CSC 110 - Intro. to Computing
... Collision occurs when multiple nodes send data to center node at same time Bad news: central node cannot differentiate all the different data Good news: central node serves as traffic cop ...
... Collision occurs when multiple nodes send data to center node at same time Bad news: central node cannot differentiate all the different data Good news: central node serves as traffic cop ...
- ShareStudies.com
... A creates IP datagram with source A, destination B A uses ARP to get R’s MAC address for 111.111.111.110 A creates link-layer frame with R's MAC address as dest, frame contains A-to-B IP datagram A’s NIC sends frame R’s NIC receives frame R removes IP datagram from Ethernet frame, sees its destined ...
... A creates IP datagram with source A, destination B A uses ARP to get R’s MAC address for 111.111.111.110 A creates link-layer frame with R's MAC address as dest, frame contains A-to-B IP datagram A’s NIC sends frame R’s NIC receives frame R removes IP datagram from Ethernet frame, sees its destined ...
SEARCH ALGORITHMS IN PEER TO PEER NETWORKS
... + Reduced bandwidth requirements – Incomplete results Peer nodes ...
... + Reduced bandwidth requirements – Incomplete results Peer nodes ...
Lecture18 - Philadelphia University
... • Source node: It is any entity in the network that can provide information. It could be a sensor node, or an actuator node that provides feedback information about an operation. • Sink node: It is the entity where information is required. It could be another sensor/actuator node used to interact wi ...
... • Source node: It is any entity in the network that can provide information. It could be a sensor node, or an actuator node that provides feedback information about an operation. • Sink node: It is the entity where information is required. It could be another sensor/actuator node used to interact wi ...
3rd Edition, Chapter 5 - Northwestern Networks Group
... seldom used on low bit-error link (fiber, some twisted pair) wireless links: high error rates • Q: why both link-level and end-end reliability? ...
... seldom used on low bit-error link (fiber, some twisted pair) wireless links: high error rates • Q: why both link-level and end-end reliability? ...
Objectives Data Link Layer Data Link Layer Protocols Data Link
... Copyright © 2001, Cisco Systems, Inc. All rights reserved. Printed in USA. Presentation_ID.scr ...
... Copyright © 2001, Cisco Systems, Inc. All rights reserved. Printed in USA. Presentation_ID.scr ...
Controller Area Network (CAN) Basics
... pier to pier prioritized messages LIN master-slave single wire bus no quartz ...
... pier to pier prioritized messages LIN master-slave single wire bus no quartz ...
Exercise in setting up a network using XBEE modules
... have changed their destination address to the routers 64 bit MAC ID 12. Try to build a mesh net-work using all 3 end-devices as routers – can that be done? 13. The final project work – handed out the first lesson must contain some XBEE nodes! 14. Some hints here https://www.loveelectronics.co.uk/Tut ...
... have changed their destination address to the routers 64 bit MAC ID 12. Try to build a mesh net-work using all 3 end-devices as routers – can that be done? 13. The final project work – handed out the first lesson must contain some XBEE nodes! 14. Some hints here https://www.loveelectronics.co.uk/Tut ...
Latency = Propagation + Transmit + Queue
... sending the data plus the overhead in setup/teardown of the transfer. We'll see a lot of these when we talk about TCP, but for now, look at it like this: ...
... sending the data plus the overhead in setup/teardown of the transfer. We'll see a lot of these when we talk about TCP, but for now, look at it like this: ...
CoolStreaming,_DONet_A_Data-driven_Overlay_Network_for_Peer
... Resort a simple heuristic of fast response time ...
... Resort a simple heuristic of fast response time ...
Networking and Communication: Bus, switch, and network structures
... There are two common types of home networks: peer-to-peer and client/server. Client/server networks have a centralized administrative system that provides information to all of the other devices. Peer-to-peer means that each device can talk directly to each other device on the network without consul ...
