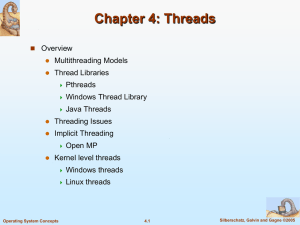
Java Threads
... Linux refers to them as tasks rather than threads Thread creation is done through clone() system call clone() allows a child task to share the address space ...
... Linux refers to them as tasks rather than threads Thread creation is done through clone() system call clone() allows a child task to share the address space ...
SafeDrive: Safe and Recoverable Extensions Using Language-Based Techniques
... • Lower overhead for isolation: SafeDrive exhibits lower overhead in general, particularly for extensions with many crossings (for which Nooks admits it is a poor fit [33, Sec. 6.4]). Compared with SafeDrive, hardware-enforced isolation incurs additional overhead due to domain changes, page table up ...
... • Lower overhead for isolation: SafeDrive exhibits lower overhead in general, particularly for extensions with many crossings (for which Nooks admits it is a poor fit [33, Sec. 6.4]). Compared with SafeDrive, hardware-enforced isolation incurs additional overhead due to domain changes, page table up ...
Chapter 1 Slides
... Process needs resources to accomplish its task CPU, memory, I/O, files (received upon creation and along execution) Initialization data (e.g., a process for presenting the status of a file) Process termination requires reclaim of any reusable resources Single-threaded process has one ...
... Process needs resources to accomplish its task CPU, memory, I/O, files (received upon creation and along execution) Initialization data (e.g., a process for presenting the status of a file) Process termination requires reclaim of any reusable resources Single-threaded process has one ...
Operating Systems
... Since every thread can access every memory address within the process’ address space, one thread can read, write, or even completely wipe out another thread’s stack. There is no protection between threads. A thread can be in any one of several states: running, blocked, ready, or terminated. th ...
... Since every thread can access every memory address within the process’ address space, one thread can read, write, or even completely wipe out another thread’s stack. There is no protection between threads. A thread can be in any one of several states: running, blocked, ready, or terminated. th ...
What is an operating system?
... OS Real-Time Extensions Extension of an OS by real-time components Cooperation between RT- and non-RT parts ...
... OS Real-Time Extensions Extension of an OS by real-time components Cooperation between RT- and non-RT parts ...
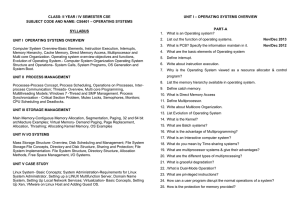
Document
... 11. Explain the facilities provided by the following operating system 12. List out the services provided by operating systems to programs and to the 13. Define operating system and list out the function and component of operating system. 14. Explain in detail the modern computer system 15. Explain t ...
... 11. Explain the facilities provided by the following operating system 12. List out the services provided by operating systems to programs and to the 13. Define operating system and list out the function and component of operating system. 14. Explain in detail the modern computer system 15. Explain t ...
File - BS
... At most one I/O request is outstanding at a time, no simultaneous I/O processing After I/O starts, control returns to user program without waiting for I/O completion System call – request to the operating system to allow user to wait for I/O completion Device-status table contains entry for ...
... At most one I/O request is outstanding at a time, no simultaneous I/O processing After I/O starts, control returns to user program without waiting for I/O completion System call – request to the operating system to allow user to wait for I/O completion Device-status table contains entry for ...
Isolating Operating System Components with Intel SGX
... are shielded from all other software running on the system including privileged software such as the operating system or the hypervisor. The Intel Skylake processor, released in October 2015, allows the creation and execution of SGX enclaves via its extended instruction set. Various researchers alre ...
... are shielded from all other software running on the system including privileged software such as the operating system or the hypervisor. The Intel Skylake processor, released in October 2015, allows the creation and execution of SGX enclaves via its extended instruction set. Various researchers alre ...
A Time-Composable Operating System for the
... active partition are scheduled in fixed-priority order. Servicing in constant time removes jitter from the time behavior of the RTOS. The TiCOS scheduler also enforces run-tocompletion semantics: a process can become ready at any time of in the partition’s scheduling slot, but its activation is defe ...
... active partition are scheduled in fixed-priority order. Servicing in constant time removes jitter from the time behavior of the RTOS. The TiCOS scheduler also enforces run-tocompletion semantics: a process can become ready at any time of in the partition’s scheduling slot, but its activation is defe ...
第六章文件系统
... The system can see from the count in the i-node that the file is still in use, but there is no way for it to find all the dir entries for the file, in order to erase them. The problem with symbolic links is the extra overhead ...
... The system can see from the count in the i-node that the file is still in use, but there is no way for it to find all the dir entries for the file, in order to erase them. The problem with symbolic links is the extra overhead ...
