AXIS Camera setup and Troublshooting
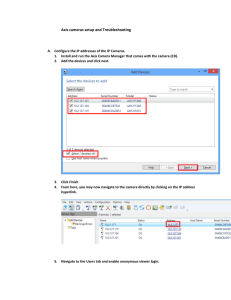
... Using a crossover network cable, connect the camera to your PC’s network card and power it up. Make sure that only one network connection is established - between PC and your Axis unit. (A crossover network cable is not need if a switch is used between Axis product and your PC or your PC supports Au ...
... Using a crossover network cable, connect the camera to your PC’s network card and power it up. Make sure that only one network connection is established - between PC and your Axis unit. (A crossover network cable is not need if a switch is used between Axis product and your PC or your PC supports Au ...
Network Interconnections - Policy and Technical Issues
... Proposed DG rating is less than the local applicant’s verifiable minimum load. Otherwise, the TDU may charge the DG applicant a fee to offset the costs of the interconnection study. The TDU must advise applicants requesting DG interconnection on secondary networks about the potential problems and ...
... Proposed DG rating is less than the local applicant’s verifiable minimum load. Otherwise, the TDU may charge the DG applicant a fee to offset the costs of the interconnection study. The TDU must advise applicants requesting DG interconnection on secondary networks about the potential problems and ...
Troubleshooting Wireless Network Connections Check the wires and wireless network adapter
... Most people, including myself, like placing it near the ceiling since most obstructions are nearer to the floor. It’s always a good idea to monitor the performance of your signal by using a diagnostic utility. This will help you to identify how strong your signal is in different locations and whethe ...
... Most people, including myself, like placing it near the ceiling since most obstructions are nearer to the floor. It’s always a good idea to monitor the performance of your signal by using a diagnostic utility. This will help you to identify how strong your signal is in different locations and whethe ...
Network accounting: An opportunity to control network-related expense through usage-based billing methodologies
... framework themselves. However, there are vendor-supplied solutions that provide usage-based accounting functionality. Depending upon site-specific requirements, usage-based billing systems may require some unique functionality. Typically, vendor-supplied products handle many requirements such as the ...
... framework themselves. However, there are vendor-supplied solutions that provide usage-based accounting functionality. Depending upon site-specific requirements, usage-based billing systems may require some unique functionality. Typically, vendor-supplied products handle many requirements such as the ...
What would Darwin Think about Clean-Slate
... in the literature, and practices such as partial deployment or backwards compatibility have been viewed as “necessary evils” for non-disruptive, evolutionary growth. This paper argues that there may be a much deeper correspondence between biological evolution and the evolution of a complex, large-sc ...
... in the literature, and practices such as partial deployment or backwards compatibility have been viewed as “necessary evils” for non-disruptive, evolutionary growth. This paper argues that there may be a much deeper correspondence between biological evolution and the evolution of a complex, large-sc ...
IF-CBDM Owner`s Manual
... Before using the unit, please take time to read this manual thoroughly to ensure you understand how to properly set up and connect the unit, as well as the operation of its many useful and convenient functions. After you have finished reading this manual, please keep it in a safe place for future re ...
... Before using the unit, please take time to read this manual thoroughly to ensure you understand how to properly set up and connect the unit, as well as the operation of its many useful and convenient functions. After you have finished reading this manual, please keep it in a safe place for future re ...
value for money model
... 'central case' value. This approach allows us to assess how much confidence we can have that the eventual outcome of the QCS Proposal will reflect the appraisal. Taking all three measures together, in over 90% of modelled simulations a positive benefit is obtained. ...
... 'central case' value. This approach allows us to assess how much confidence we can have that the eventual outcome of the QCS Proposal will reflect the appraisal. Taking all three measures together, in over 90% of modelled simulations a positive benefit is obtained. ...
PL-751 User Manual - PLANET Technology Corporation.
... The products and programs described in this User’s Manual are licensed products of PLANET Technology, This User’s Manual contains proprietary information protected by copyright, and this User’s Manual and all accompanying hardware, software, and documentation are copyrighted. No part of this User’s ...
... The products and programs described in this User’s Manual are licensed products of PLANET Technology, This User’s Manual contains proprietary information protected by copyright, and this User’s Manual and all accompanying hardware, software, and documentation are copyrighted. No part of this User’s ...
