* Your assessment is very important for improving the work of artificial intelligence, which forms the content of this project
Download Lecture (MAC)
Deep packet inspection wikipedia , lookup
Network tap wikipedia , lookup
Wake-on-LAN wikipedia , lookup
Computer network wikipedia , lookup
IEEE 802.1aq wikipedia , lookup
Airborne Networking wikipedia , lookup
Wireless USB wikipedia , lookup
Internet protocol suite wikipedia , lookup
Cellular network wikipedia , lookup
Recursive InterNetwork Architecture (RINA) wikipedia , lookup
Policies promoting wireless broadband in the United States wikipedia , lookup
IEEE 802.11 wikipedia , lookup
Wireless security wikipedia , lookup
Medium Access Control
All material copyright 1996-2009
J.F Kurose and K.W. Ross, All Rights Reserved
5: DataLink Layer
5-1
Link Layer
❒ Introduction and services
❒ Multiple access protocols
❒ Ethernet
❒ Wireless links
❒ Wireless LANs (802.11)
5: DataLink Layer
5-2
Link Layer Services
❒
__________, ___________:
❍
❍
❍
❒
encapsulate datagram into frame, adding header, trailer
channel access if shared medium
“MAC” addresses used in frame headers to identify src, dest
• different from IP address!
______________________
❍
❍
seldom used on low bit-error link (fiber, some twisted pair)
wireless links: high error rates
• Q: why both link-level and end-end reliability?
5: DataLink Layer
5-3
Link Layer Services (more)
❒
_____________:
❍
❒
pacing between adjacent sending and receiving nodes
_____________:
❍
❍
errors caused by signal attenuation, noise.
receiver detects presence of errors:
• signals sender for retransmission or drops frame
❒ _____________:
❍ receiver identifies and corrects bit error(s) without
resorting to retransmission
❒
half-duplex and full-duplex
❍
with half duplex, nodes at both ends of link can transmit,
but not at same time
5: DataLink Layer
5-4
Where is the link layer implemented?
❒ in each and every host
❒ link layer implemented in
“adaptor” (aka network
interface card NIC)
❍
❍
Ethernet card, PCMCI
card, 802.11 card
implements link, physical
layer
❒ attaches into host’s
system buses
❒ combination of
hardware, software,
firmware
host schematic
application
transport
network
link
cpu
memory
controller
link
physical
host
bus
(e.g., PCI)
physical
transmission
network adapter
card
5: DataLink Layer
5-5
Multiple Access Links and Protocols
Two types of “links”:
❒ point-to-point
❍ PPP for dial-up access
❍ point-to-point link between Ethernet switch and host
❒ broadcast (shared wire or medium)
❍ old-fashioned Ethernet
❍
❍
upstream hybrid fiber coax
________________
shared wire (e.g.,
cabled Ethernet)
shared RF
(e.g., 802.11 WiFi)
shared RF
(satellite)
humans at a
cocktail party
(shared air, acoustical)
5: DataLink Layer
5-6
Multiple Access protocols
❒ single shared broadcast channel
❒ two or more simultaneous transmissions by nodes:
interference
❍
collision if node receives two or more signals at the same time
multiple access protocol
❒ distributed algorithm that determines how nodes
share channel, i.e., determine when node can transmit
❒ communication about channel sharing must use channel
itself!
