Lecture 1 Operating System Overview
... Computer-System Operation I/O devices and the CPU can execute concurrently. Each device controller is in charge of a particular device type. Each device controller has a local buffer. CPU moves data from/to main memory to/from local buffers I/O is from the device to local buffer of contro ...
... Computer-System Operation I/O devices and the CPU can execute concurrently. Each device controller is in charge of a particular device type. Each device controller has a local buffer. CPU moves data from/to main memory to/from local buffers I/O is from the device to local buffer of contro ...
Operating System Services
... File-system manipulation - The file system is of particular interest. Obviously, programs need to read and write files and directories, create and delete them, search them, list file Information, permission management. ...
... File-system manipulation - The file system is of particular interest. Obviously, programs need to read and write files and directories, create and delete them, search them, list file Information, permission management. ...
Introduction
... simpler kernel design and functionality typically results in a more reliable operating system. User programs and system services interact in a microkernel architecture by using interprocess communication mechanisms such as messaging. These messages are conveyed by the operating system. The primary d ...
... simpler kernel design and functionality typically results in a more reliable operating system. User programs and system services interact in a microkernel architecture by using interprocess communication mechanisms such as messaging. These messages are conveyed by the operating system. The primary d ...
presentation3
... “automatic” installation of clients This means that all the questions that are asked by the installation process must be answered on a text file or “script” that can be accessed during the automatic install – with Windows 2000/3 this is known as ...
... “automatic” installation of clients This means that all the questions that are asked by the installation process must be answered on a text file or “script” that can be accessed during the automatic install – with Windows 2000/3 this is known as ...
Introduction to Distributed System
... • The popularity of LAN, WAN, MAN and the Internet networks now makes distributed systems using standard PC hardware possible ...
... • The popularity of LAN, WAN, MAN and the Internet networks now makes distributed systems using standard PC hardware possible ...
ppt
... How can the kernel be eliminated from the call path on SMMPs with user-level threads? To a thread URPC is synchronous, but to the thread library it is asynchronous … explain. Why do kernel thread switches have long term cache and TLB effects that user thread switches do not? ...
... How can the kernel be eliminated from the call path on SMMPs with user-level threads? To a thread URPC is synchronous, but to the thread library it is asynchronous … explain. Why do kernel thread switches have long term cache and TLB effects that user thread switches do not? ...
linux: a product of the internet
... Distribution. BSDI is an unusual company in that its employees are distributed over a wide geographic area; they interact electronically over the network. Two variations of BSD UNIX, NetBSD and FreeBSD, have been rewritten to eliminate all proprietary source code. The appearance of NetBSD and FreeBS ...
... Distribution. BSDI is an unusual company in that its employees are distributed over a wide geographic area; they interact electronically over the network. Two variations of BSD UNIX, NetBSD and FreeBSD, have been rewritten to eliminate all proprietary source code. The appearance of NetBSD and FreeBS ...
Mach: A System Software Kernel Abstract
... software kernel which can support a variety of operating system environments. Key elements of the Mach design which allow it to efficiently support system software include integrated virtual memory management and interprocess communication, multiple threads of control within one address space, suppo ...
... software kernel which can support a variety of operating system environments. Key elements of the Mach design which allow it to efficiently support system software include integrated virtual memory management and interprocess communication, multiple threads of control within one address space, suppo ...
No Slide Title
... •Another security feature included with the Windows 2000/XP operating systems, provided NTFS is used, is encryption. •These features are only available in the Windows NT/2000/XP operating systems if NTFS is used and not the FAT file system. ...
... •Another security feature included with the Windows 2000/XP operating systems, provided NTFS is used, is encryption. •These features are only available in the Windows NT/2000/XP operating systems if NTFS is used and not the FAT file system. ...
03_shells_and_processes
... Process Exit Status • Each process exits with some status 0-255 – 0 is typically used to indicate success – All other numbers are used to indicate some “error” condition that is application specific – In C/C++ the int return value from the main is the exit status ...
... Process Exit Status • Each process exits with some status 0-255 – 0 is typically used to indicate success – All other numbers are used to indicate some “error” condition that is application specific – In C/C++ the int return value from the main is the exit status ...
Operating systems Operating systems Protected Objects
... acts as an intermediary between a user of a computer and the computer hardware. • The purpose is to provide an environment in which a user can execute programs in a convenient and efficient manner. ...
... acts as an intermediary between a user of a computer and the computer hardware. • The purpose is to provide an environment in which a user can execute programs in a convenient and efficient manner. ...
Course Intro
... An operating system manages all peripheral devices, network interfaces, other program resources and users of such. In short, an OS is a complex program system. The study of operating systems has gained importance with the advancements made in computer organization and programming systems. This cours ...
... An operating system manages all peripheral devices, network interfaces, other program resources and users of such. In short, an OS is a complex program system. The study of operating systems has gained importance with the advancements made in computer organization and programming systems. This cours ...
Chapter 4 - Killarney Secondary School
... DOS can only run one program at a time. DOS can only run small programs and has memory limitations (640 Kb max). DOS is an essential tool for IT professionals and is used extensively for troubleshooting. ...
... DOS can only run one program at a time. DOS can only run small programs and has memory limitations (640 Kb max). DOS is an essential tool for IT professionals and is used extensively for troubleshooting. ...
choices
... systems) – The distributed file system extension of Choices is close to the mechanism used in MMLite (proxy) – MMLite focuses on support for transparently replacing components in use ...
... systems) – The distributed file system extension of Choices is close to the mechanism used in MMLite (proxy) – MMLite focuses on support for transparently replacing components in use ...
