JRA1.4 AAs in eduGAIN
... ● Permit delegation of the management of user information in a clear and secure way. ● Provide new architectural elements that could seamlessly integrate with existing architectures (to simplify technical adoption of such a solution by all the participants to the federation). ● Leverage the existing ...
... ● Permit delegation of the management of user information in a clear and secure way. ● Provide new architectural elements that could seamlessly integrate with existing architectures (to simplify technical adoption of such a solution by all the participants to the federation). ● Leverage the existing ...
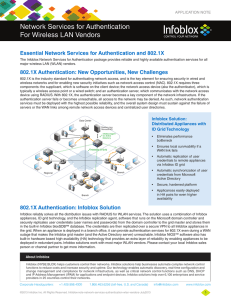
Network Services for Authentication For Wireless LAN
... 802.1X is the industry standard for authenticating network access, and is the key element for ensuring security in wired and wireless networks and for enabling new security initiatives such as network access control (NAC). 802.1X requires three components: the supplicant, which is software on the cl ...
... 802.1X is the industry standard for authenticating network access, and is the key element for ensuring security in wired and wireless networks and for enabling new security initiatives such as network access control (NAC). 802.1X requires three components: the supplicant, which is software on the cl ...
Authentication
.png?width=300)
Authentication (from Greek: αὐθεντικός authentikos, ""real, genuine,"" from αὐθέντης authentes, ""author"") is the act of confirming the truth of an attribute of a single piece of data (a datum) claimed true by an entity. In contrast with identification which refers to the act of stating or otherwise indicating a claim purportedly attesting to a person or thing's identity, authentication is the process of actually confirming that identity. It might involve confirming the identity of a person by validating their identity documents, verifying the validity of a Website with a digital certificate, tracing the age of an artifact by carbon dating, or ensuring that a product is what its packaging and labeling claim to be. In other words, authentication often involves verifying the validity of at least one form of identification.