DS3503 - Maxim Part Number Search
... and Y potentiometers (see the Stepping section). The five LSBs, bits 4:0, control the STEPCOUNT, which is the number of steps up and down the wiper moves when stepping is enabled. Bits 5 and 6 control the PERIOD, which is the number of pulses of the SYNC pin required to perform one step. Setting STE ...
... and Y potentiometers (see the Stepping section). The five LSBs, bits 4:0, control the STEPCOUNT, which is the number of steps up and down the wiper moves when stepping is enabled. Bits 5 and 6 control the PERIOD, which is the number of pulses of the SYNC pin required to perform one step. Setting STE ...
Running Commodity Operating Systems on Scalable Multiprocessors
... operating systems for resource-intensive applications that do not need the full functionality of the commodity operating systems. These simpler, specialized operating systems better support the needs of the applications and can easily scale to the size of the machine. For example, a virtual machine ...
... operating systems for resource-intensive applications that do not need the full functionality of the commodity operating systems. These simpler, specialized operating systems better support the needs of the applications and can easily scale to the size of the machine. For example, a virtual machine ...
1 Introduction 2 Problem Description Disco: Running Commodity
... operating systems for resource-intensive applications that do not need the full functionality of the commodity operating systems. These simpler, specialized operating systems better support the needs of the applications and can easily scale to the size of the machine. For example, a virtual machine ...
... operating systems for resource-intensive applications that do not need the full functionality of the commodity operating systems. These simpler, specialized operating systems better support the needs of the applications and can easily scale to the size of the machine. For example, a virtual machine ...
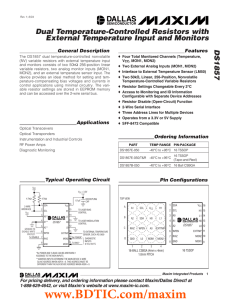
DS1857 Dual Temperature-Controlled Resistors with External Temperature Input and Monitors General Description
... Note 2: I/O pins of fast-mode devices must not obstruct the SDA and SCL lines if VCC is switched off. The address inputs should be connected to either VCC or GND depending on the desired address setting. Note 3: SDA and SCL are connected to VCC and all other input signals are connected to well-defin ...
... Note 2: I/O pins of fast-mode devices must not obstruct the SDA and SCL lines if VCC is switched off. The address inputs should be connected to either VCC or GND depending on the desired address setting. Note 3: SDA and SCL are connected to VCC and all other input signals are connected to well-defin ...
Now You See Me: Hide and Seek in Physical Address Space
... defeat existing memory forensic techniques by manipulation of system software such as OS kernel. To counter anti-forensic techniques, some recent researches suggest that memory acquisition process can be trusted if the acquisition module has not been tampered with and all the operations are performe ...
... defeat existing memory forensic techniques by manipulation of system software such as OS kernel. To counter anti-forensic techniques, some recent researches suggest that memory acquisition process can be trusted if the acquisition module has not been tampered with and all the operations are performe ...
c. omflip - PALMS - Princeton University
... There are many ways to implement a GRP operation. Here, we describe a parallel implementation. For convenience, the bits in Rs with a control bit of 0 are referred to as z bits, and the bits with control bit of 1 as w bits. The GRP operation can be performed in three conceptual steps. Step 1 grabs a ...
... There are many ways to implement a GRP operation. Here, we describe a parallel implementation. For convenience, the bits in Rs with a control bit of 0 are referred to as z bits, and the bits with control bit of 1 as w bits. The GRP operation can be performed in three conceptual steps. Step 1 grabs a ...
NTE21256 262,144–Bit Dynamic Random Access Memory (DRAM)
... Nine multiplexed address inputs permit the NTE21256 to be packaged in an industry standard 16–Lead DIP package. Features of this device include single power supply with ±10% tolerance, on– chip address, date registers which eliminate the need for interface registers, and fully TTL compatible inputs ...
... Nine multiplexed address inputs permit the NTE21256 to be packaged in an industry standard 16–Lead DIP package. Features of this device include single power supply with ±10% tolerance, on– chip address, date registers which eliminate the need for interface registers, and fully TTL compatible inputs ...
Operating System
... A time-shared operating system allows the many users to share the computer simultaneously. Since each action or command in a time-shared system tends to be short, only a little CPU time is needed for each user. As the system switches rapidly from one user to the next, each user is given the impressi ...
... A time-shared operating system allows the many users to share the computer simultaneously. Since each action or command in a time-shared system tends to be short, only a little CPU time is needed for each user. As the system switches rapidly from one user to the next, each user is given the impressi ...
