Using Digital Signature with DNS
... • The NXT record: For denial of existance • The DS record: For building the chain of trust ...
... • The NXT record: For denial of existance • The DS record: For building the chain of trust ...
Security Risks
... – Weaves 128, 160, 192, 256 bit keys through data multiple times – Popular form uses Rijndael algorithm • More secure than DES ...
... – Weaves 128, 160, 192, 256 bit keys through data multiple times – Popular form uses Rijndael algorithm • More secure than DES ...
Apply encryption to network and system security
... Encryption is the process of taking some information or data, manipulating or changing its format in a way that stops it from being used or read by unauthorized people or systems. Encryption involves scrambling data so that it needs to be unscrambled, or decrypted, to be read. Encryption can be appl ...
... Encryption is the process of taking some information or data, manipulating or changing its format in a way that stops it from being used or read by unauthorized people or systems. Encryption involves scrambling data so that it needs to be unscrambled, or decrypted, to be read. Encryption can be appl ...
Jensen3
... • Conditions required to be met by the hash function for an effective traitor tracing algorithm, as specified by Chor et al., are not mentioned. – Traitor tracing algorithm needs to identify at least one traitor and reduce possibilities of a false positives. – For a k-resilient open user scheme the ...
... • Conditions required to be met by the hash function for an effective traitor tracing algorithm, as specified by Chor et al., are not mentioned. – Traitor tracing algorithm needs to identify at least one traitor and reduce possibilities of a false positives. – For a k-resilient open user scheme the ...
IPSec
... IPSec is an abbreviation for IP security, which is used to transfer data securely over unprotected networks like “Internet”. It acts at the networks layer and is part of IPv6. The protocol/process is as follows : Sender encrypts packets before sending them on the network. Receiver authenti ...
... IPSec is an abbreviation for IP security, which is used to transfer data securely over unprotected networks like “Internet”. It acts at the networks layer and is part of IPv6. The protocol/process is as follows : Sender encrypts packets before sending them on the network. Receiver authenti ...
Security & Cryptography
... Sending Gateway determines a packet needs to be encrypted Sending Gateway opens an IKE session with the Receiving gateway- this step defines the IKE SA Diffie-Hellman key exchange uses hashing of a certificate or shared secret to authenticate each gateway, and sets up a public/private data exchange ...
... Sending Gateway determines a packet needs to be encrypted Sending Gateway opens an IKE session with the Receiving gateway- this step defines the IKE SA Diffie-Hellman key exchange uses hashing of a certificate or shared secret to authenticate each gateway, and sets up a public/private data exchange ...
Power point
... – Much of network traffic contents predictable – Easier when three or more packets collide ...
... – Much of network traffic contents predictable – Easier when three or more packets collide ...
MATHEMATICS REVISION NOTES Sequential Operations. Example
... For numbers where the pre-exponential term is not 1, the pre-exponential term must be shown. Thus 120,000,000 can be written as 120 × 106 or 12 × 107 or as 1.2 × 108 . In scientific notation, the pre-exponential term is usually written as less than 10 so that in this example it would be 1.2 × 108 or ...
... For numbers where the pre-exponential term is not 1, the pre-exponential term must be shown. Thus 120,000,000 can be written as 120 × 106 or 12 × 107 or as 1.2 × 108 . In scientific notation, the pre-exponential term is usually written as less than 10 so that in this example it would be 1.2 × 108 or ...
Unit 11
... • unauthorized traffic saturates a network’s resources, restricting access for legitimate users • typical: flood servers with data packets ...
... • unauthorized traffic saturates a network’s resources, restricting access for legitimate users • typical: flood servers with data packets ...
ppt
... session) which are expensive to re-establish at a fresh server, you may use client IP affinity to insure that requests from the same client are repeatedly satisfied by the same server during this session. The trade off is that the load may be unevenly distributed. This organization is still robust t ...
... session) which are expensive to re-establish at a fresh server, you may use client IP affinity to insure that requests from the same client are repeatedly satisfied by the same server during this session. The trade off is that the load may be unevenly distributed. This organization is still robust t ...
Math 373-578 Exam 3 - WVU Math Department
... 2. Let P be a point on the elliptic curve E mod n. Suppose that we know an integer k > 0 such that kP = O. We know what to know if k is the order of P , by showing the following properties. (A) (4 %) Suppose that for each prime factor p of k, (k/p)P 6= O. Explain why k is the order of P . (B) (4 %) ...
