Unit OS2: Operating Systems Principles
... Explain why Windows NT 4 move windows manager and graphics services from running in the context of the Windows Subsystem process to a set of callable services running in kernel mode. The primary reason for this shift was to improve overall system performance. Having a separate server process that co ...
... Explain why Windows NT 4 move windows manager and graphics services from running in the context of the Windows Subsystem process to a set of callable services running in kernel mode. The primary reason for this shift was to improve overall system performance. Having a separate server process that co ...
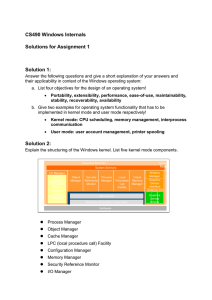
Windows Kernel Internals Overview - reverse - reverse
... Goals of the NT System • Reliability – Nothing should be able to crash the OS. Anything that crashes the OS is a bug and we won’t ship until it is fixed • Security – Built into the design from day one • Portability – Support more than one processor, avoid assembler, abstract HW dependencies. • Exte ...
... Goals of the NT System • Reliability – Nothing should be able to crash the OS. Anything that crashes the OS is a bug and we won’t ship until it is fixed • Security – Built into the design from day one • Portability – Support more than one processor, avoid assembler, abstract HW dependencies. • Exte ...
Blizzard Bag #2 – PC Maintenance
... (Internet Explorer) as part of the operating system This caused a lot of controversy and helped involve Microsoft in an antitrust suit that made it all the way to the United States Supreme Court. ...
... (Internet Explorer) as part of the operating system This caused a lot of controversy and helped involve Microsoft in an antitrust suit that made it all the way to the United States Supreme Court. ...
Windows Kernel Internals Overview
... Lots of legacy code now hooked to the internet Most code written to work correctly under normal conditions Security design issues are subtle, particularly w.r.t. DoS Constantly evolving threats: Stack-buffer overruns, Heap overruns, Format string overruns One byte overruns, Integer overflows © Micro ...
... Lots of legacy code now hooked to the internet Most code written to work correctly under normal conditions Security design issues are subtle, particularly w.r.t. DoS Constantly evolving threats: Stack-buffer overruns, Heap overruns, Format string overruns One byte overruns, Integer overflows © Micro ...
Windows Kernel Internals Overview
... Lots of legacy code now hooked to the internet Most code written to work correctly under normal conditions Security design issues are subtle, particularly w.r.t. DoS Constantly evolving threats: Stack-buffer overruns, Heap overruns, Format string overruns One byte overruns, Integer overflows © Micro ...
... Lots of legacy code now hooked to the internet Most code written to work correctly under normal conditions Security design issues are subtle, particularly w.r.t. DoS Constantly evolving threats: Stack-buffer overruns, Heap overruns, Format string overruns One byte overruns, Integer overflows © Micro ...
Operating System and Computer Security
... Microsoft must address stability problems in home computers – Windows XP was a small step Linux becomes more popular, but only for advanced users and in server market. Macintosh’s market penetration more based on hardware appeal rather than software ...
... Microsoft must address stability problems in home computers – Windows XP was a small step Linux becomes more popular, but only for advanced users and in server market. Macintosh’s market penetration more based on hardware appeal rather than software ...
Operating System and Computer Security
... Microsoft must address stability problems in home computers – Windows XP was a small step Linux becomes more popular, but only for advanced users and in server market. Macintosh’s market penetration more based on hardware appeal rather than software ...
... Microsoft must address stability problems in home computers – Windows XP was a small step Linux becomes more popular, but only for advanced users and in server market. Macintosh’s market penetration more based on hardware appeal rather than software ...
Basic Functions of the operating system
... What’s this called & what can you do to stop this? – UAC; lower the settings in the User Account in CP ...
... What’s this called & what can you do to stop this? – UAC; lower the settings in the User Account in CP ...
A+ Guide to Managing and Maintaining your PC, 6e
... – Revamped engine • Faster • Too security conscious for typical users. ...
... – Revamped engine • Faster • Too security conscious for typical users. ...
A+ Guide to Managing and Maintaining your PC, 6e
... – Revamped engine • Faster • Too security conscious for typical users. ...
... – Revamped engine • Faster • Too security conscious for typical users. ...
Windows, in computer science, personal computer operating system
... another GUI operating system. Windows version 2.0 included the overlapping window feature. The more powerful version 3.0 of Windows, introduced in 1990, and subsequent versions 3.1 and 3.11 rapidly made Windows the market leader in operating systems for personal computers, in part because it was ...
... another GUI operating system. Windows version 2.0 included the overlapping window feature. The more powerful version 3.0 of Windows, introduced in 1990, and subsequent versions 3.1 and 3.11 rapidly made Windows the market leader in operating systems for personal computers, in part because it was ...
Windows, in computer science, personal computer operating system
... another GUI operating system. Windows version 2.0 included the overlapping window feature. The more powerful version 3.0 of Windows, introduced in 1990, and subsequent versions 3.1 and 3.11 rapidly made Windows the market leader in operating systems for personal computers, in part because it was pre ...
... another GUI operating system. Windows version 2.0 included the overlapping window feature. The more powerful version 3.0 of Windows, introduced in 1990, and subsequent versions 3.1 and 3.11 rapidly made Windows the market leader in operating systems for personal computers, in part because it was pre ...
CS 550 - IIT Computer Science Department
... • separate user account creation specifically for running email attachments can isolate the account and so, no virus or a trojan can attack. ...
... • separate user account creation specifically for running email attachments can isolate the account and so, no virus or a trojan can attack. ...
Operating System
... information • UNIX: –Can be used on many computer system types and platforms • Red Hat Linux: –Can manage a cluster of up to eight servers • Mac OS X Server: ...
... information • UNIX: –Can be used on many computer system types and platforms • Red Hat Linux: –Can manage a cluster of up to eight servers • Mac OS X Server: ...
Export As PDF - Macrium KB
... While booting Windows – Driver not signed error You will see this if you are using 64bit Windows Vista or later and you have injected an unsigned driver. Reboot, hitting F8 to get the windows boot options menu. Chose the allow unsigned drivers option and Windows should complete booting. Locate signe ...
... While booting Windows – Driver not signed error You will see this if you are using 64bit Windows Vista or later and you have injected an unsigned driver. Reboot, hitting F8 to get the windows boot options menu. Chose the allow unsigned drivers option and Windows should complete booting. Locate signe ...
Operating System
... •JCL was used? • Identified as JCL or data. • What program needs to be run or what data file will be used. ...
... •JCL was used? • Identified as JCL or data. • What program needs to be run or what data file will be used. ...
CS101 Lecture - Sonoma State University
... • Open = No one owns the rights to making a computer with that operating system installed on the computer. • Closed = Someone dose own the rights to making a computer with that operating system on the computer. ...
... • Open = No one owns the rights to making a computer with that operating system installed on the computer. • Closed = Someone dose own the rights to making a computer with that operating system on the computer. ...
Slide 1
... • Blocks of code contained in the operating system • Coordinate the operating system with software applications – Similar toolbars and menus ...
... • Blocks of code contained in the operating system • Coordinate the operating system with software applications – Similar toolbars and menus ...