Crypto in data security
... • Two keys • Sender uses recipient’s public key to encrypt • Recipient uses private key to decrypt ...
... • Two keys • Sender uses recipient’s public key to encrypt • Recipient uses private key to decrypt ...
Security
... receiver with a key can decipher the content A single (symmetric) secret key is used to encrypt and decrypt Requires the communication of the key between sender and receiver! Basis of nuclear war-head command and control security ...
... receiver with a key can decipher the content A single (symmetric) secret key is used to encrypt and decrypt Requires the communication of the key between sender and receiver! Basis of nuclear war-head command and control security ...
security
... • Produce fixed-length hash (~32 bits) from variable-length message – It is computationally infeasible to find a message with that hash; in fact one can't determine any usable information about a message with that hash, not even a single bit. – Biometrics usually work the same way! ...
... • Produce fixed-length hash (~32 bits) from variable-length message – It is computationally infeasible to find a message with that hash; in fact one can't determine any usable information about a message with that hash, not even a single bit. – Biometrics usually work the same way! ...
Protecting Valuable Physical Assets in a High Traffic Setting
... “With the Medeco XT cylinders we now have audit capabilities similar to our card reader system,” continues Agee. The Medeco XT lock brand was attractive also because the only part that needed to be replaced was the cylinder—making the upgrade to existing locks easy and more cost-effective than insta ...
... “With the Medeco XT cylinders we now have audit capabilities similar to our card reader system,” continues Agee. The Medeco XT lock brand was attractive also because the only part that needed to be replaced was the cylinder—making the upgrade to existing locks easy and more cost-effective than insta ...
E-Commerce Security
... venturing into new markets, new channels and new products. Their focus is on competitive advantage through new ways of managing relationships and doing business. • Experimentation: These businesses want to become learning organizations. They are exploring the Internet and Intranet and funding small ...
... venturing into new markets, new channels and new products. Their focus is on competitive advantage through new ways of managing relationships and doing business. • Experimentation: These businesses want to become learning organizations. They are exploring the Internet and Intranet and funding small ...
Well-Tempered Clavier
... • New key-profile values – New problem: Repetitions of notes affect result ...
... • New key-profile values – New problem: Repetitions of notes affect result ...
Implementing Security for Electronic Commerce
... Encodes messages by using two mathematicallyrelated numeric keys: a public key and a private key. The public key is freely available to anyone (public) who wants to communicate with the holder of both keys. It is used to encrypt messages. ...
... Encodes messages by using two mathematicallyrelated numeric keys: a public key and a private key. The public key is freely available to anyone (public) who wants to communicate with the holder of both keys. It is used to encrypt messages. ...
compatible-development-of
... often used for signing, encrypting and decrypting e-mails to increase the security of email communications. RSA Security Inc. released their RSA algorithm into the public domain, a few days in advance of their U.S. Patent 4,405,829 expiring. Following the relaxation of the U.S. government export res ...
... often used for signing, encrypting and decrypting e-mails to increase the security of email communications. RSA Security Inc. released their RSA algorithm into the public domain, a few days in advance of their U.S. Patent 4,405,829 expiring. Following the relaxation of the U.S. government export res ...
Introduction to quantum cryptography
... • and telescopes with 8-inch mirrors to send and receive photons over the air. • Using the quantum transmitted key messages were encrypted at the rate 1 million bits per second. The speed was impressive but the distance between two NIST buildings was only 730 ...
... • and telescopes with 8-inch mirrors to send and receive photons over the air. • Using the quantum transmitted key messages were encrypted at the rate 1 million bits per second. The speed was impressive but the distance between two NIST buildings was only 730 ...
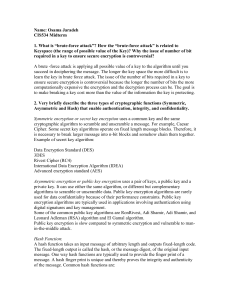
Three challenges with secret key encryption
... Keyspace (the range of possible value of the Key)? Why the issue of number of bit required in a key to ensure secure encryption is controversial? A brute -force attack is applying all possible value of a key to the algorithm until you succeed in deciphering the message. The longer the key space the ...