... 2. Let P be a point on the elliptic curve E mod n. Suppose that we know an integer k > 0 such that kP = O. We know what to know if k is the order of P , by showing the following properties. (A) (4 %) Suppose that for each prime factor p of k, (k/p)P 6= O. Explain why k is the order of P . (B) (4 %) ...
Chapter X Slides
... VoIP Security Requirements: Integrity: The recipient should receive the packets that the originator sends without and change to content. Privacy: A third party should not be able to read the data Authenticity Each party should be confident they are communicating with whom each claims to be Availabi ...
... VoIP Security Requirements: Integrity: The recipient should receive the packets that the originator sends without and change to content. Privacy: A third party should not be able to read the data Authenticity Each party should be confident they are communicating with whom each claims to be Availabi ...
EAP
... Was supposed to provide authentication and privacy Secret 40 bit keys, but unsafe at any length Static-manually-configured keys Weakness due to long life of keys and they are shared among many users ...
... Was supposed to provide authentication and privacy Secret 40 bit keys, but unsafe at any length Static-manually-configured keys Weakness due to long life of keys and they are shared among many users ...
CN 2015 5 - SNGCE DIGITAL LIBRARY
... RSA Algorithm Steps Choose two large prime numbers (P,Q) Compute n=P*Q Compute Z=(P-1)*(Q-1) Choose a number relatively prime to Z and call it D Find E such that E*D=1 mod Z ...
... RSA Algorithm Steps Choose two large prime numbers (P,Q) Compute n=P*Q Compute Z=(P-1)*(Q-1) Choose a number relatively prime to Z and call it D Find E such that E*D=1 mod Z ...
PK b
... assuming the PEKS is semantically secure against an adaptive chosen message attack.(once can send a bit?) Building non-interactive public-key searchable encryption is at least as hard as building an IBE system. ...
... assuming the PEKS is semantically secure against an adaptive chosen message attack.(once can send a bit?) Building non-interactive public-key searchable encryption is at least as hard as building an IBE system. ...
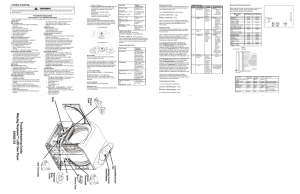
Troubleshooting Guide Maytag Neptune™ LED Gas Dryer 6390 2110
... keys for 2 seconds, will start a Membrane Pad Switch Test. To exit the test at any point, press the same keys again for 2 seconds or press the OFF key to exit Service Mode. Diagnostic Codes The Diagnostic Codes are identified when the severity level of the abnormality detected is higher and service ...
... keys for 2 seconds, will start a Membrane Pad Switch Test. To exit the test at any point, press the same keys again for 2 seconds or press the OFF key to exit Service Mode. Diagnostic Codes The Diagnostic Codes are identified when the severity level of the abnormality detected is higher and service ...
Factoring and RSA Codes using DERIVE
... Obviously everbody who is capable of factoring the modulus n can also compute the secret key. Therefore n should be sufficiently large. At present, the most common bit length of n is 512, which corresponds to about 155 decimal digits, but this may no longer be safe in a few years. For this reason al ...
... Obviously everbody who is capable of factoring the modulus n can also compute the secret key. Therefore n should be sufficiently large. At present, the most common bit length of n is 512, which corresponds to about 155 decimal digits, but this may no longer be safe in a few years. For this reason al ...
Public-key encryption
... recovering m given p, g, A, R, and C is equivalent to solving the Diffie-Hellman problem given the latest progress on the discrete logarithm problem, the size of the modulus p should at least be 1024 bits ...
... recovering m given p, g, A, R, and C is equivalent to solving the Diffie-Hellman problem given the latest progress on the discrete logarithm problem, the size of the modulus p should at least be 1024 bits ...
Hybrid cryptography using symmetric key encryption
... locations. Generally we have so many encryption algorithms which encrypt data, each encryption algorithm has its own style of formatting plain text to cipher text. The main problem nowadays faced by the network engineers is security, time taken to complete, probability of encrypting the data. The ba ...
... locations. Generally we have so many encryption algorithms which encrypt data, each encryption algorithm has its own style of formatting plain text to cipher text. The main problem nowadays faced by the network engineers is security, time taken to complete, probability of encrypting the data. The ba ...
