Operating Systems - Rutgers CS
... developed during this time. Users from remote locations communicated with the central computer via typewriter terminals. With systems such as SABRE: Although SABRE was a dedicated system and not a general purpose operating environment, it ushered in new requirements for computing. With systems such ...
... developed during this time. Users from remote locations communicated with the central computer via typewriter terminals. With systems such as SABRE: Although SABRE was a dedicated system and not a general purpose operating environment, it ushered in new requirements for computing. With systems such ...
2016 C++ PPT - Dr. Gang Xu
... Early computers could perform only one job or task at a time. This is often called single-user batch processing. The computer runs a single program at a time while processing data in groups or batches. Early operating systems smoothed and speeded up the transition between jobs, and hence increased t ...
... Early computers could perform only one job or task at a time. This is often called single-user batch processing. The computer runs a single program at a time while processing data in groups or batches. Early operating systems smoothed and speeded up the transition between jobs, and hence increased t ...
Goals of this lecture Let us assume … Human Brain – No Problem!
... // fill the arrays 'a' and 'b' on the CPU for (int i=0; i
... // fill the arrays 'a' and 'b' on the CPU for (int i=0; i
Software Computer Systems Standard Grade Computing Studies
... same time as a foreground interactive process. The foreground process is the one that accepts input from the keyboard, mouse, or other input device. Background processes cannot accept interactive input from a user, but they can access data stored on a disk and write data to the video display unit. F ...
... same time as a foreground interactive process. The foreground process is the one that accepts input from the keyboard, mouse, or other input device. Background processes cannot accept interactive input from a user, but they can access data stored on a disk and write data to the video display unit. F ...
LoadBalancing - Indico
... Bigger and better hardware (= increasing MTBF) Redundant architecture Load balancing + Failover ...
... Bigger and better hardware (= increasing MTBF) Redundant architecture Load balancing + Failover ...
MultiOS - Trinity College Dublin
... • no easy way to add another environment • assumes environments will not over-write others • only the current image is accessible ...
... • no easy way to add another environment • assumes environments will not over-write others • only the current image is accessible ...
The 5 generations of computers
... with an operating system, which allowed the device to run many different applications at one time with a central program that monitored the memory. Computers for the first time became accessible to a mass audience because they were smaller and cheaper than their predecessors. ...
... with an operating system, which allowed the device to run many different applications at one time with a central program that monitored the memory. Computers for the first time became accessible to a mass audience because they were smaller and cheaper than their predecessors. ...
Overview - Computing Science
... hardware components. You are in a computing science program, and computing science is not much about the development of hardware components. ...
... hardware components. You are in a computing science program, and computing science is not much about the development of hardware components. ...
Document
... Unix is a multitasking, multi-user operating system originally developed in 1969 by a group of AT&T employees at Bell Labs, including Ken Thompson, Dennis Ritchie, and Brian Kernighan. The Unix operating system was first developed in assembly language, but by 1973 had been almost entirely recoded in ...
... Unix is a multitasking, multi-user operating system originally developed in 1969 by a group of AT&T employees at Bell Labs, including Ken Thompson, Dennis Ritchie, and Brian Kernighan. The Unix operating system was first developed in assembly language, but by 1973 had been almost entirely recoded in ...
document
... • Current objective is to step toward this goal. • Terabit/second network will require many lambdas operating at minimum OC-768 and its architecture is not yet clear. R. Stevens / C. Catlett ...
... • Current objective is to step toward this goal. • Terabit/second network will require many lambdas operating at minimum OC-768 and its architecture is not yet clear. R. Stevens / C. Catlett ...
For CSIS-110 Students
... An introduction to the procedural design paradigm with an emphasis on problem solving, algorithm development, and implementation of algorithms in computer programs in a procedural language, such as Java, C, or C++. Other topics will include hardware organization, data representation, system software ...
... An introduction to the procedural design paradigm with an emphasis on problem solving, algorithm development, and implementation of algorithms in computer programs in a procedural language, such as Java, C, or C++. Other topics will include hardware organization, data representation, system software ...
www.ijecs.in International Journal Of Engineering And Computer Science ISSN:2319-7242
... gateway to some other networks which provides a powerful data processing, storage center, and an access point to the sensor nodes in its network. Sensor nodes sense their environment, collect sensed data and transmit it to the BS but their power, computational capacity and memory are limited due to ...
... gateway to some other networks which provides a powerful data processing, storage center, and an access point to the sensor nodes in its network. Sensor nodes sense their environment, collect sensed data and transmit it to the BS but their power, computational capacity and memory are limited due to ...
powerpoint 97 - Computer Science Division
... 2.5" ATA drives are limited to 2/4 disks per ATA bus How does a research project pick N? What’s natural? Is there sufficient processing power and memory to run the AME monitoring and testing tasks as well as the application requirements? – Isn't ISTORE-2 a good HW prototype for this model? Software ...
... 2.5" ATA drives are limited to 2/4 disks per ATA bus How does a research project pick N? What’s natural? Is there sufficient processing power and memory to run the AME monitoring and testing tasks as well as the application requirements? – Isn't ISTORE-2 a good HW prototype for this model? Software ...
Application Layer Multicast
... Self-Configuring source specific trees where data topology is comprised within the control topology. Centralized Directory Server (DS) maintains an updated records of the tree. New members query the DS for a list of potential parents and informs it in case they change their parent Each member incorp ...
