Proceedings of MobiSys 2003: The First International Conference on
... according to the relational data model. Its architecture is based on an extended client/server middleware architecture, as depicted in figure 3. Mobisnap server and clients rely on unmodified relational database systems to store data. The server holds the primary copy of all data items in the centra ...
... according to the relational data model. Its architecture is based on an extended client/server middleware architecture, as depicted in figure 3. Mobisnap server and clients rely on unmodified relational database systems to store data. The server holds the primary copy of all data items in the centra ...
Backup + Restore
... Exec sp_addumpdevice ‘disk’, ‘Nwindbaclog’, ‘D:\Baclup\Nwind backuplog.bak’ Backup log Northwind To NwindBaclog ...
... Exec sp_addumpdevice ‘disk’, ‘Nwindbaclog’, ‘D:\Baclup\Nwind backuplog.bak’ Backup log Northwind To NwindBaclog ...
IST 274 -10 Database Administrator
... need to use a special password (not CHANGE_ON_INSTALL) •An INTERNAL connection also requires this password •The “Special” password is held encrypted in a password file (PWD.ORA) by the operating
system
•Oracle provides a utility (ORAPWD) that creates the
password file and sets the initial value ...
... need to use a special password (not CHANGE_ON_INSTALL) •An INTERNAL connection also requires this password •The “Special” password is held encrypted in a password file (PWD
transaction
... transactions that run concurrently and generate results that are consistent with the results that would have occurred if they had run separately. • Two-phased locking is one of the techniques used to achieve serializability. ...
... transactions that run concurrently and generate results that are consistent with the results that would have occurred if they had run separately. • Two-phased locking is one of the techniques used to achieve serializability. ...
Principles of Transaction-Oriented Database Recovery
... scheme for logging techniques, which are precisely defined by using the other terms. It is shown that these criteria are related to all relevant questions such as speed and scope of recovery and amount of redundant information required. The primary purpose of this paper, however, is to establish an ...
... scheme for logging techniques, which are precisely defined by using the other terms. It is shown that these criteria are related to all relevant questions such as speed and scope of recovery and amount of redundant information required. The primary purpose of this paper, however, is to establish an ...
T - VUB STARLab
... share no physical component Database systems that run on each site are independent of each other Transactions may access data at one or more sites ...
... share no physical component Database systems that run on each site are independent of each other Transactions may access data at one or more sites ...
Not All Database Security Solutions Are Created Equal
... application/database performance—A database security solution cannot slow down businesscritical database services. Solutions that force you to compromise and disable certain features so as to reduce the database performance impact or reduce your network load can be counterproductive. ...
... application/database performance—A database security solution cannot slow down businesscritical database services. Solutions that force you to compromise and disable certain features so as to reduce the database performance impact or reduce your network load can be counterproductive. ...
Roger. Roger. ?? - Gassenhuber Systementwicklung
... Sometimes it is possible. But many catalogues are not well enough structured for it. In this case the database supplies the necessary material which has been produced in the network onto the layout page. And the designer shapes the more or less preformed objects. This flexibility is one of the outst ...
... Sometimes it is possible. But many catalogues are not well enough structured for it. In this case the database supplies the necessary material which has been produced in the network onto the layout page. And the designer shapes the more or less preformed objects. This flexibility is one of the outst ...
Pangea: An Eager Database Replication Middleware
... delay due to locking, but Tj will abort immediately when it attempts to update x (the abort does not wait until Tj attempts to commit). In short, a transaction will successfully commit only if no other concurrent transaction causing conflict has already been committed. Although the ultimate effect o ...
... delay due to locking, but Tj will abort immediately when it attempts to update x (the abort does not wait until Tj attempts to commit). In short, a transaction will successfully commit only if no other concurrent transaction causing conflict has already been committed. Although the ultimate effect o ...
How Oracle Database Manages Data Concurrency and Consistency
... A SELECT statement is an explicit query and can have nested queries or a join operation. An INSERT statement can use nested queries. UPDATE and DELETE statements can use WHERE clauses or subqueries to affect only some rows in a table rather than all rows. Queries used in INSERT, UPDATE, and DELETE s ...
... A SELECT statement is an explicit query and can have nested queries or a join operation. An INSERT statement can use nested queries. UPDATE and DELETE statements can use WHERE clauses or subqueries to affect only some rows in a table rather than all rows. Queries used in INSERT, UPDATE, and DELETE s ...
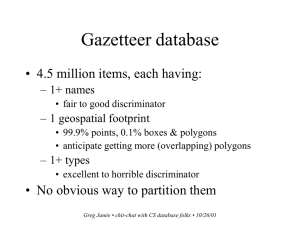
CS chit-chat - ERI people pages
... • Gazetteer is an instance of a much more general problem • To wit: – how to describe the automatic translation of dynamic queries written in an abstract query language to SQL – in an easy, powerful, flexible way – making as few assumptions as possible about the underlying schema – and producing “re ...
... • Gazetteer is an instance of a much more general problem • To wit: – how to describe the automatic translation of dynamic queries written in an abstract query language to SQL – in an easy, powerful, flexible way – making as few assumptions as possible about the underlying schema – and producing “re ...
TIBCO Foresight Transaction Insight
... maintenance. At a high level, partitioning allows the database to sub-divide the data for any particular table into smaller segments based around time or numeric values. For example, instead of keeping the data for all dates in one large table, as shown here… ...
