Recenti sviluppi della Meccanica Quantistica: dalla
... several variables, not in a relatively small set of numbers ... In order to verify the [quantum] theory in its generality, at least a succession of two measurements are needed. There is in general no way to determine the original state of the system, but having produced a definite state by a first m ...
... several variables, not in a relatively small set of numbers ... In order to verify the [quantum] theory in its generality, at least a succession of two measurements are needed. There is in general no way to determine the original state of the system, but having produced a definite state by a first m ...
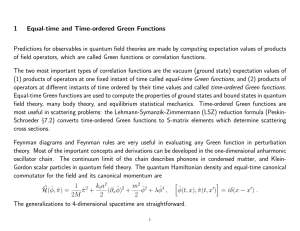
Chapter 5
... circling around a nucleus and concluded that electrons have specific energy levels. • Erwin Schrödinger (1887–1961): Proposed quantum mechanical model of atom, which focuses on wavelike properties of electrons. ...
... circling around a nucleus and concluded that electrons have specific energy levels. • Erwin Schrödinger (1887–1961): Proposed quantum mechanical model of atom, which focuses on wavelike properties of electrons. ...
Fundamentals of quantum mechanics Quantum Theory of Light and Matter
... σA2 = hψ|(Â − hAi)(Â − hA)|ψi = ha|ai σB2 ...
... σA2 = hψ|(Â − hAi)(Â − hA)|ψi = ha|ai σB2 ...
From quantum to quantum computer
... (1) One of the founders of the quantum concept (2) A first, thought there must be something wrong with the quantum theory. (3) After much debate with Bohr, he finally was convinced that QM gives correct results, but it could not be the final theory. It is incomplete! ...
... (1) One of the founders of the quantum concept (2) A first, thought there must be something wrong with the quantum theory. (3) After much debate with Bohr, he finally was convinced that QM gives correct results, but it could not be the final theory. It is incomplete! ...
18.7 NnV mx - Leiden Institute of Physics
... At the quantum level, common sense is often violated — for example, by pairs of entangled photons in which each seems to ‘know’ about the state of the other. Entanglement may be more robust than had been thought. wo particles are just two particles, aren’t they? Well, no, actually — not always. In t ...
... At the quantum level, common sense is often violated — for example, by pairs of entangled photons in which each seems to ‘know’ about the state of the other. Entanglement may be more robust than had been thought. wo particles are just two particles, aren’t they? Well, no, actually — not always. In t ...
Talk, 15 MB - Seth Aubin - College of William and Mary
... Surprise! Reach Tc with only a 30x loss in number. (trap loaded with 2x107 atoms) Experimental cycle = 5 - 15 seconds ...
... Surprise! Reach Tc with only a 30x loss in number. (trap loaded with 2x107 atoms) Experimental cycle = 5 - 15 seconds ...
ppt
... and B) don't commute leads to a problem. A and B represent momentum and position respectively (uncertainty principle) this means knowing the momentum of the particle means its coordinate has no physical reality. ...
... and B) don't commute leads to a problem. A and B represent momentum and position respectively (uncertainty principle) this means knowing the momentum of the particle means its coordinate has no physical reality. ...
Quantum key distribution
Quantum key distribution (QKD) uses quantum mechanics to guarantee secure communication. It enables two parties to produce a shared random secret key known only to them, which can then be used to encrypt and decrypt messages. It is often incorrectly called quantum cryptography, as it is the most well known example of the group of quantum cryptographic tasks.An important and unique property of quantum key distribution is the ability of the two communicating users to detect the presence of any third party trying to gain knowledge of the key. This results from a fundamental aspect of quantum mechanics: the process of measuring a quantum system in general disturbs the system. A third party trying to eavesdrop on the key must in some way measure it, thus introducing detectable anomalies. By using quantum superpositions or quantum entanglement and transmitting information in quantum states, a communication system can be implemented which detects eavesdropping. If the level of eavesdropping is below a certain threshold, a key can be produced that is guaranteed to be secure (i.e. the eavesdropper has no information about it), otherwise no secure key is possible and communication is aborted.The security of encryption that uses quantum key distribution relies on the foundations of quantum mechanics, in contrast to traditional public key cryptography which relies on the computational difficulty of certain mathematical functions, and cannot provide any indication of eavesdropping at any point in the communication process, or any mathematical proof as to the actual complexity of reversing the one-way functions used. QKD has provable security based on information theory, and forward secrecy.Quantum key distribution is only used to produce and distribute a key, not to transmit any message data. This key can then be used with any chosen encryption algorithm to encrypt (and decrypt) a message, which can then be transmitted over a standard communication channel. The algorithm most commonly associated with QKD is the one-time pad, as it is provably secure when used with a secret, random key. In real world situations, it is often also used with encryption using symmetric key algorithms like the Advanced Encryption Standard algorithm. In the case of QKD this comparison is based on the assumption of perfect single-photon sources and detectors, that cannot be easily implemented.