* Your assessment is very important for improving the work of artificial intelligence, which forms the content of this project
Download interrupt - Universidade de Coimbra
Survey
Document related concepts
Burroughs MCP wikipedia , lookup
Mobile operating system wikipedia , lookup
Unix security wikipedia , lookup
Spring (operating system) wikipedia , lookup
Copland (operating system) wikipedia , lookup
Distributed operating system wikipedia , lookup
Transcript
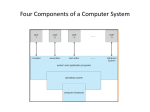
Operating Systems 2006/2007 1. Introduction Paulo Marques Departamento de Eng. Informática Universidade de Coimbra [email protected] Disclaimer This slides and notes are heavily based on the companion material of [Silberschatz05].The original material can be found at: In some cases, material from [Stallings04] may also be used. The original material can be found at: http://codex.cs.yale.edu/avi/os-book/os7/slide-dir/index.html http://williamstallings.com/OS/OS5e.html The respective copyrights belong to their owners. 2 What’s an Operating System? User Applications Operating System Hardware 3 What Operating Systems Do Controls and coordinates use of hardware among various applications and users The OS is a resource allocator: it manages all resources and decides between conflicting requests for efficient and fair resource use OS is a control program: controls execution of programs to prevent errors and improper use of the computer 4 Two Modes of Operation User Mode Kernel Mode UNIX Operating System Structure 5 Input/Output versus CPU Usage I/O devices and the CPU can execute concurrently Each device controller is in charge of a particular device type Each device controller has a local buffer CPU moves data from/to main memory to/from local buffers I/O is from the device to local buffer of controller Device controller informs CPU that it has finished its operation by causing an interrupt 6 Interrupt Timeline 7 Interrupt Operation Interrupt transfers control to the interrupt service routine generally, through the interrupt vector, which contains the addresses of all the service routines Interrupt architecture must save the address of the interrupted instruction and the relevant context of the executing program Incoming interrupts are disabled while another interrupt is being processed to prevent a lost interrupt A trap is a software-generated interrupt caused either by an error or a user request An operating system is interrupt driven 8 Interrupt Operation (2) The operating system preserves the state of the CPU by storing registers and the program counter Determines which type of interrupt has occurred: polling vectored interrupt system Separate segments of code determine what action should be taken for each type of interrupt 9 Different Types of I/O 10 Different Types of I/O (2) After I/O starts, control returns to user program only upon I/O completion: Wait instruction idles the CPU until the next interrupt Wait loop (contention for memory access) At most one I/O request is outstanding at a time, no simultaneous I/O processing or even CPU processing After I/O starts, control returns to user program without waiting for I/O completion: System call – request to the operating system to allow user to wait for I/O completion Device-status table contains an entry for each I/O device indicating its type, address, and state Operating system indexes into I/O device table to determine device status and to modify table entry to include interrupt Multiple outstanding I/O operations over time. Also, CPU processing can carry on. 11 Device Status Table 12 Direct Memory Access (DMA) Used for high-speed I/O devices able to transmit information at close to memory speeds Device controller transfers blocks of data from buffer storage directly to main memory without CPU intervention Implies the capability of arbitrating the system bus Only one interrupt is generated per block, rather than the one interrupt per byte 13 DMA (2) 14 Storage Hierarchy Caches, Buffers and a Storage Hierarchy are Essential 15 Storage Hierarchy A great part of this hierarchy is controlled by the Operating System Cache Management Policies Buffer Management Policies Memory Management Policies Principles of Locality: - Temporal Locality - Spatial Locality 16 Protection Dual Mode of Operation I/O Protection All I/O Instructions are privileged. For doing I/O a trap into the operating system must be generated. Memory Protection “User Mode” and “Kernel Mode” In “User Mode” only common instructions can be performed (e.g. arithmetic and logic). In “Kernel Mode” can do anything. A mode bit contains the current mode of operation Kernel mode assumed on traps and on interrupts Each program can only access its memory CPU Protection The CPU must remain in control of the Operating System, even if the applications don’t want to let go. 17 Dual Mode of Operation 18 System Calls, Traps and Interrupts Traps System calls Operating System Interrupts 19 Structure of a System Call 20 Example with a “Hello World” Application! #include <stdio.h> int main() { printf(“Hello World\n”); return 0; } The “strace” program is very useful: It allows you to see what system calls are made and with what parameters! 21 “strace” in Action! 22 System Call Implementation Typically, a number associated with each system call System-call interface maintains a table indexed according to these numbers The system call interface invokes intended system call in OS kernel and returns status of the system call and any return values The caller needs to know nothing about how the system call is implemented Just needs to obey an API and understand what the OS will do as a result call Most details of OS interface are hidden from the programmer by the API 23 System Call Example (Win32 API) Quick Question: Why use function libraries instead of system calls?? 