... There are two common types of home networks: peer-to-peer and client/server. Client/server networks have a centralized administrative system that provides information to all of the other devices. Peer-to-peer means that each device can talk directly to each other device on the network without consul ...
Performance and Internet Architecture Networking CS 3470, Section 1
... source to the destination Always measured in time Lots of factors can affect this – any ideas? ...
... source to the destination Always measured in time Lots of factors can affect this – any ideas? ...
The CAN-B bus network remains active until all nodes on that
... transfer messages between the buses. The FCM also stores a Diagnostic Trouble Code (DTC) for certain bus network faults. All modules (also referred to as nodes) transmit and receive messages over one of these buses. Data exchange between nodes is achieved by serial transmission of encoded data messa ...
... transfer messages between the buses. The FCM also stores a Diagnostic Trouble Code (DTC) for certain bus network faults. All modules (also referred to as nodes) transmit and receive messages over one of these buses. Data exchange between nodes is achieved by serial transmission of encoded data messa ...
1 - Portal UniMAP
... The transport layer oversees the process-to-process delivery of the entire message. It is responsible for a. dividing the message into manageable segments b. reassembling it at the destination c. flow and error control 6. . What is the difference between a port address, a logical address, and a phys ...
... The transport layer oversees the process-to-process delivery of the entire message. It is responsible for a. dividing the message into manageable segments b. reassembling it at the destination c. flow and error control 6. . What is the difference between a port address, a logical address, and a phys ...
CAN - STI Innsbruck
... n nodes would require O(n2) wires for full meshed networking (up to 100 ECUs in modern cars) Bus topology only requires a single bus with n branches: O(n) Pure CAN does not specify transmission medium Automotive CAN according to ISO 11898-2/3 uses twisted pair with differential voltages on a bus top ...
... n nodes would require O(n2) wires for full meshed networking (up to 100 ECUs in modern cars) Bus topology only requires a single bus with n branches: O(n) Pure CAN does not specify transmission medium Automotive CAN according to ISO 11898-2/3 uses twisted pair with differential voltages on a bus top ...
Here is the Power Point Presentation on Chord
... Morris, Serving DNS using a Peer-to-Peer Lookup Service, In the proceedings of the First International Workshop on Peer-to-Peer Systems ...
... Morris, Serving DNS using a Peer-to-Peer Lookup Service, In the proceedings of the First International Workshop on Peer-to-Peer Systems ...
Data Link Layer
... If channel sensed idle: transmit entire frame If channel sensed busy, defer transmission ...
... If channel sensed idle: transmit entire frame If channel sensed busy, defer transmission ...
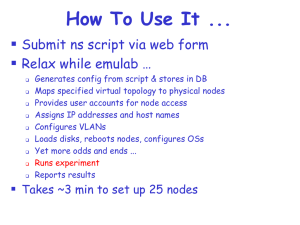
emulab.net: A Network Emulation and Distributed Systems Testbed
... “Memory and CPU demands on the individual nodes were not measured, but we believe will be modest.” “The authors ignore interrupt handling overhead in their evaluation, which likely dominates all other costs.” “You have to know the right people to use the cluster.” “The cluster is hard to use.” “
... “Memory and CPU demands on the individual nodes were not measured, but we believe will be modest.” “The authors ignore interrupt handling overhead in their evaluation, which likely dominates all other costs.” “You have to know the right people to use the cluster.” “The cluster is hard to use.” “
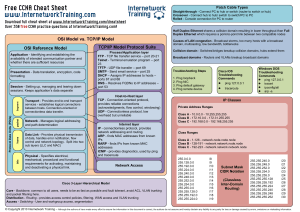
CCNA cheat sheet - Internetwork Training
... Application - Identifying and establishing the availability of intended communication partner and whether there are sufficient resources Presentation - Data translation, encryption, code formatting ...
... Application - Identifying and establishing the availability of intended communication partner and whether there are sufficient resources Presentation - Data translation, encryption, code formatting ...