SAQ D Compliance Scott St. Aubin Senior Security Consultant QSA, CISM, CISSP
... Requirement 12: Maintain a policy that addresses information security for employees and contractors • Technical Guideline (Draft) includes items that can be ...
... Requirement 12: Maintain a policy that addresses information security for employees and contractors • Technical Guideline (Draft) includes items that can be ...
Hands-On Ethical Hacking and Network Security
... Wireless LANs do not have an address associated with a physical location ...
... Wireless LANs do not have an address associated with a physical location ...
Get a WIF of this!
... IP-STSs, you use an FP-STS as an intermediary between the IP-STSs and your RP. ...
... IP-STSs, you use an FP-STS as an intermediary between the IP-STSs and your RP. ...
Red Hat Database
... combining these features with a good security strategy, and by making use of updates and information available via Red Hat Network, you can make your Red Hat Database data environment secure. ...
... combining these features with a good security strategy, and by making use of updates and information available via Red Hat Network, you can make your Red Hat Database data environment secure. ...
document
... potential pitfalls or "weak spots" in the VPN model can be easy to forget. These four concerns with VPN solutions are often raised. ...
... potential pitfalls or "weak spots" in the VPN model can be easy to forget. These four concerns with VPN solutions are often raised. ...
Best Practices for Wireless LAN Security & Operational Support
... Physicians and clinicians bringing in unauthorized devices with wireless access cards ...
... Physicians and clinicians bringing in unauthorized devices with wireless access cards ...
Chapter 8
... ▫ Hello-interval and dead-interval must match on all routers for them to form the neighbor table ...
... ▫ Hello-interval and dead-interval must match on all routers for them to form the neighbor table ...
C N+1
... The attacker modifies the ICV (detailed later) The attacker transmits the modified frame The access point receives the frame and verifies the ICV based on the frame contents The AP accepts the modified frame The destination receiver de-encapsulates the frame and processes the ...
... The attacker modifies the ICV (detailed later) The attacker transmits the modified frame The access point receives the frame and verifies the ICV based on the frame contents The AP accepts the modified frame The destination receiver de-encapsulates the frame and processes the ...
802.1X Authentication - Training
... Some EAP methods, such as EAP-TLS, use certificate-based authentication to uniquely identify a client and provide the ability for the client to authenticate to the network without user intervention. Both the client and server have an identity, and these identities, along with other certificates, are ...
... Some EAP methods, such as EAP-TLS, use certificate-based authentication to uniquely identify a client and provide the ability for the client to authenticate to the network without user intervention. Both the client and server have an identity, and these identities, along with other certificates, are ...
Lecture5 - The University of Texas at Dallas
... identity, commonly called identity proofing. Various methods of identity proofing are available ranging from in person validation using government issued identification to anonymous methods that allow the claimant to remain anonymous, but known to the system if they return. The method used for ident ...
... identity, commonly called identity proofing. Various methods of identity proofing are available ranging from in person validation using government issued identification to anonymous methods that allow the claimant to remain anonymous, but known to the system if they return. The method used for ident ...
Security - The University of Texas at Dallas
... • You hear them murmur, "Let's see you use that VISA card now, Professor "I-Don't-Give-A's-To Any MBA Candidate!" ...
... • You hear them murmur, "Let's see you use that VISA card now, Professor "I-Don't-Give-A's-To Any MBA Candidate!" ...
Cyber Solutions for NEI 08-09 Whitepaper 119 KB
... GE provides security consulting services to asset owners and operators in the nuclear sector. We also provide technical solutions designed and tested for the industrial controls environment. Our solutions are built with security in mind, and are readily integrated into broader plant-level systems an ...
... GE provides security consulting services to asset owners and operators in the nuclear sector. We also provide technical solutions designed and tested for the industrial controls environment. Our solutions are built with security in mind, and are readily integrated into broader plant-level systems an ...
lesson05 - Seneca - School of Information & Communications
... physical port, such as someone plugging into a single wall jack using an Ethernet cable, or a logical port, such as one or more people connecting to a wireless access point using the WiFi cards in one or more laptops or handheld devices. ...
... physical port, such as someone plugging into a single wall jack using an Ethernet cable, or a logical port, such as one or more people connecting to a wireless access point using the WiFi cards in one or more laptops or handheld devices. ...
Protection & Security
... Unauthorized reading of data Unauthorized modifications of data Unauthorized destruction of data Preventing legitimate use of the systems (denial of service) ...
... Unauthorized reading of data Unauthorized modifications of data Unauthorized destruction of data Preventing legitimate use of the systems (denial of service) ...
Ibrahim Aljubayri`s presentation on Secure Network Channel among
... Firewall. But they are exposed to the limitation that the IDS does not protect from new attack methods, and the firewall is defenseless if the intruder is already in the system. And system security patches and version upgrades were being applied but they are also exposed to some limitations. ...
... Firewall. But they are exposed to the limitation that the IDS does not protect from new attack methods, and the firewall is defenseless if the intruder is already in the system. And system security patches and version upgrades were being applied but they are also exposed to some limitations. ...