24 System Call Implementation (2) Often, more information is required than simply the identity of the desired system call Exact type and amount of information vary according to OS and call Three general methods used to pass parameters to the OS Simplest: pass the parameters in registers Parameters stored in a block, or table, in memory, and address of block passed as a parameter in a register In some cases, there may be more parameters than registers This approach is taken by Linux and Solaris Parameters placed, or pushed, onto the stack by the program and popped off the stack by the operating system Block and stack methods do not limit the number or length of parameters being passed 25 System Call Parameter Passing 26 Memory Protection Each program must only be able to access its own memory Segmentation is based on having a base pointer and a limit for each process running Segmentation Virtual Memory (Mostly Used Today) Any access made outside of its “space” generates a trap and normally leads to the process being killed Virtual Memory is based on having a table that translates “virtual addresses” into real ones Normally, there is such a table for each process Each process sees all the address space An access made to an non existing page generates a trap and normally leads to the process being killed 27 Segmentation 28 Virtual Memory 4Gb 4Gb Disk 5000 1000 1000 0 0 Address Space of Process A 256Mb Address Space of Process B Address Translation Table 0 Physical Memory (simplified) 29 Multiprogramming Multiprogramming: maintaining several jobs in memory, active at the same time, so that when the current program can no longer run (for example because it’s blocked waiting for I/O), another is available to run Optimizes resource utilization: CPU and I/O Time Multiplexed CPU CPU E.g. Windows 95/98! 30 Multitasking Multitasking is an extension of multiprogramming in which the execution of the active programs is time-sliced: Each program runs for a short period of time, then another is run. When a program is running and is forcibly replaced by another, typically with a higher priority, it is said to have been preempted, thus the term Preemptive Operating Systems 31 Multitasking For implementing multitasking, a non-maskable interrupt must connected to a hardware timer Every few milliseconds (e.g. 100ms), the interrupt causes a task (or process) switch User Level total = 0; for (int i=0; i<20000; i++) total = total + i; printf(“total=%d\n”, total); Kernel Level while (!feof(fd)) { if (fscanf(fd, “%d”, &d) == 1) printf(“%d\n”, d); } (...) Interrupt Handler 32 Important Note Mode Switch != Task Switch Although they are both quite heavy! 33 Nowadays… Windows XP, Linux 2.6.xx: Preemptive multitasking operating systems using virtual memory Each process thinks it has the whole computer for itself “Virtual Machine” 34 Operating System Architecture and Structures Currently, there are two dominant architectures… Microkernel: Moves as much as possible from the kernel into “user” space Communication takes place between user modules using message passing Benefits: Easier to extend a microkernel Easier to port the operating system to new architectures More reliable (less code is running in kernel mode) More secure Detriments: SLOW: Performance overhead of user space to kernel space communication 35 Operating System Architecture and Structures Currently, there are two dominant architectures… Monolithic: Consists of everything below the system-call interface and above the physical hardware Provides the file system, CPU scheduling, memory management, and other operating-system functions; a large number of functions for one level Benefits: FAST! Detriments: Less reliable (more code is running in kernel mode) Less secure No so easy to port to new architectures (… it depends) 36 Operating System Architecture and Structures Most modern operating systems implement kernel modules Uses “object-oriented approach” Each core component is separate Each talks to the others over known interfaces Each is loadable as needed within the kernel Benefits It’s easier to extend the operating system Allows to isolate functionality in well defined software entities, making the OS more maintainable and reliability 37 Kernel Modules in Solaris 38 Operating System Architecture and Structures Virtual Machines Facet A: “Abstract Machine” with a certain ISA (e.g. Java, MS.NET) Good for portability, allowing running the same unmodified application in different physical architectures Facet B: Software that allows different operating systems to be run in parallel giving them the illusion of “having a whole machine” (e.g. VMWARE, Xen) Allows for server consolidation, software testing, software fault tolerance, etc. 39 Microsoft .NET CLR .NET Application The CLR virtual machine Host Operating System Hardware 40 VMWARE Architecture 41 Operating System Booting Every time the computer wakes up, it starts executing code at a certain address At that address there is no RAM! What’s mapped there it’s an EPROM with the BIOS! The BIOS contains a small program that performs a certain number of functions: On your PC, it’s address 0x000FFFF0! Executes the POST test (Power On Self Test)… Looks and initializes the Graph Card… and other devices (…) Locates the device where to boot from… (assume a disk) Tries to execute the code at cylinder 0, head 0, sector 1! At the first sector of the disk resides the MBR: Master Boot Record 42 Operating System Booting (2) The program in the MBR checks the primary partition table of the disk If it finds a primary partition marked active, it starts executing the code of its volume boot sector This volume boot sector normally consists in a boot loader which, eventually, loads the code of the operating system and starts to execute it The operating system has to setup all the necessary data structures (e.g. special registers of the processor). The last step before entering its “main execution stage” is switching to protected mode And… that’s it! 43 Reference Chapter 1: Introduction 1.1, 1.2, 1.4, 1.5, 1.6, 1.7, 1.8, 1.9 Chapter 2: Operating Systems Structures All chapter 2! 2.1, 2.2, 2.3, 2.4, 2.5, 2.6, 2.7, 2.8, 2.9, 2.10 44













































![[Lecture 1, part 3] Kernel interaction with the hardware: Interrupt](http://s1.studyres.com/store/data/014183875_1-7af0f6b03bedcfbf8972c6054b446a98-150x150.png)