Physics 880K20: Problem Set 4 Due Wednesday, February 22 by 5PM
... Physics 880K20: Problem Set 4 ...
... Physics 880K20: Problem Set 4 ...
Syllabus
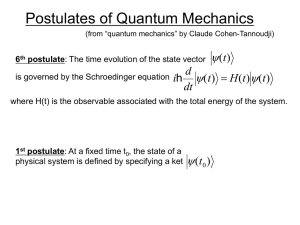
... The main objective of this course is to examine the theoretical basis for our present understanding of the structure of matter at the atomic and molecular level. To that end we will review those aspects of quantum mechanics that play the most important role in this understanding. This includes the s ...
... The main objective of this course is to examine the theoretical basis for our present understanding of the structure of matter at the atomic and molecular level. To that end we will review those aspects of quantum mechanics that play the most important role in this understanding. This includes the s ...
G040162-00 - DCC
... – Single-spin: Markovian but non-linear – Next generation of devices: both kinds! ...
... – Single-spin: Markovian but non-linear – Next generation of devices: both kinds! ...
Chapter 1 Statistical Mechanics of Quantum Dots Chapter 2 Artificial
... dynamical properties of quantum dots. These closed systems which consist of a substantial but finite number of electrons usually demonstrate behavior that is called quantum chaos.' This behavior can be caused by disorder, the geometry of a quantum dot, or interactions between electrons. The phenomen ...
... dynamical properties of quantum dots. These closed systems which consist of a substantial but finite number of electrons usually demonstrate behavior that is called quantum chaos.' This behavior can be caused by disorder, the geometry of a quantum dot, or interactions between electrons. The phenomen ...
Quantum Error-Correction Codes on Abelian Groups
... and the ones she sends to Bob. If Alice wants to measure her remaining qubits according to the check matrix for CSSG (C1 , C2 ), she obtains random values for x and z, and if she wants to measure the m EPR pair in the standard basis, she obtains a random choice of v. Then the remaining n qubits are ...
... and the ones she sends to Bob. If Alice wants to measure her remaining qubits according to the check matrix for CSSG (C1 , C2 ), she obtains random values for x and z, and if she wants to measure the m EPR pair in the standard basis, she obtains a random choice of v. Then the remaining n qubits are ...
Coherent Control
... to the question of how the present determines the future. In essence, in order to predict future probabilities, we need to (numerically) propagate the time-dependent Schrödinger equation from the present to the future. It is interesting to note that classical mechanics of macroscopic bodies, though ...
... to the question of how the present determines the future. In essence, in order to predict future probabilities, we need to (numerically) propagate the time-dependent Schrödinger equation from the present to the future. It is interesting to note that classical mechanics of macroscopic bodies, though ...
Quantum phase transition - Condensed Matter Theory and Quantum
... Three critical exponents can be defined this way: α=Λ(C,t), β=Λ(m,t) and γ=Λ(χ,t), where C is the heat capacity, m is the magnetization and χ is the magnetic susceptibility. ...
... Three critical exponents can be defined this way: α=Λ(C,t), β=Λ(m,t) and γ=Λ(χ,t), where C is the heat capacity, m is the magnetization and χ is the magnetic susceptibility. ...
PDF
... Definition 1.1. Let us recall that a quantum automaton is defined as a quantum algebraic topology object– the quantum triple QA = (G, H −
... Definition 1.1. Let us recall that a quantum automaton is defined as a quantum algebraic topology object– the quantum triple QA = (G, H −
Quantum states
... Quantum nonlocality: Spooky action at a distance Two entangled particles cannot be separated, even after they leave the interaction zone , where they became entangled. They act as a single object. Thus, they appear in two different places at the same time. ...
... Quantum nonlocality: Spooky action at a distance Two entangled particles cannot be separated, even after they leave the interaction zone , where they became entangled. They act as a single object. Thus, they appear in two different places at the same time. ...
Quantum key distribution
Quantum key distribution (QKD) uses quantum mechanics to guarantee secure communication. It enables two parties to produce a shared random secret key known only to them, which can then be used to encrypt and decrypt messages. It is often incorrectly called quantum cryptography, as it is the most well known example of the group of quantum cryptographic tasks.An important and unique property of quantum key distribution is the ability of the two communicating users to detect the presence of any third party trying to gain knowledge of the key. This results from a fundamental aspect of quantum mechanics: the process of measuring a quantum system in general disturbs the system. A third party trying to eavesdrop on the key must in some way measure it, thus introducing detectable anomalies. By using quantum superpositions or quantum entanglement and transmitting information in quantum states, a communication system can be implemented which detects eavesdropping. If the level of eavesdropping is below a certain threshold, a key can be produced that is guaranteed to be secure (i.e. the eavesdropper has no information about it), otherwise no secure key is possible and communication is aborted.The security of encryption that uses quantum key distribution relies on the foundations of quantum mechanics, in contrast to traditional public key cryptography which relies on the computational difficulty of certain mathematical functions, and cannot provide any indication of eavesdropping at any point in the communication process, or any mathematical proof as to the actual complexity of reversing the one-way functions used. QKD has provable security based on information theory, and forward secrecy.Quantum key distribution is only used to produce and distribute a key, not to transmit any message data. This key can then be used with any chosen encryption algorithm to encrypt (and decrypt) a message, which can then be transmitted over a standard communication channel. The algorithm most commonly associated with QKD is the one-time pad, as it is provably secure when used with a secret, random key. In real world situations, it is often also used with encryption using symmetric key algorithms like the Advanced Encryption Standard algorithm. In the case of QKD this comparison is based on the assumption of perfect single-photon sources and detectors, that cannot be easily implemented.