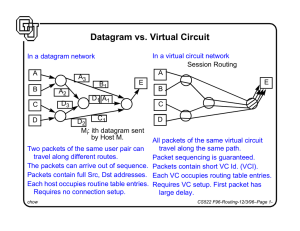
Datagram vs. Virtual Circuit
... Network Operation Center (NOC) collects information from individual nodes NOC carries out the least cost routing algorithms. NOC distributed the routing information to individual nodes. The above steps are carried out periodically. Flooding A node sends/relays a message along all its outgoing links. ...
... Network Operation Center (NOC) collects information from individual nodes NOC carries out the least cost routing algorithms. NOC distributed the routing information to individual nodes. The above steps are carried out periodically. Flooding A node sends/relays a message along all its outgoing links. ...
Assigning agents to a line
... Imagine four applicants are shortlisted for a job interview. Each interview takes an hour. Three applicants prefer to go at 1pm and one applicant prefers to go at 2pm. Every applicant would like an interview as close as possible to his preferred time slot. How should we assign time slots to the four ...
... Imagine four applicants are shortlisted for a job interview. Each interview takes an hour. Three applicants prefer to go at 1pm and one applicant prefers to go at 2pm. Every applicant would like an interview as close as possible to his preferred time slot. How should we assign time slots to the four ...
Recent Progress on the Complexity of Solving Markov Decision
... As was alluded to in the description of value iteration for average-reward MDPs in Section 1.3.2, the structure of the Markov chains induced by the stationary policies for the MDP plays a more prominent role here than in discountedreward problems. Under certain conditions, the analysis of and algori ...
... As was alluded to in the description of value iteration for average-reward MDPs in Section 1.3.2, the structure of the Markov chains induced by the stationary policies for the MDP plays a more prominent role here than in discountedreward problems. Under certain conditions, the analysis of and algori ...
paper
... The nature of wireless networks is intrinsically different from that of wired networks because the wireless medium is shared among many transmitters. The conventional approach to the Medium Access Control (MAC) problem is contention-based protocols in which multiple transmitters simultaneously attem ...
... The nature of wireless networks is intrinsically different from that of wired networks because the wireless medium is shared among many transmitters. The conventional approach to the Medium Access Control (MAC) problem is contention-based protocols in which multiple transmitters simultaneously attem ...
BSDEs and risk-sensitive control, zero-sum and nonzero
... that is an admissible control (u∗ ; v∗ ) such that J (u∗ ; v) 6 J (u∗ ; v∗ ) 6 J (u; v∗ ) for any (u; v). We solve completely this problem under the natural Isaacs’condition and we give the expression of the saddle point, furthermore we characterize the upper and lower values of this zero-sum game. ...
... that is an admissible control (u∗ ; v∗ ) such that J (u∗ ; v) 6 J (u∗ ; v∗ ) 6 J (u; v∗ ) for any (u; v). We solve completely this problem under the natural Isaacs’condition and we give the expression of the saddle point, furthermore we characterize the upper and lower values of this zero-sum game. ...
... AntNet is much better algorithm then present non- ACO based algorithms as it is highly adaptive, uses multipath and stochastic policy for routing data packets but still there is a problem with this ACO based algorithm. One of the major problem is when a path is followed from source node to destinati ...
Adaptive Fairness through intra-ONU Scheduling for Ethernet
... messages from the ONUs, the OLT performs the appropriate bandwidth allocation computation and broadcasts a GATE message to each ONU, containing the appropriate transmission grants (transmission start Tstart and Tend ). Note that MPCP does not specify any particular bandwidth allocation algorithm. In ...
... messages from the ONUs, the OLT performs the appropriate bandwidth allocation computation and broadcasts a GATE message to each ONU, containing the appropriate transmission grants (transmission start Tstart and Tend ). Note that MPCP does not specify any particular bandwidth allocation algorithm. In ...
Robust Design Optimization Strategy of IOSO Technology
... examples of these methods one can see in the [10]. The approximate methods of probability indexes evaluation usually require an additional information from mathematical model such as: responses sensitivities; variable to variable dependencies etc. Moreover, these methods are very sensitive with resp ...
