Presentation - Department of Computer Science and Engineering
... • Recall that each nodes carry an IP list of its immediate N neighbors. • By searching/routing the message to the, the node could returns
us a list of potential parents.
...
... • Recall that each nodes carry an IP list of its immediate N neighbors. • By searching/routing the message to the
Cisco QoS Notes - The Cisco Learning Network
... TCP Slow Start An algorithm used in the TCP/IP Protocol Stack where a sender transmits segments of data and gradually increases its Window Size (cWND) for each Acknowledgment (ACK) received. When an ACK is not received by the other device, this indicates a segment of data was lost in transmission. T ...
... TCP Slow Start An algorithm used in the TCP/IP Protocol Stack where a sender transmits segments of data and gradually increases its Window Size (cWND) for each Acknowledgment (ACK) received. When an ACK is not received by the other device, this indicates a segment of data was lost in transmission. T ...
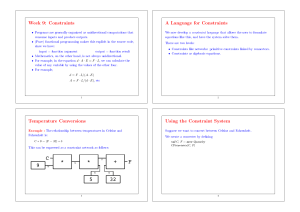
GQR -- A Fast Reasoner for Binary Qualitative Constraint
... Reasoning in GQR is based on a purely syntactical definition of qualitative calculi (Ligozat and Renz 2004; Wölfl, Mossakowski, and Schröder 2007). A (binary) qualitative calculus is defined by a non-empty finite set B of symbols (elements of B are referred to as base relations), a unary function ...
... Reasoning in GQR is based on a purely syntactical definition of qualitative calculi (Ligozat and Renz 2004; Wölfl, Mossakowski, and Schröder 2007). A (binary) qualitative calculus is defined by a non-empty finite set B of symbols (elements of B are referred to as base relations), a unary function ...
IOSR Journal of Electronics and Communication Engineering (IOSR-JECE)
... increasing, on chip communication architectures have a great influence on the performance and area of Systemon- Chip (SoC) design. Network-on-chip have been considered as a most promising candidate for the problem of on chip networks communication and widely accepted by many academician and designer ...
... increasing, on chip communication architectures have a great influence on the performance and area of Systemon- Chip (SoC) design. Network-on-chip have been considered as a most promising candidate for the problem of on chip networks communication and widely accepted by many academician and designer ...
ipqos05
... Congestion can be prevented if TCP sessions (which still make up more than 80% of average Internet traffic) can be slowed down. TCP sessions can be slowed down if some packets are occasionally dropped. Therefore, packets should be dropped when an interface is nearing congestion. ...
... Congestion can be prevented if TCP sessions (which still make up more than 80% of average Internet traffic) can be slowed down. TCP sessions can be slowed down if some packets are occasionally dropped. Therefore, packets should be dropped when an interface is nearing congestion. ...
sigcomm`11 - Cornell Computer Science
... vertex d which is reachable from all of D, and then (in the algorithm’s last line) test the absence of v-d reachability. This will produce an example of a packet that is dropped or confirm that none exists.2 Of course, in some cases packet loss is the correct behavior. For example, in the campus net ...
... vertex d which is reachable from all of D, and then (in the algorithm’s last line) test the absence of v-d reachability. This will produce an example of a packet that is dropped or confirm that none exists.2 Of course, in some cases packet loss is the correct behavior. For example, in the campus net ...
Labham Gupta
... iterative algorithm, there is no need predict the tendency of switch angles in the entire modulation range in advance. Load can be better inhibition for selective harmonic elimination method based on GA, the size of the load will affect the output waveform of the inverter, and cause the increased ha ...
... iterative algorithm, there is no need predict the tendency of switch angles in the entire modulation range in advance. Load can be better inhibition for selective harmonic elimination method based on GA, the size of the load will affect the output waveform of the inverter, and cause the increased ha ...
The Basics of Financial Mathematics Spring 2003 Richard F. Bass Department of Mathematics
... a given time. For example, suppose Microsoft is currently selling today at $40 per share. A European call option is something I can buy that gives me the right to buy a share of Microsoft at some future date. To make up an example, suppose I have an option that allows me to buy a share of Microsoft ...
