The History of Computers - City University of New York
... Zuse (Nazi Germany) – his machines were destroyed in WWII Atanasoff (Iowa State) – built a partially-working machine with his grad student Stibitz (Bell Labs) – built the MARK I computer that followed the designs of Babbage ...
... Zuse (Nazi Germany) – his machines were destroyed in WWII Atanasoff (Iowa State) – built a partially-working machine with his grad student Stibitz (Bell Labs) – built the MARK I computer that followed the designs of Babbage ...
Rain Technology - Teerthanker Mahaveer University
... Basically Rain technology has come up with the different network solutions over the internet such as nodes failure, traffic congestion, link failure, data lost. It is a cluster of nodes linked in a network topology with multiple interfaces and redundant storage. It is an implementation of RAID acros ...
... Basically Rain technology has come up with the different network solutions over the internet such as nodes failure, traffic congestion, link failure, data lost. It is a cluster of nodes linked in a network topology with multiple interfaces and redundant storage. It is an implementation of RAID acros ...
Servers
... – The drive letter mapping and partition information of a volume must be identical when viewed from both servers. This ensures that no matter which server is the active server, the volume can be accessed with the same drive letter. – NeoCLUSTER provides “volume locking” to ensure exclusive volume ac ...
... – The drive letter mapping and partition information of a volume must be identical when viewed from both servers. This ensures that no matter which server is the active server, the volume can be accessed with the same drive letter. – NeoCLUSTER provides “volume locking” to ensure exclusive volume ac ...
Software Computer Systems Standard Grade Computing Studies
... same time as a foreground interactive process. The foreground process is the one that accepts input from the keyboard, mouse, or other input device. Background processes cannot accept interactive input from a user, but they can access data stored on a disk and write data to the video display unit. F ...
... same time as a foreground interactive process. The foreground process is the one that accepts input from the keyboard, mouse, or other input device. Background processes cannot accept interactive input from a user, but they can access data stored on a disk and write data to the video display unit. F ...
Automatic Clustering of Grid Nodes
... landmarks. Each host has its own geometric coordinates based on distance from the landmarks, and the network distance between the hosts is modeled by Euclidean distance. Theilmann and Rothermel [13] propose dynamic distance maps of the Internet. They create a global view of the Internet from their m ...
... landmarks. Each host has its own geometric coordinates based on distance from the landmarks, and the network distance between the hosts is modeled by Euclidean distance. Theilmann and Rothermel [13] propose dynamic distance maps of the Internet. They create a global view of the Internet from their m ...
Overview of basics
... computer as a just a black box that executes programs by magic. All students of computing should acquire some understanding and appreciation of a computer system’s functional components, their characteristics, their performance, and their interactions. Students need to understand computer architectu ...
... computer as a just a black box that executes programs by magic. All students of computing should acquire some understanding and appreciation of a computer system’s functional components, their characteristics, their performance, and their interactions. Students need to understand computer architectu ...
BASF
... Collects processed data from B.A.S.F. through network and writes them to tapes or disk files In case of Monte Carlo event generation, event generator output is distributed to B.A.S.F. where detector simulation is running ...
... Collects processed data from B.A.S.F. through network and writes them to tapes or disk files In case of Monte Carlo event generation, event generator output is distributed to B.A.S.F. where detector simulation is running ...
Hard network lifetime wireless sensor networks with high energy first
... 2.1.HC-WSN CHS Algorithms without Energy Awareness: The cluster head selection processes for this type of clustering do not require sensors to be aware of any a priori energy information. However, without awareness of the energy information, cluster heads cannot be rotated, and traffic loads cannot ...
... 2.1.HC-WSN CHS Algorithms without Energy Awareness: The cluster head selection processes for this type of clustering do not require sensors to be aware of any a priori energy information. However, without awareness of the energy information, cluster heads cannot be rotated, and traffic loads cannot ...
For CSIS-010 Students
... gain a basic knowledge of computing, networking, databases, electronic information resources, and of the Internet that can be used to solve problems in a variety of contexts. Requirements for IS minor: CSIS-010, CSIS-110, CSIS-112 (Spring only), CSIS-114, CSIS-116 (Survey of Information Technology, ...
... gain a basic knowledge of computing, networking, databases, electronic information resources, and of the Internet that can be used to solve problems in a variety of contexts. Requirements for IS minor: CSIS-010, CSIS-110, CSIS-112 (Spring only), CSIS-114, CSIS-116 (Survey of Information Technology, ...
