* Your assessment is very important for improving the work of artificial intelligence, which forms the content of this project
Download IP Addresses
Point-to-Point Protocol over Ethernet wikipedia , lookup
IEEE 802.1aq wikipedia , lookup
Asynchronous Transfer Mode wikipedia , lookup
Distributed firewall wikipedia , lookup
Internet protocol suite wikipedia , lookup
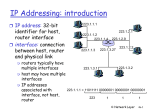
Deep packet inspection wikipedia , lookup
Network tap wikipedia , lookup
Computer network wikipedia , lookup
Multiprotocol Label Switching wikipedia , lookup
Piggybacking (Internet access) wikipedia , lookup
List of wireless community networks by region wikipedia , lookup
Airborne Networking wikipedia , lookup
Recursive InterNetwork Architecture (RINA) wikipedia , lookup
Packet switching wikipedia , lookup
Wake-on-LAN wikipedia , lookup
• IP Service • IP Addressing • Datagram Format • Routing (Forwarding) • Subnetting • Fragmentation © Jörg Liebeherr (modified by M. Veeraraghavan) 1 Orientation • IP (Internet Protocol) is a Network Layer Protocol. TCP UDP Transport Layer ICMP IP IGMP Network Layer ARP Network Access RARP Link Layer Media • IP’s current version is Version 4 (IPv4). It is specified in RFC 891. © Jörg Liebeherr (modified by M. Veeraraghavan) 2 Orientation • IP layer processing occurs at both routers and hosts: Application Application protocol Application TCP TCP protocol TCP IP Network Access Host IP IP protocol Data Link Network Access Network Access Router © Jörg Liebeherr (modified by M. Veeraraghavan) IP IP protocol Data Link Network Access IP protocol Network Access Router Data Link IP Network Access Host 3 IP Service • IP provides an unreliable and connectionless service (“datagram service”). Unreliable: IP does not guarantee that a transmitted packet will be delivered. Connectionless: Each packet (“datagram”) is handled independently. IP is not aware that packets between hosts may be sent in a logical sequence. • Consequences of an unreliable, connectionless service – Lost packets – Packets delivered out-of-sequence – Can have duplicate packets because of TCP layer resends* • e.g. if packet is delivered but ACK is lost, TCP sender will resend packet buffered at the end host. *: The audio file says duplicate packets could occur because of router-buffered packets; this is not commonplace in today’s networks because common link-layer protocols do not have retransmissions, but if they did, this could be another cause of duplicate packets; for example, 802.11 wireless link layer has retransmissions. © Jörg Liebeherr (modified by M. Veeraraghavan) 4 IP Service • IP offers a best effort * service; i.e., IP does not make performance guarantees on: • the time until a packet is delivered • the packet loss rate • the throughput of traffic between two hosts • etc. • Performance guarantees are also called Quality-of-Service or QoS guarantees. • IP provides limited QoS support. This is done via the Type-ofService (TOS) field. * “Best effort” may mean different things to different people. © Jörg Liebeherr (modified by M. Veeraraghavan) 5 IP Service • IP supports the following services: • one-to-one (unicast) • one-to-many (multicast) • one-to-all (broadcast) Unicast Broadcast Multicast • IP multicast actually supports a many-to-many service. • IP multicast requires support of other protocols (IGMP, multicast routing). © Jörg Liebeherr (modified by M. Veeraraghavan) 6 Internet Addresses • Each network interface on the Internet as a unique global address, called the IP address. • An IP address: - is 32 bits long. - encodes a network number and a host number • IP addresses are written in a dotted decimal notation : - 128.238.42.112 10000000 11101110 00101010 01110000 © Jörg Liebeherr (modified by M. Veeraraghavan) means in 1st Byte in 2nd Byte in 3rd Byte in 4th Byte 7 Internet Address Classes • IP distinguishes 5 classes of addresses. Class A Class B Class C Class D 0 network id host 7 bits 24 bits 1 0 network id host 