... examples of these methods one can see in the [10]. The approximate methods of probability indexes evaluation usually require an additional information from mathematical model such as: responses sensitivities; variable to variable dependencies etc. Moreover, these methods are very sensitive with resp ...
ECE 654: Computer Networks Final Exam
... TCP interprets packet loss as congestion and slows down. On the other hand in Ad-Hoc networks, a packet can be lost due to channel errors. In this case the node should try to transmit at full speed, not slow down. The ATCP is a sublayer between the IP and transport layer. When it detects a packet lo ...
... TCP interprets packet loss as congestion and slows down. On the other hand in Ad-Hoc networks, a packet can be lost due to channel errors. In this case the node should try to transmit at full speed, not slow down. The ATCP is a sublayer between the IP and transport layer. When it detects a packet lo ...
Kernel Estimation and Model Combination in A Bandit Problem with
... Different variants of the bandit problem motivated by real applications have been studied extensively in the past decade. One promising setting is to assume that the reward distribution of each bandit arm is associated with some common external covariate. More specifically, for an l-armed bandit pro ...
... Different variants of the bandit problem motivated by real applications have been studied extensively in the past decade. One promising setting is to assume that the reward distribution of each bandit arm is associated with some common external covariate. More specifically, for an l-armed bandit pro ...
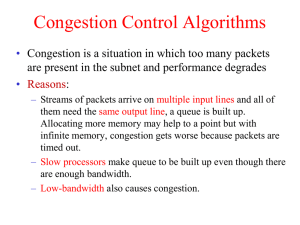
Immediate ECN
... can use existing network hardware • use weighted RED (WRED) implementation • in an unusual configuration – one FIFO queue with two instances of RED algo • smoothed queue for drop • current queue for ECN ...
... can use existing network hardware • use weighted RED (WRED) implementation • in an unusual configuration – one FIFO queue with two instances of RED algo • smoothed queue for drop • current queue for ECN ...
Random Walks on Weighted Graphs, and Applications to On
... certain selected edges (ij), and place no upper bounds on the corresponding ĉij (i.e. set cij = ∞). 2 If C = (cij ) is resistive, the matrix inversion of Section 3 will find the associated conductance matrix σ, with ĉij = cij . If C is not resistive — or even if it is — there is an iterative algor ...
... certain selected edges (ij), and place no upper bounds on the corresponding ĉij (i.e. set cij = ∞). 2 If C = (cij ) is resistive, the matrix inversion of Section 3 will find the associated conductance matrix σ, with ĉij = cij . If C is not resistive — or even if it is — there is an iterative algor ...
IOSR Journal of Electronics and Communication Engineering (IOSR-JECE)
... The AntNet algorithm is a dynamic distributed hybrid routing algorithm that consist both the instances of reactive and pro-active routing protocols. That is, the route setup process is a reactive process and the route maintenance, route improvement process is based on the proactive mechanisms. AntNe ...
... The AntNet algorithm is a dynamic distributed hybrid routing algorithm that consist both the instances of reactive and pro-active routing protocols. That is, the route setup process is a reactive process and the route maintenance, route improvement process is based on the proactive mechanisms. AntNe ...
Distributed Spectrum Management and Relay
... – Capacity of cooperative transmission may be higher or lower than that of direct transmission. Cooperate or not? [1] J. N. Laneman, D. N. C. Tse, and G. W. Wornell, “Cooperative Diversity in Wireless Networks: Efficient Protocols and Outage Behavior,” IEEE Trans. on Information ...
... – Capacity of cooperative transmission may be higher or lower than that of direct transmission. Cooperate or not? [1] J. N. Laneman, D. N. C. Tse, and G. W. Wornell, “Cooperative Diversity in Wireless Networks: Efficient Protocols and Outage Behavior,” IEEE Trans. on Information ...
- INFORMS PubsOnline
... (2006) for some of the known bounds. However, none of these bounds are directly applicable to the combinatorial optimization problem. Our interest in multivariate marginal bounds are motivated by realistic assumptions on dependence information among random parameters in applications from different a ...
... (2006) for some of the known bounds. However, none of these bounds are directly applicable to the combinatorial optimization problem. Our interest in multivariate marginal bounds are motivated by realistic assumptions on dependence information among random parameters in applications from different a ...
