Winter 2008 Physics 315 / 225
... The intensity is proportional to the number of photons (E=hf for each photon) A photon is transmitted with some Probability (depends on initial photon state and on transmission axis) After a Polaroid sheet we know the polarization state of the photon ...
... The intensity is proportional to the number of photons (E=hf for each photon) A photon is transmitted with some Probability (depends on initial photon state and on transmission axis) After a Polaroid sheet we know the polarization state of the photon ...
Ion Trap Quantum Technology for Quantum Computing
... Fig.1: Ion trap technology: microfabricated “surface electrode” ion traps built at Oxford. Both traps were entirely designed, fabricated in-house, and characterized by Ph.D. students. (a) This chip trap was the first surface trap fabricated outside the U.S.; the inset shows a string of three calcium ...
... Fig.1: Ion trap technology: microfabricated “surface electrode” ion traps built at Oxford. Both traps were entirely designed, fabricated in-house, and characterized by Ph.D. students. (a) This chip trap was the first surface trap fabricated outside the U.S.; the inset shows a string of three calcium ...
Quantum information with Rydberg atoms
... 1) Σcx |x> Σ (-1) f(x) cx |x> (-1) if x matches the “marked“ x0 2) Inversion of cx about their mean. ...
... 1) Σcx |x> Σ (-1) f(x) cx |x> (-1) if x matches the “marked“ x0 2) Inversion of cx about their mean. ...
Physics 601 Syllabus
... The main objective of this course is to examine the theoretical basis for our present understanding of the structure of matter at the atomic and molecular level. To that end we will review those aspects of quantum mechanics that play the most important role in this understanding. This includes the s ...
... The main objective of this course is to examine the theoretical basis for our present understanding of the structure of matter at the atomic and molecular level. To that end we will review those aspects of quantum mechanics that play the most important role in this understanding. This includes the s ...
Slide 1
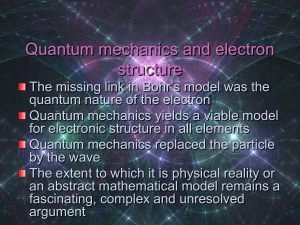
... oAn atom with its e- in the lowest possible energy levels is said to be in its “ground state” oWhen an e- occupies an orbit greater than the lowest possible energy level it is said to be in an “excited state” oΔE=-Rhc(1/nf2 - 1/ni2) Rhc=1312 kJ/mol Wave/particle duality oTaken from idea that light ...
... oAn atom with its e- in the lowest possible energy levels is said to be in its “ground state” oWhen an e- occupies an orbit greater than the lowest possible energy level it is said to be in an “excited state” oΔE=-Rhc(1/nf2 - 1/ni2) Rhc=1312 kJ/mol Wave/particle duality oTaken from idea that light ...
Syllabus
... The main objective of this course is to examine the theoretical basis for our present understanding of the structure of matter at the atomic and molecular level. To that end we will review those aspects of quantum mechanics that play the most important role in this understanding. This includes the s ...
... The main objective of this course is to examine the theoretical basis for our present understanding of the structure of matter at the atomic and molecular level. To that end we will review those aspects of quantum mechanics that play the most important role in this understanding. This includes the s ...
Quantum entropy and its use
... Entropy is a central quantity in information theory, probability and physics. This spring school will focus on fundamental concepts and basic operational interpretations of entropy with a particular focus on applications to quantum mechanics. The goal is provide a thorough overview ranging from fund ...
... Entropy is a central quantity in information theory, probability and physics. This spring school will focus on fundamental concepts and basic operational interpretations of entropy with a particular focus on applications to quantum mechanics. The goal is provide a thorough overview ranging from fund ...
Lecture 33
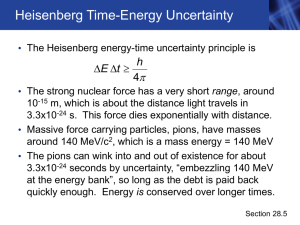
... E= h/4t is as large as their energy (Lect. 23, Slide 9). They get away with violating energy conservation because of the uncertainty relation: They vanish before they can be caught cheating. • Although we can’t catch virtual particles, their effects can be measured with great accuracy (Lect. 34, ...
... E= h/4t is as large as their energy (Lect. 23, Slide 9). They get away with violating energy conservation because of the uncertainty relation: They vanish before they can be caught cheating. • Although we can’t catch virtual particles, their effects can be measured with great accuracy (Lect. 34, ...
Quantum Complexity and Fundamental Physics
... Intermediate models of computation between P and BQP (highly mixed states? restricted sets of gates?) Foil theories that lead to complexity classes slightly larger than BQP (only example I know of: hidden variables) A sane notion of “quantum gravity polynomial-time” (first step: a sane notion of tim ...
... Intermediate models of computation between P and BQP (highly mixed states? restricted sets of gates?) Foil theories that lead to complexity classes slightly larger than BQP (only example I know of: hidden variables) A sane notion of “quantum gravity polynomial-time” (first step: a sane notion of tim ...
Chapter 28 - Purdue Physics
... molecule can absorb a photon only if the photon energy precisely matches the pigment energy level • More realistically (C), a range of energies is absorbed • Quantum mechanics and the existence of quantized energies for both photons and pigment molecules are ...
... molecule can absorb a photon only if the photon energy precisely matches the pigment energy level • More realistically (C), a range of energies is absorbed • Quantum mechanics and the existence of quantized energies for both photons and pigment molecules are ...
Quantum key distribution
Quantum key distribution (QKD) uses quantum mechanics to guarantee secure communication. It enables two parties to produce a shared random secret key known only to them, which can then be used to encrypt and decrypt messages. It is often incorrectly called quantum cryptography, as it is the most well known example of the group of quantum cryptographic tasks.An important and unique property of quantum key distribution is the ability of the two communicating users to detect the presence of any third party trying to gain knowledge of the key. This results from a fundamental aspect of quantum mechanics: the process of measuring a quantum system in general disturbs the system. A third party trying to eavesdrop on the key must in some way measure it, thus introducing detectable anomalies. By using quantum superpositions or quantum entanglement and transmitting information in quantum states, a communication system can be implemented which detects eavesdropping. If the level of eavesdropping is below a certain threshold, a key can be produced that is guaranteed to be secure (i.e. the eavesdropper has no information about it), otherwise no secure key is possible and communication is aborted.The security of encryption that uses quantum key distribution relies on the foundations of quantum mechanics, in contrast to traditional public key cryptography which relies on the computational difficulty of certain mathematical functions, and cannot provide any indication of eavesdropping at any point in the communication process, or any mathematical proof as to the actual complexity of reversing the one-way functions used. QKD has provable security based on information theory, and forward secrecy.Quantum key distribution is only used to produce and distribute a key, not to transmit any message data. This key can then be used with any chosen encryption algorithm to encrypt (and decrypt) a message, which can then be transmitted over a standard communication channel. The algorithm most commonly associated with QKD is the one-time pad, as it is provably secure when used with a secret, random key. In real world situations, it is often also used with encryption using symmetric key algorithms like the Advanced Encryption Standard algorithm. In the case of QKD this comparison is based on the assumption of perfect single-photon sources and detectors, that cannot be easily implemented.