Lecture2-Part1
... Thus, a few P2P users are using most of the bandwidth ISPs would rather give good service to users other than to P2P users – If a transfer of a large file takes a bit longer, it does not impact the utility (the user does not really care) – If a short file transfer takes longer, it greatly impact uti ...
... Thus, a few P2P users are using most of the bandwidth ISPs would rather give good service to users other than to P2P users – If a transfer of a large file takes a bit longer, it does not impact the utility (the user does not really care) – If a short file transfer takes longer, it greatly impact uti ...
Document
... polarization currents at an aperture in a conducting wall (a) Normal electric field at a conducting wall. (b) Electric field lines around an aperture in a conducting wall. (c) Electric field lines around electric polarization currents normal to a conducting wall. (d) Magnetic field lines near a cond ...
... polarization currents at an aperture in a conducting wall (a) Normal electric field at a conducting wall. (b) Electric field lines around an aperture in a conducting wall. (c) Electric field lines around electric polarization currents normal to a conducting wall. (d) Magnetic field lines near a cond ...
USB 1.1 – A device interface to your PC that supports desktops and
... A networking standard using cables (Category 5) to create a network. Network Adapter - Also known as a NIC (Network Interface Card). Used to provide PC’s or laptops with an Ethernet port or wireless access to the network. Broadband Modem - A device that allows broadband connection to the internet. B ...
... A networking standard using cables (Category 5) to create a network. Network Adapter - Also known as a NIC (Network Interface Card). Used to provide PC’s or laptops with an Ethernet port or wireless access to the network. Broadband Modem - A device that allows broadband connection to the internet. B ...
Customers
... • Affected by quantity (large families more price sensitive) • Ex: Construction unions divide & conquer ...
... • Affected by quantity (large families more price sensitive) • Ex: Construction unions divide & conquer ...
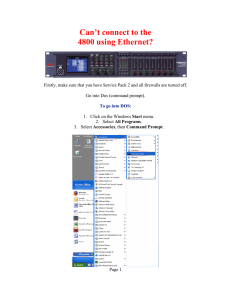
Can`t Connect to 4800
... 5. Turn the # 3 ENCODER until it reads “DHCP Disabled”. 6. Turn the # 1 ENCODER until the first section of the IP address is highlighted in blue. 7. You must change the IP address so that it matches your network address. For example: The network ID in the above Dos window is 10.0 because the subnet ...
... 5. Turn the # 3 ENCODER until it reads “DHCP Disabled”. 6. Turn the # 1 ENCODER until the first section of the IP address is highlighted in blue. 7. You must change the IP address so that it matches your network address. For example: The network ID in the above Dos window is 10.0 because the subnet ...
Troubleshooting Networks
... The netstat utility is used to identify which applications or network connections are consuming network resources. This utility allows you to see if anything is overly consuming network resources and, thereby, causing congestion on your network. Command: C:\netstat -a ...
... The netstat utility is used to identify which applications or network connections are consuming network resources. This utility allows you to see if anything is overly consuming network resources and, thereby, causing congestion on your network. Command: C:\netstat -a ...
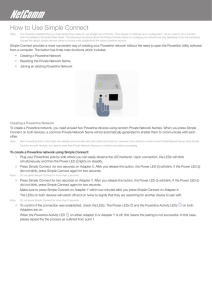
How to Use Simple Connect
... The Powerline Adapters that you have received are ready for use straight out of the box. They require no initial set-up or configuration - all you need to do is connect them as detailed in the Quick Start Guide. The following Instructions about the Simple Connect button to configure your network are ...
... The Powerline Adapters that you have received are ready for use straight out of the box. They require no initial set-up or configuration - all you need to do is connect them as detailed in the Quick Start Guide. The following Instructions about the Simple Connect button to configure your network are ...
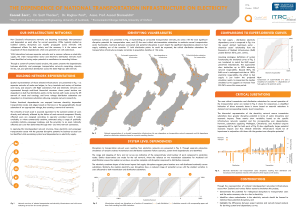
POSTER - Zorn_DependenceTrnsptInfstructureElect_QCAM_2016
... transportation nodes and edges based on the known or the geographically closest substation of an appropriate voltage, thus creating a network-of-networks. The criticality of each asset is assumed equivalent to the summed number of users directly and indirectly affected by the failure of each network ...