Threads (continued)
... • Does fork() duplicate only the calling thread or all threads? – Easy if user-level threads – Not so easy with kernel-level threads • Linux has special clone() operation – only forking thread is created in child process • Windows XP has something similar ...
... • Does fork() duplicate only the calling thread or all threads? – Easy if user-level threads – Not so easy with kernel-level threads • Linux has special clone() operation – only forking thread is created in child process • Windows XP has something similar ...
Operating-System Debugging
... Booting – starting a computer by loading the kernel Bootstrap program – code stored in ROM that is able to locate the kernel, ...
... Booting – starting a computer by loading the kernel Bootstrap program – code stored in ROM that is able to locate the kernel, ...
PPT
... Load Sharing One of the most commonly used schemes in current multiprocessors, despite the potential disadvantages • Load is distributed evenly across the processors ...
... Load Sharing One of the most commonly used schemes in current multiprocessors, despite the potential disadvantages • Load is distributed evenly across the processors ...
Race Conditions
... • So far, we have discussed Processes and Threads and talked about multithreading and MPI processes by example. • You will implement these in the programming assignment, and see that in some cases, multiple threads can be more efficient than multiple processes. • We have seen that threads can share ...
... • So far, we have discussed Processes and Threads and talked about multithreading and MPI processes by example. • You will implement these in the programming assignment, and see that in some cases, multiple threads can be more efficient than multiple processes. • We have seen that threads can share ...
The Impact of Architectural Trends on Operating System Performance
... Workload selection plays a large part in exposing operating system behavior. Our choice of workloads reflects a desire to investigate realistic applications found in a variety of computing environments. The three workloads that we use represent program development, commercial data processing, and en ...
... Workload selection plays a large part in exposing operating system behavior. Our choice of workloads reflects a desire to investigate realistic applications found in a variety of computing environments. The three workloads that we use represent program development, commercial data processing, and en ...
Definition of Operating System
... The users of batch operating system do not interact with the computer directly. Each user prepares his job on an off-line device like punch cards and submits it to the computer operator. To speed up processing, jobs with similar needs are batched together and run as a group. Thus, the programmers le ...
... The users of batch operating system do not interact with the computer directly. Each user prepares his job on an off-line device like punch cards and submits it to the computer operator. To speed up processing, jobs with similar needs are batched together and run as a group. Thus, the programmers le ...
slide
... processors If one thread in a process is blocked, kernel can schedule another thread of the same process ...
... processors If one thread in a process is blocked, kernel can schedule another thread of the same process ...
Windows 2000 System Architecture
... Included to meet US Government requirements Windows 2000 implements POSIX 1003.1 Provides limited set of services • Can’t create threads, windows or use sockets! – Executables linked against POSIX subsystem library (Psxdll.dll) – Commercial Unix-to-Win32 library better approach for porting UNIX appl ...
... Included to meet US Government requirements Windows 2000 implements POSIX 1003.1 Provides limited set of services • Can’t create threads, windows or use sockets! – Executables linked against POSIX subsystem library (Psxdll.dll) – Commercial Unix-to-Win32 library better approach for porting UNIX appl ...
Chapter 3
... • A user action (e.g. log off, quitting an application) :For an interactive application, the action of the user will indicate when the process is completed • A fault or error • Parent process terminating ...
... • A user action (e.g. log off, quitting an application) :For an interactive application, the action of the user will indicate when the process is completed • A fault or error • Parent process terminating ...
C Programming under Linux
... The origins of Linux are in an operating system called UNICS c. 1969. This system developed into UNIX through the 70s – in parallel with a new programming language written for its operating system, C. Unix was developed initially on hugely expensive computers costing millions of $, £ or Euros. Unix ...
... The origins of Linux are in an operating system called UNICS c. 1969. This system developed into UNIX through the 70s – in parallel with a new programming language written for its operating system, C. Unix was developed initially on hugely expensive computers costing millions of $, £ or Euros. Unix ...
ch13
... I/O instructions All I/O instructions defined to be privileged I/O must be performed via system calls Memory-mapped and I/O port memory locations must be protected too ...
... I/O instructions All I/O instructions defined to be privileged I/O must be performed via system calls Memory-mapped and I/O port memory locations must be protected too ...
UNIX
... When power is initially applied to the computer this triggers the RESET pin on the processor. This causes the processor to read from memory location 0xFFFFFFF0 and begin executing the code located there. This address is mapped to the ReadOnly Memory (ROM) containing the BIOS. The BIOS must poll the ...
... When power is initially applied to the computer this triggers the RESET pin on the processor. This causes the processor to read from memory location 0xFFFFFFF0 and begin executing the code located there. This address is mapped to the ReadOnly Memory (ROM) containing the BIOS. The BIOS must poll the ...