❍
no out-of-band channel for coordination
5: DataLink Layer
5-7
MAC Protocols: a taxonomy
Three broad classes:
❒ _______________
❍
❍
divide channel into smaller “pieces” (time slots,
frequency, code)
allocate piece to node for exclusive use
❒ ________________
❍ channel not divided, allow collisions
❍ “recover” from collisions
❒ _________________
❍ nodes take turns, but nodes with more to send can take
longer turns
5: DataLink Layer
5-8
Channel Partitioning MAC protocols: TDMA
TDMA: time division multiple access
❒ access to channel in "rounds"
❒ each station gets fixed length slot (length = pkt
trans time) in each round
❒ unused slots go idle
❒ example: 6-station LAN, 1,3,4 have pkt, slots 2,5,6
idle
6-slot
frame
1
3
4
1
3
4
5: DataLink Layer
5-9
Channel Partitioning MAC protocols: FDMA
FDMA: frequency division multiple access
❒ channel spectrum divided into frequency bands
❒ each station assigned fixed frequency band
❒ unused transmission time in frequency bands go idle
❒ example: 6-station LAN, 1,3,4 have pkt, frequency
FDM cable
frequency bands
bands 2,5,6 idle
time
5: DataLink Layer
5-10
Random Access Protocols
❒ When node has packet to send
❍ transmit at full channel data rate R.
❍ no a priori coordination among nodes
❒ two or more transmitting nodes ➜ “collision”,
❒ random access MAC protocol specifies:
❍ how to detect collisions
❍ how to recover from collisions (e.g., via delayed
retransmissions)
❒ Examples of random access MAC protocols:
❍ _____________________
❍
_____________________
5: DataLink Layer
5-11
Slotted ALOHA
Assumptions:
Operation:
❒ all frames same size
❒ when node obtains fresh
frame, transmits in next slot
❒ time divided into equal
size slots (time to
❍ if no collision: node can send
transmit 1 frame)
new frame in next slot
❒ nodes start to transmit
❍ if collision: node retransmits
only at slot beginning
frame in each subsequent
slot with prob. p until
❒ nodes are synchronized
success
❒ if 2 or more nodes
transmit in slot, all
nodes detect collision
5: DataLink Layer
5-12
Slotted ALOHA
Pros
❒ single active node can
continuously transmit
at full rate of channel
❒ highly decentralized:
only slots in nodes
need to be in sync
❒ simple
Cons
❒ collisions, wasting slots
❒ idle slots
❒ nodes may be able to
detect collision in less
than time to transmit
packet
❒ clock synchronization
5: DataLink Layer
5-13
CSMA (Carrier Sense Multiple Access)
CSMA: listen before transmit:
If channel sensed idle: transmit entire frame
❒ If channel sensed busy, defer transmission
❒ human analogy: don’t interrupt others!
5: DataLink Layer
5-14
CSMA collisions
collisions can still occur:
propagation delay means
two nodes may not hear
each other’s transmission
collision:
entire packet transmission
time wasted
note:
role of distance & propagation
delay in determining collision
probability
5: DataLink Layer
5-15
CSMA/CD (Collision Detection)
CSMA/CD: carrier sensing, deferral as in CSMA
detected within short time
❍ colliding transmissions aborted, reducing channel
wastage
❍ collisions
❒ collision detection:
❍ easy in wired LANs: measure signal strengths,
compare transmitted, received signals
❍ difficult in wireless LANs: received signal strength
overwhelmed by local transmission strength
❒ human analogy: the polite conversationalist
5: DataLink Layer
5-16
“Taking Turns” MAC protocols
channel partitioning MAC protocols:
❍ share channel efficiently and fairly at high load
❍ inefficient at low load: delay in channel access,
1/N bandwidth allocated even if only 1 active
node!
Random access MAC protocols
❍ efficient at low load: single node can fully
utilize channel
❍ high load: collision overhead
“taking turns” protocols
look for best of both worlds!
5: DataLink Layer
5-17
“Taking Turns” MAC protocols
Polling:
❒ master node
“invites” slave
nodes to transmit in
turn
❒ typically used with
“dumb” slave
devices
❒ concerns:
❍
❍
❍
polling overhead
latency
single point of
failure (master)
data
poll
master
data
slaves
5: DataLink Layer
5-18
“Taking Turns” MAC protocols
Token passing:
❒ control token passed
from one node to next
sequentially.
