here
... Compared with building a LAN, the new challenges are that (a) the network is now much larger; (b) long-distance circuits are needed; (c) there are possibly multiple routes from one host to another host When the network is much larger, using MAC address based forwarding tables will make the network s ...
... Compared with building a LAN, the new challenges are that (a) the network is now much larger; (b) long-distance circuits are needed; (c) there are possibly multiple routes from one host to another host When the network is much larger, using MAC address based forwarding tables will make the network s ...
section 16290 - Siemens Industry
... Power supply: The device shall accept power from 85-240 VAC (+/-10%), 47 to 63 Hz or 110-330 VDC (+/-10%) without external converters or separate ordering options. Maximum burden shall be 20 VA. Ride-through shall be a minimum of 100ms (6 cycles @ 60Hz) for 96 VAC, or 200ms (12 cycles @ 60 Hz) for 1 ...
... Power supply: The device shall accept power from 85-240 VAC (+/-10%), 47 to 63 Hz or 110-330 VDC (+/-10%) without external converters or separate ordering options. Maximum burden shall be 20 VA. Ride-through shall be a minimum of 100ms (6 cycles @ 60Hz) for 96 VAC, or 200ms (12 cycles @ 60 Hz) for 1 ...
Communication principles
... Our employees are the most important communicators. That is why messages must be created with relevant employees and distributed internally before they are communicated to the public. These are the basic, corporate principles. (In region X external communication focuses on…)* Internal communication ...
... Our employees are the most important communicators. That is why messages must be created with relevant employees and distributed internally before they are communicated to the public. These are the basic, corporate principles. (In region X external communication focuses on…)* Internal communication ...
section 16290
... Power supply: The device shall accept power from 85-240 VAC (+/-10%), 47 to 63 Hz or 110-330 VDC (+/-10%) without external converters or separate ordering options. Maximum burden shall be 20 VA. Ride-through shall be a minimum of 100ms (6 cycles @ 60Hz) for 96 VAC, or 200ms (12 cycles @ 60 Hz) for 1 ...
... Power supply: The device shall accept power from 85-240 VAC (+/-10%), 47 to 63 Hz or 110-330 VDC (+/-10%) without external converters or separate ordering options. Maximum burden shall be 20 VA. Ride-through shall be a minimum of 100ms (6 cycles @ 60Hz) for 96 VAC, or 200ms (12 cycles @ 60 Hz) for 1 ...
doc - Andrew.cmu.edu
... 11. Suppose a hacker obtains control of all the BGP-speaking routers in several different Autonomous Systems (ASes). Our hacker has each AS “hijack” several IP blocks. That is, each AS under his or her control announces via BGP that it owns IP blocks for which it does not. For example, our hacker ha ...
... 11. Suppose a hacker obtains control of all the BGP-speaking routers in several different Autonomous Systems (ASes). Our hacker has each AS “hijack” several IP blocks. That is, each AS under his or her control announces via BGP that it owns IP blocks for which it does not. For example, our hacker ha ...
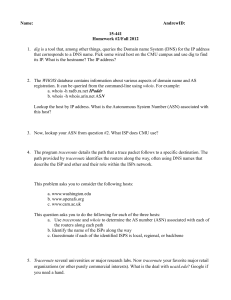
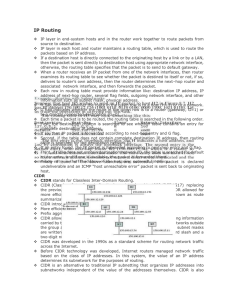
IP Routing
... know the MAC address of H3. H1 first broadcast an ARP request packet asking the destination host, which is identified by H3’s IP address, to reply. All hosts in the network receive the packet, but only the intended host, which is H3, responds to H1. The ARP response packet contains H3’s MAC address ...
... know the MAC address of H3. H1 first broadcast an ARP request packet asking the destination host, which is identified by H3’s IP address, to reply. All hosts in the network receive the packet, but only the intended host, which is H3, responds to H1. The ARP response packet contains H3’s MAC address ...
Understanding Sociograms
... Sociograms, or maps, are graphic pictures, or images, of a kind of relationship. Sociograms are illustrations of a relationship at a point in time. Each shape (node) indicates an individual, group, organization, nation, etc. Each line indicates a connection. The connections can have strength (color ...