... Keyspace (the range of possible value of the Key)? Why the issue of number of bit required in a key to ensure secure encryption is controversial? A brute -force attack is applying all possible value of a key to the algorithm until you succeed in deciphering the message. The longer the key space the ...
Teaching Cryptologic Mathematics
... and to discover the usefulness and properties of prime numbers. Also the subject of standard computational complexity classes may be introduced. As a side excursion, it is possible to explain digital signatures based on RSA cipher. Digital signatures also allow the introduction of a specific kind of ...
... and to discover the usefulness and properties of prime numbers. Also the subject of standard computational complexity classes may be introduced. As a side excursion, it is possible to explain digital signatures based on RSA cipher. Digital signatures also allow the introduction of a specific kind of ...
Random Walks on Infinite Free Products and Infinite Algebraic Systems of Generating Functions
... are initially open. He carries with him a suitcase containing infinitely many keylocks, each with a color κ ∈ N , the colors occurring with relative frequencies {pκ }κ∈N . At each step of his patrol he selects at random from his suitcase a lock and matching key. If at least one door is locked, and if ...
... are initially open. He carries with him a suitcase containing infinitely many keylocks, each with a color κ ∈ N , the colors occurring with relative frequencies {pκ }κ∈N . At each step of his patrol he selects at random from his suitcase a lock and matching key. If at least one door is locked, and if ...
Public Key Encryption and Digital Signatures
... • Computational cost of E, D reasonable • D cannot be determined from E, the algorithm, or any amount of plaintext attack with any computationally feasible technique • E cannot be broken without D (only D will accomplish the decoding) • Any method that meets these criteria is a valid Public Key Encr ...
... • Computational cost of E, D reasonable • D cannot be determined from E, the algorithm, or any amount of plaintext attack with any computationally feasible technique • E cannot be broken without D (only D will accomplish the decoding) • Any method that meets these criteria is a valid Public Key Encr ...
Single Photon Polarization
... 2. If it is head she decides to encode using a horizontal/verical basis. If it is a tail, she encodes in 45/135 basis. 3. Each bit is encoded as 0 or 1 in the chosen basis. 4. Bob receives each bit and does not know the basis used to encode. He also tosses a coin and decides to decode using the basi ...
... 2. If it is head she decides to encode using a horizontal/verical basis. If it is a tail, she encodes in 45/135 basis. 3. Each bit is encoded as 0 or 1 in the chosen basis. 4. Bob receives each bit and does not know the basis used to encode. He also tosses a coin and decides to decode using the basi ...
Chapter 08
... the 1970s and uses a 56-bit key to encrypt data using various algorithms 56 bits provide for 256 possible keys It now takes 20 hours to break a DES key DES is being phased out, but it is still widely used since relatively few people have the equipment to break the key, 20 hours is still a relatively ...
... the 1970s and uses a 56-bit key to encrypt data using various algorithms 56 bits provide for 256 possible keys It now takes 20 hours to break a DES key DES is being phased out, but it is still widely used since relatively few people have the equipment to break the key, 20 hours is still a relatively ...
Quantum Cryptography
... that the secret key exchange will be secure. The ACT OF MEASUREMENT is an integral part of quantum mechanics, not just a passive, external process as in Classic Crypto. ...
... that the secret key exchange will be secure. The ACT OF MEASUREMENT is an integral part of quantum mechanics, not just a passive, external process as in Classic Crypto. ...
Powerpoint Slides
... Message encrypted by a public key can only be decrypted by the holder of the corresponding private key. Private key can be used to generate a digital signature and anyone knowing the public key can authenticate it. Guessing or calculating the secret private key is an extremely difficult task. ...
... Message encrypted by a public key can only be decrypted by the holder of the corresponding private key. Private key can be used to generate a digital signature and anyone knowing the public key can authenticate it. Guessing or calculating the secret private key is an extremely difficult task. ...
Chapter 8: Network Security
... This property clearly wouldn’t be useful for confidentiality since anyone with the public key could decrypt such a message. This property is, however, useful for authentication since it tells the receiver of such a message that it could only have been created by the owner of the keys. ...