❒ token message
❒ concerns:
❍
❍
❍
token overhead
latency
single point of failure
(token)
T
(nothing
to send)
T
data
5: DataLink Layer
5-19
Summary of MAC protocols
❒
channel partitioning, by time, frequency or code
❍
❒
random access (dynamic),
❍
❍
❍
❍
❒
Time Division, Frequency Division
ALOHA, S-ALOHA, CSMA, CSMA/CD
carrier sensing: easy in some technologies (wire), hard in
others (wireless)
CSMA/CD used in Ethernet
CSMA/CA used in 802.11
taking turns
❍
❍
polling from central site, token passing
Bluetooth, FDDI, IBM Token Ring
5: DataLink Layer
5-20
Ethernet
“dominant” wired LAN technology:
❒ cheap $20 for NIC
❒ first widely used LAN technology
❒ simpler, cheaper than token LANs and ATM
❒ kept up with speed race: 10 Mbps – 10 Gbps
Metcalfe’s Ethernet
sketch
5: DataLink Layer
5-21
Star topology
❒ bus topology popular through mid 90s
❍ all nodes in same collision domain (can collide with each
other)
❒ today: star topology prevails
❍ active switch in center
❍ each “spoke” runs a (separate) Ethernet protocol (nodes
do not collide with each other)
switch
bus: coaxial cable
star
5: DataLink Layer
5-22
Ethernet: Unreliable, connectionless
❒ connectionless: No handshaking between sending and
receiving NICs
❒ unreliable: receiving NIC doesn’t send acks or nacks
to sending NIC
❍
❍
❍
stream of datagrams passed to network layer can have gaps
(missing datagrams)
gaps will be filled if app is using TCP
otherwise, app will see gaps
❒ Ethernet’s MAC protocol: unslotted CSMA/CD
5: DataLink Layer
5-23
Ethernet CSMA/CD algorithm
1. NIC receives datagram
4. If NIC detects another
from network layer,
transmission while
creates frame
transmitting, aborts and
sends jam signal
2. If NIC senses channel idle,
starts frame transmission 5. After aborting, NIC
If NIC senses channel
enters exponential
busy, waits until channel
backoff: after mth
idle, then transmits
collision, NIC chooses K at
random from
3. If NIC transmits entire
{0,1,2,…,2m-1}. NIC waits
frame without detecting
K·512 bit times, returns to
another transmission, NIC
Step 2
is done with frame !
5: DataLink Layer
5-24
Ethernet’s CSMA/CD (more)
Jam Signal: make sure all
other transmitters are
aware of collision; 48 bits
Bit time: .1 microsec for 10
Mbps Ethernet ;
for K=1023, wait time is
about 50 msec
Exponential Backoff:
❒ Goal: adapt retransmission
attempts to estimated
current load
❍ heavy load: random wait
will be longer
❒ first collision: choose K from
{0,1}; delay is K· 512 bit
transmission times
❒ after second collision: choose
K from {0,1,2,3}…
❒ after ten collisions, choose K
from {0,1,2,3,4,…,1023}
5: DataLink Layer
5-25
Elements of a wireless network
network
infrastructure
wireless hosts
❒ laptop, PDA, IP phone
❒ run applications
❒ may be stationary
(non-mobile) or mobile
❍
wireless does not
always mean mobility
6: Wireless and Mobile Networks
6-26
Elements of a wireless network
network
infrastructure
base station
❒ typically connected to
wired network
❒ relay - responsible
for sending packets
between wired
network and wireless
host(s) in its “area”
❍ e.g., cell towers,
802.11 access
points
6: Wireless and Mobile Networks
6-27
Elements of a wireless network
network
infrastructure
wireless link
❒ typically used to
connect mobile(s) to
base station
❒ also used as backbone
link
❒ multiple access
protocol coordinates
link access