Chapter 3 Operating Systems
... • A collection of programs that manages resources of a computer, such as - processors - memory - input/output devices • ... like the conductor of an orchestra. • A virtual machine that lets a user accomplish tasks that would be difficult to perform directly with the underlying actual machine. - graph ...
... • A collection of programs that manages resources of a computer, such as - processors - memory - input/output devices • ... like the conductor of an orchestra. • A virtual machine that lets a user accomplish tasks that would be difficult to perform directly with the underlying actual machine. - graph ...
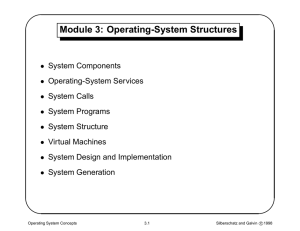
Module 3: Operating
... – command-line interpreter – shell (in UNIX) Its function is to get and execute the next command statement. ...
... – command-line interpreter – shell (in UNIX) Its function is to get and execute the next command statement. ...
ppt
... creates a new address space (called the child) copies the parent’s address space into the child’s starts a new thread of control in the child’s address space parent and child are equivalent -- almost • in parent, fork() returns a non-zero integer • in child, fork() returns a zero. • difference allow ...
... creates a new address space (called the child) copies the parent’s address space into the child’s starts a new thread of control in the child’s address space parent and child are equivalent -- almost • in parent, fork() returns a non-zero integer • in child, fork() returns a zero. • difference allow ...
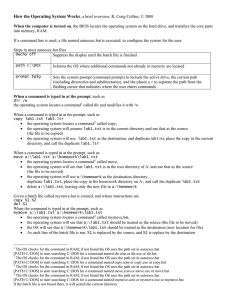
How-OS-Works.pdf
... The OS checks for the command in RAM; if not found the OS uses the path set in autoexec.bat [PATH C:\DOS] to start searching C:\DOS for a command named mymove.com or mymove.exe or mymove.bat If the batch file is not found there, it will search the current directory ...
... The OS checks for the command in RAM; if not found the OS uses the path set in autoexec.bat [PATH C:\DOS] to start searching C:\DOS for a command named mymove.com or mymove.exe or mymove.bat If the batch file is not found there, it will search the current directory ...
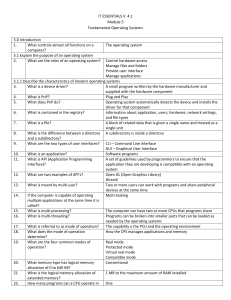
IT ESSENTIALS V. 4.1 Module 5 Fundamental Operating Systems
... protected-mode operating system Creates the environment of an earlier operating system for applications that are not compatible with the current operating system This allows an application to be run even if the user does not have the required administrative privileges Dir Xcopy ...
... protected-mode operating system Creates the environment of an earlier operating system for applications that are not compatible with the current operating system This allows an application to be run even if the user does not have the required administrative privileges Dir Xcopy ...
IT ESSENTIALS V. 4.1 Module 5 Fundamental Operating Systems 5
... system Creates the environment of an earlier operating system for applications that are not compatible with the current operating system This allows an application to be run even if the user does not have the required administrative privileges Dir Xcopy ...
... system Creates the environment of an earlier operating system for applications that are not compatible with the current operating system This allows an application to be run even if the user does not have the required administrative privileges Dir Xcopy ...
Introduction to Object Technology
... • DEC PDP-11 series – OS (RT-11) simple single user – RSTS time-sharing system – RSX-11 real-time executive (multiprogramming, memory management, file system, powerful command language) CS-550: Comparative Operating Systems ...
... • DEC PDP-11 series – OS (RT-11) simple single user – RSTS time-sharing system – RSX-11 real-time executive (multiprogramming, memory management, file system, powerful command language) CS-550: Comparative Operating Systems ...
3. Operating Systems - Informática Ingeniería en Electrónica y
... a virtual or extended machine with a much simpler use. It hides fine working details the user does not need to know (e.g. how to manage the read/write head of a magnetic disc) It provides an extra set of instructions, the System Calls They can be used by other programs or by the programmer working ...
... a virtual or extended machine with a much simpler use. It hides fine working details the user does not need to know (e.g. how to manage the read/write head of a magnetic disc) It provides an extra set of instructions, the System Calls They can be used by other programs or by the programmer working ...
An Introduction to Linux Operating System
... use TCP wrappers to limit which resources are made available to which categories of users. monitor internal users, protect your organization against unauthorized or inappropriate use of the computer facilities to harass personnel. ...
... use TCP wrappers to limit which resources are made available to which categories of users. monitor internal users, protect your organization against unauthorized or inappropriate use of the computer facilities to harass personnel. ...
CS111 Operating Systems Principles Introduction to Operating
... – OS supports richer objects, higher operations general libraries ...
... – OS supports richer objects, higher operations general libraries ...
Plan 9 from Bell Labs
.png?width=300)
Plan 9 from Bell Labs is a distributed operating system, originally developed by the Computing Sciences Research Center at Bell Labs between the mid-1980s and 2002. It takes some of the principles of Unix, developed in the same research group, but extends these to a networked environment with graphics terminals.In Plan 9, virtually all computing resources, including files, network connections, and peripheral devices, are represented through the file system rather than specialized interfaces. A unified network protocol called 9P ties a network of computers running Plan 9 together, allowing them to share all resources so represented.The name Plan 9 from Bell Labs is a reference to the Ed Wood 1959 cult science fiction Z-movie Plan 9 from Outer Space. Also, Glenda, the Plan 9 Bunny, is presumably a reference to Wood's film Glen or Glenda. The system continues to be used and developed by operating system researchers and hobbyists.