qm1 - Michael Nielsen
... state 0.8 00 0.6 11 . A NOT gate is applied to the second qubit, and a measurement performed in the computational basis. What are the probabilities for the possible measurement outcomes? ...
... state 0.8 00 0.6 11 . A NOT gate is applied to the second qubit, and a measurement performed in the computational basis. What are the probabilities for the possible measurement outcomes? ...
JKB_Paper1_QuantumEntanglementTechnologyoftheFuture
... Communication uses information encoded into quantum states called qubits. Photons are generally used for these operations. BB84 and E91 Protocol BB84 protocol is a system that uses photon polarization states to transmit information (Bennett, Giles 2014). It was the first quantum cryptography tool of ...
... Communication uses information encoded into quantum states called qubits. Photons are generally used for these operations. BB84 and E91 Protocol BB84 protocol is a system that uses photon polarization states to transmit information (Bennett, Giles 2014). It was the first quantum cryptography tool of ...
ppt - MIT
... • JHHH showed that for any R, there exists a space Hn,R of dimension 2nR+o(n) such that if S(r)
... • JHHH showed that for any R, there exists a space Hn,R of dimension 2nR+o(n) such that if S(r)
Random non-local games
... 3-SAT formula F = F1 F2 ... Fm. Alice and Bob attempt to prove that they have x1, ..., xn: F(x1, ..., xn)=1. ...
... 3-SAT formula F = F1 F2 ... Fm. Alice and Bob attempt to prove that they have x1, ..., xn: F(x1, ..., xn)=1. ...
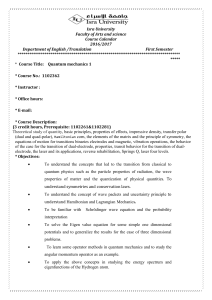
Isra University Faculty of Arts and science Course Calendar 2016
... of the case for the transition of dual-electrode, properties, transit behavior for the transition of dualelectrode, the laser and its applications, reverse rehabilitation, Springs Q, laser four levels. * Objectives: ...
... of the case for the transition of dual-electrode, properties, transit behavior for the transition of dualelectrode, the laser and its applications, reverse rehabilitation, Springs Q, laser four levels. * Objectives: ...
PDF
... Quantum entanglement and squeezing have been exploited in the context of interferometry, frequency measurements, lithography, and algorithms (see for example Refs. [1]) in order to beat classical limitations. In this paper, we show that entanglement and squeezing can also be used to increase the acc ...
... Quantum entanglement and squeezing have been exploited in the context of interferometry, frequency measurements, lithography, and algorithms (see for example Refs. [1]) in order to beat classical limitations. In this paper, we show that entanglement and squeezing can also be used to increase the acc ...
Chapter 1 Atoms Properties of Matter Intensive vs. Extensive
... Chapter 1 Atoms Properties of Matter o Intensive vs. Extensive, physical vs. chemical Chemical Change Physical Change Mixtures and Pure Substances Elements and Compounds o Group or Family o Period or Row o Metals o Nonmetals o Metalloids Chapter 2 Scientific Method SI Units of Measur ...
... Chapter 1 Atoms Properties of Matter o Intensive vs. Extensive, physical vs. chemical Chemical Change Physical Change Mixtures and Pure Substances Elements and Compounds o Group or Family o Period or Row o Metals o Nonmetals o Metalloids Chapter 2 Scientific Method SI Units of Measur ...
solve a nonlinear fourth-order quantum diffusion equation
... In order to solve the nonlinear system (2) numerically, the Nag toolbox routine c05nb, based on a modification of the Powell hybrid method for nonlinear systems, has been employed. This routine proved to be approximately three times faster than the standard Matlab routine fsolve and because of that ...
... In order to solve the nonlinear system (2) numerically, the Nag toolbox routine c05nb, based on a modification of the Powell hybrid method for nonlinear systems, has been employed. This routine proved to be approximately three times faster than the standard Matlab routine fsolve and because of that ...
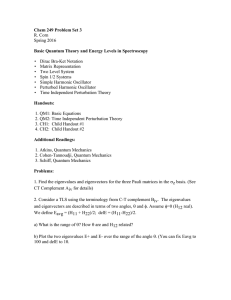
Chem 249 Problem Set 2
... 3. Consider an anharmonic oscillator with the following Hamiltonian: H = H0 + W H0 = p2/2m + kx2/2 W = x3 a. Calculate the energies of H to first order in the perturbation W. Write out formally the first order correction to the eigenstate vector, and then list the states which contribute to the ne ...
... 3. Consider an anharmonic oscillator with the following Hamiltonian: H = H0 + W H0 = p2/2m + kx2/2 W = x3 a. Calculate the energies of H to first order in the perturbation W. Write out formally the first order correction to the eigenstate vector, and then list the states which contribute to the ne ...
48x36 poster template - School of Computer Science and Engineering
... This works for any problem in NPBQP ...
... This works for any problem in NPBQP ...
Quantum Mechanics
... depends only on initial conditions of the problem The question of the distances between the planets used to be the biggest open problem in science. But we now know that it’s a complicated question that isn’t answered by the fundamental theory. ...
... depends only on initial conditions of the problem The question of the distances between the planets used to be the biggest open problem in science. But we now know that it’s a complicated question that isn’t answered by the fundamental theory. ...
planck , s law and the light quantum hypothesis
... If we subdivide the total phase space volume into cells of magnitude h3 , then the number of cells belonging to the frequency domain dv is 4πV (v2/c3) dv. Concerning the kind of subdivision of this type, nothing definitive can be said. However, the total number of cells must be interpreted as the nu ...
... If we subdivide the total phase space volume into cells of magnitude h3 , then the number of cells belonging to the frequency domain dv is 4πV (v2/c3) dv. Concerning the kind of subdivision of this type, nothing definitive can be said. However, the total number of cells must be interpreted as the nu ...
Quantum key distribution
Quantum key distribution (QKD) uses quantum mechanics to guarantee secure communication. It enables two parties to produce a shared random secret key known only to them, which can then be used to encrypt and decrypt messages. It is often incorrectly called quantum cryptography, as it is the most well known example of the group of quantum cryptographic tasks.An important and unique property of quantum key distribution is the ability of the two communicating users to detect the presence of any third party trying to gain knowledge of the key. This results from a fundamental aspect of quantum mechanics: the process of measuring a quantum system in general disturbs the system. A third party trying to eavesdrop on the key must in some way measure it, thus introducing detectable anomalies. By using quantum superpositions or quantum entanglement and transmitting information in quantum states, a communication system can be implemented which detects eavesdropping. If the level of eavesdropping is below a certain threshold, a key can be produced that is guaranteed to be secure (i.e. the eavesdropper has no information about it), otherwise no secure key is possible and communication is aborted.The security of encryption that uses quantum key distribution relies on the foundations of quantum mechanics, in contrast to traditional public key cryptography which relies on the computational difficulty of certain mathematical functions, and cannot provide any indication of eavesdropping at any point in the communication process, or any mathematical proof as to the actual complexity of reversing the one-way functions used. QKD has provable security based on information theory, and forward secrecy.Quantum key distribution is only used to produce and distribute a key, not to transmit any message data. This key can then be used with any chosen encryption algorithm to encrypt (and decrypt) a message, which can then be transmitted over a standard communication channel. The algorithm most commonly associated with QKD is the one-time pad, as it is provably secure when used with a secret, random key. In real world situations, it is often also used with encryption using symmetric key algorithms like the Advanced Encryption Standard algorithm. In the case of QKD this comparison is based on the assumption of perfect single-photon sources and detectors, that cannot be easily implemented.