❒ various data rates,
transmission distance
6: Wireless and Mobile Networks
6-28
Characteristics of selected wireless link
standards
Data rate (Mbps)
200
54
5-11
802.11n
802.11a,g
802.11b
4
1
802.11a,g point-to-point
data
802.16 (WiMAX)
UMTS/WCDMA-HSPDA, CDMA2000-1xEVDO
3G cellular
enhanced
802.15
.384
3G
UMTS/WCDMA, CDMA2000
.056
2G
IS-95, CDMA, GSM
Indoor
Outdoor
10-30m
50-200m
Mid-range
outdoor
Long-range
outdoor
200m – 4 Km
5Km – 20 Km
6: Wireless and Mobile Networks
6-29
Elements of a wireless network
network
infrastructure
__________ mode
❒ base station connects
mobiles into wired
network
❒ handoff: mobile
changes base station
providing connection
into wired network
6: Wireless and Mobile Networks
6-30
Elements of a wireless network
______ mode
❒ no base stations
❒ nodes can only
transmit to other
nodes within link
coverage
❒ nodes organize
themselves into a
network: route among
themselves
6: Wireless and Mobile Networks
6-31
Wireless network taxonomy
single hop
infrastructure
(e.g., APs)
no
infrastructure
host connects to
base station (WiFi,
WiMAX, cellular)
which connects to
larger Internet
no base station, no
connection to larger
Internet (Bluetooth,
ad hoc nets)
multiple hops
host may have to
relay through several
wireless nodes to
connect to larger
Internet: mesh net
no base station, no
connection to larger
Internet. May have to
relay to reach other
a given wireless node
MANET, VANET
6: Wireless and Mobile Networks
6-32
Wireless Link Characteristics
Differences from wired link ….
❍ _____________:
radio signal attenuates as it
propagates through matter (path loss)
❍ _______________: standardized wireless
network frequencies (e.g., 2.4 GHz) shared by
other devices (e.g., phone); devices (motors)
interfere as well
❍ _______________: radio signal reflects off
objects ground, arriving ad destination at
slightly different times
…. make communication across (even a point to point)
wireless link much more “difficult”
6: Wireless and Mobile Networks
6-33
Wireless network characteristics
Multiple wireless senders and receivers create
additional problems (beyond multiple access):
C
A
B
A
C
B
____________problem
space
B, A hear each other
❒ B, C hear each other
❒ A, C can not hear each other
means A, C unaware of their
interference at B
❒
6: Wireless and Mobile Networks
6-34
IEEE 802.11 Wireless LAN
❒ 802.11a
❒ 802.11b
❍ 5-6 GHz range
❍ 2.4-5 GHz unlicensed spectrum
❍ up to _____ Mbps
❍ up to ______ Mbps
❍ direct sequence spread spectrum ❒ 802.11g
(DSSS) in physical layer
❍ 2.4-5 GHz range
• all hosts use same chipping
❍ up to _____ Mbps
code
❒ 802.11n: multiple antennae
❍ 2.4-5 GHz range
❍ up to ______ Mbps
all use CSMA/CA for multiple access
❒ all have base-station and ad-hoc network versions
❒
6: Wireless and Mobile Networks
6-35
802.11 LAN architecture
wireless host communicates
with base station
❍ _______________
❒ _____________________
(aka “cell”) in infrastructure
mode contains:
❍ wireless hosts
❍ access point (AP): base
station
❍ ad hoc mode: hosts only
❒
Internet
AP
hub, switch
or router
BSS 1
AP
BSS 2
6: Wireless and Mobile Networks
6-36
802.11: Channels, association
❒ 802.11b: 2.4GHz-2.485GHz spectrum divided into
________ channels at different frequencies
❍ AP admin chooses frequency for AP
❍ interference possible: channel can be same as
that chosen by neighboring AP!
