Deadlocks - KSU Web Home
... Request = request vector for process Pi. If Requesti [j] = k then process Pi wants k instances of resource type Rj 1. If Requesti Needi go to step 2. Otherwise, raise error condition, since process has exceeded its maximum claim 2. If Requesti Available, go to step 3. Otherwise Pi must wait, sin ...
... Request = request vector for process Pi. If Requesti [j] = k then process Pi wants k instances of resource type Rj 1. If Requesti Needi go to step 2. Otherwise, raise error condition, since process has exceeded its maximum claim 2. If Requesti Available, go to step 3. Otherwise Pi must wait, sin ...
Comparison of Amoeba Vs Mach Operating Systems
... versions, including task and thread support, as well as the first official releases of the system, Release 0 and Release 1. Through Release 2, Mach provides compatibility with the corresponding BSD systems by including much of BSD’s code in the kernel. The new features and capabilities of Mach make ...
... versions, including task and thread support, as well as the first official releases of the system, Release 0 and Release 1. Through Release 2, Mach provides compatibility with the corresponding BSD systems by including much of BSD’s code in the kernel. The new features and capabilities of Mach make ...
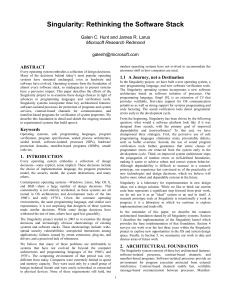
Singularity: Rethinking the Software Stack
... Low cost makes it practical to use SIPs as a fine-grain isolation and extension mechanism to replace the conventional mechanisms of hardware protected processes and unprotected dynamic code loading. As a consequence, Singularity needs only one error recovery model, one communication mechanism, one s ...
... Low cost makes it practical to use SIPs as a fine-grain isolation and extension mechanism to replace the conventional mechanisms of hardware protected processes and unprotected dynamic code loading. As a consequence, Singularity needs only one error recovery model, one communication mechanism, one s ...
Singularity: Rethinking the Software Stack
... Low cost makes it practical to use SIPs as a fine-grain isolation and extension mechanism to replace the conventional mechanisms of hardware protected processes and unprotected dynamic code loading. As a consequence, Singularity needs only one error recovery model, one communication mechanism, one s ...
... Low cost makes it practical to use SIPs as a fine-grain isolation and extension mechanism to replace the conventional mechanisms of hardware protected processes and unprotected dynamic code loading. As a consequence, Singularity needs only one error recovery model, one communication mechanism, one s ...
Guide-to-UNIX-Using-Linux-4th-Edition-Michael-Palmer-Test-Bank
... insulation, ensuring system security and user privacy. The kernel is the base operating system, and it interacts directly with the hardware, software services, application programs, and user-created scripts (which are files containing commands to execute). It is accessible only through Kernel mode, ...
... insulation, ensuring system security and user privacy. The kernel is the base operating system, and it interacts directly with the hardware, software services, application programs, and user-created scripts (which are files containing commands to execute). It is accessible only through Kernel mode, ...
This chapter covers the following key topics: • Operating Systems
... CPU Resource Management and Multitasking Although some operating systems only allow one program to run at a time (most versions of MS-DOS operate this way, for example), it’s more common to find operating systems managing multiple programs concurrently. Running multiple programs at once is called mu ...
... CPU Resource Management and Multitasking Although some operating systems only allow one program to run at a time (most versions of MS-DOS operate this way, for example), it’s more common to find operating systems managing multiple programs concurrently. Running multiple programs at once is called mu ...
ppt
... Request = request vector for process Pi. If Requesti [j] = k then process Pi wants k instances of resource type Rj 1. If Requesti Needi go to step 2. Otherwise, raise error condition, since process has exceeded its maximum claim 2. If Requesti Available, go to step 3. Otherwise Pi must wait, sin ...
... Request = request vector for process Pi. If Requesti [j] = k then process Pi wants k instances of resource type Rj 1. If Requesti Needi go to step 2. Otherwise, raise error condition, since process has exceeded its maximum claim 2. If Requesti Available, go to step 3. Otherwise Pi must wait, sin ...
xv6 - PDOS-MIT
... operating system manages and abstracts the low-level hardware, so that, for example, a word processor need not concern itself with which type of disk hardware is being used. It also multiplexes the hardware, allowing many programs to share the computer and run (or appear to run) at the same time. Fi ...
... operating system manages and abstracts the low-level hardware, so that, for example, a word processor need not concern itself with which type of disk hardware is being used. It also multiplexes the hardware, allowing many programs to share the computer and run (or appear to run) at the same time. Fi ...
A Real-Time Linux
... purpose are obvious, but we should mention both unpredictability of execution and high interrupt latency as critical problems. General purpose time-shared operating systems have schedulers that are intended to balance response time and throughput. As a result the execution of any process depends in ...
