Figure 11.01 - 醫學資訊系 鄭仁亮教授
... Simple record structure Lines Fixed length Variable length ...
... Simple record structure Lines Fixed length Variable length ...
PPT - CS
... blocks is lost due to a disk failure, its data can be reconstructed from the other blocks and the parity. ...
... blocks is lost due to a disk failure, its data can be reconstructed from the other blocks and the parity. ...
Najwa Knefati Midterm q
... When they are finished, their priorities revert to their original values. In the example above, a priority-inheritance protocol would allow process L to temporarily inherit the priority of pr ...
... When they are finished, their priorities revert to their original values. In the example above, a priority-inheritance protocol would allow process L to temporarily inherit the priority of pr ...
Windows2000-Spr-2001-sect-2-group
... is going on. • Most threads run at priority levels from 7 to ...
... is going on. • Most threads run at priority levels from 7 to ...
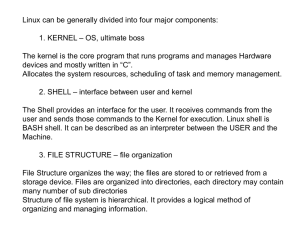
UNIX Notes:
... operating systems. Starting with Windows 2000; Windows XP, Vista and Windows 7 -all have POSIX compliant kernels. Popular Linux OS distributions include: Ubuntu, Fedora, Cygwin, UWin, GNU-win, Debian, Redhat, Knoppix, DSL, Gentu, TinyCore, and MSys. Since it started more than 50 years ago, UNIX has ...
... operating systems. Starting with Windows 2000; Windows XP, Vista and Windows 7 -all have POSIX compliant kernels. Popular Linux OS distributions include: Ubuntu, Fedora, Cygwin, UWin, GNU-win, Debian, Redhat, Knoppix, DSL, Gentu, TinyCore, and MSys. Since it started more than 50 years ago, UNIX has ...
UNIX Notes:
... operating systems. Starting with Windows 2000; Windows XP, Vista and Windows 7 -all have POSIX compliant kernels. Popular Linux OS distributions include: GNU, Ubuntu, Fedora, Debian, Redhat, Knoppix, Puppy, DSL, Gentu, Cygwin, and TinyCore. Since it started more than 50 years ago, UNIX has grown and ...
... operating systems. Starting with Windows 2000; Windows XP, Vista and Windows 7 -all have POSIX compliant kernels. Popular Linux OS distributions include: GNU, Ubuntu, Fedora, Debian, Redhat, Knoppix, Puppy, DSL, Gentu, Cygwin, and TinyCore. Since it started more than 50 years ago, UNIX has grown and ...
Linux - Rock Fort Networks
... any other operating system.[citation needed] It is a leading operating system on servers and other big iron systems such as mainframe computers and supercomputers. Although not released until 1992 due to legal complications, development of 386BSD, from which NetBSD, OpenBSD and FreeBSD descended, ...
... any other operating system.[citation needed] It is a leading operating system on servers and other big iron systems such as mainframe computers and supercomputers. Although not released until 1992 due to legal complications, development of 386BSD, from which NetBSD, OpenBSD and FreeBSD descended, ...
Chapter One
... make up an OS originated with UNIX Linux is a UNIX-like OS and can coexist with Windows and MS-DOS In UNIX, you communicate with the OS programs through an interpreter called the shell and UNIX provides shells such as the Bourne, Korn, and C shells, with Bash being the most popular on Linux systems ...
... make up an OS originated with UNIX Linux is a UNIX-like OS and can coexist with Windows and MS-DOS In UNIX, you communicate with the OS programs through an interpreter called the shell and UNIX provides shells such as the Bourne, Korn, and C shells, with Bash being the most popular on Linux systems ...
CENG334 Introduction to Operating Systems
... File Types – Name, Extension The file type provides information on what can be done with that file to the OS. Typically implemented as the extension of the filename. ...
... File Types – Name, Extension The file type provides information on what can be done with that file to the OS. Typically implemented as the extension of the filename. ...
Computer Software - Welcome to the UNC Department of
... • A type of system software that underlies all other software. • It manages all software and hardware tasks. • It provides a common set of computer functions such as input from a keyboard and output to a monitor. • It provides the user interface……that is: • How can something as simple-minded as a pr ...
... • A type of system software that underlies all other software. • It manages all software and hardware tasks. • It provides a common set of computer functions such as input from a keyboard and output to a monitor. • It provides the user interface……that is: • How can something as simple-minded as a pr ...
Implementing Processes, Threads, and Resources
... A file is an abstraction that represents user data, OS data, an executable, a device, etc. A file is simply a sequence of bytes ...
... A file is an abstraction that represents user data, OS data, an executable, a device, etc. A file is simply a sequence of bytes ...
How To Deploy Windows XP Professional O From careful planning to the
... useful for inventorying client computers. For example, QuickCensus takes a complete hardware inventory and also recognises the majority of software programs in use today. It is excellent at reporting mainstream applications, though not so good at listing software versions or sub-versions. Mid-size t ...
