RADIUS Implementation and Deployment Best Practices
... (OTP), MD5-Challenge, Transport Level Security (TLS) for smart card and certificate support, as well as any future authentication technologies. EAP is a critical technology component for secure connections. In addition to support within PPP, EAP is also supported within the IEEE 802 link layer. IEEE ...
... (OTP), MD5-Challenge, Transport Level Security (TLS) for smart card and certificate support, as well as any future authentication technologies. EAP is a critical technology component for secure connections. In addition to support within PPP, EAP is also supported within the IEEE 802 link layer. IEEE ...
Open_Id
... • Uses proven technologies like DNS, HTTP, • SSL/TLS and Diffie-Hellman • It’s Decentralized • It’s Free ...
... • Uses proven technologies like DNS, HTTP, • SSL/TLS and Diffie-Hellman • It’s Decentralized • It’s Free ...
Chapter 15
... techniques, that can be verified by anyone and includes: – The name of the holder and other identification information, such as e-mail address – A public key, which can be used to verify the digital signature of a message sender previously signed with the matching mathematically unique private key – ...
... techniques, that can be verified by anyone and includes: – The name of the holder and other identification information, such as e-mail address – A public key, which can be used to verify the digital signature of a message sender previously signed with the matching mathematically unique private key – ...
LogMeIn Security – an In-Depth Look
... Authentication of Users to the Gateway Clients must be authenticated by both the Gateway and the Host. When a client logs on to the LogMeIn website a simple email address / password verification is performed. Users are advised to enable one or more of the extra security options that LogMeIn provides ...
... Authentication of Users to the Gateway Clients must be authenticated by both the Gateway and the Host. When a client logs on to the LogMeIn website a simple email address / password verification is performed. Users are advised to enable one or more of the extra security options that LogMeIn provides ...
www.siskiyous.edu
... • Run specialized disk sanitizer program • Remove disk and use magnetic hard disk eraser ...
... • Run specialized disk sanitizer program • Remove disk and use magnetic hard disk eraser ...
Designing of a semi-automation tool for wireless LAN interoperability testing Jukka Issakainen
... Interoperability testing for devices using wireless local area networks may require a complex test environment consisting of several Access Points and authentication servers. These entities are used to verify the correct operation of a device under test. Each entity has several settings for various ...
... Interoperability testing for devices using wireless local area networks may require a complex test environment consisting of several Access Points and authentication servers. These entities are used to verify the correct operation of a device under test. Each entity has several settings for various ...
CCNPv5 Module 5 Lesson 1
... Containment: Contain the spread of the worm into your network and within your network. Compartmentalise uninfected parts of your network. Inoculation: Start patching all systems and, if possible, scanning for vulnerable systems. Quarantine: Track down each infected machine inside your network. Disco ...
... Containment: Contain the spread of the worm into your network and within your network. Compartmentalise uninfected parts of your network. Inoculation: Start patching all systems and, if possible, scanning for vulnerable systems. Quarantine: Track down each infected machine inside your network. Disco ...
12_Auth_nemo
... Multiple Methods • Example: “where you are” also requires entity to have LSS and GPS, so also “what you have” • Can assign different methods to different tasks – As users perform more and more sensitive tasks, must authenticate in more and more ways (presumably, more stringently) – File describes a ...
... Multiple Methods • Example: “where you are” also requires entity to have LSS and GPS, so also “what you have” • Can assign different methods to different tasks – As users perform more and more sensitive tasks, must authenticate in more and more ways (presumably, more stringently) – File describes a ...
CAS: The Yale Central Authentication Service
... n-tier authentication problem uPortal can authenticate users securely with CAS But it does not know about users’ primary credentials This is a good thing, except uPortal can’t impersonate the user in order to acquire secure data for the user ...
... n-tier authentication problem uPortal can authenticate users securely with CAS But it does not know about users’ primary credentials This is a good thing, except uPortal can’t impersonate the user in order to acquire secure data for the user ...
Deployment of IPSec Virtual Private Network Solutions
... Transport ESP (IP/port50) AH (IP/port51) Network address translation (NAT) ...
... Transport ESP (IP/port50) AH (IP/port51) Network address translation (NAT) ...
Advanced Operating Systems, CSci555
... Base conditions require presentation or availability of credential – Matching the condition brings in additional policy elements. ...
... Base conditions require presentation or availability of credential – Matching the condition brings in additional policy elements. ...
Protection Mechanisms
... intended to control physical access or logical access—always consists of both authentication and authorization Management of Information Security ...
... intended to control physical access or logical access—always consists of both authentication and authorization Management of Information Security ...
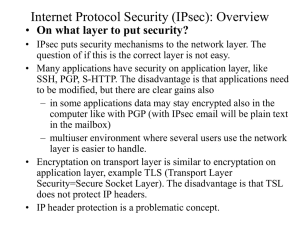
IPSec: Cryptography basics
... • OS and BITS implementation • IPsec is preferably implemented in the operating system level (OS) and merged with the IP level. This is called IPsec stack method. All IPsec options can be implemented and the implementation can be very efficient. IP fragmentation can be handled with the same code as ...