... Sociograms, or maps, are graphic pictures, or images, of a kind of relationship. Sociograms are illustrations of a relationship at a point in time. Each shape (node) indicates an individual, group, organization, nation, etc. Each line indicates a connection. The connections can have strength (color ...
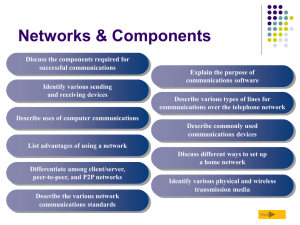
Network types
... is connected to boot through the network system via an authentication password process. Once logged into the network, this computer is capable of accessing data or services held on the network servers, based on either the machine’s access or the user’s access level. ...
... is connected to boot through the network system via an authentication password process. Once logged into the network, this computer is capable of accessing data or services held on the network servers, based on either the machine’s access or the user’s access level. ...
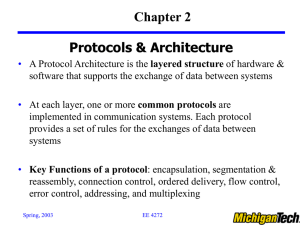
William Stallings Data and Computer Communications
... Network packets may be smaller Splitting larger blocks into smaller ones is segmentation (or fragmentation in TCP/IP) ...
... Network packets may be smaller Splitting larger blocks into smaller ones is segmentation (or fragmentation in TCP/IP) ...
File - Learning@NDGTA
... • Layer 4: defines the protocols responsible for sending messages from one end of the network to the other. It controls message flow • Layer 5: provides the function to set up communication between users at separate locations • Layer 6: ensures that the information is delivered in an understandable ...
... • Layer 4: defines the protocols responsible for sending messages from one end of the network to the other. It controls message flow • Layer 5: provides the function to set up communication between users at separate locations • Layer 6: ensures that the information is delivered in an understandable ...
presentation source - CECS Multimedia Communications
... With quality of today’s data transmission networks (e.g., fiber optics networks), bit errors are rare Bit errors occur due to noise in lines or packet switches Error detection codes in most packet switches detect presence of a bit error in the packet and can request retransmission of ...
... With quality of today’s data transmission networks (e.g., fiber optics networks), bit errors are rare Bit errors occur due to noise in lines or packet switches Error detection codes in most packet switches detect presence of a bit error in the packet and can request retransmission of ...
Control System Specification
... used in the installation of network control products to provide the functions necessary for control ...
... used in the installation of network control products to provide the functions necessary for control ...
Networks of Meaning: Communication Trajectories in Social
... new forms of communication. In addition to scientific papers, there are also but also patents, models, technical reports for consultancy, elementary texts books, magazine articles, teaching materials, performances in the field of arts and humanities, musical scores from ethnological research in anci ...
... new forms of communication. In addition to scientific papers, there are also but also patents, models, technical reports for consultancy, elementary texts books, magazine articles, teaching materials, performances in the field of arts and humanities, musical scores from ethnological research in anci ...
Simple and Affordable AAC Options
... General > Accessibility > Guided Access. Slide the option to the “on” position” then create a pass code. Next, open the app you want to lock into and triple-click the home button. Now, with your finger, circle any areas on the screen you'd like block access to. A transparent box will appear and you ...
... General > Accessibility > Guided Access. Slide the option to the “on” position” then create a pass code. Next, open the app you want to lock into and triple-click the home button. Now, with your finger, circle any areas on the screen you'd like block access to. A transparent box will appear and you ...
Wireless Communications
... duration of the connection. Ordinary voice phone service is circuit-switched. The phone company reserves a specific physical path to the number being called for the duration of the call. During that time, no one else can use the physical lines involved. ...
... duration of the connection. Ordinary voice phone service is circuit-switched. The phone company reserves a specific physical path to the number being called for the duration of the call. During that time, no one else can use the physical lines involved. ...
802.11ag The - Silex Technology
... expectations for consumer electronics are much higher. Consumer electronics must work flawlessly when the power switch is pressed-no excuses. 802.11a can deliver the necessary performance with plenty of bandwidth and clear paths for glitch-free multimedia service. Recognizing this capability, consum ...
