* Your assessment is very important for improving the workof artificial intelligence, which forms the content of this project
Download VA ECHCS Data Privacy and Security Plan Checklist
Survey
Document related concepts
Transcript
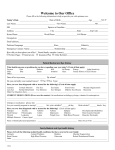
Data Privacy and Security Plan Checklist Please answer all applicable questions listed below. Every question will not necessarily be applicable to your study. If you believe any question is not applicable, you should still address the question as "N/A". This should be submitted as part of the Initial Review Application. Title of Study: ______________________________________________________________________________________ Date: _____________________ Name of Principal Investigator: ________________________ Name of VA Principal Investigator: ___________________ Data Use: Is there a Data Use Agreement? Yes No Is there a Memorandum of Understanding (MOU) in place? (Resource: ISO) Yes No Is there an Interconnection Service Agreement (ISA) in place (may be combined with an MOU if appropriate)? (Resource: ISO) Yes No Is there a contract service involved with this protocol Yes No Is Patient Health Information involved with the service contract this protocol) Yes No (If yes, then a BAA is needed for Data Privacy and Security: Per VA policy you are required to report within 1 hour of any security incident i.e. theft or loss of data or storage media, unauthorized access of sensitive data or storage devices or non-compliance with security controls to the following people: Information Security Officers Eduardo Lorenzo, 303-316-6618 [email protected] Privacy Officers Jeffrey Day, 303-399-8020 ext. 2080 [email protected] John Westfall, 303-370-7581 [email protected] Lesley Petersen, 303-399-8020, ext. 2082 [email protected] E-mail: [email protected] E-Mail: [email protected] ACOS: Robert Keith, 303-399-8020, x3182; E-Mail: [email protected] Records Manager: Norbert Zick, 303-399-8020 ext. 2973 [email protected] Please acknowledge understanding of above policy requirement Yes No Is identifiable Information collected? Yes No If yes, please give detail what is collected: ________________ _______________________________________________________________________________________________ Will the PHI collected be de-identified? Yes No If yes, who will have access to the de-identified information? ______________________________________ How will the data be de-identified? ___________________________________________________________ Revised 8/3/2016 Page 1 How will the data elements that are being collected or abstracted be stored? Electronic Paper Please provide how you plan on safeguarding the collected data? __________________________________ Describe the physical security for all areas where data is stored or processed? ________________________ List all individuals who will have access to the physical location where your data will be kept? _______________________________________________________________________________________ Termination of Data Access: Please explain how access will be removed from personnel who are no longer part of the research team? _________________________________________________________________________________ Has a waiver been submitted to the VA CIO for the use of "Other Equipment" (OE) in accordance with VA Handbook 6500? (Resource ISO or CIO) Yes No N/A Describe the method by which data will be returned to the VA at either the end of study, or by demand of the VA. _______________________________________________________________________________________________ Will any Protected Health Information (PHI) and/or Personally Identifiable Information (PII) be transmitted or transported? Yes No If so, how (e.g. security bag, thumb drive, disc)? ________________________________________ Has approval to transport, transmit, access, and store VA sensitive information been obtained in accordance with VA Handbook 6500? (Resource ISO) Yes No NA If electronically, describe the process and all protections in place (e.g. Public Infrastructure (PKI, a software that provides the ability to email sensitive information in a secure manner), encrypted CD sent via FedEx, etc). _________________ Will any third party be provided PHI or PII information in either paper or electronic format (Sponsor, Lab, Affiliate, etc.)? Yes No Accounting of Disclosure: Will PHI be shared with an outside entity (e.g. University, sponsor)? Yes No If yes, who will be responsible for documenting and tracking the accounting of disclosure if the PHI is sent to an outside entity (e.g. coordinator, PI.)? ________________________________________________________________________ Notice of Privacy Practices: Will you be enrolling non veteran’s participants in this research? Yes No NOTE: If yes, you will need to provide a Notice of Privacy Practices to each participant and obtain a signed acknowledgement receipt. The signed acknowledgement receipt will be forward to the facility Privacy Officer. Confidentiality: Is staff who has access to and/or will be working with the data been properly approved and granted appropriate VA status (e.g. Without Compensation (WOC), Inter-agency Personnel Agreement (IPA), employee, etc)? Yes No Is staff that has access to and/or will be working with the data completed all VA and IRB mandatory annual training (VA Privacy & Info Security Awareness, CITI, VA Info Security 201, etc). (Resource: VA Research Training Coordinator) Yes No Revised 8/3/2016 Page 2 HIPAA Waiver: Is there a plan to protect identifiers from improper use or disclosure? Yes No If yes, please explain: ____ ____________________________________________________________________________________________ Written Assurance of Protection: The request for waiver of HIPAA authorization provides adequate written assurance that the requested information will be protected from improper use and disclosure and will not be reused or disclosed to any other person or entity, except as required by law, for authorized oversight of the research study, or for other research for which the use or disclosure of the requested information would be permitted by the HIPAA Privacy Rule. Yes No If yes, please explain: __________________________________________________________________________ Could the research practicably be done without the access to and use of the requested information? Yes No If no, please explain: _______________________________________________________________________________ _____________________________ Signature of VA Principal Investigator Revised 8/3/2016 Page 3