14 bits 16 bits 1 1 0 1 1 1 0 network id host 21 bits 8 bits multicast group id 28 bits Class E 1 1 1 1 0 (reserved for future use) 27 bits © Jörg Liebeherr (modified by M. Veeraraghavan) 8 IP Addresses • The end points of each range are not allowed because all zeros and all ones are disallowed for netid, subnetid and hostid (see pg. 42 of text and RFC791). Class From To A 0.0.0.0 B 128.0.0.0 191.255.255.255 C 192.0.0.0 223.255.255.255 D 224.0.0.0 239.255.255.255 E 240.0.0.0 247.255.255.255 © Jörg Liebeherr (modified by M. Veeraraghavan) 127.255.255.255 9 Trade-off of Address Classes • There are a total of 232 = 4,294,967,296 IP addresses Class A: 7 bits for netid only 128 Class A networks each net can have about 16 million (224-2) hosts. Class B: 14 bits for netid about 16,000 networks About 65,000 (216 -2) hosts per network Class C: 21 bits for netid about 2 million networks Only 254 hosts per network © Jörg Liebeherr (modified by M. Veeraraghavan) 10 Special case IP addresses (not complete) • 0: all zeros (means “this host” or “this net”); -1: all ones (this is reserved for broadcasts); netid, subnetid, hostid: anything else IP address netID subnetID Can appear as Description hostID Source? Destination? 0 0 OK never This host on this net 0 hostid OK never Specified host on this net 127 anything OK OK Loopback address -1 -1 never OK Limited broadcast netid -1 never OK Net-directed broadcast to netid Subnet-directed broadcast to netid, subnetid All-subnets-directed broadcast to netid netid subnetid -1 never OK netid -1 -1 never OK © Jörg Liebeherr (modified by M. Veeraraghavan) 11 IP Datagram Format • 20 bytes Header Size 24 * 32 bit-words = 60 bytes • 20 bytes Total Length 216 bytes = 65536 bytes version (4 bits) header length Type of Service/TOS (8 bits) >= five 32-bit words Identification (16 bits) TTL Time-to-Live (8 bits) Total Length (in bytes) (16 bits) flags (3 bits) Protocol (8 bits) Fragment Offset (13 bits) Header Checksum (16 bits) Source IP address (32 bits) Destination IP address (32 bits) Options (if any, <=40 bytes) DATA 0 31 32-bit word © Jörg Liebeherr (modified by M. Veeraraghavan) 12 IP Datagram Transmission • Question: If you measure an IP datagram on the network, in which order are the fields transmitted? • Answer: • Transmission is row by row • For each row: 1. Transmit bits 0-7 2. Transmit bits 8-15 3. Transmit bits 16-23 4. Transmit bits 24-31 • This is called network byte order or big endian byte ordering. • Note: some computers store 32-bit words in little endian format. Which ones? © Jörg Liebeherr (modified by M. Veeraraghavan) 13 Fields of the IP Header • Version: current version is 4, next version will be 6. • Header length (4 bits): Number of 32-bit words in the IP header • Type of Service (TOS): contains 4 TOS bits, where each bit indicates a desired service. • minimize delay • maximize throughput • maximize reliability • minimize cost – Only one bit can be set! Not supported in all applications. © Jörg Liebeherr (modified by M. Veeraraghavan) 14 IP Header Fields Contd. • Total Length: Number of bytes in the IP datagram (header+payload) • Identification: unique identification of a datagram from a host. Incremented whenever a datagram is transmitted. • Flags and Fragment Offset: Associated with fragmentation • Time To Live (TTL): specifies longest path before datagram is dropped. – Used to prevent infinite looping of packets – TTL field is set at sending host and is decremented by 1 at each router – If a router gets a datagram whose TTL is either 0 or 1, the router will drop the packet. – If a destination host gets a datagram whose TTL is 1, the host will deliver the datagram to the higher layer. © Jörg Liebeherr (modified by M. Veeraraghavan) 15 Fields of the IP Header • Protocol: Specifies the higher-layer protocol. Used for demultiplexing to higher layers. Application TCP UDP ICMP IGMP IP • Header checksum: verifies correctness of header. © Jörg Liebeherr (modified by M. Veeraraghavan) 