Another version - Scott Aaronson
... unwanted interaction between a QC and its external environment, “prematurely measuring” the quantum state A few skeptics, in CS and physics, even argue that building a QC will be fundamentally impossible I don’t expect them to be right, but I hope they are! If so, it would be a revolution in physics ...
... unwanted interaction between a QC and its external environment, “prematurely measuring” the quantum state A few skeptics, in CS and physics, even argue that building a QC will be fundamentally impossible I don’t expect them to be right, but I hope they are! If so, it would be a revolution in physics ...
INCONSISTENT HISTORIES REVEALED BY QUANTUM
... The wave function, upon “measurement,” gives rise not only to the particles’ position and momentum but to the entire spacetime region within which it could have resided. Hence the pre-spacetime interaction determines the distances between objects Hence attraction and repulsion ...
... The wave function, upon “measurement,” gives rise not only to the particles’ position and momentum but to the entire spacetime region within which it could have resided. Hence the pre-spacetime interaction determines the distances between objects Hence attraction and repulsion ...
Cavendish Laboratory
... • Theory of Condensed Matter group – numerical electronic structure methods, many body physics, quantum transport, overlap with research activities in Semiconductor ...
... • Theory of Condensed Matter group – numerical electronic structure methods, many body physics, quantum transport, overlap with research activities in Semiconductor ...
Heuristic Optimisation in Design and Analysis
... But we can now simply measure the first qubit and we are guaranteed to see a 0 if the function f is balanced and a 1 if it isn’t. Note we have learned a global property about the system: we don’t actually know the value of any of f(0) or f(1); just that they are (or are not) the same. ...
... But we can now simply measure the first qubit and we are guaranteed to see a 0 if the function f is balanced and a 1 if it isn’t. Note we have learned a global property about the system: we don’t actually know the value of any of f(0) or f(1); just that they are (or are not) the same. ...
Limitations of Quantum Advice and One-Way
... Bob can then compute f(x,y) for Q1(f)2 values of y simultaneously, with probability 0.9 With no communication, he can still do that with probability 0.9/2K, by guessing x=I ...
... Bob can then compute f(x,y) for Q1(f)2 values of y simultaneously, with probability 0.9 With no communication, he can still do that with probability 0.9/2K, by guessing x=I ...
Gerard `t Hooft
... How does God produce random numbers ? Could these random numbers be actually created by “ordinary” physical processes at the Planck scale? ...
... How does God produce random numbers ? Could these random numbers be actually created by “ordinary” physical processes at the Planck scale? ...
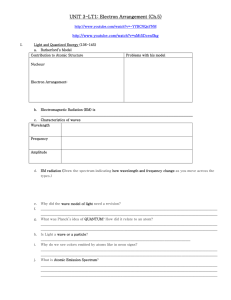
LT1: Electron.NOTES - Simpson County Schools
... EM radiation (Draw the spectrum indicating how wavelength and frequency change as you move across the types.) ...
... EM radiation (Draw the spectrum indicating how wavelength and frequency change as you move across the types.) ...
Quantum Mechanics
... Young’s Double-Slit Experiment Uncertainty Principle due to Heisenberg Schrödinger’s Cat Thought Experiment ...
... Young’s Double-Slit Experiment Uncertainty Principle due to Heisenberg Schrödinger’s Cat Thought Experiment ...
β - Indico
... of amany single particles it becomes as accurate as a particle is highly inaccurate, strong measurement. ...
... of amany single particles it becomes as accurate as a particle is highly inaccurate, strong measurement. ...
Fourth lecture, 28.10.03 (dispersion cancellation, time measurement
... Why? No interference between paths leading to different frequencies at the detectors, because in principle one could go back and measure how much energy had been absorbed. Note: it took a long time-integral to enforce this. If the detector had been open only for 1 fs, it would be impossible to tell ...
... Why? No interference between paths leading to different frequencies at the detectors, because in principle one could go back and measure how much energy had been absorbed. Note: it took a long time-integral to enforce this. If the detector had been open only for 1 fs, it would be impossible to tell ...
Quantum key distribution
Quantum key distribution (QKD) uses quantum mechanics to guarantee secure communication. It enables two parties to produce a shared random secret key known only to them, which can then be used to encrypt and decrypt messages. It is often incorrectly called quantum cryptography, as it is the most well known example of the group of quantum cryptographic tasks.An important and unique property of quantum key distribution is the ability of the two communicating users to detect the presence of any third party trying to gain knowledge of the key. This results from a fundamental aspect of quantum mechanics: the process of measuring a quantum system in general disturbs the system. A third party trying to eavesdrop on the key must in some way measure it, thus introducing detectable anomalies. By using quantum superpositions or quantum entanglement and transmitting information in quantum states, a communication system can be implemented which detects eavesdropping. If the level of eavesdropping is below a certain threshold, a key can be produced that is guaranteed to be secure (i.e. the eavesdropper has no information about it), otherwise no secure key is possible and communication is aborted.The security of encryption that uses quantum key distribution relies on the foundations of quantum mechanics, in contrast to traditional public key cryptography which relies on the computational difficulty of certain mathematical functions, and cannot provide any indication of eavesdropping at any point in the communication process, or any mathematical proof as to the actual complexity of reversing the one-way functions used. QKD has provable security based on information theory, and forward secrecy.Quantum key distribution is only used to produce and distribute a key, not to transmit any message data. This key can then be used with any chosen encryption algorithm to encrypt (and decrypt) a message, which can then be transmitted over a standard communication channel. The algorithm most commonly associated with QKD is the one-time pad, as it is provably secure when used with a secret, random key. In real world situations, it is often also used with encryption using symmetric key algorithms like the Advanced Encryption Standard algorithm. In the case of QKD this comparison is based on the assumption of perfect single-photon sources and detectors, that cannot be easily implemented.