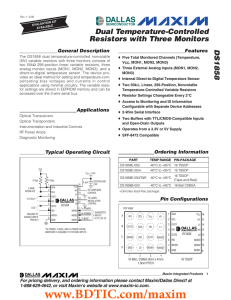
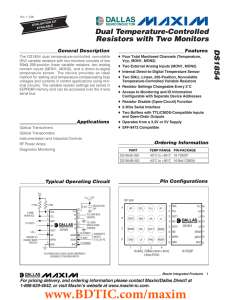
DS1858 Dual Temperature-Controlled Resistors with Three Monitors General Description
... I/O pins of fast-mode devices must not obstruct the SDA and SCL lines if VCC is switched off. SDA and SCL are connected to VCC and all other input signals are connected to well-defined logic levels. The maximum voltage the MON inputs will read is approximately 2.5V, even if the voltage on the inputs ...
... I/O pins of fast-mode devices must not obstruct the SDA and SCL lines if VCC is switched off. SDA and SCL are connected to VCC and all other input signals are connected to well-defined logic levels. The maximum voltage the MON inputs will read is approximately 2.5V, even if the voltage on the inputs ...
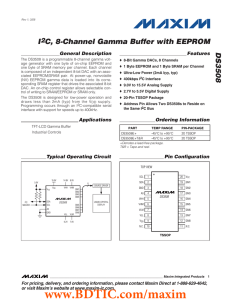
DS3508 I C, 8-Channel Gamma Buffer with EEPROM 2
... The DS3508 is a programmable 8-channel gamma voltage generator with one byte of on-chip EEPROM and one byte of SRAM memory per channel. Each channel is composed of an independent 8-bit DAC with an associated EEPROM/SRAM pair. At power-up, nonvolatile (NV) EEPROM gamma data is loaded into its corresp ...
... The DS3508 is a programmable 8-channel gamma voltage generator with one byte of on-chip EEPROM and one byte of SRAM memory per channel. Each channel is composed of an independent 8-bit DAC with an associated EEPROM/SRAM pair. At power-up, nonvolatile (NV) EEPROM gamma data is loaded into its corresp ...
DS1858 Dual Temperature-Controlled Resistors with Three Monitors
... I/O pins of fast-mode devices must not obstruct the SDA and SCL lines if VCC is switched off. SDA and SCL are connected to VCC and all other input signals are connected to well-defined logic levels. The maximum voltage the MON inputs will read is approximately 2.5V, even if the voltage on the inputs ...
... I/O pins of fast-mode devices must not obstruct the SDA and SCL lines if VCC is switched off. SDA and SCL are connected to VCC and all other input signals are connected to well-defined logic levels. The maximum voltage the MON inputs will read is approximately 2.5V, even if the voltage on the inputs ...
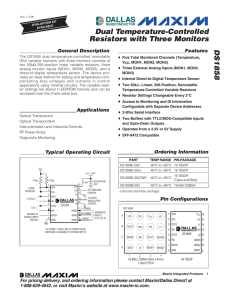
DS1854 Dual Temperature-Controlled Resistors with Two Monitors General Description
... The user can read the registers that monitor the VCC, MON1, MON2, and temperature analog signals. After each signal conversion, a corresponding bit is set that can be monitored to verify that a conversion has occurred. The signals also have alarm flags that notify the user when the signals go above ...
... The user can read the registers that monitor the VCC, MON1, MON2, and temperature analog signals. After each signal conversion, a corresponding bit is set that can be monitored to verify that a conversion has occurred. The signals also have alarm flags that notify the user when the signals go above ...
Virtual Machines
... Access rights for code limited to segments of same or lower privilege Copied into code segment selector (pointer to segment via descriptor) ...
... Access rights for code limited to segments of same or lower privilege Copied into code segment selector (pointer to segment via descriptor) ...
CY7C106D/CY7C1006D, 1-Mbit (256 K × 4) Static RAM
... © Cypress Semiconductor Corporation, 2004-2014. The information contained herein is subject to change without notice. Cypress Semiconductor Corporation assumes no responsibility for the use of any circuitry other than circuitry embodied in a Cypress product. Nor does it convey or imply any license u ...
... © Cypress Semiconductor Corporation, 2004-2014. The information contained herein is subject to change without notice. Cypress Semiconductor Corporation assumes no responsibility for the use of any circuitry other than circuitry embodied in a Cypress product. Nor does it convey or imply any license u ...
1.) Process is A.) program in High level language kept on disk B
... Q.65To avoid race condition, the maximum number ofprocesses that may be simultaneously inside the critical section is (A)zero (B)one (C)two (D)more than two Ans: (B) Q.66 The memory allocation scheme subject to “external”fragmentation is (A)segmentation (B)swapping (C) pure demand paging (D)multiple ...