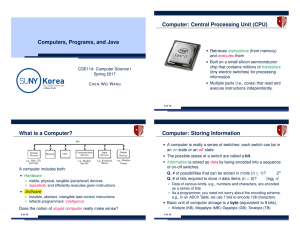
Computers, Programs, and Java What is a Computer? Computer
... Data of various kinds, e.g., numbers and characters, are encoded as a series of bits. As a programmer, you need not worry about the encoding scheme. e.g., In an ASCII Table, we use 7 bits to encode 128 characters. ...
... Data of various kinds, e.g., numbers and characters, are encoded as a series of bits. As a programmer, you need not worry about the encoding scheme. e.g., In an ASCII Table, we use 7 bits to encode 128 characters. ...
A Classification and Comparison of Data Mining Algorithms for
... Training Algorithm in a Wireless Sensor Network of the Type CluSE Generating Clusters in a static, energy aware, clustering apporach The clusterhead (CH) generates a prediction-model inside a prediction model unit. While next time unit do The CH sends a prediction-model to all the sensors in the cl ...
... Training Algorithm in a Wireless Sensor Network of the Type CluSE Generating Clusters in a static, energy aware, clustering apporach The clusterhead (CH) generates a prediction-model inside a prediction model unit. While next time unit do The CH sends a prediction-model to all the sensors in the cl ...
Part 4b: DataMining in WSNs - Algorithams and Architectures
... Training Algorithm in a Wireless Sensor Network of the Type CluSE Generating Clusters in a static, energy aware, clustering apporach The clusterhead (CH) generates a prediction-model inside a prediction model unit. While next time unit do The CH sends a prediction-model to all the sensors in the cl ...
... Training Algorithm in a Wireless Sensor Network of the Type CluSE Generating Clusters in a static, energy aware, clustering apporach The clusterhead (CH) generates a prediction-model inside a prediction model unit. While next time unit do The CH sends a prediction-model to all the sensors in the cl ...
Improving Ad Hoc Network Behaviour Using Clustering Technique with NS2 I
... A mobile ad hoc network (MANET) consists of a number of mobile nodes that jointly function as a router. A MANET can be created dynamically without any infrastructure. In this network type, the use of the clustering technique significantly reduces the routing traffic that occurs during the routing pr ...
... A mobile ad hoc network (MANET) consists of a number of mobile nodes that jointly function as a router. A MANET can be created dynamically without any infrastructure. In this network type, the use of the clustering technique significantly reduces the routing traffic that occurs during the routing pr ...
Chapter 1 - Powerpoint
... ✓ Modern computers consist of two primary components: hardware and software. Computer hardware is the physical component of the system. Computer software consists of programs that enable us to use the hardware. ✓ All information used by a computer is represented in binary form. This information incl ...
... ✓ Modern computers consist of two primary components: hardware and software. Computer hardware is the physical component of the system. Computer software consists of programs that enable us to use the hardware. ✓ All information used by a computer is represented in binary form. This information incl ...
4. Software - Ghulam Hassan
... Minicomputers were built based on integrated circuits (ICs), so-called "chips". This technology of constructing logical gates was invented independently by both Jack Kilby and Robert Noyce in late 1950s. They imprinted circuit networks on isolating material and used semiconductor material - such as ...
... Minicomputers were built based on integrated circuits (ICs), so-called "chips". This technology of constructing logical gates was invented independently by both Jack Kilby and Robert Noyce in late 1950s. They imprinted circuit networks on isolating material and used semiconductor material - such as ...
Lecture-1
... Computer Languages High Level languages language with strong abstraction from the details of the computer may use natural language elements Easier to use making the process of developing a program simpler and more understandable programs written in a high-level language must be translated ...
... Computer Languages High Level languages language with strong abstraction from the details of the computer may use natural language elements Easier to use making the process of developing a program simpler and more understandable programs written in a high-level language must be translated ...
ppt
... – Packet in reverse direction do not pass through load balancer – Greater scalability, particularly for traffic with assymmetric bandwidth (e.g., HTTP GETs) ...
... – Packet in reverse direction do not pass through load balancer – Greater scalability, particularly for traffic with assymmetric bandwidth (e.g., HTTP GETs) ...