... Self-Configuring source specific trees where data topology is comprised within the control topology. Centralized Directory Server (DS) maintains an updated records of the tree. New members query the DS for a list of potential parents and informs it in case they change their parent Each member incorp ...
lecture1
... Each pseudocode statement includes keywords that describe operations and some appropriate, English like descriptions of operand. Should be written on a separate line. If a statement requires more than one line, the continuation lines should be indented should begin with unambiguous word such as comp ...
... Each pseudocode statement includes keywords that describe operations and some appropriate, English like descriptions of operand. Should be written on a separate line. If a statement requires more than one line, the continuation lines should be indented should begin with unambiguous word such as comp ...
ClusterNetworks - Center for Computation & Technology
... inexpensive, too. Is usually a switched network, however, the link from the switch to the node is a collision ...
... inexpensive, too. Is usually a switched network, however, the link from the switch to the node is a collision ...
Microsoft Message Passing Interface
... MPI uses objects called communicators to control which collections of processes can communicate with each other. A communicator is a kind of “party line” of processes that can all receive messages from each other, but that ignore any messages within the communicator unless they are directed to them. ...
... MPI uses objects called communicators to control which collections of processes can communicate with each other. A communicator is a kind of “party line” of processes that can all receive messages from each other, but that ignore any messages within the communicator unless they are directed to them. ...
notes
... CSMA: listen before transmit: If channel sensed idle: transmit entire frame If channel sensed busy, defer transmission ...
... CSMA: listen before transmit: If channel sensed idle: transmit entire frame If channel sensed busy, defer transmission ...
A Distributive Polling Based Mobile Data Gathering in WSN
... environment, a pure static WSN could face the problems like covering the whole area of interest, holes in the coverage area. Some of the WSN architectures have been proposed based on Mobile Elements. There is large number of approaches to resolve the above problem. Clustering is a method used to ove ...
... environment, a pure static WSN could face the problems like covering the whole area of interest, holes in the coverage area. Some of the WSN architectures have been proposed based on Mobile Elements. There is large number of approaches to resolve the above problem. Clustering is a method used to ove ...
Paper Title (use style: paper title)
... on routing protocols in order to improve their quality and efficiency. But still it lacks in security due to their characteristics. So, a algorithm is proposed that uses public key cryptographic technique to protect the protocol from various attack. Hence, Cryptography provides more security and rel ...
... on routing protocols in order to improve their quality and efficiency. But still it lacks in security due to their characteristics. So, a algorithm is proposed that uses public key cryptographic technique to protect the protocol from various attack. Hence, Cryptography provides more security and rel ...
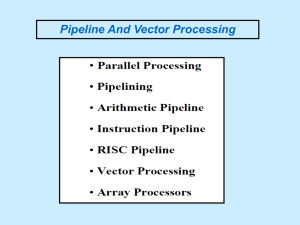
Slide 1
... Execution of Concurrent Events in the computing process to achieve faster Computational Speed The purpose of parallel processing is to speed up the computer processing capability and increase its throughput, that is, the amount of processing that can be accomplished during a given interval of time. ...
... Execution of Concurrent Events in the computing process to achieve faster Computational Speed The purpose of parallel processing is to speed up the computer processing capability and increase its throughput, that is, the amount of processing that can be accomplished during a given interval of time. ...
5 Generations of Computers
... a glass tube surrounding a vacuum (an area from which all gases have been removed). What makes it interesting is that when electrical contacts are put on the ends, you can get a current to flow though that vacuum. Thomas Edison noticed this first in 1883 ...
... a glass tube surrounding a vacuum (an area from which all gases have been removed). What makes it interesting is that when electrical contacts are put on the ends, you can get a current to flow though that vacuum. Thomas Edison noticed this first in 1883 ...
Software Architecture Design of Wireless Sensor Networks
... As shown in Figure 5, the architecture proposed contains an abstraction modeled as a Virtual Machine, similar to the architecture conceived in Section IV.A of this paper. The Virtual Machine provides the same service as in the first architecture – that of hardware independent program execution [3]. ...
... As shown in Figure 5, the architecture proposed contains an abstraction modeled as a Virtual Machine, similar to the architecture conceived in Section IV.A of this paper. The Virtual Machine provides the same service as in the first architecture – that of hardware independent program execution [3]. ...
history of computers
... • When was the first computing device invented? • Depends what is meant by “Computing Device” • Abacus • Napier’s Bones • Slide Rule ...
... • When was the first computing device invented? • Depends what is meant by “Computing Device” • Abacus • Napier’s Bones • Slide Rule ...
Computer cluster

A computer cluster consists of a set of loosely or tightly connected computers that work together so that, in many respects, they can be viewed as a single system. Unlike grid computers, computer clusters have each node set to perform the same task, controlled and scheduled by software.The components of a cluster are usually connected to each other through fast local area networks (""LAN""), with each node (computer used as a server) running its own instance of an operating system. In most circumstances, all of the nodes use the same hardware and the same operating system, although in some setups (i.e. using Open Source Cluster Application Resources (OSCAR)), different operating systems can be used on each computer, and/or different hardware.They are usually deployed to improve performance and availability over that of a single computer, while typically being much more cost-effective than single computers of comparable speed or availability.Computer clusters emerged as a result of convergence of a number of computing trends including the availability of low-cost microprocessors, high speed networks, and software for high-performance distributed computing. They have a wide range of applicability and deployment, ranging from small business clusters with a handful of nodes to some of the fastest supercomputers in the world such as IBM's Sequoia. The applications that can be done however, are nonetheless limited, since the software needs to be purpose-built per task. It is hence not possible to use computer clusters for casual computing tasks.