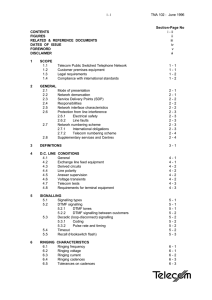
i - i TNA 102
... (1) As far as is practicable, the Telecom PSTN is compliant with ITU-T (formerly CCITT) Recommendations. Reference is made as appropriate to specific Recommendations throughout this Specification. For convenience, such references indicate the Recommendation current at the date of issue, e.g. 'CCITT ...
... (1) As far as is practicable, the Telecom PSTN is compliant with ITU-T (formerly CCITT) Recommendations. Reference is made as appropriate to specific Recommendations throughout this Specification. For convenience, such references indicate the Recommendation current at the date of issue, e.g. 'CCITT ...
Network Deployment Guide for NovoPRO
... A. Follow the above configuration steps to connect to the organization’s WiFi network; B. After the WiFi is connected, click on button “Browser” on the home screen (see the ...
... A. Follow the above configuration steps to connect to the organization’s WiFi network; B. After the WiFi is connected, click on button “Browser” on the home screen (see the ...
slides - Fei Hu
... Vendor certification—typically one week Lab testing by operator Staged deployment on less critical systems first Avoid interrupting any critical process phases ...
... Vendor certification—typically one week Lab testing by operator Staged deployment on less critical systems first Avoid interrupting any critical process phases ...
Document
... Vendor certification—typically one week Lab testing by operator Staged deployment on less critical systems first Avoid interrupting any critical process phases ...
... Vendor certification—typically one week Lab testing by operator Staged deployment on less critical systems first Avoid interrupting any critical process phases ...
TNS07%20PPP
... With a serial connection (串列連線) , information is sent across one wire, one data bit at a time. In reality, it is often the case that serial links can be clocked considerably faster than parallel links, and they achieve a higher data rate. ...
... With a serial connection (串列連線) , information is sent across one wire, one data bit at a time. In reality, it is often the case that serial links can be clocked considerably faster than parallel links, and they achieve a higher data rate. ...
Emergence of communication networks in organizations:
... term as “reorganizing.” Acknowledging Monge and Eisenberg (1987), Brass (1995) underscored the substantively compelling argument to articulate the dynamic nature of the inter-relationships among networks, their antecedents and outcomes. Echoing these concerns, in a special issue of the Journal of Ma ...
... term as “reorganizing.” Acknowledging Monge and Eisenberg (1987), Brass (1995) underscored the substantively compelling argument to articulate the dynamic nature of the inter-relationships among networks, their antecedents and outcomes. Echoing these concerns, in a special issue of the Journal of Ma ...
nmea protocol - Stefano Trivellini
... 6) GPS Quality Indicator, 0 - fix not available, 1 - GPS fix, 2 - Differential GPS fix 7) Number of satellites in view, 00 - 12 8) Horizontal Dilution of precision 9) Antenna Altitude above/below mean-sea-level (geoid) 10) Units of antenna altitude, meters 11) Geoidal separation, the difference betw ...
... 6) GPS Quality Indicator, 0 - fix not available, 1 - GPS fix, 2 - Differential GPS fix 7) Number of satellites in view, 00 - 12 8) Horizontal Dilution of precision 9) Antenna Altitude above/below mean-sea-level (geoid) 10) Units of antenna altitude, meters 11) Geoidal separation, the difference betw ...
What is an L3 Master Device?
... The L3 Master Device (l3mdev) concept was introduced to the Linux networking stack in v4.4. While it was created for the VRF implementation, it is a separate API that can be leveraged by other drivers that want to influence FIB lookups or want to manipulate packets at layer 3. This paper discusses t ...
... The L3 Master Device (l3mdev) concept was introduced to the Linux networking stack in v4.4. While it was created for the VRF implementation, it is a separate API that can be leveraged by other drivers that want to influence FIB lookups or want to manipulate packets at layer 3. This paper discusses t ...
William Stallings Data and Computer Communications
... Addressing level Level in architecture at which entity is named Unique address for each end system (computer) and router Network level address IP or internet address (TCP/IP) Network service access point or NSAP (OSI) ...
... Addressing level Level in architecture at which entity is named Unique address for each end system (computer) and router Network level address IP or internet address (TCP/IP) Network service access point or NSAP (OSI) ...
Translation
... • I. Read the following statements carefully, and decide whether they are true (T) or false (F) according to the text. – ___1.This concept of location based systems follows the standardized concept of real-time locating systems and related local services. – ___2.LBS was originally developed by mobil ...
... • I. Read the following statements carefully, and decide whether they are true (T) or false (F) according to the text. – ___1.This concept of location based systems follows the standardized concept of real-time locating systems and related local services. – ___2.LBS was originally developed by mobil ...
PPT Version
... to perform an ENUM query to complete a telephone call to an E.164 number. – A party making an ENUM query, whether a calling user or service provider, is not obligated to use any of the services in the NAPTR records returned. – All E.164 numbers must have a Public Switched Telephone Network (PSTN) po ...
... to perform an ENUM query to complete a telephone call to an E.164 number. – A party making an ENUM query, whether a calling user or service provider, is not obligated to use any of the services in the NAPTR records returned. – All E.164 numbers must have a Public Switched Telephone Network (PSTN) po ...
Slides
... A: ASN.1 is an encoding standard. It defines how you encode data for different types: how to send an integer, a string, a bit string, an object-id, a real number, a null, etc. It also tries to minimize the space it takes to encode things. As a result, it is barf-making. A truly evil thing. (As a res ...
