Figure 15.1 A distributed multimedia system
... Presents users (and applications) with an integrated computing ...
... Presents users (and applications) with an integrated computing ...
Operating Systems
... when you log in (e.g., /afs/umbc.edu/users/j/d/jdoe28). • The current directory is where you are located at any time while you are using the system. • Files within the same directory must be given unique names. • Paths allow us to give the same name to different files located in different directorie ...
... when you log in (e.g., /afs/umbc.edu/users/j/d/jdoe28). • The current directory is where you are located at any time while you are using the system. • Files within the same directory must be given unique names. • Paths allow us to give the same name to different files located in different directorie ...
Processes
... • First CS 415 project is up • Contact Bill Hogan ([email protected]) by 3:30 if you don’t have CSUGLab account or are not able to get to CMS ...
... • First CS 415 project is up • Contact Bill Hogan ([email protected]) by 3:30 if you don’t have CSUGLab account or are not able to get to CMS ...
File System Maintenance (continued)
... • A file can be found by using the find command: – atime for last accessed time – ctime for last changed time – mtime for last modification time – name for the filename, including the use of wildcard searches ...
... • A file can be found by using the find command: – atime for last accessed time – ctime for last changed time – mtime for last modification time – name for the filename, including the use of wildcard searches ...
Linux+ Guide to Linux Certification
... • TREE: Displays directories and subdirectories in hierarchical and indented list – Options allow user to delete files while tree is being generated – TREE /F displays names of files in each directory – Can also be used to delete file that’s duplicated on several different directories ...
... • TREE: Displays directories and subdirectories in hierarchical and indented list – Options allow user to delete files while tree is being generated – TREE /F displays names of files in each directory – Can also be used to delete file that’s duplicated on several different directories ...
Bhargavi Konduru`s presentation on Constructing Secure Operating
... to introduce protected domains to the existing embedded systems. This approach employs a microkernel to provide protected execution environments for the existing embedded kernels. It can achieve the maximum reusability of the existing software resources including embedded OS kernels and their ap ...
... to introduce protected domains to the existing embedded systems. This approach employs a microkernel to provide protected execution environments for the existing embedded kernels. It can achieve the maximum reusability of the existing software resources including embedded OS kernels and their ap ...
Mod1: Chapter 1 (and a little extra)
... primarily in C language.It can be changed up slightly to work on different hardware (which is why we have so many versions from the different companies) ...
... primarily in C language.It can be changed up slightly to work on different hardware (which is why we have so many versions from the different companies) ...
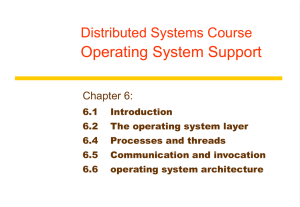
CS4513 Distributed Computing Systems
... Network OS’s are not transparent. Distributed OS’s are not independent of computers. ...
... Network OS’s are not transparent. Distributed OS’s are not independent of computers. ...
Course\FOS\FOS Unit-1 2014
... called because you use a mouse (or some other pointing device) to work with graphical objects such as windows, menus, icons, buttons, and other tools. These graphical tools represent different types of commands; the GUI enables you to issue commands to the computer by using visual objects instead of ...
... called because you use a mouse (or some other pointing device) to work with graphical objects such as windows, menus, icons, buttons, and other tools. These graphical tools represent different types of commands; the GUI enables you to issue commands to the computer by using visual objects instead of ...
Assignment0: Linux Basics and /proc
... makes /proc the current directory. Once you have made /proc the current directory, you can list its contents by using the ls command. The contents appear to be ordinary files and directories. However, a file in /proc or one of its subdirectories is actually a program that reads kernel variables and ...
... makes /proc the current directory. Once you have made /proc the current directory, you can list its contents by using the ls command. The contents appear to be ordinary files and directories. However, a file in /proc or one of its subdirectories is actually a program that reads kernel variables and ...
Sandboxing - Syracuse University
... resources, and they cannot see the rest of the resources. Chroot: (e.g., used by ftp) Virtual Machine (Isolated OS) Adding extra access control: the program can SEE everything, but an extra layer of access control is added, such that the program cannot make arbitrary access (even though the OS ...
... resources, and they cannot see the rest of the resources. Chroot: (e.g., used by ftp) Virtual Machine (Isolated OS) Adding extra access control: the program can SEE everything, but an extra layer of access control is added, such that the program cannot make arbitrary access (even though the OS ...
Berkeley NOW
... – treated as part of the hardware. No comm is like no power – you don’t bring up the device then “configure comm.” ...