... maintenance. At a high level, partitioning allows the database to sub-divide the data for any particular table into smaller segments based around time or numeric values. For example, instead of keeping the data for all dates in one large table, as shown here… ...
PokerRoom.com Powers High Transaction Online Poker System
... In the late 1990s, two Swedish students decided to take a break from their university studies. Traveling across North America, they made a living as professional poker players. A couple of years later, upon their return to Sweden, they started an online poker site – PokerRoom.com. Today the site, in ...
... In the late 1990s, two Swedish students decided to take a break from their university studies. Traveling across North America, they made a living as professional poker players. A couple of years later, upon their return to Sweden, they started an online poker site – PokerRoom.com. Today the site, in ...
Powerpoint - SQL Saturday
... Workflow for the client library 1. Create a database called a “Shard Map Manager”. 2. Register databases as shards in the SMM. 3. Setup the shard distribution method (lists of keys or ranges). 4. Request a connection from the library based on the sharding key (data dependent routing). 5. Use that c ...
... Workflow for the client library 1. Create a database called a “Shard Map Manager”. 2. Register databases as shards in the SMM. 3. Setup the shard distribution method (lists of keys or ranges). 4. Request a connection from the library based on the sharding key (data dependent routing). 5. Use that c ...
Configuring Automatic Database Space Expansion in
... This white paper introduces system administrators to the automatic database expansion feature in SAP Adaptive Server Enterprise (SAP ASE). Here we will focus on deployments of SAP Business Suite applications running on SAP ASE. With automatic database expansion activated, administrators can further ...
... This white paper introduces system administrators to the automatic database expansion feature in SAP Adaptive Server Enterprise (SAP ASE). Here we will focus on deployments of SAP Business Suite applications running on SAP ASE. With automatic database expansion activated, administrators can further ...
Relational Database Management System
... 33. _______ services is an integrated component within the oracle9! Server and the enabling technology for oracle’s next generation of Open Gateway products. a. Distributed b. Heterogeneous c. Query optimization ...
... 33. _______ services is an integrated component within the oracle9! Server and the enabling technology for oracle’s next generation of Open Gateway products. a. Distributed b. Heterogeneous c. Query optimization ...
Distributed Database Design
... Each set has values from a domain That domain is used in a specific role which is the attribute name Given R(A1, A2, .........., An) r(R) dom (A1) X dom (A2) X ....X dom(An) ...
... Each set has values from a domain That domain is used in a specific role which is the attribute name Given R(A1, A2, .........., An) r(R) dom (A1) X dom (A2) X ....X dom(An) ...
Distributed Databases
... Database systems that run on each site are independent of each other Transactions may access data at one or more sites ...
... Database systems that run on each site are independent of each other Transactions may access data at one or more sites ...
What are the components of instance?
... session information. The amount of PGA memory used and its content depends on the instance configuration, that is, whether the instance is running in dedicated server or shared server mode. B) Oracle Background Process Oracle creates a set of background processes for an instance that interact with e ...
... session information. The amount of PGA memory used and its content depends on the instance configuration, that is, whether the instance is running in dedicated server or shared server mode. B) Oracle Background Process Oracle creates a set of background processes for an instance that interact with e ...
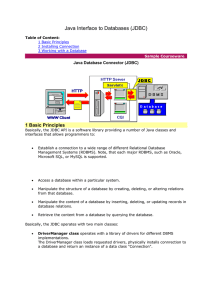
Java Interface to Databases (JDBC)
... 3. a so-called Database URL, which encoded using standard URL syntax (protocol + host + object). The protocol part starts always with "jdbc:" folowed by the name of the RDBMS (in our case "mysql") and terminated with "://" symbols. Thus, the protocol part in our example is "jdbc:mysql://". The host ...
... 3. a so-called Database URL, which encoded using standard URL syntax (protocol + host + object). The protocol part starts always with "jdbc:" folowed by the name of the RDBMS (in our case "mysql") and terminated with "://" symbols. Thus, the protocol part in our example is "jdbc:mysql://". The host ...
Parallel Databases - Brown Computer Science
... than query optimization in sequential databases. Cost models are more complicated, since we must take into account partitioning costs and issues such as skew and resource contention. When scheduling execution tree in parallel system, must decide: ...
... than query optimization in sequential databases. Cost models are more complicated, since we must take into account partitioning costs and issues such as skew and resource contention. When scheduling execution tree in parallel system, must decide: ...
CS2311924
... important to notice the shift of focus between the two papers, with respect to data structure. Older data models focused heavily on semi-structured and XML data in a traditional database.There is also a trend of abstraction by database models only providing API's for operation and manipulation. As m ...
... important to notice the shift of focus between the two papers, with respect to data structure. Older data models focused heavily on semi-structured and XML data in a traditional database.There is also a trend of abstraction by database models only providing API's for operation and manipulation. As m ...
Title Goes Here - Binus Repository
... • DLCHKTIME (db cfg) sets the time interval for checking for deadlocks – It defines the frequency that the database manager checks for deadlocks among all the applications connected to a ...
... • DLCHKTIME (db cfg) sets the time interval for checking for deadlocks – It defines the frequency that the database manager checks for deadlocks among all the applications connected to a ...