... a given time. For example, suppose Microsoft is currently selling today at $40 per share. A European call option is something I can buy that gives me the right to buy a share of Microsoft at some future date. To make up an example, suppose I have an option that allows me to buy a share of Microsoft ...
Presenting
... D={Di,j}, defines the demand Di,j, between each source i and destination j. • We define the following routing paradigms : • Unrestricted Splitable Routing (US-R) – a flow can be split among the outgoing links arbitrarily • Restricted Splitable Routing (RS-R) - a flow can be split over a predefined n ...
... D={Di,j}, defines the demand Di,j, between each source i and destination j. • We define the following routing paradigms : • Unrestricted Splitable Routing (US-R) – a flow can be split among the outgoing links arbitrarily • Restricted Splitable Routing (RS-R) - a flow can be split over a predefined n ...
On the Optimal Communication Spanning Tree Problem Working
... OCST problem we use a classical canonical GA (Goldberg, 1989) with crossover as the main search operator and some background mutation. We know from previous work (Harik, Cantú-Paz, Goldberg, & Miller, 1997) that the probability of GA failure α goes with O(exp(−N )), where N is the used population s ...
... OCST problem we use a classical canonical GA (Goldberg, 1989) with crossover as the main search operator and some background mutation. We know from previous work (Harik, Cantú-Paz, Goldberg, & Miller, 1997) that the probability of GA failure α goes with O(exp(−N )), where N is the used population s ...
Sharp estimation of the almost-sure Lyapunov exponent for the
... u, a direction which was never achieved precisely before, with potentially important consequences for the physical systems connected to the Anderson model. We refer to [7] and [11] for specific physical motivations in astrophysics, hydrodynamics, and other fields. In general modeling terms, our ulti ...
... u, a direction which was never achieved precisely before, with potentially important consequences for the physical systems connected to the Anderson model. We refer to [7] and [11] for specific physical motivations in astrophysics, hydrodynamics, and other fields. In general modeling terms, our ulti ...
Simple Seeding of Evolutionary Algorithms for Hard Multiobjective
... that for hard MOPs this may not be possible if weighted sums of the objective functions are minimized to obtain seeds, as done here. We include a simple proof for completeness. Let P be the Pareto front and denote by C the nonnegative orthant of the space of objective vectors. Let P + C be the set o ...
... that for hard MOPs this may not be possible if weighted sums of the objective functions are minimized to obtain seeds, as done here. We include a simple proof for completeness. Let P be the Pareto front and denote by C the nonnegative orthant of the space of objective vectors. Let P + C be the set o ...
Towards Joint Resource Allocation and Routing to Optimize Video
... distribution over media cloud [6], [7], by jointly considering the NFV-enabled storage and computing resource allocation, and the SDN-enabled routing. In particular, we consider the orchestration of routing, caching and transcoding functions. At each node, the caching function brings the contents to ...
... distribution over media cloud [6], [7], by jointly considering the NFV-enabled storage and computing resource allocation, and the SDN-enabled routing. In particular, we consider the orchestration of routing, caching and transcoding functions. At each node, the caching function brings the contents to ...
Finding Optimal Bayesian Network Given a Super
... limiting edge additions to the one present in the retrieved skeleton. As a result, it follows a similar technique than that of SC, except that the number of candidate parents is tuned adaptively for each node, and that the chosen candidates are sound in the sample limit. It is worth to notice that t ...
... limiting edge additions to the one present in the retrieved skeleton. As a result, it follows a similar technique than that of SC, except that the number of candidate parents is tuned adaptively for each node, and that the chosen candidates are sound in the sample limit. It is worth to notice that t ...
Optimality of Walrand-Varaiya Type Policies and Markov Sources
... stage deterministically, i.e. at = αt (x0 , . . . , xt ). The set of all deterministic policies is denoted ΠD . Note that ΠD ⊂ ΠA . Definition 1.14 (Markov Policy [9]). A Markov policy is a policy Π such that for each time stage the choice of control is only dependent on the current state xt , i.e. ...
