Server Installation - Information Technology Gate
... In Linux, the hostname can exist on more than computer, it only uses IP addresses for communication ...
... In Linux, the hostname can exist on more than computer, it only uses IP addresses for communication ...
Unix and shell programming
... It is like a traffic cop -- it makes sure that different programs and users running at the same time do not interfere with each other. The operating system is also responsible for security, it ensuring that unauthorized users do not access the system. ...
... It is like a traffic cop -- it makes sure that different programs and users running at the same time do not interfere with each other. The operating system is also responsible for security, it ensuring that unauthorized users do not access the system. ...
Linux Kernel—File Systems
... Does not point to an inode; It is possible to create cross-file systems symbolic links Point to any type of file, even on nonexistent files. ...
... Does not point to an inode; It is possible to create cross-file systems symbolic links Point to any type of file, even on nonexistent files. ...
CHAPTER 1: Computer Systems
... information should be addressed to the Permissions Department, John Wiley & Sons, Inc. The purchaser may make back-up copies for his/her own use only and not for distribution or resale. The Publisher assumes no responsibility for errors, omissions, or damages caused by the use of these programs or f ...
... information should be addressed to the Permissions Department, John Wiley & Sons, Inc. The purchaser may make back-up copies for his/her own use only and not for distribution or resale. The Publisher assumes no responsibility for errors, omissions, or damages caused by the use of these programs or f ...
Lecture 16
... information should be addressed to the Permissions Department, John Wiley & Sons, Inc. The purchaser may make back-up copies for his/her own use only and not for distribution or resale. The Publisher assumes no responsibility for errors, omissions, or damages caused by the use of these programs or f ...
... information should be addressed to the Permissions Department, John Wiley & Sons, Inc. The purchaser may make back-up copies for his/her own use only and not for distribution or resale. The Publisher assumes no responsibility for errors, omissions, or damages caused by the use of these programs or f ...
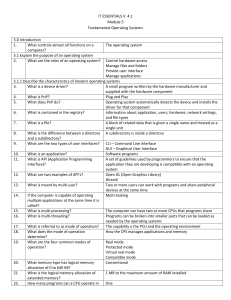
IT ESSENTIALS V. 4.1 Module 5 Fundamental Operating Systems
... The source code can be distributed and changed by anyone as a free download or from other developers 1. Supports multiple users 2. Runs multi-user applications 3. Is robust and redundant 4. Provides increased security Microsoft Windows Novell Netware Linux/Unix Active Directory ...
... The source code can be distributed and changed by anyone as a free download or from other developers 1. Supports multiple users 2. Runs multi-user applications 3. Is robust and redundant 4. Provides increased security Microsoft Windows Novell Netware Linux/Unix Active Directory ...
IT ESSENTIALS V. 4.1 Module 5 Fundamental Operating Systems 5
... What boot configuration utility allows you Msconfig to set the programs that run at startup and to edit configuration files? ...
... What boot configuration utility allows you Msconfig to set the programs that run at startup and to edit configuration files? ...
Services - University of Worcester
... – components that support operating system functions and applications – can run in various different contexts – typically do not offer many user-configurable options ...
... – components that support operating system functions and applications – can run in various different contexts – typically do not offer many user-configurable options ...
CrossOver Compared to Competing Emulation
... in a separate partition and wait for it to load before then loading the actual application. Given the memory issues just discussed, it is impractical for many users to simply keep VMWare running in the background at all times, meaning that the user suffers this startup penalty whenever s/he uses the ...
... in a separate partition and wait for it to load before then loading the actual application. Given the memory issues just discussed, it is impractical for many users to simply keep VMWare running in the background at all times, meaning that the user suffers this startup penalty whenever s/he uses the ...
ppt - Purdue University :: Computer Science
... Current Directory Every process also has a current directory. The open file operations such as open() and fopen() will use the current directory to resolve relative paths. If the path does not start with “/” then a path is relative to the current directory. /etc/hello.c – Absolute path hello.c – Re ...
... Current Directory Every process also has a current directory. The open file operations such as open() and fopen() will use the current directory to resolve relative paths. If the path does not start with “/” then a path is relative to the current directory. /etc/hello.c – Absolute path hello.c – Re ...
Chapter 1 Operating System Fundamentals - computerscience
... PCs and Computer Networks • As desktop computing matured in the workplace, companies installed local-area networks (LANs) to connect desktop PCs so that the PCs could share data and peripherals, such as printers. • A Network operating system (NOS) requires more computing muscle than the desktop cou ...
... PCs and Computer Networks • As desktop computing matured in the workplace, companies installed local-area networks (LANs) to connect desktop PCs so that the PCs could share data and peripherals, such as printers. • A Network operating system (NOS) requires more computing muscle than the desktop cou ...
OS Services System calls and their types
... Operating systems provide an environment for execution of programs and services to programs and users One set of operating-system services provides functions that are helpful to the user: – User interface - Almost all operating systems have a user interface (UI). • Varies between Command-Line (CLI), ...