16 Fields of the IP Header • Source and Destination Addresses: identify the interfaces on the sending and receiving hosts • Options: • Security restrictions • Record Route: each router that processes the packet adds its IP address to the header. • Timestamp: each router that processes the packet adds its IP address and time to the header. • (loose) Source Routing: specifies a list of routers that must be traversed. • (strict) Source Routing: specifies a list of the only routers that can be traversed. • Padding: ensures that header ends on a 4-byte boundary © Jörg Liebeherr (modified by M. Veeraraghavan) 17 Routing • The routing functions at the network layer must be able to deliver a packet from a source host to a destination host. • There are two parts to the routing problem: 1. How to pass a packet from an input interface to the output interface of a router (“packet forwarding”) ? 2. How to create routing tables? • In this lecture, we only discuss the packet forwarding part. The other function is discussed in Lecture 6. © Jörg Liebeherr (modified by M. Veeraraghavan) 18 Major Tenets for Datagram Forwarding • Every IP datagram contains the IP address of an interface of a destination host. • The network id of an IP address uniquely identifies a single physical network that is part of the larger Internet. • All hosts and routers that have the same network id are connected to the same physical network and can directly communicate by sending MAC layer frames. • Every physical network of the Internet has at least one router, which is also connected to at least one other physical network. © Jörg Liebeherr (modified by M. Veeraraghavan) 19 IP Forwarding • A packet is typically forwarded to a large number of routers before reaching the destination host. • IP forwarding is done on a hop-by-hop basis, i.e., no one knows the complete route. The goal of forwarding is to bring the IP datagram closer to the destination. © Jörg Liebeherr (modified by M. Veeraraghavan) 20 IP Forwarding • IP forwarding is performed by both hosts and routers. • The difference between IP forwarding in a host and in a router is that a host’s IP module does not forward packets received on an interface to another interface (if it does then it is behaving as a router). In a host, IP forwarding is from the higher layers to an interface or vice versa • Both routers and hosts have a routing table. Routing table entries look like this and is looked up for each datagram: Destination IP address of Flags IP address Next-Hop-Router Specification of an interface Whole IP Address of router address or interface or directly network ID of connected network IP address Interface to which the datagram is passed © Jörg Liebeherr (modified by M. Veeraraghavan) 21 Flags • H: Whether the destination address is the network ID of an IP address (H=0) or the complete IP address of a host interface (H=1). • G: Whether the next-hop router field is really a next-hop router (G=1) or a directly connected interface (G=0) © Jörg Liebeherr (modified by M. Veeraraghavan) 22 Forwarding Functions at Host • Forwarding an IP datagram at a host: DestNet = Network id in destination IP address If (DestNet == my Network id) Deliver datagram to destination directly; else Send datagram to default router; • Reception of an IP datagram at a host: Datagram is received on an interface If (Destination IP address == (my IP address || broadcast address)) Deliver datagram to higher layer; else Discard the datagram; © Jörg Liebeherr (modified by M. Veeraraghavan) 23 Forwarding Functions at Router • Reception of an IP datagram at a router: Packet is received on an interface If (Destination IP address != my IP address) Perform datagram forwarding; • Forwarding an IP datagram at a router: DestNet = Network id in destination IP address DestIP = destination IP address If (DestIP == Destination IP address in my routing table) Deliver datagram to the next-hop-router in the table; elseif (DestNet == Network id in my