functions in a computer program, there are rules about how the paramet ...
Difference between extended and expanded memory
... processor architectures. For details of x86's implementation of segmentation in both 16-bit and 32-bit mode, please see the article on memory segments. Segmentation is a memory-management scheme that supports this user view of memory. A logical address space is a collection of segments. Each segment ...
... processor architectures. For details of x86's implementation of segmentation in both 16-bit and 32-bit mode, please see the article on memory segments. Segmentation is a memory-management scheme that supports this user view of memory. A logical address space is a collection of segments. Each segment ...
Memory - UNL CSE
... • If plan for VM during design of ISA, easy to reduce instructions executed by VMM, speed to emulate – ISA is virtualizable if can execute VM directly on real machine while letting VMM retain ultimate control of CPU: “direct execution” – Since VMs have been considered for desktop/PC server apps only ...
... • If plan for VM during design of ISA, easy to reduce instructions executed by VMM, speed to emulate – ISA is virtualizable if can execute VM directly on real machine while letting VMM retain ultimate control of CPU: “direct execution” – Since VMs have been considered for desktop/PC server apps only ...
Computer System Overview
... The unit of data exchanged between cache and main memory Larger block size more hits until probability of using newly fetched data becomes less than the probability of reusing data that have to be moved out of cache ...
... The unit of data exchanged between cache and main memory Larger block size more hits until probability of using newly fetched data becomes less than the probability of reusing data that have to be moved out of cache ...
Notes
... Programmer – Uses languages, utilities (frequently used functions) and OS services (linkers, assemblers, etc.) to develop applications instead. This method is used to reduce complexity by abstracting the detail of machine dependant calls into APIs and various utilities and OS services. OS – Masks th ...
... Programmer – Uses languages, utilities (frequently used functions) and OS services (linkers, assemblers, etc.) to develop applications instead. This method is used to reduce complexity by abstracting the detail of machine dependant calls into APIs and various utilities and OS services. OS – Masks th ...
Chapter 8: Virtual Memory
... Error code, unusual routines (yearly basis), large data structures (arrays, lists, and tables) ...
... Error code, unusual routines (yearly basis), large data structures (arrays, lists, and tables) ...
Memory management unit

A memory management unit (MMU), sometimes called paged memory management unit (PMMU), is a computer hardware unit having all memory references passed through itself, primarily performing the translation of virtual memory addresses to physical addresses. It is usually implemented as part of the central processing unit (CPU), but it also can be in the form of a separate integrated circuit.An MMU effectively performs virtual memory management, handling at the same time memory protection, cache control, bus arbitration and, in simpler computer architectures (especially 8-bit systems), bank switching.