... Operating systems provide an environment for execution of programs and services to programs and users One set of operating-system services provides functions that are helpful to the user: – User interface - Almost all operating systems have a user interface (UI). • Varies between Command-Line (CLI), ...
Downloading and installing Java SE Development Kit v.8:
... Go to http://www.oracle.com/technetwork/java/javase/downloads/index.html . You should be at a page which says “Oracle” in the top left corner. There should be a gray bar which says “Oracle Technology Network > Java > Java SE > Downloads”. ...
... Go to http://www.oracle.com/technetwork/java/javase/downloads/index.html . You should be at a page which says “Oracle” in the top left corner. There should be a gray bar which says “Oracle Technology Network > Java > Java SE > Downloads”. ...
Chapter 1 Operating System Fundamentals
... MS-DOS • There are several reasons for using MS-DOS: – MS-DOS is a simple, low-overhead operating system – MS-DOS is inexpensive – MS-DOS is stable and reliable – MS-DOS is easy to learn and use – Many programs are available for MS-DOS ...
... MS-DOS • There are several reasons for using MS-DOS: – MS-DOS is a simple, low-overhead operating system – MS-DOS is inexpensive – MS-DOS is stable and reliable – MS-DOS is easy to learn and use – Many programs are available for MS-DOS ...
FileSystems
... Levels of structuring None - sequence of words, bytes Simple record structure Lines Fixed length Variable length Complex structures Formatted document Relocatable load file Can simulate last two with first method by inserting appropriate control characters. Need at least execut ...
... Levels of structuring None - sequence of words, bytes Simple record structure Lines Fixed length Variable length Complex structures Formatted document Relocatable load file Can simulate last two with first method by inserting appropriate control characters. Need at least execut ...
Directories
... Linux file system(History) • It has maximum size limit of 64 megabytes • There was also a filename length limit of 14 characters. • In 1991 a new file system came with addition of new file system as a layer on top of linux kerenl that provide generic file API. Termed as VFS termed as ext. • But has ...
... Linux file system(History) • It has maximum size limit of 64 megabytes • There was also a filename length limit of 14 characters. • In 1991 a new file system came with addition of new file system as a layer on top of linux kerenl that provide generic file API. Termed as VFS termed as ext. • But has ...
slides.01.pdf
... Model: A file is an abstraction of a real storage device (e.g. disk): you can read/write data from/to a file by providing (1) a position in that file, and (2) the amount of data to transfer. Organization: a file is contained in a directory. A directory holds an identifier for each file it contains. ...
... Model: A file is an abstraction of a real storage device (e.g. disk): you can read/write data from/to a file by providing (1) a position in that file, and (2) the amount of data to transfer. Organization: a file is contained in a directory. A directory holds an identifier for each file it contains. ...
Modes of Processing - Bangor Grammar School
... programs at the same time, but only one task is executed at a time • The OS must keep track of where the user is in these tasks and enable them to go from one to the other without losing data (the OS allocates storage and other resources accordingly) ...
... programs at the same time, but only one task is executed at a time • The OS must keep track of where the user is in these tasks and enable them to go from one to the other without losing data (the OS allocates storage and other resources accordingly) ...
Operating Systems and File Management Learning Steps LAP CC
... a) A backup is a copy of one or more files that have been made in case the original files become damages. A good backup plan allows you to 1.______________________ your computing environment to its pre-disaster state with minimum of fuss. b) Your personal backup plan depends on the files you need to ...
... a) A backup is a copy of one or more files that have been made in case the original files become damages. A good backup plan allows you to 1.______________________ your computing environment to its pre-disaster state with minimum of fuss. b) Your personal backup plan depends on the files you need to ...
Desktop PC Operating Systems
... Unused clusters have a zero entry pointer. When a file is deleted, the clusters that were used to save the file are set to zero pointer. In order to store a new file, the OS finds the first cluster with a zero pointer entry and enters the cluster number in the directory table. OS searches linearly f ...
... Unused clusters have a zero entry pointer. When a file is deleted, the clusters that were used to save the file are set to zero pointer. In order to store a new file, the OS finds the first cluster with a zero pointer entry and enters the cluster number in the directory table. OS searches linearly f ...
Ch. 3 - Installation
... Name of computer is not related to how the computer is recognized on the Internet In Linux, the hostname can exist on more than computer, it only uses IP addresses for communication ...
... Name of computer is not related to how the computer is recognized on the Internet In Linux, the hostname can exist on more than computer, it only uses IP addresses for communication ...
General overview of the System
... • Asynchronously – it reads the next cmd line and executes it without waiting for the prior cmd to terminate. Commands executed asynchronously are said to execute in the background.. ...
... • Asynchronously – it reads the next cmd line and executes it without waiting for the prior cmd to terminate. Commands executed asynchronously are said to execute in the background.. ...
Operating System
... • When two or more processes – need to access a restricted resource, – can get into a stalemate situation ...
... • When two or more processes – need to access a restricted resource, – can get into a stalemate situation ...