... Q.65To avoid race condition, the maximum number ofprocesses that may be simultaneously inside the critical section is (A)zero (B)one (C)two (D)more than two Ans: (B) Q.66 The memory allocation scheme subject to “external”fragmentation is (A)segmentation (B)swapping (C) pure demand paging (D)multiple ...
8 Mbit / 16 Mbit Single Operation Voltage
... corresponding memory area is protected. Any program The function of Status Register bits are described as or erase operation to that area will be inhibited. Note: follows: a Chip Erase (CHIP_ER) instruction is executed successfully only if all the Block Protection Bits are set WIP bit: The Write In ...
... corresponding memory area is protected. Any program The function of Status Register bits are described as or erase operation to that area will be inhibited. Note: follows: a Chip Erase (CHIP_ER) instruction is executed successfully only if all the Block Protection Bits are set WIP bit: The Write In ...
Disco: Running Commodity Operating Systems on Scalable Multiprocessors
... operating systems for resource-intensive applications that do not need the full functionality of the commodity operating systems. These simpler, specialized operating systems better support the needs of the applications and can easily scale to the size of the machine. For example, a virtual machine ...
... operating systems for resource-intensive applications that do not need the full functionality of the commodity operating systems. These simpler, specialized operating systems better support the needs of the applications and can easily scale to the size of the machine. For example, a virtual machine ...
Xen and the Art of Virtualization
... manner [13]. A tagged TLB is another useful feature supported by most server-class RISC architectures, including Alpha, MIPS and SPARC. Associating an address-space identifier tag with each TLB entry allows the hypervisor and each guest OS to efficiently coexist in separate address spaces because th ...
... manner [13]. A tagged TLB is another useful feature supported by most server-class RISC architectures, including Alpha, MIPS and SPARC. Associating an address-space identifier tag with each TLB entry allows the hypervisor and each guest OS to efficiently coexist in separate address spaces because th ...
Xen and the Art of Virtualization
... manner [13]. A tagged TLB is another useful feature supported by most server-class RISC architectures, including Alpha, MIPS and SPARC. Associating an address-space identifier tag with each TLB entry allows the hypervisor and each guest OS to efficiently coexist in separate address spaces because th ...
... manner [13]. A tagged TLB is another useful feature supported by most server-class RISC architectures, including Alpha, MIPS and SPARC. Associating an address-space identifier tag with each TLB entry allows the hypervisor and each guest OS to efficiently coexist in separate address spaces because th ...
Lecture 1 - The Laboratory for Advanced Systems Research
... – Printer drivers make different printers look the same – Browser plug-ins to handle multi-media data CS 111 Spring 2015 ...
... – Printer drivers make different printers look the same – Browser plug-ins to handle multi-media data CS 111 Spring 2015 ...
Paper - Revision Science
... Write your name, centre number and candidate number in the spaces at the top of this page. Answer all questions. Write your answers in the spaces provided in this booklet. If you run out of space, use the continuation page at the back of the booklet, taking care to number the question(s) correctly. ...
... Write your name, centre number and candidate number in the spaces at the top of this page. Answer all questions. Write your answers in the spaces provided in this booklet. If you run out of space, use the continuation page at the back of the booklet, taking care to number the question(s) correctly. ...
DS3502 High-Voltage, NV, I C POT 2
... (ACK) or Not Acknowledge (NACK) is always the 9th bit transmitted during a byte transfer. The device receiving data (the master during a read or the slave during a write operation) performs an ACK by transmitting a 0 during the 9th bit. A device performs a NACK by transmitting a 1 during the 9th bit ...
... (ACK) or Not Acknowledge (NACK) is always the 9th bit transmitted during a byte transfer. The device receiving data (the master during a read or the slave during a write operation) performs an ACK by transmitting a 0 during the 9th bit. A device performs a NACK by transmitting a 1 during the 9th bit ...
Xen and the Art of Virtualization
... manner [13]. A tagged TLB is another useful feature supported by most server-class RISC architectures, including Alpha, MIPS and SPARC. Associating an address-space identifier tag with each TLB entry allows the hypervisor and each guest OS to efficiently coexist in separate address spaces because th ...
... manner [13]. A tagged TLB is another useful feature supported by most server-class RISC architectures, including Alpha, MIPS and SPARC. Associating an address-space identifier tag with each TLB entry allows the hypervisor and each guest OS to efficiently coexist in separate address spaces because th ...
Memory management unit

A memory management unit (MMU), sometimes called paged memory management unit (PMMU), is a computer hardware unit having all memory references passed through itself, primarily performing the translation of virtual memory addresses to physical addresses. It is usually implemented as part of the central processing unit (CPU), but it also can be in the form of a separate integrated circuit.An MMU effectively performs virtual memory management, handling at the same time memory protection, cache control, bus arbitration and, in simpler computer architectures (especially 8-bit systems), bank switching.