routing table) Deliver datagram to destination of the interface; else deliver packet to default router; © Jörg Liebeherr (modified by M. Veeraraghavan) 24 Example (from Textbook) ftp.uu.net 192.48.96.9 140.252.1.0 140.252.13.0 140.252.1.183 140.252.104.1 140.252.1.4 Gateway netb modem modem 140.252.1.29 140.252.13.33 sun 140.252.13.35 bsdi • Scenario 1: bsdi sends a datagram to sun • Scenario 2: bsdi sends a datagram to ftp.uu.net © Jörg Liebeherr (modified by M. Veeraraghavan) 25 Scenario 1 140.252.13.0 140.252.13.33 sun 140.252.13.35 bsdi • Bsdi looks up its routing table and finds sun as being located on the same network. • How ? The network address of sun and bsdi match. •Bsdi issues an ARP request for 140.252.13.33 •Sun replies with the MAC address for its interface •Bsdi can then send the IP datagram encapsulated in an ethernet frame © Jörg Liebeherr (modified by M. Veeraraghavan) 26 Scenario 2 ftp.uu.net 192.48.96.9 140.252.1.0 140.252.13.0 140.252.1.183 140.252.104.1 140.252.1.4 Gateway modem modem 140.252.1.29 netb 140.252.13.33 sun 140.252.13.35 bsdi • bsdi sends a datagram to ftp.uu.net. 1. bsdi sees that its network ID differs from that of the destination address 2. So it sends the datagram to its default router (sun) (by using the MAC address of the 140.252.13.33 interface on sun - obtained by ARP) © Jörg Liebeherr (modified by M. Veeraraghavan) 27 Scenario 2, Part II ftp.uu.net 192.48.96.9 140.252.1.0 140.252.13.0 140.252.1.183 140.252.104.1 140.252.1.4 Gateway netb modem modem 140.252.1.29 140.252.13.33 sun 140.252.13.35 bsdi 3. sun (is configured as router) forwards the packet to its default router (which is set to netb). 4. netb forwards the datagram to its default next-hop-router, set to Gateway (140.252.1.4). 5. Gateway forwards the packet to somewhere else (not known). © Jörg Liebeherr (modified by M. Veeraraghavan) 28 Subnetting • The address classes makes Class A and B addresses very attractive and Class C addresses not attractive: - The number of network id’s relates to the size of the routing table in IP routers. - The number of hosts on a network is limited to 255. - Organization must contact IANA for each new LAN. - Management of a large number of Class C addresses is cumbersome. • But: There are only few Class A and B addresses! • Solution: © Jörg Liebeherr (modified by M. Veeraraghavan) Subnetting 29 Subnetting • Goal: Reduce the need for a large number of network ids. • Basic Idea: - Split the host id portion of an IP address into a subnet id and a host id. - Assign one subnet id to each physical network. • Then: • Subnets can be freely assigned and be used for many physical networks. • Distant routers need not be aware of subnet id’s. © Jörg Liebeherr (modified by M. Veeraraghavan) 30 Subnet Masks • Routers and hosts use a subnet mask to separate the subnetwork id from the host id. Class B 1 0 network id host 14 bits with subnetting 1 0 16 bits network id 14 bits Subnet mask subnet id host 8 bits 8 bits 111111111111111111111111 00000000 24 bits 8 bits (255.255.255.0) Question: In the IP address 152.164.9.10 with subnet mask 255.255.255.128, what class does this IP address belong to and what are the 14 bits netid, subnet id and hostid? How many bits are in the subnet id and in the hostid? Answer: Class B; 14 bits netid = 24.164, subnet id (9 bits) = 9.0 hostid (7 bits) = 10 © Jörg Liebeherr (modified by M. Veeraraghavan) 31 Subnetting: Host Processing • Each host has to know the IP address and the subnet mask of its interface • For each IP datagram received from the application, the IP layer at the host peforms: if ((Destination IP address & Subnet Mask) == (My IP address & Subnet Mask)) Deliver datagram directly (perform ARP if shared medium LAN); else Forward datagram to default router; © Jörg Liebeherr (modified by M. Veeraraghavan) 32 Subnetting: Router Processing • A router has a table: < SubnetNumber, SubnetMask, NextHop> » SubnetNumber is the <network id, subnet id> » SubnetMask is the