File - I Love such things which is available in the World.
... An operating system interacts with: All hardware installed in or connected to a computer system. All software installed or running from a storage device on a computer system File management is another important task of OS. It protects the information of computer system It involves in inter ...
... An operating system interacts with: All hardware installed in or connected to a computer system. All software installed or running from a storage device on a computer system File management is another important task of OS. It protects the information of computer system It involves in inter ...
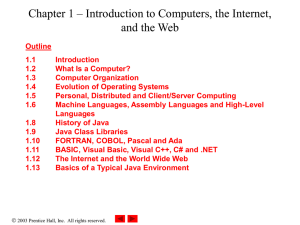
Chapter 1 – Introduction to Computers, the Internet, and the Web
... – Arithmetic and logic unit (ALU) • Performs calculations ...
... – Arithmetic and logic unit (ALU) • Performs calculations ...
PowerPoint Template
... typically used in traditional embedded clusters – Cache is helpful! Avoid flush/invalidate by software – Tradeoff between performance and embedded constraints ...
... typically used in traditional embedded clusters – Cache is helpful! Avoid flush/invalidate by software – Tradeoff between performance and embedded constraints ...
Step by step: How to install exchange 2003 cluster part...
... 17. It will configure DNS, DHCP and AD for you. easy huh? 18. System will reboot, it will take an awfully long time but that is typical for a DC. (when you reboot exchange server and DC at the same time, make sure DC boots up first and you can login to DC, and turn on exchange server. If not, exchan ...
... 17. It will configure DNS, DHCP and AD for you. easy huh? 18. System will reboot, it will take an awfully long time but that is typical for a DC. (when you reboot exchange server and DC at the same time, make sure DC boots up first and you can login to DC, and turn on exchange server. If not, exchan ...
Chapter I: - captainhermando.com
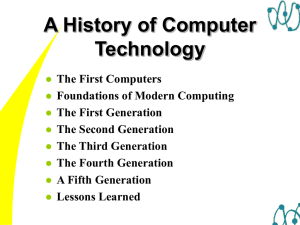
... Like the Mark I, built to calculate range tables for artillery shells. Completed at the University of Pennsylvania in 1946 by J. Presper Eckert and John Mauchly. Used 17,000 vacuum tubes which required special fans for cooling. ...
... Like the Mark I, built to calculate range tables for artillery shells. Completed at the University of Pennsylvania in 1946 by J. Presper Eckert and John Mauchly. Used 17,000 vacuum tubes which required special fans for cooling. ...
Software environment
... 1.5. ParaView. ParaView is a mature, understandable visualization application available as free software (full source code available and re-distributable) from paraview.org. When developing a numerical algorithm or a mathematical model, it can be useful to look at a graphical representation of solut ...
... 1.5. ParaView. ParaView is a mature, understandable visualization application available as free software (full source code available and re-distributable) from paraview.org. When developing a numerical algorithm or a mathematical model, it can be useful to look at a graphical representation of solut ...
.pdf
... to more traditional computing environments like clusters or super computers, the network characteristics between grid sites are both very heterogeneous and dynamically changing. Therefore, communication libraries need to take this heterogeneity into account to maintain efficiency in a world-wide env ...
... to more traditional computing environments like clusters or super computers, the network characteristics between grid sites are both very heterogeneous and dynamically changing. Therefore, communication libraries need to take this heterogeneity into account to maintain efficiency in a world-wide env ...
Com_Sys_Software
... What is meant by software Cont. The programs are written in special languages which interact with the computer’s processors and operating systems. ...
... What is meant by software Cont. The programs are written in special languages which interact with the computer’s processors and operating systems. ...
system software
... a computer's processor to perform specific operations. Computer software contrasts with computer hardware, which is the physical component of computers. Computer hardware and software require each other and neither can be realistically used without the other. Software provides instructions that tell ...
... a computer's processor to perform specific operations. Computer software contrasts with computer hardware, which is the physical component of computers. Computer hardware and software require each other and neither can be realistically used without the other. Software provides instructions that tell ...
I/O Multiplexing and select() - Computer Science & Engineering
... System to put your process to sleep when nothing is happening (no input). Once input arrives, the OS will wake up your process and read() (or whatever) will ...
... System to put your process to sleep when nothing is happening (no input). Once input arrives, the OS will wake up your process and read() (or whatever) will ...
Introduction to Unix (CA263) Computing With Unix
... – Computer programs are instructions written in a programming language that CPU understands. – Computer programs that perform word processing, financial analysis are called application software or just applications. – Programs designed to help people to use computers and applications are called syst ...