... A: ASN.1 is an encoding standard. It defines how you encode data for different types: how to send an integer, a string, a bit string, an object-id, a real number, a null, etc. It also tries to minimize the space it takes to encode things. As a result, it is barf-making. A truly evil thing. (As a res ...
Sample – Firewall PowerPoint
... • How do you enforce your standards? • Planning for response if you are attacked ...
... • How do you enforce your standards? • Planning for response if you are attacked ...
2 Network topology
... The shape of the cabling layout used to link devices is called the physical topology of the network. This refers to the layout of cabling, the locations of nodes, and the interconnections between the nodes and the cabling. The physical topology of a network is determined by the capabilities of the n ...
... The shape of the cabling layout used to link devices is called the physical topology of the network. This refers to the layout of cabling, the locations of nodes, and the interconnections between the nodes and the cabling. The physical topology of a network is determined by the capabilities of the n ...
1 - City of San Carlos
... community’s input early on in our evaluation proved to be extremely useful. Equally important is an organization’s ability to manage and maintain its telecommunications resources in-house. This generally allows for significant costs savings over outside vendorsupported services. The present City tel ...
... community’s input early on in our evaluation proved to be extremely useful. Equally important is an organization’s ability to manage and maintain its telecommunications resources in-house. This generally allows for significant costs savings over outside vendorsupported services. The present City tel ...
ppt - Courses
... number of distinguishable networks are connected together using packet communications processors called gateways which implement a store and forward packet forwarding algorithm” John Chuang IS250 UC Berkeley ...
... number of distinguishable networks are connected together using packet communications processors called gateways which implement a store and forward packet forwarding algorithm” John Chuang IS250 UC Berkeley ...
Related paper.
... INVITATION. Instead of directly reaching an intended callee, a SIP request may trigger a chain of new SIP requests by proxies. Users can register their location(s) with SIP servers. In this paper, we consider only peer-to-peer communications without any SIP server. ...
... INVITATION. Instead of directly reaching an intended callee, a SIP request may trigger a chain of new SIP requests by proxies. Users can register their location(s) with SIP servers. In this paper, we consider only peer-to-peer communications without any SIP server. ...
appendix a: wlan-related terminology - University of Houston
... For the past couple of years, increasing number of wireless local area networks (WLANs), based on the IEEE 802.11 protocols, have been deployed in various types of locations, including homes, schools, airports, business offices, government buildings, military facilities, coffee shops, book stores, a ...
... For the past couple of years, increasing number of wireless local area networks (WLANs), based on the IEEE 802.11 protocols, have been deployed in various types of locations, including homes, schools, airports, business offices, government buildings, military facilities, coffee shops, book stores, a ...
CREATING A PROMOTIONAL MESSAGE: EXPLORING THE ROLE
... the coding system. For instance, pointing a finger towards something, or approaching someone are examples of non-verbal behaviour in its essence. Using iconic coding system some aspects of the person that codes the message is kept. It can be said that the similarity between the code and the person i ...
... the coding system. For instance, pointing a finger towards something, or approaching someone are examples of non-verbal behaviour in its essence. Using iconic coding system some aspects of the person that codes the message is kept. It can be said that the similarity between the code and the person i ...
General Specifications FieldMate
... FieldMate is used for the field device setting and adjustment, which must be connected for all activities. Moreover off line database function for up to 500 devices which maintains a complete record for all device configuration and maintenance activities. FieldMate is a PC based configuration tool t ...
... FieldMate is used for the field device setting and adjustment, which must be connected for all activities. Moreover off line database function for up to 500 devices which maintains a complete record for all device configuration and maintenance activities. FieldMate is a PC based configuration tool t ...
RS-232 Communications
... RS-232 hardware samples the line multiple times during a single bit transmission. If the samples do not all have the same voltage, a framing error occurs. A framing error should only occur if one device is sending faster than the other device is set to receive. An intentional frame error can be caus ...
... RS-232 hardware samples the line multiple times during a single bit transmission. If the samples do not all have the same voltage, a framing error occurs. A framing error should only occur if one device is sending faster than the other device is set to receive. An intentional frame error can be caus ...
1.Physical Layer & Data Link Layer
... Multiple Cisco networking products allow remote attackers to cause a denial of service on the local network via a series of ARP packets sent to the router's interface that contains a different MAC address for the router, which eventually causes the router to overwrite the MAC address in its ARP tabl ...
... Multiple Cisco networking products allow remote attackers to cause a denial of service on the local network via a series of ARP packets sent to the router's interface that contains a different MAC address for the router, which eventually causes the router to overwrite the MAC address in its ARP tabl ...
Communication without Agents? From Agent-Oriented to
... sage sending paradigm. Second, and maybe less obvious, there is a tendency for the sender of a message to disappear in large-scale communication processes. Life and death of communications in a Usenet discussion group are largely independent from life and death of the individual agents participating ...
... sage sending paradigm. Second, and maybe less obvious, there is a tendency for the sender of a message to disappear in large-scale communication processes. Life and death of communications in a Usenet discussion group are largely independent from life and death of the individual agents participating ...
internet2 network
... • Develop a hybrid network capable of providing pointto-point services together with an IP network • Every connector (RON) connects to the backbone across a metro location not requiring extensive backhaul • The community retains complete control of the layer 1 optical system including provisioning a ...
... • Develop a hybrid network capable of providing pointto-point services together with an IP network • Every connector (RON) connects to the backbone across a metro location not requiring extensive backhaul • The community retains complete control of the layer 1 optical system including provisioning a ...
Document
... A network protocol used on Internet or LAN connections Developed in 1969 beginning with RFC 15 Standardized as IETF STD 8 ...
... A network protocol used on Internet or LAN connections Developed in 1969 beginning with RFC 15 Standardized as IETF STD 8 ...