Pdf - Text of NPTEL IIT Video Lectures
... being reconstructed. And we will get an optimal solution for that linear programming problem as well. And we will repeat the process in the similar manner we will check whether all the constraints are being satisfied are not. If these are being satisfied we can declare the next optimal solution of t ...
... being reconstructed. And we will get an optimal solution for that linear programming problem as well. And we will repeat the process in the similar manner we will check whether all the constraints are being satisfied are not. If these are being satisfied we can declare the next optimal solution of t ...
Presentation - Kuwait Anesthesia & Critical Care Council
... ■ Need stool assay to rule out C. difficile associated diarrhea ■ Enteroviruses: Rotavirus, norwalk ■ CMV colitis in immunosuppressed ○ Contamination of enteral feeding solution ■ Needs to ensure gloves are clean when handling enteral spike sets/ tubing for open tube feeding formulas ■ All equipment ...
... ■ Need stool assay to rule out C. difficile associated diarrhea ■ Enteroviruses: Rotavirus, norwalk ■ CMV colitis in immunosuppressed ○ Contamination of enteral feeding solution ■ Needs to ensure gloves are clean when handling enteral spike sets/ tubing for open tube feeding formulas ■ All equipment ...
IEEE C802.16maint-08/175r1 Project Title
... exclude these target BSs from the recommended list; however, MS will not be able to perform fast ranging with these BSs. One possible solution is to allow more than one action times to be sent by the BS so that the MS has another chance to ...
... exclude these target BSs from the recommended list; however, MS will not be able to perform fast ranging with these BSs. One possible solution is to allow more than one action times to be sent by the BS so that the MS has another chance to ...
A Survey of Partially Observable Markov Decision Processes
... differently. In some models an observation is taken and then the transition to the new state is made. In this presentation, movement in the chain is followed by an observation. Although the formula for updating the information vector, eqn. (2.2), may be slightly different, the two views are equivale ...
... differently. In some models an observation is taken and then the transition to the new state is made. In this presentation, movement in the chain is followed by an observation. Although the formula for updating the information vector, eqn. (2.2), may be slightly different, the two views are equivale ...
Aalborg Universitet MPE inference in conditional linear gaussian networks Dyhre
... [10]. On the other hand, if the variables of interest correspond to the complement of the observation set, then the problem is referred to as that of finding the most probable explanation (MPE) [2, 6]; MPE can therefore be considered a specialization of MAP. For Bayesian networks containing only dis ...
... [10]. On the other hand, if the variables of interest correspond to the complement of the observation set, then the problem is referred to as that of finding the most probable explanation (MPE) [2, 6]; MPE can therefore be considered a specialization of MAP. For Bayesian networks containing only dis ...
Why Steiner-tree type algorithms work for community detection
... The power law graph family is a natural set of graphs that is not homogenous. For this case, we have a negative result: knowing the structure of the graph is information-theoretically valueless. On the other hand, if none of the highly connected nodes are in S, then finding S in a power law network ...
... The power law graph family is a natural set of graphs that is not homogenous. For this case, we have a negative result: knowing the structure of the graph is information-theoretically valueless. On the other hand, if none of the highly connected nodes are in S, then finding S in a power law network ...
Cost-effective Outbreak Detection in Networks Jure Leskovec Andreas Krause Carlos Guestrin
... these objective functions is NP-hard, so for large, real-world problems, we cannot expect to find the optimal solution. In this paper, we show, that these and many other realistic outbreak detection objectives are submodular, i.e., they exhibit a diminishing returns property: Reading a blog (or placi ...
... these objective functions is NP-hard, so for large, real-world problems, we cannot expect to find the optimal solution. In this paper, we show, that these and many other realistic outbreak detection objectives are submodular, i.e., they exhibit a diminishing returns property: Reading a blog (or placi ...
RUN-TO-RUN OPTIMIZATION VIA CONTROL OF
... optimal solution that are invariant with respect to uncertainty and provide them as references to a feedback control scheme. It will be shown in this paper that, in the run-to-run framework, the invariants correspond to the active terminal constraints and cost sensitivities with respect to input par ...
... optimal solution that are invariant with respect to uncertainty and provide them as references to a feedback control scheme. It will be shown in this paper that, in the run-to-run framework, the invariants correspond to the active terminal constraints and cost sensitivities with respect to input par ...