subnet mask » NextHop is the IP address of a router. • The router perfoms the following algorithm: – Reception of an IP datagram at a router: Packet is received on an interface whose IP address is IP1. dest = destination IP address; If (dest == IP1) Deliver datagram to TL/application in router ; © Jörg Liebeherr (modified by M. Veeraraghavan) 33 Subnetting: Router processing Contd. Else for each entry <SubnetNumber, SubnetMask, NextHop> sub1 = dest & SubnetMask; if (sub1 == SubnetNumber) Forward datagram to NextHop; else Go to next entry in routing table; © Jörg Liebeherr (modified by M. Veeraraghavan) 34 Advantages of Subnetting • Improves efficiency of IP address usage by not consuming an entire Class B or Class C address for each physical network. • Reduces routing table sizes. Since external routers do not know about subnetting, the size of routing tables is reduced. • Networks become easier to manage. • Note that there are three levels of aggregation: • Network • Subnet • Host © Jörg Liebeherr (modified by M. Veeraraghavan) 35 IP Fragmentation • Host A sends a large IP datagram to Host B. • Any Problem with that? FDDI Ring Host A MTUs: FDDI: 4352 Ethernet Router Host B Ethernet: 1500 • IP router splits the datagram into several fragments • Fragmentation requires that the data portion of every fragment except the last be a multiple of 8 bytes. © Jörg Liebeherr (modified by M. Veeraraghavan) 36 Where is Fragmentation done? • Fragmentation can be done at the sender or at intermediate routers. • The same datagram can be fragmented several times. • Reassembly of original datagram is only done at destination hosts. IP datagram H Fragment 2 H2 Fragment 1 H1 Router © Jörg Liebeherr (modified by M. Veeraraghavan) 37 What’s involved in Fragmentation? • The following fields in the IP header are involved: version (4 bits) header length Type of Service/TOS flags Identification TTL Time-to-Live (8 bits) Total Length (in bytes) Protocol (8 bits) Fragment Offset Header Checksum (16 bits) ...... Identification Flags is the same in all fragments. contains a “more fragments” bit. (There is also a “don’t fragment bit” that can be set). Fragment offset Total length © Jörg Liebeherr (modified by M. Veeraraghavan) contains the offset (in 8-byte units) of current fragment in the original datagram. is changed to be the size of the fragment. 38 Multiple links • The ID field stays the same for all fragments of a datagram sent by a sender to allow for reassembly • The fragment offset is relative to the datagram sent by the sender. • Two fragments created on X.25 link (offsets 0, 69) – 576 – 20 (IP header) = 556; 552 divides by 8 as 69. • Each is fragmented further on the PPP link – ID stays the same on all fragments – Fragment offset on the second set of fragments is relative to the original (0, 34, 68, 69, 103) • 296-20=276; 272/8 = 34 IP datagram sent has a payload of 1000 bytes © Jörg Liebeherr (modified by M. Veeraraghavan) X.25 Router (MTU=576) 1 PPP Router (MTU=296) 2 39 Configuring a Network Interface • The ifconfig command is used for setting and testing network interfaces (in Unix systems) that run TCP/IP • Ifconfig must be run at boot time to initialize the network interfaces. • Ifconfig -a plots a report on all interfaces. : aida:/ ; ifconfig -a ed1: flags=8863<UP,BROADCAST,NOTRAILERS,RUNNING,SIMPLEX, MULTICAST> mtu 1500 inet 128.238.42.114 netmask 0xffffff00 broadcast 128.238.42.255 lo0: flags=8049<UP,LOOPBACK,RUNNING,MULTICAST> mtu 16384 inet 127.0.0.1 netmask 0xff000000 © Jörg Liebeherr (modified by M. Veeraraghavan) 40 Configuring a Network Interface • The netstat command plots (a lot of) network related data structures in the operating system. • Netstat -i plots information on the network interfaces. : aida:/ ; netstat -i Name Mtu Network Address ed1 1500 128.238.42.114 aida lo0 16384 your-net localhost © Jörg Liebeherr (modified by M. Veeraraghavan) Ipkts Ierrs Opkts Oerrs Coll 2394482 35664 346880 223 119591 153 0 153 0 0 41