Cryptanalysis of Shieh-Lin-Yang
... The message m is first signed by an initiator U1, and then is sent separately to all signer. Finally,U1 is responsible for combining these individual signature into a multisignature. ...
... The message m is first signed by an initiator U1, and then is sent separately to all signer. Finally,U1 is responsible for combining these individual signature into a multisignature. ...
MT311-14
... webpages. When Java was first introduced, applets were sensational because they provided a cross-platform solution for making a webpage more interesting. To safeguard users from malicious applets, applets are run in a sandbox, which imposes rather stringent restrictions on what the applets can do. ...
... webpages. When Java was first introduced, applets were sensational because they provided a cross-platform solution for making a webpage more interesting. To safeguard users from malicious applets, applets are run in a sandbox, which imposes rather stringent restrictions on what the applets can do. ...
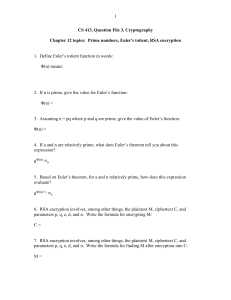
QuestionFile3Cryptography
... 17. Suppose that p = 5, q = 7, and d = 11. Assume the English alphabet is matched with the decimal digits 0-25 as usual. A sequence of decimal digits which are the result of RSA encryption is shown. Give the message that they decrypt to. In other words, find the plaintext. The sequence of decimal di ...
... 17. Suppose that p = 5, q = 7, and d = 11. Assume the English alphabet is matched with the decimal digits 0-25 as usual. A sequence of decimal digits which are the result of RSA encryption is shown. Give the message that they decrypt to. In other words, find the plaintext. The sequence of decimal di ...
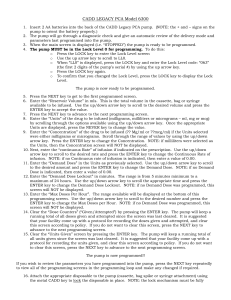
CADD LEGACY PCA Model 6300
... The pump is now ready to be programmed. 5. Press the NEXT key to get to the first programmed screen. 6. Enter the “Reservoir Volume” in mls. This is the total volume in the cassette, bag or syringe available to be infused. Use the up/down arrow key to scroll to the desired volume and press the ENTER ...
... The pump is now ready to be programmed. 5. Press the NEXT key to get to the first programmed screen. 6. Enter the “Reservoir Volume” in mls. This is the total volume in the cassette, bag or syringe available to be infused. Use the up/down arrow key to scroll to the desired volume and press the ENTER ...
Securing Distribution Automation
... The availability of an enterprise uplink can generally not be ensured at all times and a local authentication solution is still required. To fulfill this requirement, some vendors provide an innovative mechanism where a remote access server grants the user a limited duration “security ticket” that ...
... The availability of an enterprise uplink can generally not be ensured at all times and a local authentication solution is still required. To fulfill this requirement, some vendors provide an innovative mechanism where a remote access server grants the user a limited duration “security ticket” that ...
Diffie–Hellman key exchange
Diffie–Hellman key exchange (D–H) is a specific method of securely exchanging cryptographic keys over a public channel and was one of the first public-key protocols as originally conceptualized by Ralph Merkle. D–H is one of the earliest practical examples of public key exchange implemented within the field of cryptography. The Diffie–Hellman key exchange method allows two parties that have no prior knowledge of each other to jointly establish a shared secret key over an insecure channel. This key can then be used to encrypt subsequent communications using a symmetric key cipher.The scheme was first published by Whitfield Diffie and Martin Hellman in 1976. By 1975, James H. Ellis, Clifford Cocks and Malcolm J. Williamson within GCHQ, the British signals intelligence agency, had also shown how public-key cryptography could be achieved; however, their work was kept secret until 1997.Although Diffie–Hellman key agreement itself is a non-authenticated key-agreement protocol, it provides the basis for a variety of authenticated protocols, and is used to provide perfect forward secrecy in Transport Layer Security's ephemeral modes (referred to as EDH or DHE depending on the cipher suite).The method was followed shortly afterwards by RSA, an implementation of public-key cryptography using asymmetric algorithms.U.S. Patent 4,200,770, from 1977, is now expired and describes the now public domain algorithm. It credits Hellman, Diffie, and Merkle as inventors.