internetworking iv
... verify their connectivity. Ping tests will not give true data unless workstations are always left on. Again, this method of monitoring should be used only if there is no other method available. 11. Traffic monitoring is a much more sophisticated method of network monitoring. It looks at the actual p ...
... verify their connectivity. Ping tests will not give true data unless workstations are always left on. Again, this method of monitoring should be used only if there is no other method available. 11. Traffic monitoring is a much more sophisticated method of network monitoring. It looks at the actual p ...
Brochure
... electricity supply with the current infrastructure while keeping the costs low. As engineers contemplate options such as capacitor placement and Volt/VAR optimization to yield a more optimal outcome from the system’s assets, other solutions exist as a first step to reducing electricity cost while mi ...
... electricity supply with the current infrastructure while keeping the costs low. As engineers contemplate options such as capacitor placement and Volt/VAR optimization to yield a more optimal outcome from the system’s assets, other solutions exist as a first step to reducing electricity cost while mi ...
Slide 1
... don’t usually address the most pernicious attack vectors • Offense is generally easier and cheaper than defense, and is getting more so as networks become more complex • You can’t afford infinite resilience against all possible vulnerabilities and threats ...
... don’t usually address the most pernicious attack vectors • Offense is generally easier and cheaper than defense, and is getting more so as networks become more complex • You can’t afford infinite resilience against all possible vulnerabilities and threats ...
lesson2
... ‘netstat’ • It can show a lot of information about the current state of your host’s networking subsystem – such as routing-table entries, active connections, ports and protocols, or statistics for the active Network Interfaces • Example: $ netstat -i • It’s not a ‘privileged’ command – any user can ...
... ‘netstat’ • It can show a lot of information about the current state of your host’s networking subsystem – such as routing-table entries, active connections, ports and protocols, or statistics for the active Network Interfaces • Example: $ netstat -i • It’s not a ‘privileged’ command – any user can ...
Troubleshooting speed problems with SuccessWare
... computers. Remove all other network protocols (IPX/SPX, NETBUI) from client workstations, unless there is a server on the network that requires an alternate protocol, or you are running network software that requires one. If any of these alternate protocols must be used, remove its bindings to any M ...
... computers. Remove all other network protocols (IPX/SPX, NETBUI) from client workstations, unless there is a server on the network that requires an alternate protocol, or you are running network software that requires one. If any of these alternate protocols must be used, remove its bindings to any M ...
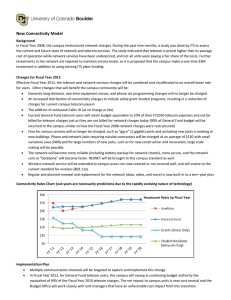
IT Executive Committee - New Connectivity Model
... In Fiscal Year 2008, the campus restructured network charges. During the past nine months, a study was done by ITS to assess the current and future state of network and telecom services. The study indicated that telecom is priced higher than its average cost of operation while network services have ...
... In Fiscal Year 2008, the campus restructured network charges. During the past nine months, a study was done by ITS to assess the current and future state of network and telecom services. The study indicated that telecom is priced higher than its average cost of operation while network services have ...
2014 HFPN Physician Incentive Structure www
... Cost of Care* (measured at the Network level) 30-Day Readmission rate (measured at the Network level) ED Visits/1,000 patients (measured at the Network level) Patient Satisfaction (measured by individual physician performance) Network Participation (measured by individual physician performance) ...
... Cost of Care* (measured at the Network level) 30-Day Readmission rate (measured at the Network level) ED Visits/1,000 patients (measured at the Network level) Patient Satisfaction (measured by individual physician performance) Network Participation (measured by individual physician performance) ...
LTEC4550_Assignment3_Whitaker
... •Exists at layers 4-7 on the OSI model •A device or program which allows for communications between devices which use different protocols •Can operate as part of a router, switch, or as a program on a computer •On a typical IP network, computers send packets destined for a different network to its d ...
... •Exists at layers 4-7 on the OSI model •A device or program which allows for communications between devices which use different protocols •Can operate as part of a router, switch, or as a program on a computer •On a typical IP network, computers send packets destined for a different network to its d ...
ppt - Terena
... • Operated by UNI•C • Development by UNI•C (and others) The Network for the educational sector – Sektornet • Governed by UNI•C • Basic Network infrastructure operated by TDC • Services operated by UNI•C • Development by UNI•C ...
... • Operated by UNI•C • Development by UNI•C (and others) The Network for the educational sector – Sektornet • Governed by UNI•C • Basic Network infrastructure operated by TDC • Services operated by UNI•C • Development by UNI•C ...
What is a VPN? A VPN (Virtual Private Network) is a private
... for your Wide Area Networking Needs What is a VPN? A VPN (Virtual Private Network) is a private connection between two machines that send private data traffic over a shared or public network, the Internet. This emerging technology lets organizations extend its network service over the Internet to br ...
... for your Wide Area Networking Needs What is a VPN? A VPN (Virtual Private Network) is a private connection between two machines that send private data traffic over a shared or public network, the Internet. This emerging technology lets organizations extend its network service over the Internet to br ...
Optimal Brain Surgeon
... Find the smallest Saliency If Saliency is much smaller than meansquare, delete that weight and repeat for next weight, other go to next step Update all weights ...
... Find the smallest Saliency If Saliency is much smaller than meansquare, delete that weight and repeat for next weight, other go to next step Update all weights ...
Network effect

In economics and business, a network effect (also called network externality or demand-side economies of scale) is the effect that one user of a good or service has on the value of that product to other people. When a network effect is present, the value of a product or service is dependent on the number of others using it.The classic example is the telephone. The more people who own telephones, the more valuable the telephone is to each owner. This creates a positive externality because a user may purchase a telephone without intending to create value for other users, but does so in any case. Online social networks work in the same way, with sites like Twitter and Facebook becoming more attractive as more users join.The expression ""network effect"" is applied most commonly to positive network externalities as in the case of the telephone. Negative network externalities can also occur, where more users make a product less valuable, but are more commonly referred to as ""congestion"" (as in traffic congestion or network congestion).Over time, positive network effects can create a bandwagon effect as the network becomes more valuable and more people join, in a positive feedback loop.