... • OS and BITS implementation • IPsec is preferably implemented in the operating system level (OS) and merged with the IP level. This is called IPsec stack method. All IPsec options can be implemented and the implementation can be very efficient. IP fragmentation can be handled with the same code as ...
Operating System Security Rules
... Systems that have sensitive corporate data must authenticate users with one-time passwords generated by handheld devices or software such as S/Key. S/Key requires that the remote host know a password that will not be transmitted over an insecure channel. When you connect to the host, you get a chall ...
... Systems that have sensitive corporate data must authenticate users with one-time passwords generated by handheld devices or software such as S/Key. S/Key requires that the remote host know a password that will not be transmitted over an insecure channel. When you connect to the host, you get a chall ...
PCI DSS glossary of terms - PCI Security Standards Council
... (2) For Discover, JCB, MasterCard, and Visa payment cards, the second type of card verification value or code is the rightmost three-digit value printed in the signature panel area on the back of the card. For American Express payment cards, the code is a four-digit unembossed number printed above t ...
... (2) For Discover, JCB, MasterCard, and Visa payment cards, the second type of card verification value or code is the rightmost three-digit value printed in the signature panel area on the back of the card. For American Express payment cards, the code is a four-digit unembossed number printed above t ...
Data Encryption Standard - gozips.uakron.edu
... From whom should data be protected? What costs are associated with security being breached and ...
... From whom should data be protected? What costs are associated with security being breached and ...
Cybersecurity for Critical Control Systems in the Power Industry
... assets (CCAs) at power generation facilities through the voluntary efforts of the North American Electric Reliability Corporation (NERC). A non-governmental, independent, and not-for-profit organization, NERC seeks to ensure the reliability of the bulk electric system in North America through the de ...
... assets (CCAs) at power generation facilities through the voluntary efforts of the North American Electric Reliability Corporation (NERC). A non-governmental, independent, and not-for-profit organization, NERC seeks to ensure the reliability of the bulk electric system in North America through the de ...
Speech Title Here
... Principle #1: The defender must defend all points; the attacker can choose the weakest point. Principle #2: The defender can defend only against known attacks; the attacker can probe for unknown vulnerabilities. Principle #3: The defender must be constantly vigilant; the attacker can strike at will. ...
... Principle #1: The defender must defend all points; the attacker can choose the weakest point. Principle #2: The defender can defend only against known attacks; the attacker can probe for unknown vulnerabilities. Principle #3: The defender must be constantly vigilant; the attacker can strike at will. ...
SSH - Information Services and Technology
... that only the recipient can read the transmitted data. • Man-in-the-Middle Attack: The SSH protocol applies server authentication and cryptographic integrity checks to ensure that the data cannot be modified undetected while sent through a network. ...
... that only the recipient can read the transmitted data. • Man-in-the-Middle Attack: The SSH protocol applies server authentication and cryptographic integrity checks to ensure that the data cannot be modified undetected while sent through a network. ...
Oracle9i Security
... $455,848,000 in quantifiable losses $170,827,000 theft of proprietary information $115,753,000 in financial fraud ...
... $455,848,000 in quantifiable losses $170,827,000 theft of proprietary information $115,753,000 in financial fraud ...
Permissions
... • Users need an account in each database they need to access • There are two special accounts ...
... • Users need an account in each database they need to access • There are two special accounts ...
Joshua White - Everis Inc.
... The Attacker Is Sitting (Sniffing) A Live Session And HiJacks It Using Both Spoofed IP, MAC, Authentication, Etc. Used Heavily In MITM Attacks ...
... The Attacker Is Sitting (Sniffing) A Live Session And HiJacks It Using Both Spoofed IP, MAC, Authentication, Etc. Used Heavily In MITM Attacks ...
Application Security within Java 2, Standard Edition (J2SE)
... is loaded, the system uses a class called the SecureClassLoader (java.security.SecureClassLoader) to load the class. First the class is loaded from the specified URL and then the digital signature of the class is checked to make sure that the class is correct and intact. A CodeSource object is deriv ...
... is loaded, the system uses a class called the SecureClassLoader (java.security.SecureClassLoader) to load the class. First the class is loaded from the specified URL and then the digital signature of the class is checked to make sure that the class is correct and intact. A CodeSource object is deriv ...
Authentication
.png?width=300)
Authentication (from Greek: αὐθεντικός authentikos, ""real, genuine,"" from αὐθέντης authentes, ""author"") is the act of confirming the truth of an attribute of a single piece of data (a datum) claimed true by an entity. In contrast with identification which refers to the act of stating or otherwise indicating a claim purportedly attesting to a person or thing's identity, authentication is the process of actually confirming that identity. It might involve confirming the identity of a person by validating their identity documents, verifying the validity of a Website with a digital certificate, tracing the age of an artifact by carbon dating, or ensuring that a product is what its packaging and labeling claim to be. In other words, authentication often involves verifying the validity of at least one form of identification.