Information Loss
... known. It seems to me that there is plenty of room for nuances in the dictionary when black holes are present that would allow the late time observable correspondence to fail. Put another way, why can’t the CFT state at late times continue to encode the information that went into a black hole, even ...
... known. It seems to me that there is plenty of room for nuances in the dictionary when black holes are present that would allow the late time observable correspondence to fail. Put another way, why can’t the CFT state at late times continue to encode the information that went into a black hole, even ...
4.4 The Hamiltonian and its symmetry operations
... allows to calculate the time evolution easily. REMARK: This is just one example in natural science where discussing the symmetries serve fundamental information on the system. The search for symmetries in nature and the formulation of mathematical models based on sometimes quite abstract symmetries ...
... allows to calculate the time evolution easily. REMARK: This is just one example in natural science where discussing the symmetries serve fundamental information on the system. The search for symmetries in nature and the formulation of mathematical models based on sometimes quite abstract symmetries ...
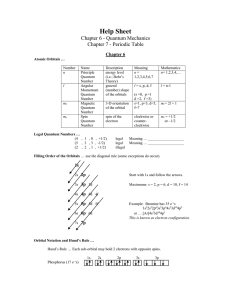
Help Sheet
... Three unpaired electrons in the valence shell. Diamagnetism and Paramagnetism … Paramagnetic, attracted by a magnet. ...
... Three unpaired electrons in the valence shell. Diamagnetism and Paramagnetism … Paramagnetic, attracted by a magnet. ...
Observer Effect - Continuum Center
... our attention on is an act of observation and consciousness and we can choose. The frontal lobe gives us the capacity, the power to choose where and how we focus our attention. We are observers and as such are part of bringing "reality" into existence...collapsing potentiality into actuality. Becaus ...
... our attention on is an act of observation and consciousness and we can choose. The frontal lobe gives us the capacity, the power to choose where and how we focus our attention. We are observers and as such are part of bringing "reality" into existence...collapsing potentiality into actuality. Becaus ...
WP1
... with themselves! What! How? Does a single electron go through both slits (to cause the interference)? How can an electron that causes a localized flash on the absorbing screen go through both slits? Can an electron be in two places at once? Counter common sense. As Feynman said “No one understands q ...
... with themselves! What! How? Does a single electron go through both slits (to cause the interference)? How can an electron that causes a localized flash on the absorbing screen go through both slits? Can an electron be in two places at once? Counter common sense. As Feynman said “No one understands q ...
Unit 2 – Electrons and Periodic Behavior Cartoon courtesy of
... orientation of the electron’s orbital with respect to the three axes in space (x,y,z). Have to split up p, d, f orbitals. ...
... orientation of the electron’s orbital with respect to the three axes in space (x,y,z). Have to split up p, d, f orbitals. ...
Quantum Zeno Effect, Anti Zeno Effect and the Quantum recurrence theorem
... where Ps (t) is the probability of finding the particle undecayed in each measurement (this is important). We get a decay factor of Γ = |V |2 τ ...
... where Ps (t) is the probability of finding the particle undecayed in each measurement (this is important). We get a decay factor of Γ = |V |2 τ ...
Single-photon sources based on NV
... Attach a GaP layer on top of a bulk diamond as the waveguide (2.26 eV bandgap, n = 3.3) ...
... Attach a GaP layer on top of a bulk diamond as the waveguide (2.26 eV bandgap, n = 3.3) ...
PPT
... Lab 1: Background • Entangled photons cannot be described in terms of single particle states • A measurement performed on one of a pair of entangled photons will affect the outcome of a measurement performed on the other one. • Bell’s inequality is a classical relationship. A violation of Bell’s in ...
... Lab 1: Background • Entangled photons cannot be described in terms of single particle states • A measurement performed on one of a pair of entangled photons will affect the outcome of a measurement performed on the other one. • Bell’s inequality is a classical relationship. A violation of Bell’s in ...
Quantum key distribution
Quantum key distribution (QKD) uses quantum mechanics to guarantee secure communication. It enables two parties to produce a shared random secret key known only to them, which can then be used to encrypt and decrypt messages. It is often incorrectly called quantum cryptography, as it is the most well known example of the group of quantum cryptographic tasks.An important and unique property of quantum key distribution is the ability of the two communicating users to detect the presence of any third party trying to gain knowledge of the key. This results from a fundamental aspect of quantum mechanics: the process of measuring a quantum system in general disturbs the system. A third party trying to eavesdrop on the key must in some way measure it, thus introducing detectable anomalies. By using quantum superpositions or quantum entanglement and transmitting information in quantum states, a communication system can be implemented which detects eavesdropping. If the level of eavesdropping is below a certain threshold, a key can be produced that is guaranteed to be secure (i.e. the eavesdropper has no information about it), otherwise no secure key is possible and communication is aborted.The security of encryption that uses quantum key distribution relies on the foundations of quantum mechanics, in contrast to traditional public key cryptography which relies on the computational difficulty of certain mathematical functions, and cannot provide any indication of eavesdropping at any point in the communication process, or any mathematical proof as to the actual complexity of reversing the one-way functions used. QKD has provable security based on information theory, and forward secrecy.Quantum key distribution is only used to produce and distribute a key, not to transmit any message data. This key can then be used with any chosen encryption algorithm to encrypt (and decrypt) a message, which can then be transmitted over a standard communication channel. The algorithm most commonly associated with QKD is the one-time pad, as it is provably secure when used with a secret, random key. In real world situations, it is often also used with encryption using symmetric key algorithms like the Advanced Encryption Standard algorithm. In the case of QKD this comparison is based on the assumption of perfect single-photon sources and detectors, that cannot be easily implemented.







![Quantum computers - start [kondor.etf.rs]](http://s1.studyres.com/store/data/008623556_1-6dce2335493dbd35f44ebeba6fa8564e-300x300.png)