Chapter 6 Configuring, Monitoring & Troubleshooting IPsec
... •Request or require a valid computer certificate, requires at least one CA •Only accept health certificates: request or require a valid health certificate to authenticate, requires IPsec NAP ...
... •Request or require a valid computer certificate, requires at least one CA •Only accept health certificates: request or require a valid health certificate to authenticate, requires IPsec NAP ...
Document
... NAcPs can be accessed by anybody because it is open , but service will be restricted by service provider , only authorized persons will be allowed to access the network. Suggested security architecture is built around common access key (CAK) concept . ...
... NAcPs can be accessed by anybody because it is open , but service will be restricted by service provider , only authorized persons will be allowed to access the network. Suggested security architecture is built around common access key (CAK) concept . ...
Hands-On Ethical Hacking and Network Security
... Both WPA and WPA-2 can run in either mode Pre-Shared Key uses a passphrase the user types into each device Less secure because the user might choose a guessable ...
... Both WPA and WPA-2 can run in either mode Pre-Shared Key uses a passphrase the user types into each device Less secure because the user might choose a guessable ...
Security Whitepaper, PDF
... Besides authentication via user ID and password, use of a biometric device is also possible. The data for the biometric authentication device, is handled securely and cannot be used illegally. The vein in the finger as biometric data: The vein is located within the body and, unlike fingerprints, it ...
... Besides authentication via user ID and password, use of a biometric device is also possible. The data for the biometric authentication device, is handled securely and cannot be used illegally. The vein in the finger as biometric data: The vein is located within the body and, unlike fingerprints, it ...
An IPSec-based Host Architecture for Secure
... Need to provide intra-host access control. – MSA must list member applications/users – Allow only members to listen to group traffic. ...
... Need to provide intra-host access control. – MSA must list member applications/users – Allow only members to listen to group traffic. ...
Security Whitepaper, PDF
... striven to develop and implement technology that safeguards the confidentiality of electronic documents. The most important security standard in Europe is ISO 15408, also known as Common Criteria certification. Konica Minolta has newly introduced multifunctional bizhub products validated to Common C ...
... striven to develop and implement technology that safeguards the confidentiality of electronic documents. The most important security standard in Europe is ISO 15408, also known as Common Criteria certification. Konica Minolta has newly introduced multifunctional bizhub products validated to Common C ...
Security & Cryptography
... Sending Gateway determines a packet needs to be encrypted Sending Gateway opens an IKE session with the Receiving gateway- this step defines the IKE SA Diffie-Hellman key exchange uses hashing of a certificate or shared secret to authenticate each gateway, and sets up a public/private data exchange ...
... Sending Gateway determines a packet needs to be encrypted Sending Gateway opens an IKE session with the Receiving gateway- this step defines the IKE SA Diffie-Hellman key exchange uses hashing of a certificate or shared secret to authenticate each gateway, and sets up a public/private data exchange ...
VPN: Virtual Private Network
... To establish security association (SA), the VPN( client & server) use the Internet Key Exchange IKE protocol to exchange computer certificates . Computer certificate authentication is a much stronger authentication method therefore is highly recommended. This type of authentication is used by ...
... To establish security association (SA), the VPN( client & server) use the Internet Key Exchange IKE protocol to exchange computer certificates . Computer certificate authentication is a much stronger authentication method therefore is highly recommended. This type of authentication is used by ...
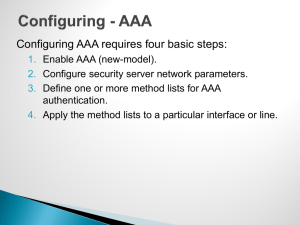
Router/Switch Security
... Configuring AAA requires four basic steps: 1. Enable AAA (new-model). 2. Configure security server network parameters. 3. Define one or more method lists for AAA authentication. 4. Apply the method lists to a particular interface or line. ...
... Configuring AAA requires four basic steps: 1. Enable AAA (new-model). 2. Configure security server network parameters. 3. Define one or more method lists for AAA authentication. 4. Apply the method lists to a particular interface or line. ...
Document
... [--Note: L. Lilien made changes to improve clarity and formatting of slides, including: (1) adding more levels for prioritization of text, (2) changing font to larger size for most slides, (3) splitting many slides into 2 or more slides (necessary due to the above changes) (4) adding emphasis by cha ...
... [--Note: L. Lilien made changes to improve clarity and formatting of slides, including: (1) adding more levels for prioritization of text, (2) changing font to larger size for most slides, (3) splitting many slides into 2 or more slides (necessary due to the above changes) (4) adding emphasis by cha ...
Authentication
.png?width=300)
Authentication (from Greek: αὐθεντικός authentikos, ""real, genuine,"" from αὐθέντης authentes, ""author"") is the act of confirming the truth of an attribute of a single piece of data (a datum) claimed true by an entity. In contrast with identification which refers to the act of stating or otherwise indicating a claim purportedly attesting to a person or thing's identity, authentication is the process of actually confirming that identity. It might involve confirming the identity of a person by validating their identity documents, verifying the validity of a Website with a digital certificate, tracing the age of an artifact by carbon dating, or ensuring that a product is what its packaging and labeling claim to be. In other words, authentication often involves verifying the validity of at least one form of identification.