... purpose are obvious, but we should mention both unpredictability of execution and high interrupt latency as critical problems. General purpose time-shared operating systems have schedulers that are intended to balance response time and throughput. As a result the execution of any process depends in ...
A Real-Time Linux
... purpose are obvious, but we should mention both unpredictability of execution and high interrupt latency as critical problems. General purpose time-shared operating systems have schedulers that are intended to balance response time and throughput. As a result the execution of any process depends in ...
... purpose are obvious, but we should mention both unpredictability of execution and high interrupt latency as critical problems. General purpose time-shared operating systems have schedulers that are intended to balance response time and throughput. As a result the execution of any process depends in ...
Book 2.indb
... just for CPU usage but for counting pages printed, cards punched, cards read, disk storage used and for signaling when operator intervention was required by jobs such as changing magnetic tapes. All these features were building up towards the repertoire of a fully capable operating system. Eventuall ...
... just for CPU usage but for counting pages printed, cards punched, cards read, disk storage used and for signaling when operator intervention was required by jobs such as changing magnetic tapes. All these features were building up towards the repertoire of a fully capable operating system. Eventuall ...
Chapter 1
... In Unix, each file is identified by an i-number o i-number indexes into i-node table Link creates a new directory entry with same i-number o Has a new name (note instead of memo) ...
... In Unix, each file is identified by an i-number o i-number indexes into i-node table Link creates a new directory entry with same i-number o Has a new name (note instead of memo) ...
Windows, Linux and Mac Operating system Booting Process: a
... operating system starts its loading on the computer. Step03: after getting the idea about the primary partition the first bootstrap loader load into the memory is GRUB (Grand Unified Boot Loader) or LiLo (Linux Loader) which try to load the operating system feature form the supporting resources the ...
... operating system starts its loading on the computer. Step03: after getting the idea about the primary partition the first bootstrap loader load into the memory is GRUB (Grand Unified Boot Loader) or LiLo (Linux Loader) which try to load the operating system feature form the supporting resources the ...
z/VM Conversational Monitor System (CMS)
... a virtual machine and provides both the interactive z/VM end-user interface and the general z/VM application programming interface. CMS runs only under the control of the z/VM Control Program (CP). CMS Pipelines- CMS job control product for z/VM that enables complex tasks to be specified and execute ...
... a virtual machine and provides both the interactive z/VM end-user interface and the general z/VM application programming interface. CMS runs only under the control of the z/VM Control Program (CP). CMS Pipelines- CMS job control product for z/VM that enables complex tasks to be specified and execute ...
PPT_ch01_PPT_ch01 - CCRI Faculty Web
... • In 1984, Apple Macintosh developed a GUI and mouse pointing device, which allowed users to interact with the OS on a graphical screen. • The mouse allowed users to point at or click icons or to select items from menus to accomplish tasks. • When the Macintosh was introduced, it seemed light years ...
... • In 1984, Apple Macintosh developed a GUI and mouse pointing device, which allowed users to interact with the OS on a graphical screen. • The mouse allowed users to point at or click icons or to select items from menus to accomplish tasks. • When the Macintosh was introduced, it seemed light years ...
Trusted Operating Systems
... • Formal description of the allowable paths of information flow in a secure system • Set of subjects and another set of objects • Each subject s has a fixed security clearance C(s) • Each object o has a fixed security class C(o) ...
... • Formal description of the allowable paths of information flow in a secure system • Set of subjects and another set of objects • Each subject s has a fixed security clearance C(s) • Each object o has a fixed security class C(o) ...
Advanced Operating Systems
... Today, everything is embedded systems and OS an essential part of it. ...
... Today, everything is embedded systems and OS an essential part of it. ...
Process and Thread Scheduling - UC Davis
... • CPU utilization – keep the CPU as busy as possible • Throughput – # of processes that complete their execution per time unit • Turnaround time – amount of time to execute a particular process • Waiting time – amount of time a process has been waiting in the ready queue • Response time – amount of ...
... • CPU utilization – keep the CPU as busy as possible • Throughput – # of processes that complete their execution per time unit • Turnaround time – amount of time to execute a particular process • Waiting time – amount of time a process has been waiting in the ready queue • Response time – amount of ...
Lecture 4, Part 1
... What Is Scheduling? • An operating system often has choices about what to do next • In particular: – For a resource that can serve one client at a time – When there are multiple potential clients – Who gets to use the resource next? – And for how long? ...
... What Is Scheduling? • An operating system often has choices about what to do next • In particular: – For a resource that can serve one client at a time – When there are multiple potential clients – Who gets to use the resource next? – And for how long? ...
Why Threads? - WordPress.com
... • multi-threaded applications have multiple threads within a single process, each having their own program counter, stack and set of registers, but sharing common code, data, and certain structures such as open files. • For example in a word processor, a background thread may check spelling and gram ...
... • multi-threaded applications have multiple threads within a single process, each having their own program counter, stack and set of registers, but sharing common code, data, and certain structures such as open files. • For example in a word processor, a background thread may check spelling and gram ...