... useful for inventorying client computers. For example, QuickCensus takes a complete hardware inventory and also recognises the majority of software programs in use today. It is excellent at reporting mainstream applications, though not so good at listing software versions or sub-versions. Mid-size t ...
Windows Server 2008
... the number of the second cluster used – When the second cluster is full, the OS continues with the next free cluster and the FAT entry for the second cluster points to the number of the third cluster used, and so on… – When a file is completely written to the disk, the FAT entry for the final cluste ...
... the number of the second cluster used – When the second cluster is full, the OS continues with the next free cluster and the FAT entry for the second cluster points to the number of the third cluster used, and so on… – When a file is completely written to the disk, the FAT entry for the final cluste ...
Introducing and Comparing Operating Systems - c-jump
... – 64-bit processing is faster than 32-bit processing – 64-bit OS requires that device drivers operating in kernel mode be 64-bit drivers – Application is compiled to process 64 bits or 32 bits – 32-bit OS can only address up to 4 GB of memory – Benefit from 64-bit computing if: • Many applications o ...
... – 64-bit processing is faster than 32-bit processing – 64-bit OS requires that device drivers operating in kernel mode be 64-bit drivers – Application is compiled to process 64 bits or 32 bits – 32-bit OS can only address up to 4 GB of memory – Benefit from 64-bit computing if: • Many applications o ...
LESSON 6: COMPUTER OPERATING SYSTEMS Working on a
... Operating System: An operating system controls how programs work with each other and how they interact with the computer hardware. It also creates the file system that determines how your data is stored within a storage device. The performance of an operating system depends on the number of bits th ...
... Operating System: An operating system controls how programs work with each other and how they interact with the computer hardware. It also creates the file system that determines how your data is stored within a storage device. The performance of an operating system depends on the number of bits th ...
Introduction
... • The information about a process is stored in an operating system table called the process table. • A process called the command interpreter or shell is used to read commands from a terminal. • If a process can create one or more other process (child processes) and these process create child proces ...
... • The information about a process is stored in an operating system table called the process table. • A process called the command interpreter or shell is used to read commands from a terminal. • If a process can create one or more other process (child processes) and these process create child proces ...
Windows Vista Boot process
... 1. Options to boot Windows by invoking winload.exe. 2. Options to resume Windows from hibernation by invoking winresume.exe. 3. Options to boot a prior version of the Windows NT family by invoking its NTLDR. 4. Options to load and to execute a Volume Boot Record. 5. Boot Configuration Data allows fo ...
... 1. Options to boot Windows by invoking winload.exe. 2. Options to resume Windows from hibernation by invoking winresume.exe. 3. Options to boot a prior version of the Windows NT family by invoking its NTLDR. 4. Options to load and to execute a Volume Boot Record. 5. Boot Configuration Data allows fo ...
LEC6-FileSystem
... ° OS provide a way to map files into the address space of a running process; map() and unmap() • No read or write system calls are needed thereafter ...
... ° OS provide a way to map files into the address space of a running process; map() and unmap() • No read or write system calls are needed thereafter ...
Introduction to the Solaris Operating Environment
... User name (userl) Specifies the name used by the system to identify the user. Depending on the system administrator, user names are usually some combination of a user's first and last names. For example, a user named Bob Wood might be given the user name bobw, bwood, or woodb. The user name must be ...
... User name (userl) Specifies the name used by the system to identify the user. Depending on the system administrator, user names are usually some combination of a user's first and last names. For example, a user named Bob Wood might be given the user name bobw, bwood, or woodb. The user name must be ...
Operating Systems and File Management 4 Operating System
... To designate a file’s location, you must first specify the device where the file is stored The main hard disk usually is referred to as drive C ...
... To designate a file’s location, you must first specify the device where the file is stored The main hard disk usually is referred to as drive C ...
BackDoors
... Hide the Backdoor Just before commencing the installation of a backdoor, a hacker must investigate within the server to find activated services. He could simply add a new service and give it an inconspicuous name, but he would be better off choosing a service that never gets used and that is either ...
... Hide the Backdoor Just before commencing the installation of a backdoor, a hacker must investigate within the server to find activated services. He could simply add a new service and give it an inconspicuous name, but he would be better off choosing a service that never gets used and that is either ...
Linux Pres1 - Parent Directory
... There may be two types of regular files Executable-Executable files are program that can be run Non-Executable-Non-executable files are text or data files. Directory Files Contains the information about various files stored in the directory. Identified by “d” in the first column of the output of ls ...
... There may be two types of regular files Executable-Executable files are program that can be run Non-Executable-Non-executable files are text or data files. Directory Files Contains the information about various files stored in the directory. Identified by “d” in the first column of the output of ls ...
Operating Systems and File Management
... Boot and Recovery Disks • You can create a custom recovery CD that contains your computer’s current settings and device drivers • Norton Ghost is a product of Symantec, which also provides a more specialized recovery disk called the Symantec Recovery Disk • Certain PC manufacturers have pre-install ...
... Boot and Recovery Disks • You can create a custom recovery CD that contains your computer’s current settings and device drivers • Norton Ghost is a product of Symantec, which also provides a more specialized recovery disk called the Symantec Recovery Disk • Certain PC manufacturers have pre-install ...