... This property clearly wouldn’t be useful for confidentiality since anyone with the public key could decrypt such a message. This property is, however, useful for authentication since it tells the receiver of such a message that it could only have been created by the owner of the keys. ...
Preface
... information flowing through the network. In 1976, the paper “New Directions in Cryptography”, by Whitfield Diffie and Martin Hellman, caused a shock in the academic community. This seminal paper showed that people who are communicating with each other over an insecure line can do so in a secure way ...
... information flowing through the network. In 1976, the paper “New Directions in Cryptography”, by Whitfield Diffie and Martin Hellman, caused a shock in the academic community. This seminal paper showed that people who are communicating with each other over an insecure line can do so in a secure way ...
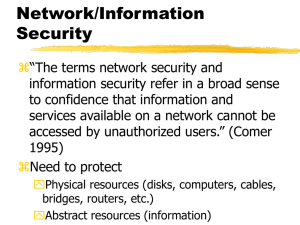
Network Security
... facto standard program for secure e-mail and file encryption on the Internet. Its public-key cryptography system enables people who have never met to secure transmitted messages against unauthorized reading and to add digital signatures to messages to guarantee their authenticity. Why do we need PGP ...
... facto standard program for secure e-mail and file encryption on the Internet. Its public-key cryptography system enables people who have never met to secure transmitted messages against unauthorized reading and to add digital signatures to messages to guarantee their authenticity. Why do we need PGP ...
Lecture 10
... Public-key methods are mostly use for key exchange or key agreement protocols p and q should be at least 155 decimal digits each ...
... Public-key methods are mostly use for key exchange or key agreement protocols p and q should be at least 155 decimal digits each ...
Lecture on Security
... I produce a certificate saying the holder of this certificate is Ronaldo Now If I do have the private key corresponding to the public key on the certificate, then I am indeed the person who owns the certificate. ...
... I produce a certificate saying the holder of this certificate is Ronaldo Now If I do have the private key corresponding to the public key on the certificate, then I am indeed the person who owns the certificate. ...
Cryptography and Coding Theory
... IT662 Cryptography and Coding Theory L – T – P: 3 – 0 – 0 Credit: 3 Objectives: The objective of the course is to provide detail knowledge of cryptography and Coding Theory Pre-requisite: Cryptography knowledge of under grad level. Outcome: Should have earned knowledge of several cryptographic algor ...
... IT662 Cryptography and Coding Theory L – T – P: 3 – 0 – 0 Credit: 3 Objectives: The objective of the course is to provide detail knowledge of cryptography and Coding Theory Pre-requisite: Cryptography knowledge of under grad level. Outcome: Should have earned knowledge of several cryptographic algor ...
Diffie–Hellman key exchange
Diffie–Hellman key exchange (D–H) is a specific method of securely exchanging cryptographic keys over a public channel and was one of the first public-key protocols as originally conceptualized by Ralph Merkle. D–H is one of the earliest practical examples of public key exchange implemented within the field of cryptography. The Diffie–Hellman key exchange method allows two parties that have no prior knowledge of each other to jointly establish a shared secret key over an insecure channel. This key can then be used to encrypt subsequent communications using a symmetric key cipher.The scheme was first published by Whitfield Diffie and Martin Hellman in 1976. By 1975, James H. Ellis, Clifford Cocks and Malcolm J. Williamson within GCHQ, the British signals intelligence agency, had also shown how public-key cryptography could be achieved; however, their work was kept secret until 1997.Although Diffie–Hellman key agreement itself is a non-authenticated key-agreement protocol, it provides the basis for a variety of authenticated protocols, and is used to provide perfect forward secrecy in Transport Layer Security's ephemeral modes (referred to as EDH or DHE depending on the cipher suite).The method was followed shortly afterwards by RSA, an implementation of public-key cryptography using asymmetric algorithms.U.S. Patent 4,200,770, from 1977, is now expired and describes the now public domain algorithm. It credits Hellman, Diffie, and Merkle as inventors.