❒ host: must
associate with an AP
6: Wireless and Mobile Networks
6-37
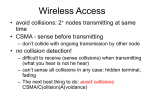
IEEE 802.11: multiple access
❒ avoid collisions: 2+ nodes transmitting at same time
❒ 802.11: CSMA - sense before transmitting
❍ don’t collide with ongoing transmission by other node
❒ 802.11: no collision detection!
❍ difficult to receive (sense collisions) when transmitting due
to weak received signals (fading)
❍ can’t sense all collisions in any case: hidden terminal, fading
❍ goal: avoid collisions: CSMA/C(ollision)A(voidance)
A
C
A
B
A’s signal
strength
B
C
C’s signal
strength
space
6: Wireless and Mobile Networks
6-38
IEEE 802.11 MAC Protocol: CSMA/CA
802.11 sender
1 if sense channel idle for DIFS then
transmit entire frame (no CD)
2 if sense channel busy then
start random backoff time
timer counts down while channel idle
transmit when timer expires
if no ACK, increase random backoff
interval, repeat 2
802.11 receiver
- if frame received OK
sender
receiver
DIFS
data
SIFS
ACK
return ACK after SIFS (ACK needed due to
hidden terminal problem)
6: Wireless and Mobile Networks
6-39
Avoiding collisions (more)
idea: allow sender to “reserve” channel rather than random
access of data frames: avoid collisions of long data frames
❒ sender first transmits small request-to-send (RTS) packets
to BS using CSMA
❍ RTSs may still collide with each other (but they’re short)
❒ BS broadcasts clear-to-send CTS in response to RTS
❒ CTS heard by all nodes
❍ sender transmits data frame
❍ other stations defer transmissions
avoid data frame collisions completely
using small reservation packets!
6: Wireless and Mobile Networks
6-40
Collision Avoidance: RTS-CTS exchange
A
AP
B
time
6: Wireless and Mobile Networks
6-41
802.11: advanced capabilities
QAM256 (8 Mbps)
QAM16 (4 Mbps)
BPSK (1 Mbps)
operating point
10-1
10-2
10-3
BER
Rate Adaptation
❒ base station, mobile
dynamically change
transmission rate
(physical layer
modulation technique)
as mobile moves, SNR
varies
10-4
10-5
10-6
10-7
10
20
30
SNR(dB)
40
1. SNR decreases, BER
increase as node moves
away from base station
2. When BER becomes too
high, switch to lower
transmission rate but with
lower BER
6: Wireless and Mobile Networks
6-42
802.11: advanced capabilities
Power Management
❒ node-to-AP: “I am going to sleep until next
beacon frame”
❍ AP knows not to transmit frames to this
node
❍ node wakes up before next beacon frame
❒ beacon frame: contains list of mobiles with APto-mobile frames waiting to be sent
❍ node will stay awake if AP-to-mobile frames
to be sent; otherwise sleep again until next
beacon frame
6: Wireless and Mobile Networks
6-43
802.15: personal area network
❒ less than 10 m diameter
❒ replacement for cables
(mouse, keyboard,
headphones)
❒ ad hoc: no infrastructure
❒ master/slaves:
❍
❍
slaves request permission to
send (to master)
master grants requests
❒ 802.15: evolved from
Bluetooth specification
❍
❍
2.4-2.5 GHz radio band
up to 721 kbps
P
S
P
radius of
coverage
M
S
P
S
P
M Master device
S Slave device
P Parked device (inactive)
6: Wireless and Mobile Networks
6-44
Wireless, mobility: impact on higher layer protocols
should be minimal …
❍ best effort service model remains unchanged
❍ TCP and UDP can (and do) run over wireless, mobile
❒ … but performance-wise:
❍ packet loss/delay due to bit-errors (discarded
packets, delays for link-layer retransmissions), and
handoff
❍ TCP interprets loss as congestion, will decrease
congestion window un-necessarily
❍ delay impairments for real-time traffic
❍ limited bandwidth of wireless links
❒ logically, impact
6: Wireless and Mobile Networks
6-45