... transportation nodes and edges based on the known or the geographically closest substation of an appropriate voltage, thus creating a network-of-networks. The criticality of each asset is assumed equivalent to the summed number of users directly and indirectly affected by the failure of each network ...
Instructions for On-Campus Wireless Network Access
... If your Laptop does not have built-in wireless capabilities, confirm that your wireless card has been inserted into a PCI or PCMCIA (mini-PC) card slot, or your that your USB wireless adapter has been inserted into a USB port as detailed in the documentation provided from the associated manufacturer ...
... If your Laptop does not have built-in wireless capabilities, confirm that your wireless card has been inserted into a PCI or PCMCIA (mini-PC) card slot, or your that your USB wireless adapter has been inserted into a USB port as detailed in the documentation provided from the associated manufacturer ...
Technology Infrastructure Services T I
... The Technology Infrastructure LOB in the Department of Information Technology (DIT) is responsible for providing and maintaining the core, underlying technology infrastructure environment supporting all Fairfax County agencies and programs for IT (applications and data), and communications capabilit ...
... The Technology Infrastructure LOB in the Department of Information Technology (DIT) is responsible for providing and maintaining the core, underlying technology infrastructure environment supporting all Fairfax County agencies and programs for IT (applications and data), and communications capabilit ...
IP/Networking Commands
... Remember when typing from the command prompt you can only type one command per line, and press Enter after each one to execute it. C:\>arp –a: is short for address resolution protocol, It will show the IP address of your computer along with the IP address and MAC address of your router. C:\>hostname ...
... Remember when typing from the command prompt you can only type one command per line, and press Enter after each one to execute it. C:\>arp –a: is short for address resolution protocol, It will show the IP address of your computer along with the IP address and MAC address of your router. C:\>hostname ...
Chapter 12
... • A central troubleshooting group should also be responsible for contacting hardware, software vendors or common carriers. • To aid in network monitoring, managed devices are now being installed that record data on the messages they process and send this information back to a central management data ...
... • A central troubleshooting group should also be responsible for contacting hardware, software vendors or common carriers. • To aid in network monitoring, managed devices are now being installed that record data on the messages they process and send this information back to a central management data ...
Configuration Management
... • A central troubleshooting group should also be responsible for contacting hardware, software vendors or common carriers. • To aid in network monitoring, managed devices are now being installed that record data on the messages they process and send this information back to a central management data ...
... • A central troubleshooting group should also be responsible for contacting hardware, software vendors or common carriers. • To aid in network monitoring, managed devices are now being installed that record data on the messages they process and send this information back to a central management data ...
Research on Management Innovation of Traditional Chinese
... The network economy has a great influence on production, exchange, distribution, consumption mode in the condition of traditional economy. The economic operational mode social economic value standard and increment mode of traditional economy have been remodeled. The application of the network techno ...
... The network economy has a great influence on production, exchange, distribution, consumption mode in the condition of traditional economy. The economic operational mode social economic value standard and increment mode of traditional economy have been remodeled. The application of the network techno ...
Myths and Truths about Advertising
... Reach is the actual total number of target customers who come in contact with an advertising message. Cumulative Reach is the reach that is achieved over a period of time. Frequency is the average number of times each person who is reached is exposed to an advertisement during a given time ...
... Reach is the actual total number of target customers who come in contact with an advertising message. Cumulative Reach is the reach that is achieved over a period of time. Frequency is the average number of times each person who is reached is exposed to an advertisement during a given time ...
Network effect

In economics and business, a network effect (also called network externality or demand-side economies of scale) is the effect that one user of a good or service has on the value of that product to other people. When a network effect is present, the value of a product or service is dependent on the number of others using it.The classic example is the telephone. The more people who own telephones, the more valuable the telephone is to each owner. This creates a positive externality because a user may purchase a telephone without intending to create value for other users, but does so in any case. Online social networks work in the same way, with sites like Twitter and Facebook becoming more attractive as more users join.The expression ""network effect"" is applied most commonly to positive network externalities as in the case of the telephone. Negative network externalities can also occur, where more users make a product less valuable, but are more commonly referred to as ""congestion"" (as in traffic congestion or network congestion).Over time, positive network effects can create a bandwagon effect as the network becomes more valuable and more people join, in a positive feedback loop.