Silberschatz, Galvin and Gagne ©2011 Operating System Concepts
... Error code, unusual routines (yearly basis), large data structures (arrays, lists, and tables) ...
... Error code, unusual routines (yearly basis), large data structures (arrays, lists, and tables) ...
Chapter 9: Virtual Memory
... 10. Correct the page table and other tables to show page is now in memory 11. Wait for the CPU to be allocated to this process again 12. Restore the user registers, process state, and new page table, and then resume the ...
... 10. Correct the page table and other tables to show page is now in memory 11. Wait for the CPU to be allocated to this process again 12. Restore the user registers, process state, and new page table, and then resume the ...
ppt
... 10. Correct the page table and other tables to show page is now in memory 11. Wait for the CPU to be allocated to this process again 12. Restore the user registers, process state, and new page table, and then resume the ...
... 10. Correct the page table and other tables to show page is now in memory 11. Wait for the CPU to be allocated to this process again 12. Restore the user registers, process state, and new page table, and then resume the ...
CIF: Criswell Information Flow
... • But Malicious OS can examine/modify any data in memory • Need an agent to control a potentially malicious OS • Need something below the OS! ...
... • But Malicious OS can examine/modify any data in memory • Need an agent to control a potentially malicious OS • Need something below the OS! ...
Chapter 9: Virtual Memory
... 10. Correct the page table and other tables to show page is now in memory 11. Wait for the CPU to be allocated to this process again 12. Restore the user registers, process state, and new page table, and then resume the ...
... 10. Correct the page table and other tables to show page is now in memory 11. Wait for the CPU to be allocated to this process again 12. Restore the user registers, process state, and new page table, and then resume the ...
Operating Systems. Memory Management
... Swapping is possible only if processes return to the same memory positions they used before being swapped out (fixed partitions) ...
... Swapping is possible only if processes return to the same memory positions they used before being swapped out (fixed partitions) ...
Protected, User-Level DMA for the SHRIMP Network Interface
... mechanism uses virtual memory mapping to allow user processes to start DMA operations via a pair of ordinary load and store instructions. UDMA uses the existing virtual memory mechanisms { address translation and permission checking { to provide the same degree of protection as the traditional DMA o ...
... mechanism uses virtual memory mapping to allow user processes to start DMA operations via a pair of ordinary load and store instructions. UDMA uses the existing virtual memory mechanisms { address translation and permission checking { to provide the same degree of protection as the traditional DMA o ...
DDR4 Memory Technology on HP Z Workstations
... buffer register in the case of RDIMMs and LR DIMMs, and various discrete components. The DRAM chips used define the principal characteristics of a DIMM. DRAM characteristics Dynamic Random Access Memory (DRAM) chips come in different capacities. Today, 4 Gigabit (Gb) DRAMs are the most common and co ...
... buffer register in the case of RDIMMs and LR DIMMs, and various discrete components. The DRAM chips used define the principal characteristics of a DIMM. DRAM characteristics Dynamic Random Access Memory (DRAM) chips come in different capacities. Today, 4 Gigabit (Gb) DRAMs are the most common and co ...
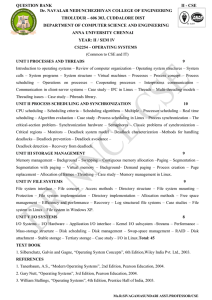
modelpaper
... assuming one, six or seven frames? Remember that all frames are initially empty, so your first unique page with all cost one fault each. LRU replacement FIFO replacement Optimal replacement 22.Describe the functioning of Multi-Level Paging Technique? How it is different from Simple Paging? 23.Why it ...
... assuming one, six or seven frames? Remember that all frames are initially empty, so your first unique page with all cost one fault each. LRU replacement FIFO replacement Optimal replacement 22.Describe the functioning of Multi-Level Paging Technique? How it is different from Simple Paging? 23.Why it ...
Andes Technology PPT Temp
... will be a "sealed box" when delivered for use. A very important part of an RTOS is managing the resources of the computer so that a particular operation executes in precisely the same amount of time, every time it occurs. In a complex machine, having a part move more quickly just because system ...
... will be a "sealed box" when delivered for use. A very important part of an RTOS is managing the resources of the computer so that a particular operation executes in precisely the same amount of time, every time it occurs. In a complex machine, having a part move more quickly just because system ...
Solution Operating System Concepts By Galvin,Silberschatz Solved
... The primary difference is that kernel-level context switches involve execution of OS code. As such it requires crossing the boundary between user- and kernel-land two times. When the kernel is switching between two different address spaces it must store the registers as well as the address space. Sa ...
... The primary difference is that kernel-level context switches involve execution of OS code. As such it requires crossing the boundary between user- and kernel-land two times. When the kernel is switching between two different address spaces it must store the registers as well as the address space. Sa ...
RAJALAKSHMI ENGINEERING COLLEGE
... A more common definition is that the OS is the one program running at all times on the computer, usually called the kernel, with all else being application programs. 24. What are Batch systems? Batch systems are quite appropriate for executing large jobs that need little interaction. The user can su ...
... A more common definition is that the OS is the one program running at all times on the computer, usually called the kernel, with all else being application programs. 24. What are Batch systems? Batch systems are quite appropriate for executing large jobs that need little interaction. The user can su ...
3.1 What are the five major activities of an operating system in
... 3.9 The main advantage of the layered approach to operating systems design is that debugging and testing are simplified. The layers are designed so that each uses only lower-level services. The interface between the layers is well defined, and encapsulates the implementation details of each level fr ...