... – Computer programs are instructions written in a programming language that CPU understands. – Computer programs that perform word processing, financial analysis are called application software or just applications. – Programs designed to help people to use computers and applications are called syst ...
sensor data
... Sensor nodes should be self-organizing. Also the operation of the sensor networks is unattended, so the organization and configuration should be performed automatically Most application sensor nodes are stationary. However, in some applications nodes may allowed to change their location Sensor ...
... Sensor nodes should be self-organizing. Also the operation of the sensor networks is unattended, so the organization and configuration should be performed automatically Most application sensor nodes are stationary. However, in some applications nodes may allowed to change their location Sensor ...
architectural study of littoral zone sensing using
... Communication is said to be successful only if the message is received at the right recipient at the right time at the right format. This architecture [7] shown in Fig.5 focus on reliability and robustness. It aims to ensure that the data send must be received by any of the sink and then send to on- ...
... Communication is said to be successful only if the message is received at the right recipient at the right time at the right format. This architecture [7] shown in Fig.5 focus on reliability and robustness. It aims to ensure that the data send must be received by any of the sink and then send to on- ...
Unit 6 Operating Systems
... programs that allow the user to perform basic tasks like copying, moving, saving and printing files. It also provides an interface (i.e. provides ...
... programs that allow the user to perform basic tasks like copying, moving, saving and printing files. It also provides an interface (i.e. provides ...
Lecture 12
... * Portable/multi-platform, including Unix and Windows NT platforms * Available in C/C++ and Fortran implementations * Can be very easy and simple to use - provides for "incremental parallelism" https://computing.llnl.gov/tutorials/parallel_comp/ ...
... * Portable/multi-platform, including Unix and Windows NT platforms * Available in C/C++ and Fortran implementations * Can be very easy and simple to use - provides for "incremental parallelism" https://computing.llnl.gov/tutorials/parallel_comp/ ...
powerpoint 97
... • Diagnostic Processor Interface SW complete • PCB backplane: not yet designed • Finish 80 node system: Summer 2000 ...
... • Diagnostic Processor Interface SW complete • PCB backplane: not yet designed • Finish 80 node system: Summer 2000 ...
DNS Load Balancing and Failover Mechanism at
... delegation (see below) and the use of caching requests for the duration of a configured TTL are used to decrease the request rate to a DNS server. Name space segmentation is one of the reasons for the success of DNS. The ability to segment the name space is called delegation – the administrator has ...
... delegation (see below) and the use of caching requests for the duration of a configured TTL are used to decrease the request rate to a DNS server. Name space segmentation is one of the reasons for the success of DNS. The ability to segment the name space is called delegation – the administrator has ...
COMPUTATION
... • How parallel computations can be expressed in a highlevel language? – Simple extensions through an API (applicationprogramming interface) of common programming languages such as C/C++ or FORTRAN: ...
... • How parallel computations can be expressed in a highlevel language? – Simple extensions through an API (applicationprogramming interface) of common programming languages such as C/C++ or FORTRAN: ...
UNIT – II – Virtualization
... • Node 1 goes down, no heartbeat • The services are transferred and rendered from Node 2 • This is transparent and hence virtual to the client ...
... • Node 1 goes down, no heartbeat • The services are transferred and rendered from Node 2 • This is transparent and hence virtual to the client ...
CGS 3460 PROGRAMMING USING C
... – A program is the driving force behind any job that any computer does • A program is a list of detailed instructions • These instructions are written in certain programming language ...
... – A program is the driving force behind any job that any computer does • A program is a list of detailed instructions • These instructions are written in certain programming language ...
Computer cluster

A computer cluster consists of a set of loosely or tightly connected computers that work together so that, in many respects, they can be viewed as a single system. Unlike grid computers, computer clusters have each node set to perform the same task, controlled and scheduled by software.The components of a cluster are usually connected to each other through fast local area networks (""LAN""), with each node (computer used as a server) running its own instance of an operating system. In most circumstances, all of the nodes use the same hardware and the same operating system, although in some setups (i.e. using Open Source Cluster Application Resources (OSCAR)), different operating systems can be used on each computer, and/or different hardware.They are usually deployed to improve performance and availability over that of a single computer, while typically being much more cost-effective than single computers of comparable speed or availability.Computer clusters emerged as a result of convergence of a number of computing trends including the availability of low-cost microprocessors, high speed networks, and software for high-performance distributed computing. They have a wide range of applicability and deployment, ranging from small business clusters with a handful of nodes to some of the fastest supercomputers in the world such as IBM's Sequoia. The applications that can be done however, are nonetheless limited, since the software needs to be purpose-built per task. It is hence not possible to use computer clusters for casual computing tasks.