ISTORE-1 - Computer Science Division
... – Single physical form factor, fixed cooling required, compatible network interface to simplify physical maintenance, scaling over time – Contents should evolve over time: contains most cost effective MPU, DRAM, disk, compatible NI – If useful, could have special bricks (e.g., DRAM rich) – Suggests ...
... – Single physical form factor, fixed cooling required, compatible network interface to simplify physical maintenance, scaling over time – Contents should evolve over time: contains most cost effective MPU, DRAM, disk, compatible NI – If useful, could have special bricks (e.g., DRAM rich) – Suggests ...
Introduction to Computer Organization, Operating Systems
... organization, operating systems and computer networks for programmers. Topics include: computer organization, data representation, the Windows/UNIX/LINUX operating system; and computer networks. Lecture 2 hours, laboratory 3 hours. Graded ABC/NC b) Prerequisites or co-requisites: CS 202 c) Required/ ...
... organization, operating systems and computer networks for programmers. Topics include: computer organization, data representation, the Windows/UNIX/LINUX operating system; and computer networks. Lecture 2 hours, laboratory 3 hours. Graded ABC/NC b) Prerequisites or co-requisites: CS 202 c) Required/ ...
effects_of_virus_by_Dima_1
... loaded onto a computer every time one starts up, and in time, they can spread to other readable disks. Booting problems and start up problems, problems with retrieving data, computer performance instability and the inability to locate hard drives are all issues that may arise due to an infection. 4. ...
... loaded onto a computer every time one starts up, and in time, they can spread to other readable disks. Booting problems and start up problems, problems with retrieving data, computer performance instability and the inability to locate hard drives are all issues that may arise due to an infection. 4. ...
(.ppt)
... Supports malleability and fault-tolerance Supports data-sharing between different branches through Shared Objects cpu 2 ...
... Supports malleability and fault-tolerance Supports data-sharing between different branches through Shared Objects cpu 2 ...
HP Education Services This course teaches system administrators how to
... herein is subject to change without notice. The only warranties for HP products and services are set forth in the express warranty statements accompanying such products and services. Nothing herein should be construed as constituting an additional warranty. HP shall not be liable for technical or ed ...
... herein is subject to change without notice. The only warranties for HP products and services are set forth in the express warranty statements accompanying such products and services. Nothing herein should be construed as constituting an additional warranty. HP shall not be liable for technical or ed ...
ICS 1.1 Computer History
... Ritchie developed C for the new Unix system being created at the same time. C is very commonly used to program operating systems such as Unix, Windows, the MacOS, and Linux. ...
... Ritchie developed C for the new Unix system being created at the same time. C is very commonly used to program operating systems such as Unix, Windows, the MacOS, and Linux. ...
paper - IJANA International Journal of Advanced Networking And
... to remove delays at both the MAC and routing layers, but this approach does not work against all types of rushing attackers and is not general [5]. For example, in a dense network using a CSMA MAC layer, if a node A initiates a Route Discovery, and B is two hops away from A, and C and D are neighbor ...
... to remove delays at both the MAC and routing layers, but this approach does not work against all types of rushing attackers and is not general [5]. For example, in a dense network using a CSMA MAC layer, if a node A initiates a Route Discovery, and B is two hops away from A, and C and D are neighbor ...
Computer cluster

A computer cluster consists of a set of loosely or tightly connected computers that work together so that, in many respects, they can be viewed as a single system. Unlike grid computers, computer clusters have each node set to perform the same task, controlled and scheduled by software.The components of a cluster are usually connected to each other through fast local area networks (""LAN""), with each node (computer used as a server) running its own instance of an operating system. In most circumstances, all of the nodes use the same hardware and the same operating system, although in some setups (i.e. using Open Source Cluster Application Resources (OSCAR)), different operating systems can be used on each computer, and/or different hardware.They are usually deployed to improve performance and availability over that of a single computer, while typically being much more cost-effective than single computers of comparable speed or availability.Computer clusters emerged as a result of convergence of a number of computing trends including the availability of low-cost microprocessors, high speed networks, and software for high-performance distributed computing. They have a wide range of applicability and deployment, ranging from small business clusters with a handful of nodes to some of the fastest supercomputers in the world such as IBM's Sequoia. The applications that can be done however, are nonetheless limited, since the software needs to be purpose-built per task. It is hence not possible to use computer clusters for casual computing tasks.