... 3.9 The main advantage of the layered approach to operating systems design is that debugging and testing are simplified. The layers are designed so that each uses only lower-level services. The interface between the layers is well defined, and encapsulates the implementation details of each level fr ...
physics department
... (2) Print your name on this sheet and sign it also. (3) Do all scratch work anywhere on this exam that you like. Circle your answers on the test form. At the end of the test, this exam printout is to be turned in. No credit will be given without both answer sheet and printout. (4) Blacken the circle ...
... (2) Print your name on this sheet and sign it also. (3) Do all scratch work anywhere on this exam that you like. Circle your answers on the test form. At the end of the test, this exam printout is to be turned in. No credit will be given without both answer sheet and printout. (4) Blacken the circle ...
IA-32 Architecture
... Introduced in 2004 64-bit superset of the IA-32 processor architecture 64-bit general-purpose registers and integer support Number of general-purpose registers increased from 8 to 16 64-bit pointers and flat virtual address space Large physical address space: up to 240 = 1 Terabytes IA-3 ...
... Introduced in 2004 64-bit superset of the IA-32 processor architecture 64-bit general-purpose registers and integer support Number of general-purpose registers increased from 8 to 16 64-bit pointers and flat virtual address space Large physical address space: up to 240 = 1 Terabytes IA-3 ...
Chapter 9: Virtual Memory Silberschatz, Galvin and Gagne ©2013! Edition!
... 10. Correct the page table and other tables to show page is now in memory" 11. Wait for the CPU to be allocated to this process again" 12. Restore the user registers, process state, and new page table, and then resume the ...
... 10. Correct the page table and other tables to show page is now in memory" 11. Wait for the CPU to be allocated to this process again" 12. Restore the user registers, process state, and new page table, and then resume the ...
IA-32 Processor Architecture
... Memory responds much more slowly than the CPU Address is placed on address bus Read Line (RD) goes low, indicating that processor wants to read CPU waits (one or more cycles) for memory to respond Read Line (RD) goes high, indicating that data is on the data bus ...
... Memory responds much more slowly than the CPU Address is placed on address bus Read Line (RD) goes low, indicating that processor wants to read CPU waits (one or more cycles) for memory to respond Read Line (RD) goes high, indicating that data is on the data bus ...
File
... that is considered abnormal; for example, a user program that attempts to divide by zero. It may also be generated by a running process that issues a service request from the operating system; for example, a program that attempts to access protected memory or execute a privileged instruction. A trap ...
... that is considered abnormal; for example, a user program that attempts to divide by zero. It may also be generated by a running process that issues a service request from the operating system; for example, a program that attempts to access protected memory or execute a privileged instruction. A trap ...
Modern Operating System by Tanenbaum
... instruction. The word fetched could also span a page boundary, generating two more faults, for a total of four. If words must be aligned in memory, the data word can cause only one fault, but an instruction to load a 32-bit word at address 4094 on a machine with a 4-KB page is legal on some machines ...
... instruction. The word fetched could also span a page boundary, generating two more faults, for a total of four. If words must be aligned in memory, the data word can cause only one fault, but an instruction to load a 32-bit word at address 4094 on a machine with a 4-KB page is legal on some machines ...
Computer System Arch..
... for this segment. Overcomes external fragmentation problem of segmented memory. Paging also makes allocation simpler; time to search for a suitable segment (using best-fit etc.) reduced. Introduces some internal fragmentation and table space overhead. ...
... for this segment. Overcomes external fragmentation problem of segmented memory. Paging also makes allocation simpler; time to search for a suitable segment (using best-fit etc.) reduced. Introduces some internal fragmentation and table space overhead. ...
Operating Systems II
... Hardware Support for Operating Systems Recall that OS should securely multiplex resources. ⇒ we need to ensure that an application cannot: • compromise the operating system. • compromise other applications. • deny others service (e.g. abuse resources) To achieve this efficiently and flexibly, we ne ...
... Hardware Support for Operating Systems Recall that OS should securely multiplex resources. ⇒ we need to ensure that an application cannot: • compromise the operating system. • compromise other applications. • deny others service (e.g. abuse resources) To achieve this efficiently and flexibly, we ne ...
Operating Systems
... • Also usually want to abstract away from grungy harware, i.e. OS provides a virtual machine: – share CPU (in time) and provide each app with a virtual processor, – allocate and protect memory, and provide applications with their own virtual address space, – present a set of (relatively) hardware in ...
... • Also usually want to abstract away from grungy harware, i.e. OS provides a virtual machine: – share CPU (in time) and provide each app with a virtual processor, – allocate and protect memory, and provide applications with their own virtual address space, – present a set of (relatively) hardware in ...
Processes and OS Basics
... • What are the advantages of using Virtual Memory address spaces? • What happens if the running processes use more virtual memory than the amount of available physical memory? • What is a page hit? a page fault? • Why should the OS try to minimise the number of page faults? • Can you think of other ...
... • What are the advantages of using Virtual Memory address spaces? • What happens if the running processes use more virtual memory than the amount of available physical memory? • What is a page hit? a page fault? • Why should the OS try to minimise the number of page faults? • Can you think of other ...
Physics Definitions - Dominican
... Energy The ability to do work. Energy is neither created nor destroyed but can be converted from one form to another. ...
... Energy The ability to do work. Energy is neither created nor destroyed but can be converted from one form to another. ...
Memory management unit

A memory management unit (MMU), sometimes called paged memory management unit (PMMU), is a computer hardware unit having all memory references passed through itself, primarily performing the translation of virtual memory addresses to physical addresses. It is usually implemented as part of the central processing unit (CPU), but it also can be in the form of a separate integrated circuit.An MMU effectively performs virtual memory management, handling at the same time memory protection, cache control, bus arbitration and, in simpler computer architectures (especially 8-bit systems), bank switching.