... – treated as part of the hardware. No comm is like no power – you don’t bring up the device then “configure comm.” ...
Operating Systems for Embedded Computers
... Benu is a collection of increments that uses step by step presentation of core operating system operations, data structures and algorithms, where each new increment brings only a few new subjects. Other educational operating systems, while presenting single topic still use complete system, highlight ...
... Benu is a collection of increments that uses step by step presentation of core operating system operations, data structures and algorithms, where each new increment brings only a few new subjects. Other educational operating systems, while presenting single topic still use complete system, highlight ...
Network File System
... (b) File Descriptors: In UNIX and Windows, fds are unique to each process. In VxWorks fds are global entities, accessible by any task except for std input, std output and std error which can be task specific. (c) I/O Control: The specific parameters passed to ioctl() functions can differ between UNI ...
... (b) File Descriptors: In UNIX and Windows, fds are unique to each process. In VxWorks fds are global entities, accessible by any task except for std input, std output and std error which can be task specific. (c) I/O Control: The specific parameters passed to ioctl() functions can differ between UNI ...
Micro-CernVM: Slashing the Cost of Building and
... /.ucernvm_bootstrap This is a shell script provided by the operating system repository. It is sourced just before the root file system is switched and allows for custom actions. Special care has to be taken in the shutdown script of the operating system. Typically, the shutdown script does not expe ...
... /.ucernvm_bootstrap This is a shell script provided by the operating system repository. It is sourced just before the root file system is switched and allows for custom actions. Special care has to be taken in the shutdown script of the operating system. Typically, the shutdown script does not expe ...
PPT
... Used to communicate I/O requests and responses For bulk data transfer devices (DMA, network), buffer space allocated out of band by GuestOS Descriptor contains unique identifier to allow out of order processing Multiple requests can be added before hypercall made to begin processing Event notificati ...
... Used to communicate I/O requests and responses For bulk data transfer devices (DMA, network), buffer space allocated out of band by GuestOS Descriptor contains unique identifier to allow out of order processing Multiple requests can be added before hypercall made to begin processing Event notificati ...
Figure 15.1 A distributed multimedia system
... Presents users (and applications) with an integrated computing ...
... Presents users (and applications) with an integrated computing ...
CS-3013 Week 0:- Introduction
... reliability: what happens if something goes wrong – hardware or software extensibility: can we add new features? communication: how do programs exchange information concurrency: how are parallel activities created and controlled? scale: what happens as demands or resources increase? persistence: how ...
... reliability: what happens if something goes wrong – hardware or software extensibility: can we add new features? communication: how do programs exchange information concurrency: how are parallel activities created and controlled? scale: what happens as demands or resources increase? persistence: how ...
Chapter 1
... fashion like from cron. • SQL scripts used to troubleshoot various issues. Usually the DBA runs these manually while checking various aspects of the database. ...
... fashion like from cron. • SQL scripts used to troubleshoot various issues. Usually the DBA runs these manually while checking various aspects of the database. ...
2.01 - Computer Science at Rutgers
... I/O operations - A running program may require I/O, which may involve a file or an I/O device. ...
... I/O operations - A running program may require I/O, which may involve a file or an I/O device. ...
eFS: encrypted File system
... Design and Implementation Ideas.. Many of the Implementation that we have seen here, has a kernel level implementation of the file system. Certain implementations have also user level daemons running that call the kernel level programs ( e.g.: NFS) I am just describing one system architecture, ...
... Design and Implementation Ideas.. Many of the Implementation that we have seen here, has a kernel level implementation of the file system. Certain implementations have also user level daemons running that call the kernel level programs ( e.g.: NFS) I am just describing one system architecture, ...
Plan 9 from Bell Labs
.png?width=300)
Plan 9 from Bell Labs is a distributed operating system, originally developed by the Computing Sciences Research Center at Bell Labs between the mid-1980s and 2002. It takes some of the principles of Unix, developed in the same research group, but extends these to a networked environment with graphics terminals.In Plan 9, virtually all computing resources, including files, network connections, and peripheral devices, are represented through the file system rather than specialized interfaces. A unified network protocol called 9P ties a network of computers running Plan 9 together, allowing them to share all resources so represented.The name Plan 9 from Bell Labs is a reference to the Ed Wood 1959 cult science fiction Z-movie Plan 9 from Outer Space. Also, Glenda, the Plan 9 Bunny, is presumably a reference to Wood's film Glen or Glenda. The system continues to be used and developed by operating system researchers and hobbyists.