... expectations for consumer electronics are much higher. Consumer electronics must work flawlessly when the power switch is pressed-no excuses. 802.11a can deliver the necessary performance with plenty of bandwidth and clear paths for glitch-free multimedia service. Recognizing this capability, consum ...
When Failure is NOT an Option
... What is redundancy and why is it important? Today, serial devices still play a major role in many applications worldwide to collect or report process data. No matter the industry, from Power/Utility, Water Wastewater or Treatment, Oil/Gas or Mining, Transportation, Factory or Process Control Automat ...
... What is redundancy and why is it important? Today, serial devices still play a major role in many applications worldwide to collect or report process data. No matter the industry, from Power/Utility, Water Wastewater or Treatment, Oil/Gas or Mining, Transportation, Factory or Process Control Automat ...
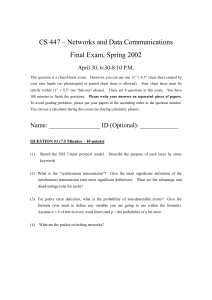
CS447_Spring2002_Rea..
... Assume the following rules: 1. Whichever host that has "a token" can transmit data (data as a packet). 2. If a host finishes transmitting a packet, the host has to wait for the transmitted packet to come back on the ring. 3. Then the host removes the transmitted packet. 4. When a transmitting host c ...
... Assume the following rules: 1. Whichever host that has "a token" can transmit data (data as a packet). 2. If a host finishes transmitting a packet, the host has to wait for the transmitted packet to come back on the ring. 3. Then the host removes the transmitted packet. 4. When a transmitting host c ...
Guide to Social Networks - Kellogg School of Management
... earlier. Thierry Jomard, a former Carrier engineer who transferred to UTRC to lead the PureCycle development effort, explains: "Carrier people are trained to think in terms of using heat exchange to produce cold air -- that's the output that counts; the compressor is just there to move the fluid. Pr ...
... earlier. Thierry Jomard, a former Carrier engineer who transferred to UTRC to lead the PureCycle development effort, explains: "Carrier people are trained to think in terms of using heat exchange to produce cold air -- that's the output that counts; the compressor is just there to move the fluid. Pr ...
arubaos xsec module - SecureWirelessWorks.com
... Traditionally, encryption has been performed at Layer 3 (Network Layer) in the form of IPsec. IPsec uses 3DES or AES encryption and can encrypt the IP packet including the source and destination IP addresses in the header. IPsec provides a commonly accepted, secure method of communication over untru ...
... Traditionally, encryption has been performed at Layer 3 (Network Layer) in the form of IPsec. IPsec uses 3DES or AES encryption and can encrypt the IP packet including the source and destination IP addresses in the header. IPsec provides a commonly accepted, secure method of communication over untru ...
Cisco Network Visibility Flow Protocol Specification
... Of particular note is data retention and data suppression by an exporter. For example, an exporter should have some means of securely preserving data when it is unable to communicate with the collec ...
... Of particular note is data retention and data suppression by an exporter. For example, an exporter should have some means of securely preserving data when it is unable to communicate with the collec ...
Voice over IP at UCSB
... and synonymous with VoIP are IP telephony, Internet telephony, voice over broadband (VoBB), broadband telephony, and broadband phone. Internet telephony refers to communications services — voice, facsimile, and/or voice-messaging applications — that are transported via the Internet, rather than th ...
... and synonymous with VoIP are IP telephony, Internet telephony, voice over broadband (VoBB), broadband telephony, and broadband phone. Internet telephony refers to communications services — voice, facsimile, and/or voice-messaging applications — that are transported via the Internet, rather than th ...
Demonstrating the Optimal Placement of Virtualized Cellular
... This demonstration highlights how Network Functions Virtualization (NFV) [1] can be used by a mobile network operator to dynamically provide required mobile core network functions for a large “Mega” event like a football game or a concert. Economic reasons may not justify the deployment or continuou ...
... This demonstration highlights how Network Functions Virtualization (NFV) [1] can be used by a mobile network operator to dynamically provide required mobile core network functions for a large “Mega” event like a football game or a concert. Economic reasons may not justify the deployment or continuou ...