... stage deterministically, i.e. at = αt (x0 , . . . , xt ). The set of all deterministic policies is denoted ΠD . Note that ΠD ⊂ ΠA . Definition 1.14 (Markov Policy [9]). A Markov policy is a policy Π such that for each time stage the choice of control is only dependent on the current state xt , i.e. ...
The dual of the space of holomorphic functions on locally closed
... is a topological isomorphism into and when it is surjective. ...
... is a topological isomorphism into and when it is surjective. ...
Evaluation of di erent Multicast Techniques for Video
... level. By this process we obtain 8 additional subWait For All (WFA): this algorithm elimibands from second resolution level. Therefore, at nates the consolidation noise, because it wait the end of the decomposition process we obtain one BRM cell for each branch of the multicast 7+7+8 subbands. A ful ...
... level. By this process we obtain 8 additional subWait For All (WFA): this algorithm elimibands from second resolution level. Therefore, at nates the consolidation noise, because it wait the end of the decomposition process we obtain one BRM cell for each branch of the multicast 7+7+8 subbands. A ful ...
- Wiley Online Library
... function of the input random processes, to represent them in terms of a set of uncorrelated random variables [33, 34]. Polynomial chaos expansion can also be used to represent random fields [35–37], where the coefficients of the PC modes can be determined based on the principles of maximum likelihoo ...
... function of the input random processes, to represent them in terms of a set of uncorrelated random variables [33, 34]. Polynomial chaos expansion can also be used to represent random fields [35–37], where the coefficients of the PC modes can be determined based on the principles of maximum likelihoo ...
Generalised Integer Programming Based on Logically Defined
... Let V be a set of variables. For x ∈ V and a ∈ D, the inequalities x ≥ a and x ≤ a are called positive and negative literals, respectively. A clause is a disjunction of literals. A clausal pattern is a multiset of the form P = (+a1 , . . . , +ap , −b1 , . . . , −bq ) where p, q ∈ N and ai , bi ∈ D f ...
... Let V be a set of variables. For x ∈ V and a ∈ D, the inequalities x ≥ a and x ≤ a are called positive and negative literals, respectively. A clause is a disjunction of literals. A clausal pattern is a multiset of the form P = (+a1 , . . . , +ap , −b1 , . . . , −bq ) where p, q ∈ N and ai , bi ∈ D f ...
Moral Hazard and the Spanning Condition
... the FOA is not always valid. That is, sometimes the agent must be prevented from deviating to more remote actions; “non-local”incentive compatibility constraints may be binding. Another common approach simply assumes that the agent’s e¤ort is either high or low, in which case the incentive compatibi ...
... the FOA is not always valid. That is, sometimes the agent must be prevented from deviating to more remote actions; “non-local”incentive compatibility constraints may be binding. Another common approach simply assumes that the agent’s e¤ort is either high or low, in which case the incentive compatibi ...
Using Loss Pairs to Discover Network Properties
... for predicting delay and jitter for multimedia applications using the path. In some settings it may be relatively easy to estimate the amount of buffering on a link. When packets flow over only a single hop (or in the absence of any cross traffic on a multi-hop path) then one can estimate buffering ...
... for predicting delay and jitter for multimedia applications using the path. In some settings it may be relatively easy to estimate the amount of buffering on a link. When packets flow over only a single hop (or in the absence of any cross traffic on a multi-hop path) then one can estimate buffering ...
IOSR Journal of Electronics and Communication Engineering (IOSR-JECE)
... Code Division Multiple Access (CDMA) is the preferred access technique for mobile communications mainly for its capacity reasons [1]. Its advantage over other multiple access schemes (like FDMA and TDMA) include higher spectral reuse efficiency, greater immunity to multipath fading, more robust hand ...
... Code Division Multiple Access (CDMA) is the preferred access technique for mobile communications mainly for its capacity reasons [1]. Its advantage over other multiple access schemes (like FDMA and TDMA) include higher spectral reuse efficiency, greater immunity to multipath fading, more robust hand ...